Tip: Ghidra & ZIP Files
I don't know where I got the idea, but I erroneously assumed that Ghidra could help with the analysis of document files. Ghidra is a software reverse engineering framework developed by the NSA and released at RSA 2019.
My test revealed the following.
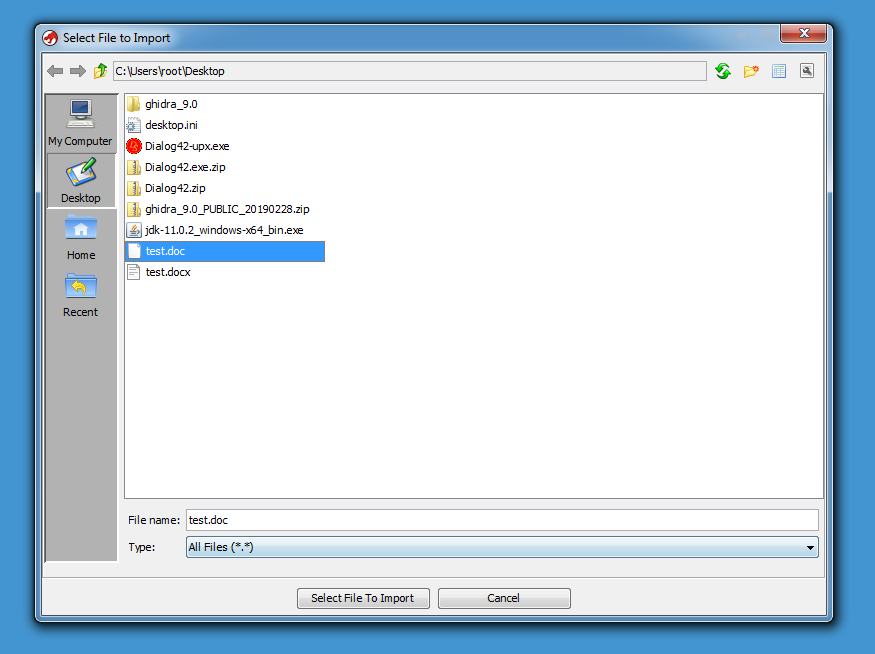
.doc files (e.g. Compound File Binary Format files) are not recognized at all:
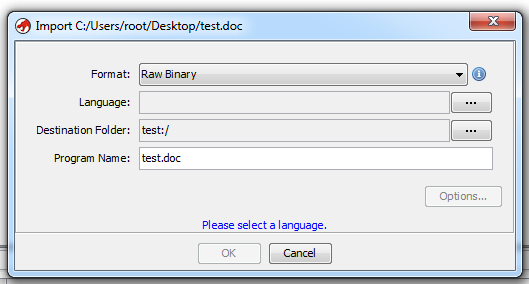
But with .docx files (Office Open XML files, e.g. ZIP files), something else happened:
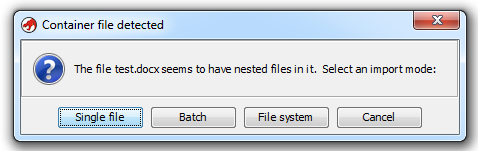
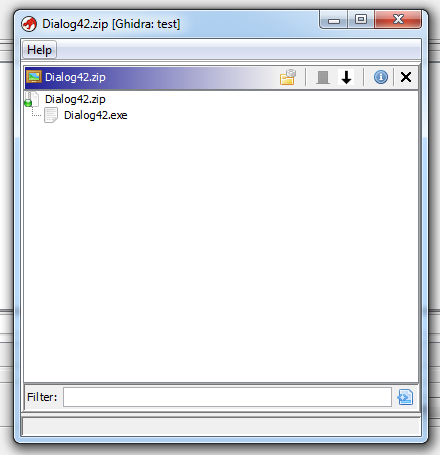
Ghidra recognizes the ZIP file format, and can look inside ZIP files. Here I'm opening a ZIP file containing an EXE:
