Snorpy a Web Base Tool to Build Snort/Suricata Rules
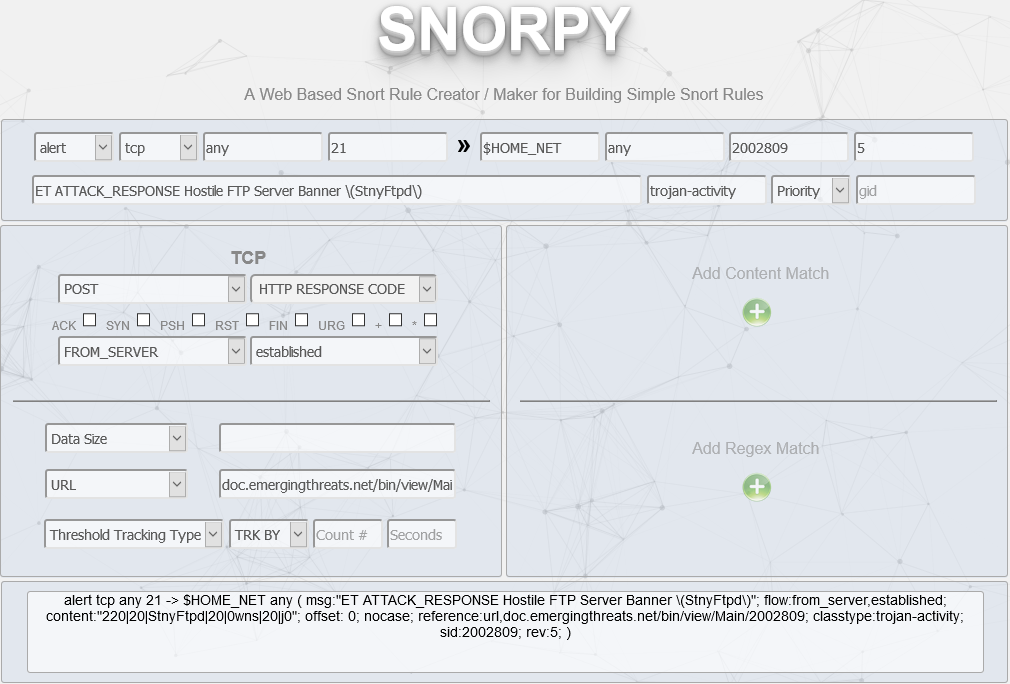
Snorpy is a web base application to easily build Snort/Suricata rules in a graphical way. It is simple to use starting from the Action and Protocol fields and as you pick each field, the rule builder shows the rule in the bottom window. Before setting up your own local copy, you want to test a live version maintained by the author go here.
This is an example of an existing Snort rule entered via the interface. The rule used for my example is from Emergingthreats with sid:2002809.
alert tcp any 21 -> $HOME_NET any (msg:"ET ATTACK_RESPONSE Hostile FTP Server Banner (StnyFtpd)"; flow:established,from_server; content:"220 StnyFtpd 0wns j0"; offset:0; nocase; reference:url,doc.emergingthreats.net/bin/view/Main/2002809; classtype:trojan-activity; sid:2002809; rev:5; metadata:created_at 2010_07_30, updated_at 2010_07_30;)
Note: You have to excape any of the special characters in the MSG fields (see example), just make sure you remove them after you copy the rule. There are a few fields that currently don't exist but they can be added in the code since the code is available.
If you are interested in trying Snorpy, I wrote a guide to install it on CentOS 7.6 located here.
[1] http://snorpy.com/
[2] https://github.com/chrisjd20/Snorpy
[3] https://handlers.sans.org/gbruneau/snorpy_setup.htm
[4] https://rules.emergingthreats.net/open/snort-2.9.0/rules/emerging-attack_response.rules
-----------
Guy Bruneau IPSS Inc.
My Handler Page
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu



Comments
I just added a super easy way to run this in docker!
#twitter post here https://twitter.com/Grotezinfosec/status/1084350405792813057
Try this: docker run --rm -p 80:80 followthewhiterabbit/flowrulegen
Anonymous
Jan 13th 2019
6 years ago
Instead, I just banged out a parser to log barnyard events to elasticsearch. And because those events were indexed with all of the things I wanted to search by/for (source IP/port, dest IP.port, etc) all of the search filter problems in snorby became academic. Even better, using kibana as my front end meant I got to use all of the viz tools and dashboard tools in kibana. I made a quick demo showing how kibana's viz tools and search tools made detecting a bot infection easy and then using my other logs (DNS queries for instance) made it easy to see exactly how and when the infection occurred. :-)
https://www.minds.com/newsfeed/783558588600688656?referrer=linuxgeek
Anonymous
Jan 14th 2019
6 years ago