Quickie: Extracting HTTP URLs With tshark
After I posted diary entry "Quickie: tshark & Malware Analysis", someone asked me how to extract HTTP URLs from capture files with tshark.
Use option -r to read a capture file, and options -T fields and -e http.request.full_uri to let tshark print the full URL of HTTP requests. Problem is that tshark will also output an empty line for each packet. I filter these out with findstr or grep:
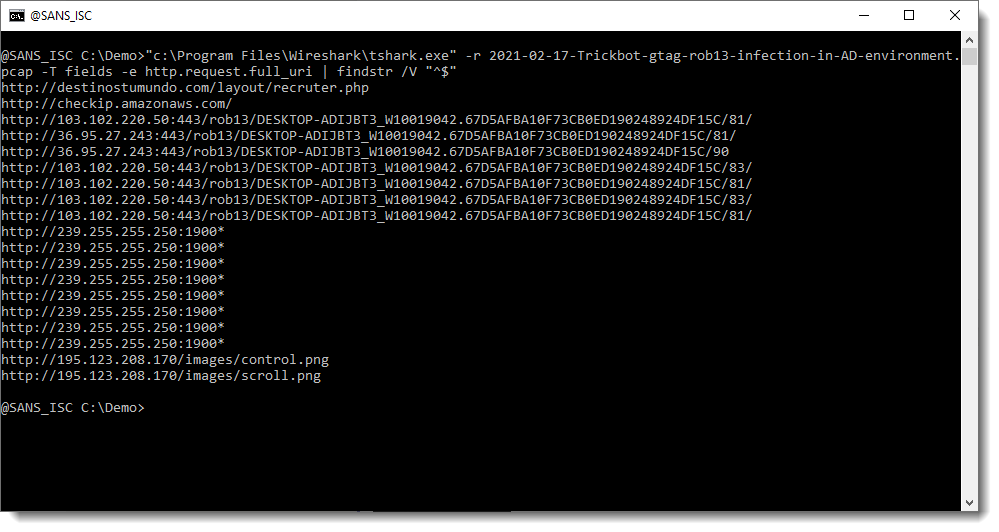
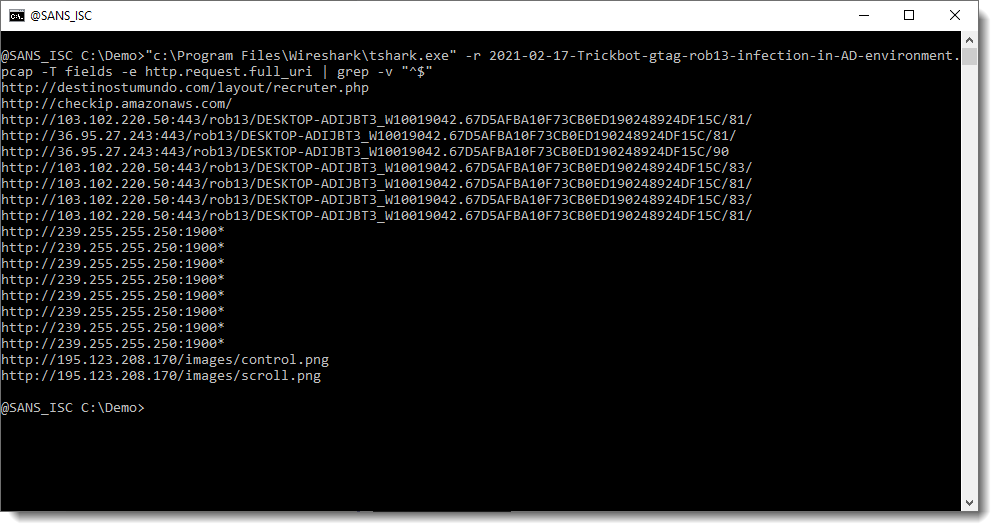
Please post a comment if you know how you can avoid these empty lines with a tshark option.
It's also possible to print the full protocol packet tree with packet details, and search this for URLs with my re-search.py tool. The difference here, is that you will find all kinds op URLs, not only for HTTP requests.
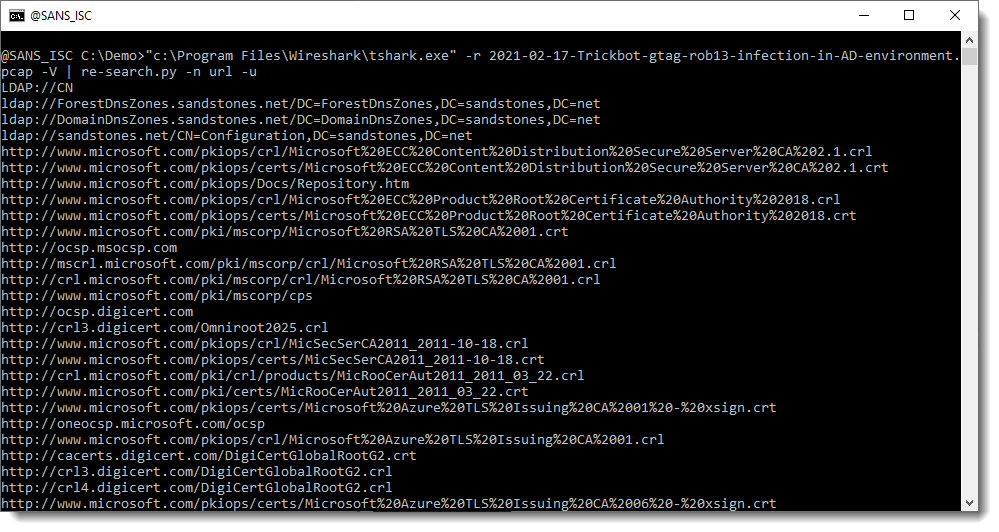
For example, many of the URLs seen in this screenshot, are found inside certificates.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments