TShark Tip: Extracting Field Values From Capture Files
TShark is WireShark's console program: it's like WireShark, but with a command-line interface in stead of a GUI.
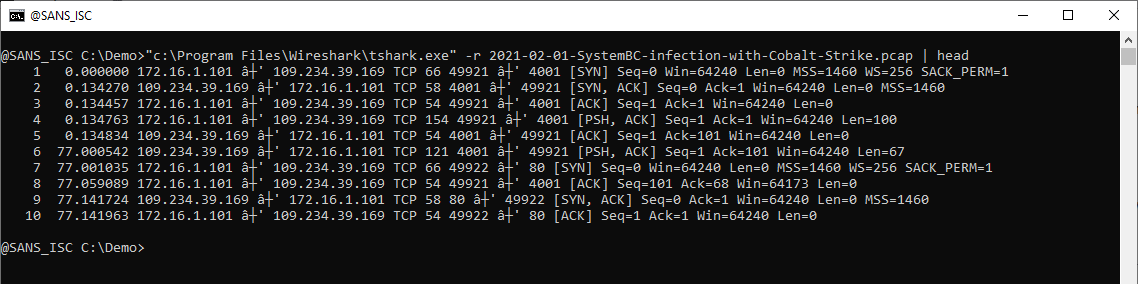
TShark can process a capture file: use option -r to read and process the capture file, like this:
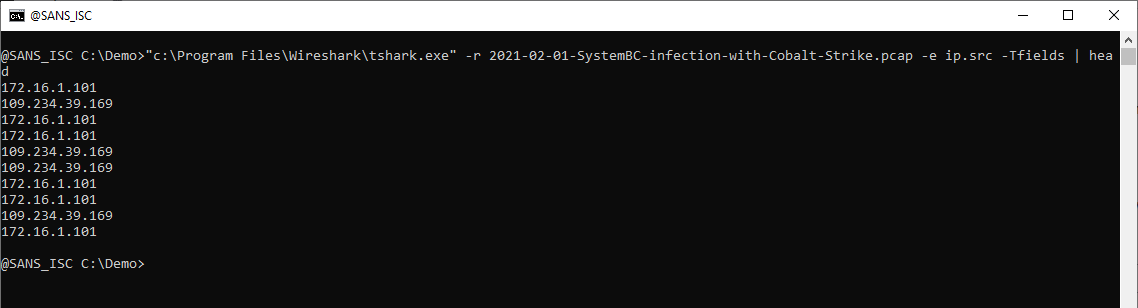
Option -e can be used to display the value of a field, like ip.src. You have to combine option -e with option -Tfields to display field values:
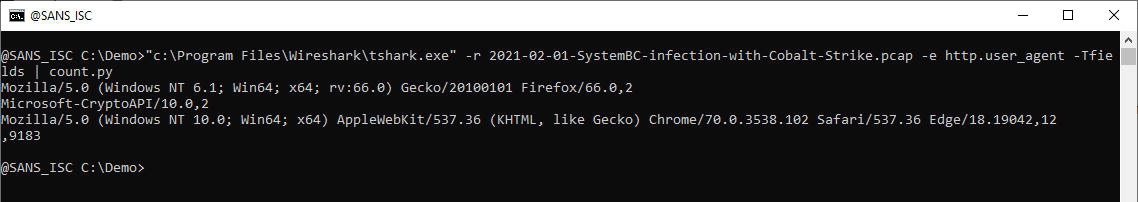
 When I want to produce a list of User Agent Strings found in a capture file, I select field http.user_agent. Piping the output of TShark into my tool count.py allows me to produce a list of unique values (with counter):
When I want to produce a list of User Agent Strings found in a capture file, I select field http.user_agent. Piping the output of TShark into my tool count.py allows me to produce a list of unique values (with counter):
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com
Click HERE to learn more about classes Didier is teaching for SANS
×
![modal content]()
Diary Archives


Comments