Have a Happy New Year
I know in some parts of the world it's already 2010, so I'd like to take the time to wish you all a Happy New Year. Here's looking for a safer 2010, as the movement away from OS exploits and into client exploits gets hotter, I think this will be a busy year.
For those of you celebrating or are going to celebrate, be safe.
-- Joel Esler | http://blog.joelesler.net | http://twitter.com/joelesler
Sendmail 8.14.4 has been released
As my college (Swa) here at the ISC said in the coffee room this morning, "It's been awhile since Sendmail has put out a release that fixed security issues."
You may review the release notes here: http://www.sendmail.org/releases/8.14.4
About mid-way down are the security enhancements that have been made to the product. Please consider upgrading and let us know how it works out. I am sure all the *nix distros that bundle sendmail (pretty much all of them) will be following soon with their own packaged releases.
-- Joel Esler | http://blog.joelesler.net | http://twitter.com/joelesler
0 Comments
Ready to use IDS Sensor with Sguil
I have just released an update on my 32-bit hardened IDS sensor (version 6.4) with all the Sguil components ready to use installation CD available here. I have also released for the first time a 64-bit equivalent (version 1.0) of the same hardened sensor available here. The CD has 3 options: sensor only, database only or all components on the same system.
The install.pdf document on how to install and configure the system is in the rel_note directory and available online for the 32-bit here and 64-bit here.
-----------
Guy Bruneau IPSS Inc. gbruneau at isc dot sans dot org
2 Comments
GSM Cell Phone Encryption is Cracked - Interception of Cell Calls Possible
According to the Financial Times, a "hacking" contest sponsored by Karstren Nohl, a German Encryption Expert, has resulted in the cracking of the encryption used for GSM phones world-wide. This potentially means about 3 billion cell phones are susciptible to eavesdropping. It doesn't affect data trasmissions or 3G calls, but others are affected.
The encryption method used is A5/1 which was developed over 21 years ago. Apparently the vulnerability has been known for about 15 years but this puts it into "practical" application. Practical is in quotes because the trade association of GSM manufacturers says this cracking requires equipment beyond the reach of most people. Nohl and others disagree putting the pricetag at about $1500 USD for the equipment to begin listening to calls.
In 2004, a similar vulnerability (in A5/2, a different algorithm) caused cell phone companies to replace base stations in 3 continents to remediate the problem and took over 18 months to complete. Assuming the same action is taken, a similar multi-billion dollar effort would be needed to update cell towers worldwide. Another plan could be as simple as blanketing every area with 3G which uses a different method all together (though I'm not a cellular technology expert).
The vulnerability was annouced at this years Chaos Communications Congress in Berlin. It is not likely that wide-spread exploitation is underway or will be in the near future. Time will tell how big the impact actually is.
--
John Bambenek
bambenek at gmail /dot/ com
4 Comments
KDC DoS in cross-realm referral processing
If you are currently using MIT krb5 release krb5-1.7, a null pointer dereference has been reported where an unauthenticated remote attacker could cause the KDC to crash (DoS). This is not a vulnerability in the Kerberos protocol. A patch and a workaround has been made available here.
-----------
Guy Bruneau IPSS Inc. gbruneau at isc dot sans dot org
0 Comments
Microsoft responds to possible IIS 6 0-day
Following up to recent diaries 7816 and 7810 and numerous other sources regarding a possible IIS 0-day. Microsoft has responded indicating that there is no problem with IIS 6, but rather this is a configuration issue which should not be present in an out of the box IIS 6 server or any server properly configured to Microsoft standards.
-- Rick Wanner - rwanner at isc dot sans dot org
0 Comments
What's up with port 12174? Possible Symantec server compromise?
This is a heads-up that we have received a number of queries from readers about an increase in probes to port 12174. The dshield data for port 12174 clearly corroborates a large increase.
Another reader indicates that they are seeing Symantec servers being attacked and compromised via port 12174. Once compromised a whole bunch of nasty malware is downloaded to the machine. He provides a tcpdump signature which has been effective for them in helping detect the resulting traffic.
'src port 7000 and dst port 445'
If anyone has first-hand observations into what is going on, please let us know via our contact link.
-- Rick Wanner - rwanner at isc dot sans dot org
5 Comments
It's been 10 years
The Internet Storm Center directly traces it's roots back to the year 1999. A SANS Project called the Consensus Internet Database was created as part of the infamous Y2K effort.
On March 22, 2001, intrusion detection sensors around the globe logged an increase in the number of probes to port 53, the port that supports the Domain Name Service. Over a period of a few hours, more and more probes to port 53 were arriving - first from dozens and then from hundreds of attacking machines.
Within an hour of the first report, several analysts, all of whom were fully qualified as SANS GIAC certified intrusion detection experts back then called "Track 3", now named "503", agreed that a global security incident was underway. They immediately sent a notice to a global community of technically savvy security practitioners asking them to check their systems to see whether they had experienced an attack. Within three hours a system administrator in the Netherlands responded that some of his machines had been infected, and he sent the first copy of the worm code to the analysts. The analysts determined what damage the worm did and how it did it, and then they developed a computer program to determine which computers had been infected. They tested the program in multiple sites and they also let the FBI know of the attack. Just fourteen hours after the spike in port 53 traffic was first noticed, the analysts were able to send an alert to 200,000 people warning them of the attack in progress, telling them where to get the program to check their machines, and advising what to do to avoid the worm. The Li0n worm event demonstrated what the community acting together can do to respond to broad-based malicious attacks. Most importantly, it demonstrated the value of sharing intrusion detection logs in real time. Only in the regional and global aggregates was the attack obvious. The technology, people, and networks that found the Li0n worm were all part of the SANS Institute's Consensus Incident Database (CID) project that had been monitoring global Internet traffic. CID's contribution the night of March 22 was sufficient to earn it a new title: the SANS Internet Storm Center. Today the Internet Storm Center gathers millions of intrusion detection log entries every day, from sensors covering over 500,000 IP addresses in over 50 countries. It is rapidly expanding in a quest to do a better job of finding new storms faster, identifying the sites that are used for attacks, and providing authoritative data on the types of attacks that are being mounted against computers in various industries and regions around the globe. The Internet Storm Center is a free service to the Internet community. The work is supported by the SANS Institute from tuition paid by students attending SANS security education programs. Volunteer incident handlers donate their valuable time to analyze detects and anomalies, and post a daily diary of their analysis and thoughts on the Storm Center web site. What we would like to hear from you, the readers is, in the past 10 years. What are the memorable moments? What are the highs and lows of the past ten years (information security/ISC wise)? Rather a 'decade in review'. What we are going to is put these all together and on January 1st of 2010, we'll post a diary showing these. The past 10 years in review, submitted by you, the readers, whom without -- The Internet Storm Center, would not function. Please give us feedback via the Contact link at the top of the page on http://isc.sans.org. -- Joel Esler | http://blog.joelesler.net | http://twitter.com/joelesler
2 Comments
How this weekend's attempted Terrorist attack relates to IT.
In case you were spending time with your family this weekend and not watching the news, there was an attempted Terrorist attack on a flight from Amsterdam to Detroit, USA on December 25th. From what I understand this "terrorist" was on the flight, and as the plane was getting ready to land, tried to ignite something in his lap to catch the plane on fire, or cause it to explode. (DHS is looking into which one it was supposed to be).
As a result, the US Gov't (and several foreign Gov'ts) stepped up security. Adding more Air Marshalls, increasing security screening at checkpoints, explosive sniffing dogs, and not allowing people to use PED's during portions of the flight. (PED = Portable Electronic Devices).
So, how does this related to Information Security?
