Analysis of PDFs Created with OpenOffice/LibreOffice
From time to time, I get a question about PDFs that have an /OpenAction, but don't seem to contain (malicious) code.
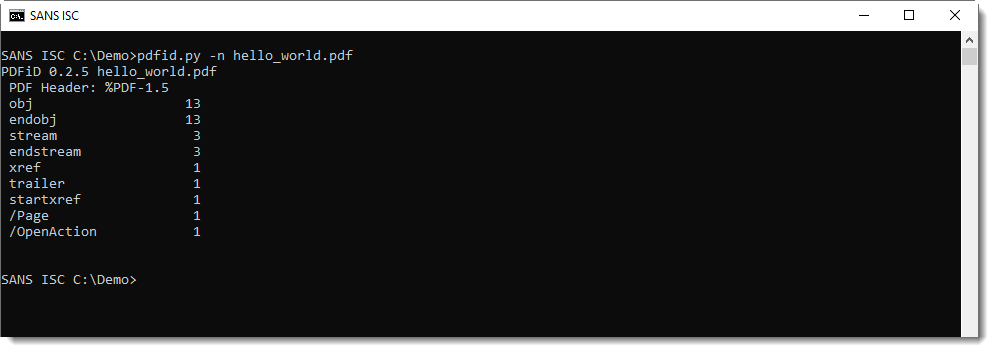
When you look at such a PDF with pdfid.py, everything looks OK, except that there is an /OpenAction:
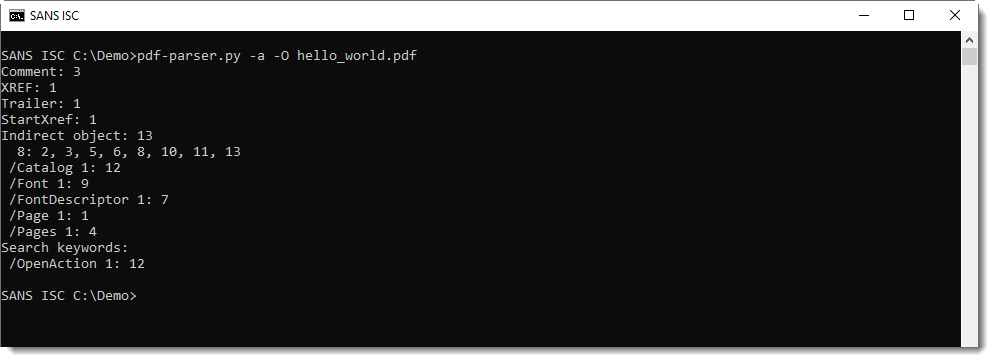
You can also find search keywords like /OpenAction using pdf-parser.py's statistics option (-a). Best is to combine this with option -O to look inside stream objects, should they be present:
The /OpenAction is in object 12:
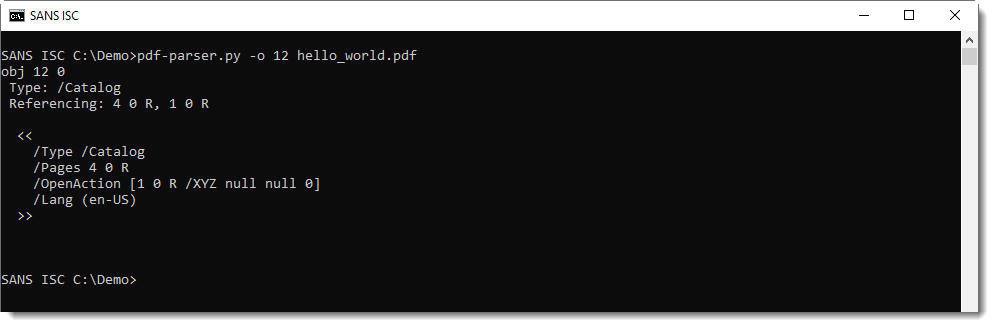
This /OpenAction is typically added by OpenOffice and LibreOffice when creating a PDF document. Its purpose is to present the first page when you open the document for the first time. This is called an Explicit Destination.
/OpenAction here is not used to execute JavaScript code upon opening of the PDF (as is often the case with malicious PDFs), but it is used to present the first page with the desired position and zoom. This is explained in the PDF reference documents:
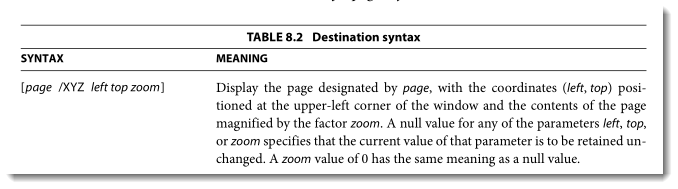
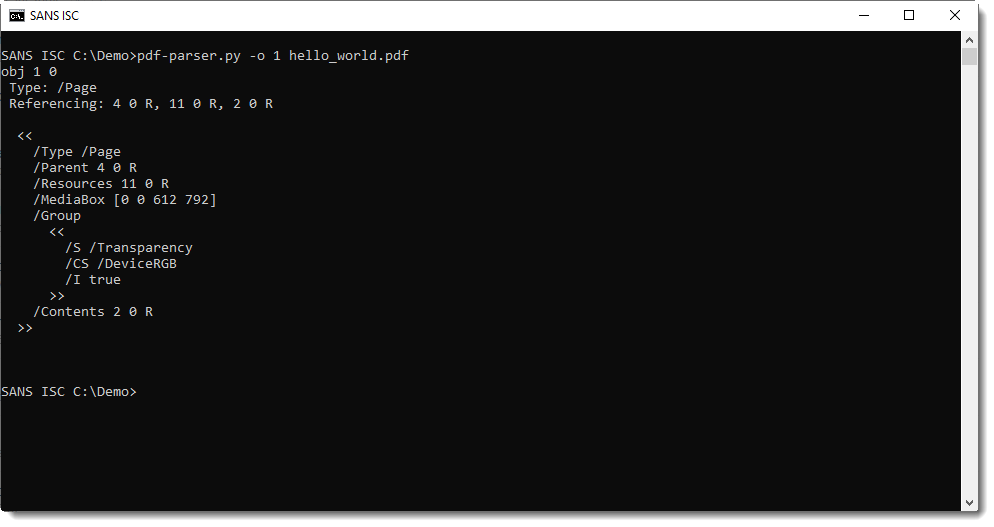
This explicit destination refers to object 1: this is a page:
When you encounter a document like this, it's most likely not malicious. Should you suspect that this is targeted, then you could continue your analysis as explained in diary entry series "It is a resume", for example. A targeted attack might use a more sofisticated exploit, without any of the signs reported by pdfid or pdf-parser's statistics. But it's very unlikely to find this in common maldocs.
Here is a video for this quick analysis:
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments