Cisco default credentials - again!
Cisco today released a security advisory announcing that some of Cisco's IronPort "virtual appliance" products contain "multiple default SSH keys". To quote:
A vulnerability in the remote support functionality of Cisco WSAv, Cisco ESAv, and Cisco SMAv Software
could allow an unauthenticated, remote attacker to connect to the affected system with the privileges of the root user.
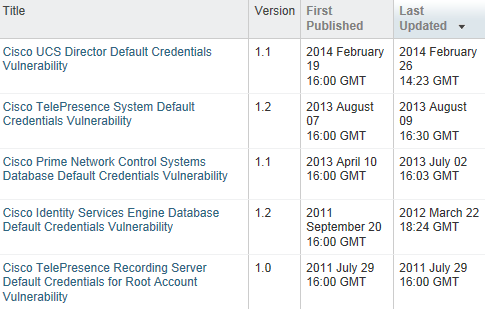
Oh, good thing it's only "root". You had me worried there for a second :). Interestingly, there was a somewhat similar Cisco advisory one year ago (on CUCDM) where also a default SSH key was present, and equally led to root privileges. Searching for "default credentials" on Cisco's advisory web site shows that for the past several years, the presence of backdoor and default users continues to be a recurring issue:
To Cisco's credit, they seem to have found today's SSH key problem on their own, before it was abused, so maybe this is a sign of better times to come, and evidence that after all these years, someone at Cisco has actually started to systematically audit their entire code base for the presence of default credentials. Or maybe it just was a lucky find, and the "stellar" 10 year track record of default credential security bulletins will continue for another decade? Time will tell...


Comments
Anonymous
Jun 26th 2015
1 decade ago