#1) Stepping up the security that didn't work in the first place
It's not enough to ramp up the security that obviously didn't work. This suspect was able to get on board, with some type of incendiary device. (Notice I said "Incendiary device", not PED. I don't know why Gov't regulators and Airlines insist on punishing things like DVD players and iPhones, (etc) when something bad happens.) In the normal reactionary mode, you would say "how did 'x' device get on board the plane and why didn't we catch it?" Obviously, it's impossible to look for everything that people will invent to circumvent security policy, it's impossible to make your air travel 100% safe. Anytime you have that many people that want to do that many bad things, there is a way that the "Bad guys" will find a way to do something "Bad". It's inevitable. The answer is compensating controls. Ramping up more of the same isn't going to do it. But doing additional things that are different that focus on different areas will help. You can't lock down port 80 because there are too many attack vectors. But you can force people through a proxy and keep them from doing bad things using tools like Websense, (etc). But all of that doesn't matter if you allow external proxies and can SSH out of the network. If you lock down one area, you have to lock down them all.
#2) Playing the Blame Game.
Oh, it was PED's. Oh, it was because we let the suspect out of their seat to retrieve something from the overhead bin. Oh, it's because this person is running a non-standard configuration of IIS. Oh, it's because this person is running Firefox instead of IE. Stop blaming and fix the problem. Don't sit in a meeting and say "Oh, well, it's because he was running that evil Mozilla and not our precious IE, that's how we got hacked!" Don't blame the tool, blame the person for not patching the tool. How can you get Firefox to update? How can you keep people from installing it in the first place? It's not about placing blame, it's about finding what went wrong and fixing the problem in a way that YOU CAN CONTROL. Not allowing people to get up during a flight isn't going to work, because people are going to NEED to get up on a flight. Not allowing people to use their iPods on flights isn't going to work, because people are going to do it anyway. The big question is, what is the device the guy had and tried to ignite, and how did it get on the plane?
#3) Incorrect allowances.
In the words of the comedian Louis Black "...you can't bring a lighter on board the plane, but you can bring matches. You can bring matches.. That's what is wrong with this country, your brain can't cope with that kind of logic." We don't allow you to bring a lighter on board, to you know, ignite things with, but you can bring matches on board. I know I'll catch flack from the Smokers who are reading this, and I understand, but listen.. you can't smoke on a plane anyway. There is no need for anyone to have anything that ignites past security. "So how do we smoke in the airport", well.. 1) Don't. 2) Quit, (Yes, you can do it, I did) or 3) I am sure we can figure out some kind of electronic ignition device that we place in the smoking rooms in the airports. All of today's modern technology, and we can't figure out how to NOT let people carry something that causes FLAME on a plane. Allowing people to bypass one security control by compensating with an equally damaging one kinda defeats the purpose doesn't it? You don't allow people to run Firefox, but you allow them to run Safari. You don't allow people to run OSX because you "can't control it" (yes I've heard this), but you allow people to run Linux. Poor examples, and I welcome more if you'd like, but you get my point.
From my armchair quarterbacking spot, how did the flame get on the plane? How did the device get on the plane? What was the device?
-- Joel Esler | http://blog.joelesler.net | http://twitter.com/joelesler
5 Comments
Microsoft puts up a blurb on their website about the IIS 0day.
Microsoft has put up a response on their security blog concerning the IIS "0day". They say that only installations in a specific "non-default" and "unsafe configuration" are vulnerable to the condition. Also they note that if the administrator had not altered the default configuration and followed best practices in the securing of the webserver, then this exploit wouldn't work.
Unfortunately, we know that doesn't always wind up being the case. Read more of their blog post here.
-- Joel Esler | http://blog.joelesler.net | http://twitter.com/joelesler
0 Comments
Pressure increasing for Microsoft to patch IIS 0 day
The other day ISC Handler Guy Bruneau posted a Diary pointing to a "Microsoft IIS 0Day Vulnerability in Parsing Files (semi-colon bug). Secunia has confirmed the vulnerability "on a fully patched Windows Server 2003 R2 SP2 running Microsoft IIS version 6. Other versions may also be affected". It should be mentioned that if you don't think you're vulnerable because you are running a non-vulnerable version of IIS, the vulnerable functionality may have been made available by your webmaster when deploying IIS.
After reading up on related posts and IIS issues, the nature of the vulnerability is such that it's going to be widely exploited soon, quite successfully, and not only by the usual suspects, but more effectively by the specialized groups of attackers that are after unrestricted access to your protected network, and, of course, the other groups after more mundane items like bank accounts.
No response yet from Microsoft that I see, I would expect significant customer pressure is on Microsoft to correct this vulnerability in the January patch cycle.
2 Comments
Did any digital nasties show up under your tree this year?
As many of our readers may recall the past two years we had numerous reports of infected digital devices arriving as Christmas and holiday presents. We believe that the global manufacturing process has improved based on consumer complaints, but there is always the possibility that something got through due to the complexity of the digital supply chain. Let us know via our contact form if you, your family, or your friends received any malicious "value-added features" in electronic hardware either given or received as gifts. We are especially interested in USB devices such as photo frames, GPS units, external hard drives, etc. since they seemed to be the items most vulnerable in the past.
Otherwise, have a safe and happy holiday season and best wishes to you and your families.
Marcus H. Sachs
Director, SANS Internet Storm Center
2 Comments
Microsoft IIS File Parsing Extension Vulnerability
A vulnerability has been identified in Microsoft Internet Information Services (IIS) where the server in incorrectly handling files with multiple extensions separated by the ";" character such as "malicious.asp;.jpg" as an ASP file. This could allow attackers to upload malicious executables on a vulnerable web server, bypassing file extension protections and restrictions. This vulnerability does not work with ASP.Net.
Pending an IIS security patch, some workaround are available here.
-----------
Guy Bruneau IPSS Inc. gbruneau at isc dot sans dot org
0 Comments
F5 BIG-IP ASM and PSM Remote Buffer Overflow
The BIG-IP Application Security Manager (ASM) and Protocol Security Manager (PSM) "bd" daemon is vulnerable to a remote buffer overflow which could be exploited by remote attackers to cause a denial of service and may cause the system to crash and dump core.
The following products affected by this issue are:
F5 BIG-IP ASM versions 9.4.4 through 9.4.7
F5 BIG-IP ASM versions 10.0.0 through 10.0.1
F5 BIG-IP PSM versions 9.4.5 through 9.4.7
F5 BIG-IP PSM versions 10.0.0 through 10.0.1
Registered users can access the advisory here.
-----------
Guy Bruneau IPSS Inc. gbruneau at isc dot sans dot org
0 Comments
Merry Festivus: Commence the "Airing of Infosec Grievaces"
In honor of today's holiday, Festivus (for those familiar with Seinfeld)... what is on your list of infosec grievances for 2009? What's the "wins" for the year? Use the comment feature on these entry, will update with a Top 10 list assuming we get enough responses.
--
John Bambenek
bambenek at gmail /dot/ com
21 Comments
Blackberry Outage
UPDATED 6:00AM CST (bambenek) - It appears Blackberry's network is back up. The outage affected only those applications that needed to go through that network. Native IP was working fine, but seemed to be all providers.
Several readers have told us that their Blackberry PDAs have not been working for the past few hours. I can attest that mine is dead too, the last email came in a bit over three hours ago. There is a lot of chatter on Twitter and several of the support forums on the Blackberry website confirm that the outage is widespread. More to follow as we learn about it.
Marcus H. Sachs
Director, SANS Internet Storm Center
5 Comments
Tell us about your Christmas Family Emergency Kit
If you read this diary, then you are probably one of those people who will be asked to fix various family computer problems [1]. Maybe you avoid it by just telling them that you never graduated and still work as a waiter. But then again, that doesn't work so well once you hit 40.
So what do you take with you when you visit family? Any tools / software / hardware that you like? Leave a comment to this story or let us know via our contact form [2]
[1] http://theoatmeal.com/comics/computers
[2] https://isc.sans.org/contact.html
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
17 Comments
Howard Schmidt named as new Cybersecurity Coordinator
The White House announced this morning that Howard Schmidt was named as the first White House Cybersecurity Coordinator. I've known and worked with Howard for over 12 years and I think he's going to do well in this position.
Marcus H. Sachs
Director, SANS Internet Storm Center
2 Comments
There is no such thing as a free lunch .
An ISC reader wrote in alerting us to unconfirmed reports that organizations and some government agencies are received "unexpected" shipments of USB thumb drives. Don't know if it's true or not, but with the holidays upon us it bears reminding that USB devices received in suspicious ways often are loaded with hostile software. Sometimes, even commercial off-the-shelf USB devices like photo frames and the like can be infected (see: the Digital Hijackers ISC diary from last Christmas).
It remains a favorite trick of pentesters to throw USB keys infected with malware around for a low-tech vector of an attack in an organization. Trade shows and the like, even a better venue (and you can target by industry or organization). A colleague told me that his favorite trick was to mark a USB thumb drive as "Joe's Bachelor Party Pictures" for that extra "incentive" to get people to plug the device in.
If you're an organization and receive USB keys, even promotional swag, do a low-level format first. If you buy a USB storage device from the store, wipe it first (especially the annoying U3 devices). Sometimes vendors ship USB keys with firmware updates that can be infected (see this example involving HP firmware, there was also a report for Checkpoint Firewall firmware too). Those devices can't be low-level formatted, but a quick "media check" for hidden goodness may be warranted.
There's no such thing as a free lunch, but there is such a thing as free malware. Cavaet Emptor.
If you've had such shipments of unknown USB devices, let us know so we can coorelate data.
--
John Bambenek
bambenek at gmail /dot/ com
0 Comments
iPhone Botnet Analysis
SRI's Malware Threat Center has published an excellent analysis of the iPhone botnet that we covered in a diary a few weeks ago. Here is the abstract:
We present an analysis of the iKee.B (duh) Apple iPhone bot client, captured on 25 November 2009. The bot client was released throughout several countries in Europe, with the initial purpose of coordinating its infected iPhones via a Lithuanian botnet server. This report details the logic and function of iKee's scripts, its configuration files, and its two binary executables, which we have reverse engineered to an approximation of their C source code implementation. The iKee bot is one of the latest offerings in smartphone malware, in this case targeting jailbroken iPhones. While its implementation is simple in comparison to the latest generation of PC-based malware, its implications demonstrate the potential extension of crimeware to this valuable new frontier of handheld consumer devices.
Thanks to Phil Porras and the MTC team for all of their great work!
Marcus H. Sachs
Director, SANS Internet Storm Center
3 Comments
Educationing Our Communities
A few weeks ago it was my pleasure to talk to a group of young people who were participating in a program through Iowa State University School of Engineering. This program is designed to get children interested in and excited about science, technology and engineering. www.isek.iastate.edu/fll/ The group was preparing for the regional Lego League competition and the project that they chose for the competition was how to safeguard their VIrtual Community. They asked me questions about what we see happening on the Internet and how it effects them as individuals as well as the businesses that are connected to the Internet. I explained to them the dangers of illegal download activity, clicking on links in emails, messages and websites, etc. They asked what could be done to improve the condition of the virtual world. I told them how we often times joke about creating a "test" and that everyone would have to pass the test and receive a driver's license before they were allowed on the Internet - the World Wide Superhighway. The group took this to the next level and created a test:
Facts to Know to Keep Your Computer Safe from Viruses
A virus is a computer program that is intended to do harm. A virus can delete information on your computer or use your e-mail to send viruses to other computers.
Malware is a computer program such as a Trojan Horse or a Worm.
A Trojan Horse is when a computer virus pretends to be something that it is not. EX: screen savers or computer games. If something sound too good to be true, then don’t trust it.
A Worm is a computer virus that moves through ports and uses the computer network.
A DNS code is an address that changes the number code into words so we can remember them.
A router is a device that ships and delivers information and a router switch is the same thing but it is more efficient.
If you get an unexpected email from somebody you don’t know don’t open it.
If there is an attachment to an email you can open it as long as you have the file checked with Anti-Virus protection software.
There are many ways to be protected from a virus like thru a firewall and anti-virus programs like Norton, and Mac-Updates that are already on a Mac.
Firewalls don’t accept some things because they don’t fit the criteria.
Be careful when going to game sites or other sites that let you download things because you may get a virus.
Remember, nothing is free. Beware of free stuff, programs, games, etc. that are offered on the Internet. These usually contain viruses.
Anything that connects to the internet can contact a virus this includes your cell phone and Xbox.
Are you prepared to protect your computer against a virus? Earn your Internet User’s License
Take this quiz to see if the internet is a safe place for you to be. Get a piece of paper to write your answers down.
1. What is a virus?
A. an illness causing you to become sick
B. An uncommon program that goes into your computer to help
C. A malicious computer program intended to do harm.
D. None of the above
2. What is Malware?
A. A malicious program such as a worm or Trojan horse.
B. A kind of Anti-virus program.
C. A new style of clothing that is in fashion.
D. A newsletter on the internet providing information about viruses
3. What is a DNS (Domain Name Server) code?
A. It changes numbers into words so we remember them
B. It is a program protecting your computer.
C. It turns your name for your computer in to a number address.
D. None of the above
4. How do you know if you can trust the source of an email, im, etc?
A. If the source looks somewhat familiar just open it.
B. The email will check it anyway so you can open it.
C. If you do not know the source and was not expecting a message do not trust it.
D. None of the above
5. What is a Trojan horse?
A. A virus that hides your files
B. A moving virus infecting many computers
C. A mystical being
D. A virus that pretends to be one thing that it’s not. i.e. screen saver.
6. What is a worm?
A. Something crawling through soil.
B. A computer virus moving through ports.
C. Something that is tracking the computer
D. None of the above
7. Which of these are not computer protection programs?
A. Firewall
B. Norton
C. Plato
D. Mac-Updates
8. If you get an unexpected e-mail how should you open the attachments?
A. Don’t open it all.
B. Have your antivirus program verify it.
C. Go ahead and open it
D. None of the above.
9. Why don’t fire-walls accept some ports?
A. Because it doesn’t meet it’s criteria
B. It doesn’t like them.
C. It is too much work.
D. None of the above
10. How is a router switch different than a router?
A. It’s not different at all.
B. It’s more efficient
C. It’s less efficient
D. None of the above
Deb Hale Long Lines, LLC
4 Comments
Frustrations of ISP Abuse Handling
I am the Abuse Coordinator for a small ISP in the Midwest and am very receptive and proactive when dealing with spam originating from our network. I monitor log reports from servers and firewalls, have subscribed to all of the FBL's that I am aware of, participate in an abuse listserve, review our domain information on MS site, SenderBase and Trusted Source daily, and resolve to eliminate spam from our network as quickly as possible often times before we even receive the first official notification. We have been under a barrage of spam attacks from various ip addresses all over the world just like many others have reported and have felt the pain of email DOS first hand. We recently implemented a Red Condor filtering system blocking over 24 million spam emails from just one of our domains in the first 3 weeks of December. We know first hand the damage that can be done by spam. We strive everyday to work with our customers to reduce the amount of spam coming from their home computers as well as with our business customers to ensure that they secure their mail servers to prevent abuse. As soon as abuse is discovered it is handled.
So where am I going with this? I am frustrated with organizations such as Trend Micro, Sorbs, etc that block IP's for NO reason whatsoever. They simply don't like the "server name" that was chosen or the way the IP is identified in ARIN registration. One example of one of our business mail servers that was blocked because they didn't like the name.... da2.our.domain (real name masked). They assumed that da2 stood for "dialup access" instead of "direct admin". There had been absolutely no spam reported from the box but because they THOUGHT it was a dialup computer they blocked the IP. We recently have been battling blocklists that are preventing email from being delivered simply because our ARIN listing does not indicate that the IP address is static. Now these are legitimate mail servers on IP addresses that are statically assigned to our customers. There has been absolutely no spam reports from any of the servers yet they are being blocked from sending legitimate email.
The companies that are doing this have taken it upon themselves to act as god of the Internet. They insist that we comply with their demands, in the manner that THEY want it done and because we won't comply they will not allow legitimate emails to be delivered. One of the servers that they have blocked is a mail server for a small city government, for their police dept, fire dept, and EMS dept. It was explained to Trend Micro that they were endangering the well being of this small community without justification. I asked them if they had any examples of spam originating from the IP's and they indicated they had none. They sent an email with what needed to be done to comply with their rules. They said that we had to comply or they WILL NOT remove the block.
Some of you are probably thinking - why don't you just do what they want done so that it doesn't happen again? We have considered that. However, last week it was SORBS, this week it is Trend Micro, next week someone else, the next week someone else and we will end up spending all of our time trying to comply with every one of these groups that comes along. We were told by Trend Micro that they want all mail servers to indicate that they are mail servers by using mail. or smtp. for the server names. We don't control our customers mail servers. We don't tell them what they have to name the server and many times we don't even know that they put up a mail server unless they have problems delivering or receiving mail. We don't have time to be big brother to our customers. If the customer violates our AUP, if the customer's IP is reported for spam or copyright infringement it is handled immediately. Otherwise, it is up to the business themselves and their IT folks what they do with the static IP's that are assigned to them.
Some people complain that the ISP's aren't doing enough to keep the Internet free from spam and malicious activity and you may be right. It could be because the ISP's are spending all of their free time playing games with the Internet Big Brothers. I for one am tired of hearing the criticism of ISP's, of the complaining that we aren't doing enough. I know folks that work for other small ISP's such as ours and I know that they too are doing their best to stay ahead of the game. I think it is time for all of the "Big Brothers" out there to get a clue, you are doing more damage to the Internet by your lack of responsibility then all of us put together. Until we all agree to one standard, until the Internet "police" provide all of us with one set of rules that we all have to comply with we will continue to fight the battle of not only spam but also the differing opinions on how these lists should be handled.
If these companies want to set rules, why not use SPF (Sender Policy Framework) to set these rules. SPF has been in place for a long time and has been a recommended standard. We are working towards SPF records for all of our mail servers and hope to have all SPF records completed within the next week. Will this be enough to satisfy the "big brothers"? We are also setting up RDNS records for our customers mail servers that we are aware of. Will this be enough? I am all for blocking computers, mail servers or home computers that are identified as sending legitimate spam. If one of our devices is spamming, I block it on our network before it ever gets to yours.
The frustrating thing about all of this is that I know that these companies are making big bucks selling a product to their customers that will break the customers ability to receive email. Are these companies explaining that to the customers? Obviously not. The folks emailing our customers expecting a response from our customers don't have a clue that it is their "filter" that is preventing the delivery of the email. It is this Handlers opinion that we will all really need to take a step back and learn to work TOGETHER to resolve the spam problem without causing more issues for an already stressed business community.
Deb Hale Long Lines, LLC
13 Comments
Twitter outage via DNS hijacking
A number of diary readers have submitted that the popular micro blogging site, Twitter.com has been defaced this morning.
The twitter.com status page has the following report:
If we receive any more information concerning the outage, or how the hijacking occured, we shall update the diary during the day. If you have any additional information, please let us know via the contact form.
Update: The following screen grab shows the DNS hijacking as recorded via the PassiveDNS systems. The host www . mowjcamp . org is currently hosting the defacement.

Steve Hall
5 Comments
In caches, danger lurks
When ISC reader Greg searched for a particular piece of information, and found the site hosting the information currently down, he reverted to Google Cache to retrieve the info from there.
But .. the site was apparently down for a reason: They were cleaning up a malware infection, and the infected pages were of course already duly mirrored in the ever effective Google cache, complete with all the hidden iframes leading to yet another unsolicited "Anti Virus" tool.
A cache, being a mirror image of the real world, can be expected to reflect that world in all its badness. Nevertheless, users would probably assume that the content comes from the search engine provider, and pay (even) less attention than normal to what happens next.
The badware is currently delivered through the domain todolust-dot-com. The EXE changes about twice per hour, and has very low AV coverage (Virustotal). Microsoft and Sunbelt are currently the only two AV tools on Virustotal that do not seem to be perturbed by the rapid morphing of the EXE, and keep catching it reliably.
2 Comments
overlay.xul is back
It's been a while. If I remember correctly, a variant of Vundo was using the "overlay.xul" mechanism to hi-jack searches in the Firefox browser almost a year ago. Now, ISC reader Tom contacted us with a mystery that took him and his colleagues several days to unravel. The symptoms: You try to search with Google/Yahoo/Ask/Bing, but NoScript (a great add-on!!) warns you that the browser is actually trying to run a JavaScript from innoshots-dot-org. Having checked all the usual culprits, and run all the Anti-Virus tools you have, you find: Nothing. And the browser still redirects.
overlay.xul is a Firefox mechanism to allow applications to add elements to the browser GUI, and is used for good effect by several tools. We don't know which infection vector was used in Tom's case to deposit the malicious overlay file on the machine. All we have is the file, and the knowledge that it apparently either resides in
Documents and Settings/user/Local Settings/Application Data/{randomstring}/chrome/content -- or --
Program Files/Mozilla Firefox/extensions/{randomstring}/chrome/content
and is accompanied by a suspicious Javascript file called _cfg.js.
overlay.xul contains heavily obfuscated JavaScript, and has nice copyright headers to make it look like a valid Firefox add-on, but the "smoking gun" is still visible in the lower portion of the file:
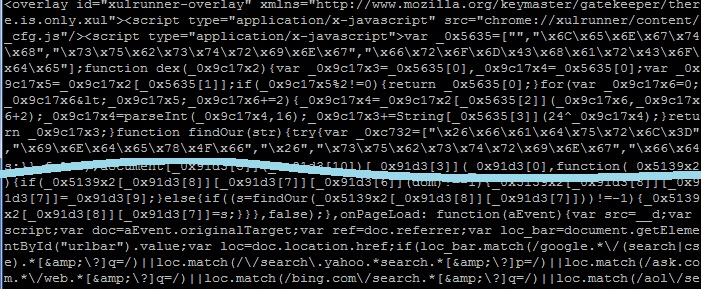
Yup. Some sort of matching for "google", "ask", "yahoo", "aol" and "bing" is going on here. This particular sample of "overlay.xul" is almost a month old, and yet there are still some very prominent Anti-Virus products that do not see anything wrong with it: Virustotal
Did anyone else notice a recent resurgence of "overlay.xul" and its search engine redirection malware? If you have a sample, or know anything about the mechanism this latest version uses to get onto the system, please let us know.
Note: overlay.xul also has good uses, so don't go for a frantic deletion rampage now. But take a careful and suspicious look at the files you find!
0 Comments
Cisco WebEx WRF Player Vulnerabilities
Cisco today released details of a set of buffer overflow vulnerabilities and fixes for their WebEx WRF player. The exploits describe multiple buffer overflows caused by a maliciously crafted WRF file (generally posted on a website), or by attending a WebEx meeting with an attacker attending. The results of the exploit can result in execution of arbitrary code on the target system.
The exploits are categorized as: CVE-2009-2875, CVE-2009-2876, CVE-2009-2877, CVE-2009-2878, CVE-2009-2879 and CVE-2009-2880.
The WebEx site itself has the fixed client code. If you have an inhouse WebEx server, updating the server updates all the clients (as they connect). You won't find an easier to install fix than this one!
From the Cisco advisory, the "first fixed" releases are listed below, by Major Release and Client OS. All versions subsequent to these are fixed as well.
|
Platform |
Major Release 26.x |
Major Release 27.x |
|
Microsoft Windows |
26.49.32; available now except lockdown sites |
27.10.x; available now for non-PSO and non-lockdown sites |
|
Mac OS X |
26.49.35; available early February 2010 |
27.11.8; available now for non-PSO and non-lockdown sites |
|
Linux |
26.49.35; available early February 2010 |
27.11.8; available now for non-PSO and non-lockdown sites |
The full cisco advisory is here ==>
http://www.cisco.com/warp/public/707/cisco-sa-20091216-webex.shtml
1 Comments
Beware the Attack of the Christmas Greeting Cards !
With the holiday season upon us, lots of folks (me included) have elected to send online greeting cards instead of using traditional paper cards, "saving" the carbon and emissions footprint involved in traditional mail services (not that email is carbon free or anything, but that's a whole other discussion).
Just a word of warning - as happens every year, fake greeting cards are being circulated via email, with malware payloads attached. We got our first reader email on this today, Daniel received a greeting card with a ".net" at the tail end of a legitimate domain. The attackers even went to the trouble of making their site look like the real one! These attacks use more sophisticated phishing techniques every year, and the malware payloads are of course also more difficult to detect each time.
So if you get a greeting card, even if it's from someone you know, be sure that the link you click is taking you where you expect to go. Check that the link is to a reputable greeting card site, and that it doesn't have "extra" characters at the end, that would indicate you are going someplace else entirely. Even better, "don't click that link!" - copy and paste it into your browser rather than clicking it directly, that way you have that much more assurance that you know where you are browsing to.
Have a safe, malware-free holiday everyone !
0 Comments
Important BIND name server updates - DNSSEC
Over the first half of 2010, ICANN/IANA plan to sign the root zone [1]. The DNSSEC signature will use SHA256 hashes, which are not supported in older but common versions of BIND. If you run BIND 9.6.0 or 9.6.0P1, you may have issues with these signatures. The bug was fixed in BIND 9.6.1.
From the ISC.org mailing list:
ISC has arranged for two test zones to be made available which are
signed using the new algorithms which are listed in dlv.isc.org.
You can test whether you can successfully resolve these zones using the
following queries.
dig rsasha256.island.dlvtest.dns-oarc.net soa
dig rsasha512.island.dlvtest.dns-oarc.net soa
[1] http://www.icann.org/en/announcements/announcement-2-09oct08-en.htm
[2] https://www.isc.org/software/bind/dnssec
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
0 Comments
Adobe 0-day in the wild - again
Update1: One of the samples that we had access shows the following behavior that could help you to identify infections in your network/system:
The exploit has the executable included: AdobeUpdate.exe - Size 9.356k (hash 069175846447506b3811632535395bc3 ).
This executable will download another file called ab.exe (and save it as winver32.exe on C:windows folder). You may also check your logs for the website hxxp://foruminspace.com . This file is hosted there.
The current sample has the following specs: Size 386,016k and hash 686738eb5bb8027c524303751117e8a9 .
-------------------------------------------------
Handler on Duty: Pedro Bueno (pbueno //&&// isc. sans. org)
Twitter: twitter.com/besecure
--------------------------------------------------------------------------------------------------------------------------------------------------------------------------
It's not ground hog day, but it surely feels like it. The Shadowserver Foundation [1] is reporting about spotting another Adobe 0-day in the wild
Adobe acknowledged the issue in a PSIRT post [2].
The quick summary: The is currently no patch available and commonly used anti-virus products appear to be mostly missing it. The bug requires JavaScript. Turning off JavaScript support appears to be your best defense. I could recommend that you don't open any malicious PDFs. But it would probably be as useful to go and hide in a cave until all Adobe bugs got fixed.
Please let us know if you find any malicious PDFs like this, and let the Adobe PSIRT know as well.
[1] http://www.shadowserver.org/wiki/pmwiki.php/Calendar/20091214
[2] http://blogs.adobe.com/psirt/2009/12/new_adobe_reader_and_acrobat_v.html
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
10 Comments
Anti-forensics, COFEE vs. DECAF
Recently was told by a reader about anti-forensics efforts to stimy a Microsoft produced digital forensics set of tools called COFEE. Computer Online Forensic Evidence Extractor (COFEE) is mainly designed as a first responder data collection tool for Law Enforcement to run on a live Windows system. The data collected can be analyzed back at the lab by more technical staff. The system could then be powered off and presumably a disk image could be taken without all of the volatile forensic data being lost. Detect and Eliminate Computer Assisted Forensics (DECAF) is specifically designed to delete, deny access, or obfuscate the evidence that COFEE would try to obtain. Anti-forensics isn't particularly new. In the physical world it has existed since before Sir Conan Doyle's time. In the digital world, where forensics is arguably is much newer and less developed science the active destruction of evidence or forensic counter-measures are also somewhat new. DECAF monitors for the use of or introduction of COFEE, performs predetermined actions, and otherwise obstruct access to digital evidence. Interesting stuff. At this time illegal copies of COFEE appear to be available for download. DECAF is available from its web site. Both are rather easy to find using your search engine of choice.
I prefer green tea.

Thanks for writing in Paul!
Cheers,
Adrien de Beaupré
Intru-shun.ca Inc.
6 Comments
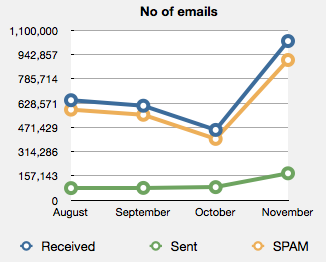
Metrics and SPAM
|
|
Like all good security people I regularly look at different metrics to see what is going on in the environment. Usually this is a bit of a ho hum task, but every now and then you do come across something interesting. I find it helps to graphically represent the information as abnormalities often jump out at you which otherwise might not be as obvious. Take the graph on the left. This represents the SPAM traffic received in a month. August and September are fairly steady a noticeable drop in October in email received and then, Whoa! What is going on in November? Email messages received increased by more than 100% and the yellow line shows that the majority is SPAM. It is not exactly parallel to the received line so either normal mail increased as well or more SPAM was missed by the tool used to block SPAM. Both are worth investigating further. Metrics, especially visualised metrics, can be very effective in identifying whether you need to jump and fix something or whether it is business as usual. |
Now all of you use some form of metrics in your organisation for security and I can guarantee that others are looking for useful metrics that they can apply in their environment. So if you are using a nifty metric that is easy to obtain and you are willing to share with the rest of us let us know.
(On a second note, if you SPAM increased by similar numbers in November, I'd be interested as well)
Mark H - Shearwater
8 Comments
Microsoft Update providing 403 error code?
We've had two separate reports this morning from readers telling us, when they try to visit the Microsoft Update site (for XP or 2003) they are receiving 403 error messages. One of the emails we received details having to remove MS Update and reinstall it in order to get updates to work again.
Can anyone else replicate this issue? We've tried from several locations globally and we can't reproduce the problem.
-- Joel Esler | http://blog.joelesler.net | http://twitter.com/joelesler
24 Comments
Another good reason to update to Thunderbird 3.0
One of our readers sent this in to us (Thanks Juha-Matti), a security advisory against versions of Thunderbird <= 2.0.0.23.
Aside from all the other good reasons to update to Thunderbird 3.0, this is a vulnerability in Thunderbird's dtoa implementation. Many Thunderbird users like to integrate things like Lightning (the calendar application) right into their Mail client, similar to Outlook. This tight integration allows for much the same functionality that Outlook has in it's mail client, except for the Exchange server portion. I've seen Thunderbird and Lightning used at countless organizations to be able to handle calendars, so be sure and pay attention to this one.
The flaw, according to the link, is in how Thunderbird's dtoa implementation works. Since Thunderbird uses the same dtoa implementation as Firefox, one would tend to think that Firefox (and it's variations, Camino..etc) would be vulnerable too.
This would affect many plugins as well, things like Lightning (as previously mentioned) and Thunderbrowse (as mentioned it the link above). Who knows what else, so make sure and update everything that you can.
-- Joel Esler | http://blog.joelesler.net | http://twitter.com/joelesler
0 Comments
Facebook Password Reset Confirmation. Customer Support. (Malware)
I received an email today purporting to be from Facebook, which of course had an attachment. The file was Facebook_Password_833fd.zip, which unzipped to be Facebook_Password_833fd.exe. The zip file is in fact a zip file, and the exe is in fact MS-DOS executable PE for MS Windows (GUI) Intel 80386 32-bit (according to the file command). The subject line is "Facebook Password Reset Confirmation. Customer Support. " The body of the email is pretty straight forward:
"Hey email,
Because of the measures taken to provide safety to our clients, your password has been changed.
You can find your new password in attached document.
Thanks,
Your Facebook."
Which is an attempt to get you to first open the attachment, unzip the file, and then run the executable content. The executable has the following attributes:
File size: 27648 bytes
MD5 : 11dee2f7ecc31a9a6f5fcab4e9654073
SHA1 : 30cfe72393ca5c58e7bba452c401932c6dcc9a9f
First set of Virustotal results were 20/41 today at 01:30:12 (UTC) https://www.virustotal.com/analisis/af6abaa7d0a29cdd4cf2680771d6d87e22d190a6a293572910ab89bd0653b322-1260408612 when I ran it again at 17:49:06 (UTC) they were up to 26/41 detection. It is a dropper which subsequently downloads and executes other badness.
Facebook does not send out passwords in attached files. If you have forgotten your password on Facebook reset it here: http://www.facebook.com/reset.php if you cannot login to your account (someone else has taken it over) go to this page: http://www.facebook.com/help.php?topic=login, which also has this advisory on it:
Some users have received fake password reset emails with attachments that contain viruses. Do not click on these emails or download the attachment. Also, please note that Facebook will never send you a new password as an attachment. To learn more visit our Security page: facebook.com/security"
Cheers,
Adrien de Beaupré
Intru-shun.ca Inc.
2 Comments
Facebook announces privacy improvements
Facebook, one of the largest social networking sites and somewhat notorious on the privacy front, has been working on a turn about of their privacy approach.
Last week there was a message from the founder Mark Zuckerberg referencing earlier trials with improved tools and settings and stating:
The plan we've come up with is [...] to create a simpler model for privacy control where you can set content to be available to only your friends, friends of your friends, or everyone.
We're adding something that many of you have asked for - the ability to control who sees each individual piece of content you create or upload. In addition, we'll also be fulfilling a request made by many of you to make the privacy settings page simpler by combining some settings. If you want to read more about this, we began discussing this plan back in July.
A press release was made today accompanied by a blog post highlighting:
- Adding Control For Each Item
- Simplified Privacy Settings
- Help In Choosing Settings
- Expanded Privacy Education
Privacy settings can be reached on: http://www.facebook.com/privacy/ it still feels quite complex to a casual user like myself, but adding more control is a good thing. Now onto getting security for the information you post online by default I guess.
--
Swa Frantzen -- Section 66
1 Comments
OSSEC 2.3 released
OSSEC 2.3 was actually released a few days ago, but a careful reader pointed out we had not covered it yet.
From the announcement: What's New?
- Log analysis rules for the Nginx web server
- Log analysis rules for Suhosin (Hardened PHP)
- Support for real time file integrity monitoring on Windows systems
- Support for monitoring the output of commands (process monitoring)
The Changelog has more detailed coverage of the changes.
--
Swa Frantzen -- Section 66
0 Comments
ntpd upgrade to prevent spoofed looping
Martin wrote in to point to VU #568372. It contains a description of a vulnerability (CVE-2009-3563) in the ntpd.org reference implementation of ntpd, which will sound very familiar for any dog owner seeing his pet chase it's own tail. Basically all that's needed is a single spoofed packet to set of ntp daemons to start endlessly sending messages to themselves or to each-other.
Filtering in the short term is a possible workaround, but upgrading your ntp software to at least version 4.2.4p8 is a far better long term strategy.
Note that this software is often embedded in various devices and operating systems, so upgrading it might take a bit of effort in tracking it all down.
--
Swa Frantzen -- Section 66
0 Comments
Adobe flash player and air patched
The almost universally installed flash player of adobe has been update to version 10.0.42.34. Adobe air as upgraded to 1.5.3.
Read more about it in the apsb09-19 bulletin from adobe.
The reason behind it are 7 vulnerabilities: CVE-2009-3794, CVE-2009-3796, CVE-2009-3797, CVE-2009-3798, CVE-2009-3799, CVE-2009-3800 and, CVE-2009-3951 of which 6 lead to arbitrary code execution and the last one is a windows only issue leading to unauthorized information disclosure, related to CVE-2008-4820.
"Upgrade!" is the loud and clear message should our audience need that encouragement.
At this point we have no guidance for users wishing to know more about version 9 of the flash player aside of considering an upgrade to latest incarnation of version 10.
Thanks for the heads up go to David and Andrew
--
Swa Frantzen -- Section 66
2 Comments
December 2009 Black Tuesday Overview
Overview of the December 2009 Microsoft patches and their status.
| # | Affected | Contra Indications | Known Exploits | Microsoft rating | ISC rating(*) | |
|---|---|---|---|---|---|---|
| clients | servers | |||||
| MS09-069 | Remote code execution vulnerability could allow denial of service if a remote, authenicated attacker sends a specially crafted ISAKMP message while communicating through IPSEC to LSASS. (Replaces MS09-025) | |||||
| LSASS CVE-2009-3675 |
KB 974392 | No known exploits. | Severity:Important Exploitability: 3 |
Important | Important | |
| MS09-070 | Multiple vulnerabilities allow remote code execution if an attacker sent a specially crafted HTTP request to an ADFS-enabled Web Server. | |||||
| ADFS CVE-2009-2508 CVE-2009-2509 |
KB 971726 |
No known exploits. | Severity:Important Exploitability: 3,1 |
N/A | Critical | |
| MS09-071 |
Authentication Bypass Vulnerability in MS-CHAP and memory corruption (code execution) |
|||||
| Internet Authentication Service CVE-2009-2505 CVE-2009-3677 |
KB 974318 |
No known exploits. | Severity:Critical Exploitability: 2,3 |
N/A | Critical | |
| MS09-072 | Multiple vulnerabilities allow remote code execution if a user views a specially crafted web page using Internet Explorer. Higher risk with Higher user rights. Replaces MS09-054. |
|||||
|
Internet Explorer |
KB 976325 | CVE-2009-3672 known. | Severity:Critical Exploitability: 1,1,1,1 |
PATCH NOW | Important | |
| MS09-073 |
Remote code execution vulnerability if a specially crafted file is opened in WordPad or Microsoft Office Word a user could gain the same privileges as the logged in user. |
|||||
| WordPad and Office Text Converters CVE-2009-2506 |
KB 975539 | No known exploits. | Severity:Important Exploitability: 2 |
Critical | Important | |
| MS09-074 | Remote code execution vulnerability if a user opens a specially crafted Project file allowing the attacker to take complete control of the afftected system. Replaces MS08-018. |
|||||
| Microsoft Office Project CVE-2009-0102 |
KB 967183 |
No known exploits. | Severity:Important Exploitability:2 |
Critical | Important | |
We appreciate updates
US based customers can call Microsoft for free patch related support on 1-866-PCSAFETY
- We use 4 levels:
- PATCH NOW: Typically used where we see immediate danger of exploitation. Typical environments will want to deploy these patches ASAP. Workarounds are typically not accepted by users or are not possible. This rating is often used when typical deployments make it vulnerable and exploits are being used or easy to obtain or make.
- Critical: Anything that needs little to become "interesting" for the dark side. Best approach is to test and deploy ASAP. Workarounds can give more time to test.
- Important: Things where more testing and other measures can help.
- Less Urgent: Typically we expect the impact if left unpatched to be not that big a deal in the short term. Do not forget them however.
- The difference between the client and server rating is based on how you use the affected machine. We take into account the typical client and server deployment in the usage of the machine and the common measures people typically have in place already. Measures we presume are simple best practices for servers such as not using outlook, MSIE, word etc. to do traditional office or leisure work.
- The rating is not a risk analysis as such. It is a rating of importance of the vulnerability and the perceived or even predicted threat for affected systems. The rating does not account for the number of affected systems there are. It is for an affected system in a typical worst-case role.
- Only the organization itself is in a position to do a full risk analysis involving the presence (or lack of) affected systems, the actually implemented measures, the impact on their operation and the value of the assets involved.
- All patches released by a vendor are important enough to have a close look if you use the affected systems. There is little incentive for vendors to publicize patches that do not have some form of risk to them
3 Comments
Layer 2 Network Protections – reloaded!
So Rob, you say, aren’t we done talking about protecting switches and the like at Layer 2 yet? We talked about Man in the Middle Attacks in October, and Layer 2 remediation against Man in the Middle Attacks in November, that should cover it, right?
The short answer is “no” – we haven’t talked about Broadcast control or MAC address flooding yet !
Broadcasts are part of everyday life on most networks – they’re necessary for most networks to operation. ARP and DHCP are both a great examples of protocols that use broadcasts for different reasons. However, the problem with broadcasts is that they are received by every station on the subnet, each station has to actually read at least the packet header to then determine that the packet is or isn’t for them, then discard it if it’s not theirs. This takes up a very small but measurable amount of CPU. It's this CPU useage that gives broadcasts their bad name.
So what level of broadcast traffic on a network is “reasonable”? A Cisco paper that I often refer to (http://www.cisco.com/en/US/docs/internetworking/design/guide/nd20e.html ) indicates that at 1,000 broadcasts per second, you can expect to lose on average roughly 1% CPU per host. Now considering the age of this document (it references 25MHz 386 processors), you can see that we can probably go much higher than that these days. But at 1,000 broadcasts per second, you've probably either got a very (very) large subnet, or some other problem that should be addressed !
So, when can you see broadcast floods? In most cases, seeing more than 2-3 broadcasts per minute from any one host would be high. But you absolutely will see higher rates – for instance, as a workstation logs in, it will send DHCP requests for an IP address, then ARP requests for it’s DNS server, gateway, Domain Controller (if it’s a windows host), as well it will also ARP for the IP address of each host it has a resource (or share) on. This can really add up !
We can see higher broadcast levels when a station is running a recon tool. For instance, initiating an nmap scan on a local subnet initiates a broadcast flood (one ARP request per ip address in the subnet range).
I’ve seen broadcast floods during testing of new network gear as well, usually by engineer-types. For instance, in one case we saw engineers developing new ip cameras generate enough broadcasts per second that it overflowed the capture buffer in wireshark on my laptop. For political reasons we couldn’t move them (or their tests) off the production, so we changed their VLAN and implemented broadcast control (see below) to limit their impact on the production networks.
If you run "real" video servers on your network, you'll likely see higher levels of broadcast (or more likely multicast) traffic originating from them. You'll need to consider the switch ports for these servers in detail if you are configuring broadcast control on your switches.
MAC Address flooding is different than broadcast flooding - a MAC address flood occurs when a station sends traffic from several different MAC addresses (stations generally only have 1 MAC address each). Virtual switches on platforms like VMware, XEN or Hyper-V will source traffic from multiple MAC addresses (their own, plus one per virtual machine),and clusters and load balancers will also "play games" with MAC addresses. But aside from these, you won’t normally see single hosts with multiple MACs in real life, it’s generally a malicious thing. What you will see in real life though is unmanaged switches under people's desk, with 3-4 PCs each plugged into them. Or classrooms with unmanaged switches, hosting 24 or more PCs. (you see the pattern here)
Tools like macof (part of dug song’s most excellent dsniff suite) can be used to generate mac address floods. The purpose of MAC Address floods is to overflow the MAC Address table (or CAM table, depending on your switch vendor and model). The MAC Address table relates mac addresses to switch ports, and since this table is stored in memory on the switch, it will have a fixed maximum size. What happens on a switch when the mac address table is full will vary. Once the CAM table is full, all existing mac entries behave as before, but new MAC addresses are "new", so requests for them are flooded to all ports as part of the normal learning process. So under a sustained attack, a MAC address flood will essentially turn your expensive switch into a cheap hub, and all traffic will be visible to your attacker. Since macof can generate in excess of 15,000 MACs per second, it's not a tough attack to carry out. In older or less robust switches, the switch may crash, so if you are experimenting with these tools, it's best to do it on a test network.
REMEDIATION:
Remediation against broadcast floods is simple. At a macro level, an alternative definition for a VLAN is “broadcast domain”. Since broadcasts are a layer 2 phenomena (aside from helper addresses and directed broadcasts), VLANs are a good way to limit the scope of broadcasts. So if you have devices that generate higher levels of broadcast traffic, you can put them in their own VLAN to at least contain the offending traffic.
Broadcasts are commonly controlled at the port level with “storm control” commands. These commands generally limit broadcast traffic to a configured number of packets per second. On some switches, the limit is on a percentage of interface bandwidth metric, so “0” blocks all broadcasts, and 100 imposes no limits at all. Multicast and true broadcast packets can usually be limited separately.
Remediation against MAC address floods is also very easy. “Port security” commands restrict how many MAC addresses can appear on a single Ethernet port. Similar to broadcast control, you can set the level of how many MAC addresses are permitted on each port, and also you can configure what happens when you exceed the limit.
A violation of either port security or broadcast storm control settings will by default place the offending Ethernet port in an “errdisable” state. Again, by default, the port will stay in that state, unusable, until you reset it. You can set a timer and recovery options on a port with the “errdisable recovery” commands. Recovery options can usually be set separately for each error type. So you might allow automatic recovery from a broadcast storm after 30 seconds, but force manual intervention to recover from a MAC address flood.
Again, note that anyone with a cheap switch or hub under their desk, with 2-3 PCs attached to it can easily trigger port security, shutting down the entire uplink for their whole switch. We’ve also seen classrooms with unmanaged 24 or 48 port switches in this situation. You’ll want to either eradicate hubs and switches like these, or at least identify where they are and set your metric high enough on those ports so that you don’t shut down their uplinks.
Before you implement these remediations - do your homework !! Both of these commands will disable ports when triggered, so read your vendor documentation and know your network before you go live! If you are in doubt, having violations trigger alerts rather than disable ports is usually a safer approach, at least until you know where you have problems you need to fix, and where you need to grant exceptions to the rules.
0 Comments
Cheat Sheet: Analyzing Malicious Documents
Today was a calm day at the ISC, so I had some time to catch up on some backlogged email. One of the items I came across is a cheat sheet to assist with Analyzing Malicious Documents. This is another in the excellent series of cheat sheets by fellow handler Lenny Zeltser, with input from others, including a number of ISC Handlers. These are excellent guides and I highly recommend them to anyone who is interested in malware analysis or other aspects of Information Security.
Also off of Lenny's cheat sheet page are links to a number of other InfoSec related cheat sheets published by others in the security industry. All of this content is distributed under the Creative Commons v3 "Attribution" License.
Enjoy!
-- Rick Wanner - rwanner at isc dot sans dot org
0 Comments
Java JRE Buffer and Integer Overflow
Sun acknowledged that multiple buffer and integer overflow vulnerabilities exist in the Java Runtime Environment with processing audio and image files may allow an untrusted applet or Java Web Start application to escalate privileges. The advisory was posted here.
Handler Mark Hofman posted a onliner on 3 Dec 2009 on the released of an Apple Java update APPLE-SA-2009-12-03-1 & 2 (for 10.5 and 10.6) that fixed a number of issues. Sun had released a Java update for all platforms (Windows, Solaris and Linux), it is a good time to patch for this vulnerability because exploit code has been made public. For now, browsers on unpatched systems will crash but that could soon change.
You can find the Windows, Solaris and Linux update here.
You can find the Apple update here.
Si tu veux assister au cours SANS SEC 503 en français en mai 2010 à Nice, France, suis ce lien.
----------- Guy Bruneau IPSS Inc. gbruneau at isc dot sans dot org
0 Comments
The economics of security advice (MSFT research paper)
A new research paper by Microsoft examines the economics of "security advice" and how users react to password rules, phishing URLs and certificate errors. Their conclusion on password rules is similar to the one that we discussed here in the SANS ISC diary a couple weeks ago.
0 Comments
Max Power's Malware Paradise
Who Max Power is? Well, we don't know either. It's a pseudonym of a gang or guy who has a decent-sized spyware racket going. Max has been sitting on the same IP address for the past three months, 210.51.166.119, in AS9929. ChinaNet. Even Google knows that 10% of the sites in this AS are malicious.
Looking at the IP address in Reverse DNS or MalwareURL.com, we can see the many malware domains "Max Power" has been using in the recent past. Some of the names are associated with the Koobface and Zeus malware families. The address lay dormant for the last week of November, but just woke up again yesterday morning, and is currently serving the malware domain "tempa3-dot-cn". This domain is at the moment linked to from various questionable "pharmaceuticals" web sites, and it currently pushes a bunch of exploits which, if successful, download and run a backdoor of the "TDSS"/"Tidserv" family. Detection was dismal at first, but has improved a bit over the last 24 hours.
4 Comments
Avast false positives
We have received a number of reports of Avast Antivirus false positives (Thanks Ken, Don, Luca & others). With a recent update the Avast antivirus product have started identifying legitimate products as containing Win32-Dell-MZG. The Avast forum is awash with some of the products that have been tagged, many of which are known to be good and have been functioning quite normally.
The recommendation at the moment is to not reply delete or quarantine files as this may fry the product they belong to (a few readers are currently reinstalling applications). As far as we know the files are consistently identified as Win32-Dell-MZG so if others pop up there is a fair chance that these are legit.
Mark
Update
A new update was released fixing the issue. 091203-1. If you haven't used your computer between 12:00am UTC and 5.50 am UTC, then you will receive the new update and you should be fine. For those that were affected I recommend you keep an eye on the Avast blog http://forum.avast.com/index.php?topic=51647 as they are working on some how to's to help fix any issues.
2 Comments
SPAM and Malware taking advantage of H1N1 concerns
Gary writes in, telling us of a recent spike in SPAM with a title similar to "“State Wide H1N1 Vaccination Program", which pretends to originate from the CDC (Center for Disease Control). The email goes on to instruct you to "follow this link to create a vaccination profile on the CDC website".
Needless to say, this email is a fake, it redirects you to a site in the Ukraine, and plants malware on your PC. The URL is "http://online.cdc.gov, followed of course by the real domain name, six or seven digits of seemingly random characters.
You do not need to register with the CDC to receive a vaccine for the H1N1 strain of influenza
There's also a rise in fake H1N1 sites using other vulnerabilties to compromise your PC, including the recent Adobe issues.
It never ceases to amaze me the depths that these "malware folks" will stoop to.
If you are following a link in your email - always check to see that it's taking you where you think you are going before you click it. Copy and paste it through your clipboard, or rekey the link entirely in your browser. This kind of deception is just so prevalent that clicking links in a received note is simply not safe!
1 Comments
Updates to Sysinternals Toolkit
Roseman tells us of updates to the popular Sysinternals toolkit. This round includes updates to the utilities: VMMap, Disk2vhd, Sigcheck, Autoruns, PsExec and PsKill.
The Disk2vhd update is the one I find most interesting - they've updated it to fix the kernel and HAL during the migrate, to make migrated VHDs bootable in Virtual PC. This has been around forever in VMware's P2V and newer versions of the same tool, I'm glad to see this function available on other virtual platforms!
Disk2vhd also allows you to skip sectors with CRC errors, which gives you a shot at recovering failing physical disks by migrating them to virtual - this feature is a really helpful one !
Find more information here ==> http://blogs.technet.com/sysinternals/archive/2009/12/01/updates-vmmap-v2-5-disk2vhd-v1-4-sigcheck-v1-63-autoruns-v9-57-psexec-v1-97-pskill-v1-13-and-a-new-windows-internals-session-video-from-mark-at-pdc-2009.aspx
0 Comments
Microsoft Black Screen of Death - Fact of Fiction?
We've had a lot of interest in the drama unfolding around Prevx's announcment on Nov 27 that they had found a "Black Screen of Death" issue that they had researched - you can find their initial post on this issue here ==> http://www.prevx.com/blog/140/Black-Screen-woes-could-affect-millions-on-Windows--Vista-and-XP.html
The title of their blog indicates that this could affect "millions of Windows 7, Vista and XP stations". Prevx's root cause post on dec 1 ( http://www.prevx.com/blog/141/Windows-Black-Screen-Root-Cause.html ) fleshes this out further, indicating that that one of the recent Microsoft patches, either KB915597 and/or KB976098 seemed to modify the ACLs on a registry key that in turn denies local users the right to view their own desktop, which results in the "black screen" symptom.
This is a well known and long-standing symptom - you can deny users access to their own screen by changing the ACLs on the registry key HKEY_LOCAL_MACHINESoftwareMicrosoftWindows NTCurrentVersionWinlogonShell . This isn't a problem on it's own, it's part of the overall design of Windows - I can think of a few cases where this might be a useful thing in fact.
Anyway, on to the drama: Microsoft also posted on Dec 1 ( http://blogs.technet.com/msrc/archive/2009/12/01/reports-of-issues-with-november-security-updates.aspx ) - they had a few important points:
- They've reviewed all of their recent updates - they simply do not change this ACL
- They are not receiving millions of calls - this can't be affecteding millions of systems
- Prevx went straight to press without involving Microsoft
I'd echo Microsoft on this one (on all 3 points actually) - we simply aren't seeing any widespread "black screen" issue.
Prevx has posted a final blog entry today ( http://www.prevx.com/blog/142/Windows-Black-Screen-recap.html ). They're now agreeing with Microsoft, that the black screen issue that they've seen appears to have some cause unrelated to the Microsoft updates. I can see how this might be an easy mistake to make, especially if you are researching several issues on one machine or VM image.
The thing I find most interesting in this cyber-opera is the number of posts that we're seeing on other sites that took the original post as truth without doing any check at all. I realize people are busy and everything, but a little bit of fact-checking goes a long way ....
So to recap - the "Black Screen of Death" is in fact a real thing, but it's not a recent thing, and you won't be seeing it as a result of applying any of the Microsoft patches to date. It's still recommended to keep your Windows systems (and any other systems for that matter) as up to date as possible with vendor updates.
1 Comments
Vulnerabilities in the PDF distiller of the BlackBerry Attachment Service
Brian and Francois let us know about a new vulnerability in the PDF distiller of the BlackBerry Attachment Service for the Blackberry Enterprise Server.
"
The RIM announcement can be found here, and a brief US-CERT announcement is posted here.
Christopher Carboni - Handler On Duty
1 Comments
Clientless SSL VPN products break web browser domain-based security models
Matt sent a note pointing to a new advisory issued by US-CERT
"By convincing a user to view a specially crafted web page, a remote attacker may be able to obtain VPN session tokens and read or modify content (including cookies, script, or HTML content) from any site accessed through the clientless SSL VPN. This effectively eliminates same origin policy restrictions in all browsers. For example, the attacker may be able to capture keystrokes while a user is interacting with a web page. Because all content runs at the privilege level of the web VPN domain, mechanisms to provide domain-based content restrictions, such as Internet Explorer security zones and the Firefox add-on NoScript, may be bypassed."
The complete advisory can be viewed here.
Christopher Carboni - Handler On Duty
0 Comments



2 Comments