Corrupt Office Documents
My tool to analyze CFBF files, oledump.py, is not only used to analyze malicious Office documents.
Over the years, a couple of users reached out to me informing me that they were able to recover their VBA code from corrupt Word or Excel documents with my tool.
Although Word or Excel is no longer able to open/repair the corrupted document, the stream(s) with VBA code can remain intact, and parsed with oledump.py to extract the VBA source code.
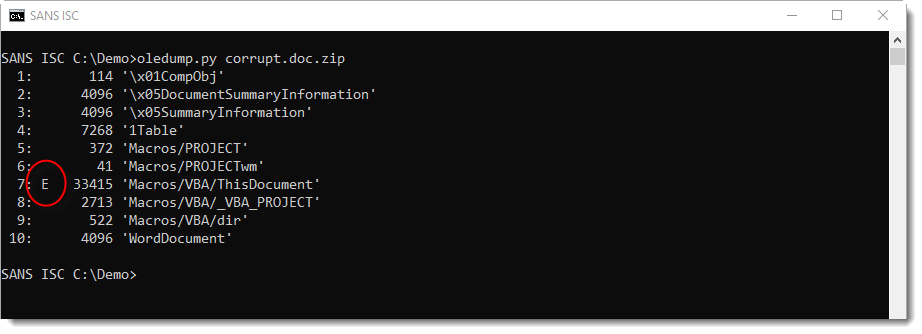
When oledump.py finds streams with VBA code, but is not able to completely extract the VBA source code, an E indicator will be used to mark the stream (in stead of M/m).
Like in this example:
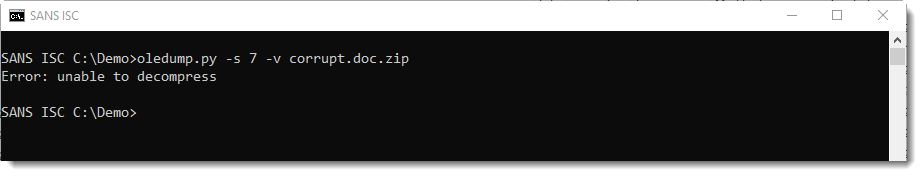
When this happens, option -v can not be used to extract and decompress the VBA source code:
But you can try another option, --vbadecompresscorrupt, to try a partial recover of the VBA source code:
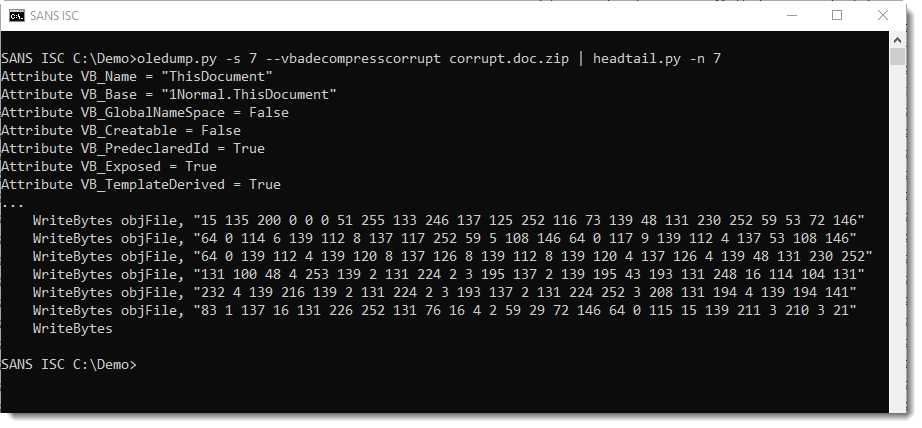
Remark that this will not always work, it depends on the type of corruption.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments