January 2017 Microsoft Patch Tuesday
If your job today is to apply Microsoft patches: You get to go home early today! I think this is the lightest patch Tuesday ever.
Microsoft today released 3 bulletins itself plus one for Adobe. While two of the vulnerabilities are "publicly known", they only affect non-critical updates: A privilege escalation vulnerability in Microsoft Edge (CVE-2017-0002) and a denial of service vulnerability in LSASS (CVE-2017-0004). For the first time in a many many months there is no Internet Explorer update this month.
You can find all the details again via our MSFT Patch page: https://isc.sans.edu/mspatchdays.html?viewday=2017-01-10 or our API if you prefer a more structured format: https://isc.sans.edu/api/getmspatchday/2017-01-10
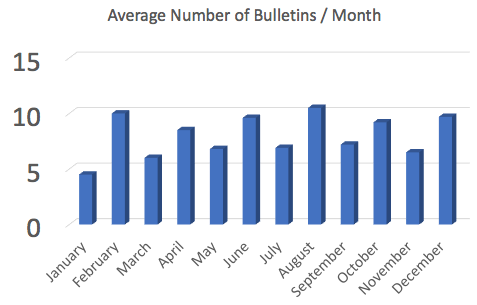
I doubt that Microsoft ran out of vulnerabilities to fix, but due to the holidays at the end of December, they likely had less time to fix existing vulnerabilities. January has been historically a "light month" for bulletins:
Adobe January 2017 Patches
Adobe today released a security update for Flash (APSB17-02) and it updated an update released last week for Acrobat/PDF Reader (APSB17-01).
The Acrobat/PDF Reader update addresses 29 vulnerabilities. Many of these vulnerabilities are considered critical as they can lead to code execution, but currently, there are no known exploits available according to Adobe. Later today, we should expect an update from Microsoft addressing these issues in Microsoft products that include Flash.
The Flash update fixes 13 vulnerabilities and exploitation of some of these vulnerabilities may also lead to code execution. Adobe considers this update a higher priority than the PDF Reader update.
Port 37777 "MapTable" Requests
Thanks to Bjørn for noticing an increase in port 37777 TCP traffic. He wrote a blog with some of the payloads he found, and after he notified us, I was able to confirm his observations in our honeypot [1].
First 32 bytes of the payload:
c1 00 00 00 00 14 00 00 63 6f 6e 66 69 67 00 00
c. o. n. f. i. g
31 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
ASCII representation of the payload (640 Bytes. The payload is followed by 0 padding for a total payload size of 5151 bytes.
{ "Enable" : 1, "MapTable" : [
{ "Enable" : 1, "InnerPort" : 85, "OuterPort" : 85, "Protocol" : "TCP", "ServiceName" : "HTTP" },
{ "Enable" : 1, "InnerPort" : 37777, "OuterPort" : 37777, "Protocol" : "TCP", "ServiceName" : "TCP" },
{ "Enable" : 1, "InnerPort" : 37778, "OuterPort" : 37778, "Protocol" : "UDP", "ServiceName" : "UDP" },
{ "Enable" : 1, "InnerPort" : 554, "OuterPort" : 554, "Protocol" : "TCP", "ServiceName" : "RTSP" },
{ "Enable" : 1, "InnerPort" : 23, "OuterPort" : 23231, "Protocol" : "TCP", "ServiceName" : "TELNET" },
{ "Enable" : 1, "InnerPort" : 23, "OuterPort" : 23123, "Protocol" : "TCP", "ServiceName" : "NEW" } ] }
The payload appears to attempt to configure port forwarding rules, which is typically done via UPNP (and UPNP has been heavily abused, but is typically not reachable from the "outside"). But the requests are different from UPNP in some ways:
- UPNP usually uses HTTP like headers. These requests do not use any readable headers, just a brief binary pre-ample.
- UPNP is typically using UDP. These requests arrive over TCP
- UPNP uses XML/SOAP for its payload. These requests use what looks like JSON
Some newer versions of UPNP allow for REST/JSON instead of the older SOAP/XML format. But this still doesn't explain the missing headers. Port 37777 is typically used to stream video from CCTV DVRs, not for configuration. But then again, it is possible that some DVRs do accept configuration commands like the one shown above. But a request like this should probably be directed at the gateway/router, not the DVR.
So there are still a lot of questions. Please let us know if you have any answers ;-)
Realtors Be Aware: You Are a Target
Real estate transactions are some of the higher value transactions performed by individuals and organizations. They often exceed hundreds of thousands of dollars in value, and for commercial properties, millions of dollars are quite normal. Many buyers and sellers are not familiar with what is normal when it comes to real estate transactions. Over the last few years, we have seen this exploited in a specific form of "Business E-Mail Compromise," where an attacker is injecting e-mails into conversations to trick the victim to transfer money to the wrong account.
A weak link in this transaction is often the realtor. Realtor's e-mail addresses are easy to find. Many realtors work more or less on their own and do not benefit from a corporate IT department with security monitoring. Instead, they use public webmail systems and heavily rely on cloud-based file sharing systems and e-mail attachments to exchange documents.
Recently, a realtor aware of this issue forwarded me the following exchange. Initially, the realtor received an e-mail that is very typical for the type of e-mail realtors receive from new clients:
Hi My name is James . I got your contact while searching for good realtor in Florida. My Partner and I are planning to relocate to the area by year end and would be interested in buying a house. Are you full time realtor?. Are we also suppose to contact bank as we are very new to this.
The realtor sent more or less a standard reply:
Hi, James: I will be very happy to help you with finding a home here. The first step is to get a mortgage pre approval letter. If you do not have any mortgage agent, I can recommend some. Give me a call when you have time.
Note that the realtor is asking for a mortgage pre-approval letter. This is a common "first step" to find out how much money the buyer can spend on a new house. Of course, James responded the next day:
Thanks for getting back to me on my request to purchase a house and sorry for the late response . I have been busy with some project . I actually got your contact while looking for good realtors online . Presently i live in Palos Hills Chicago, but i wish to have a property in your state for Income Revenue.Am interested in purchasing a 3 to 4 bed room house with a large parking garage ( a house with a pool within our price range will be perfect ). I was told i needed pre approval so i obtained it from my bank. I have shared it with you as well as details on desired location and what I'm looking for via google docs . Check it and let me know so i can call you when i finish from meeting to decide when to come and view the property.
Kind Regards James
Approval letter.pdf
Again, the e-mail is in-line with what you would expect from a buyer. Note the link to the "Approval Letter." This is where things get more interesting.
The link went to http:// myrealestategoogldrive .atspace.cc/ . A fairly "plausible" URL for a link like this. There are dozens of different file sharing sites out there, and this hostname is certainly in line with what a realtor would consider normal.
The site has been taken down now, but it offered a login screen asking for the realtor's webmail credentials. This is where the realtor contacting me got suspicious, so we do not know what "James" would have done with the credentials. But typically, the next steps involve:
- "James" will use the realtor's e-mail credentials to log into the webmail system
- Then, "James" will add a "Forward" address. This way, James will receive copies of all e-mails send to the realtor
- Once an e-mail comes across the realtor's inbox asking for bank details to wire money, "James" will reply with his information
The result, if successful, is that the buyer transfers money to the wrong account. Sadly, these wire transfers ("ACH Transfers") are often not reversible. The money will typically go first to a domestic account that "James" is monitoring, and as soon as the money arrives, it will be forwarded to a foreign account at which point the trail of the money often gets lost.
Yes, the e-mails from "James" contain typos and bad grammar. But realtors will typically happily do business with you even if you are not an expert in the use of the English language.


Comments