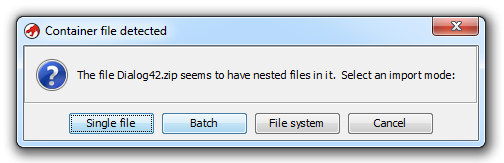
I can select "File system" and browse the content of the ZIP file:
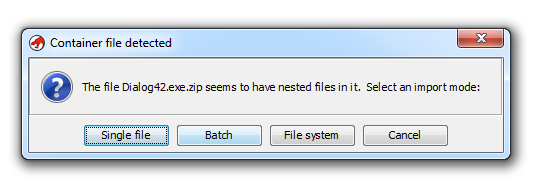
And then import the EXEs I want:
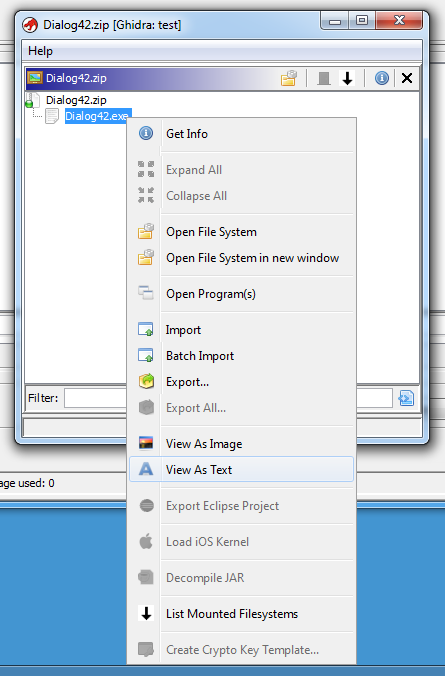
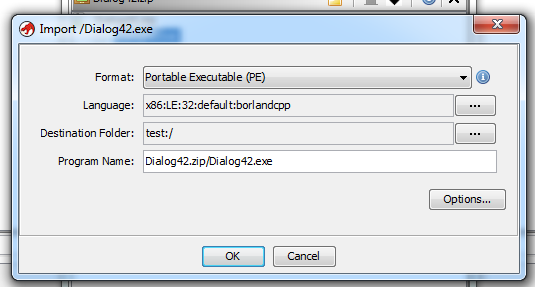
I like this feature, as my malware samples are often stored in a ZIP file. I can also select Batch and have all contained files (or a selection) imported.
Unfortunately, password protected ZIP files are not supported:
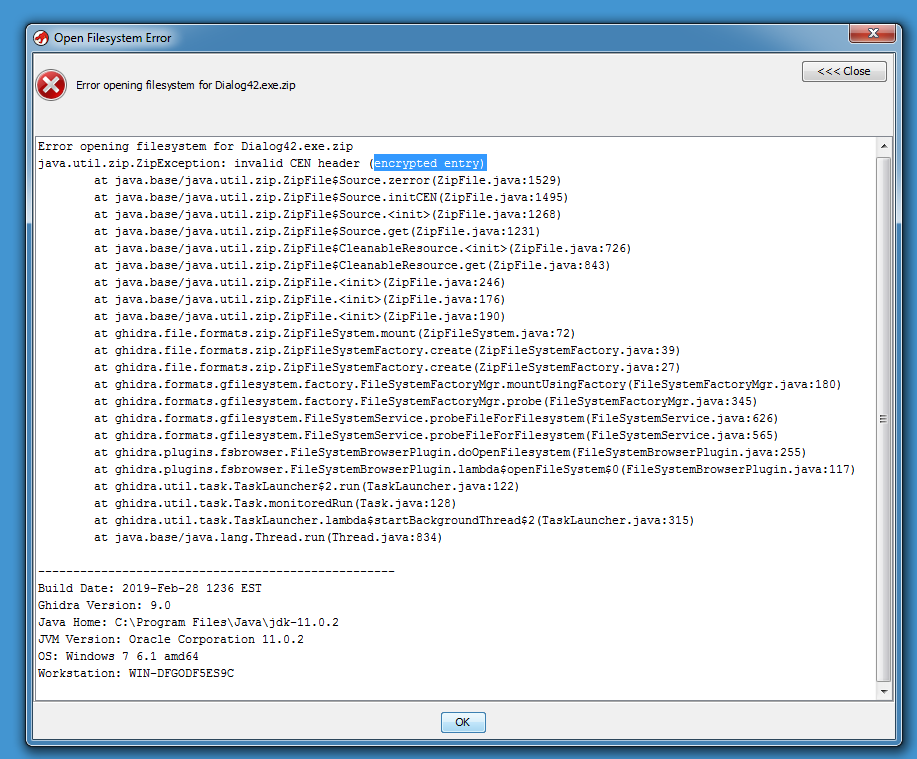
I don't think it would be difficult to add support for password protected ZIP file to Ghidra. When the NSA officially releases the source code, I'll take a look.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments