Remote Desktop (TCP/3389) and Telnet (TCP/23), What might they have in Common?
I'm glad you asked. I'm always interested in trends and reviewing the activity capture by my honeypot over this past week, it shows that no matter what port the RDP service is listening on, a specific RDP string (Cookie: mstshash=) might be sent to any ports to find out if it is listing for this service. Here are some examples:
20200821-114923: 192.168.25.9:3389-104.140.188.38:39674 data '\x03\x00\x00\'"\xe0\x00\x00\x00\x00\x00Cookie: mstshash=TJdMjIgKn\r\n'
20200821-114924: 192.168.25.9:3389-104.140.188.38:53052 data "\x03\x00\x00,'\xe0\x00\x00\x00\x00\x00Cookie: mstshash=gJuhZZ\r\n\x01\x00\x08\x00\x01\x00\x00\x00"
20200821-114924: 192.168.25.9:3389-104.140.188.38:60644 data "\x03\x00\x00,'\xe0\x00\x00\x00\x00\x00Cookie: mstshash=bnmiei\r\n\x01\x00\x08\x00\x03\x00\x00\x00"
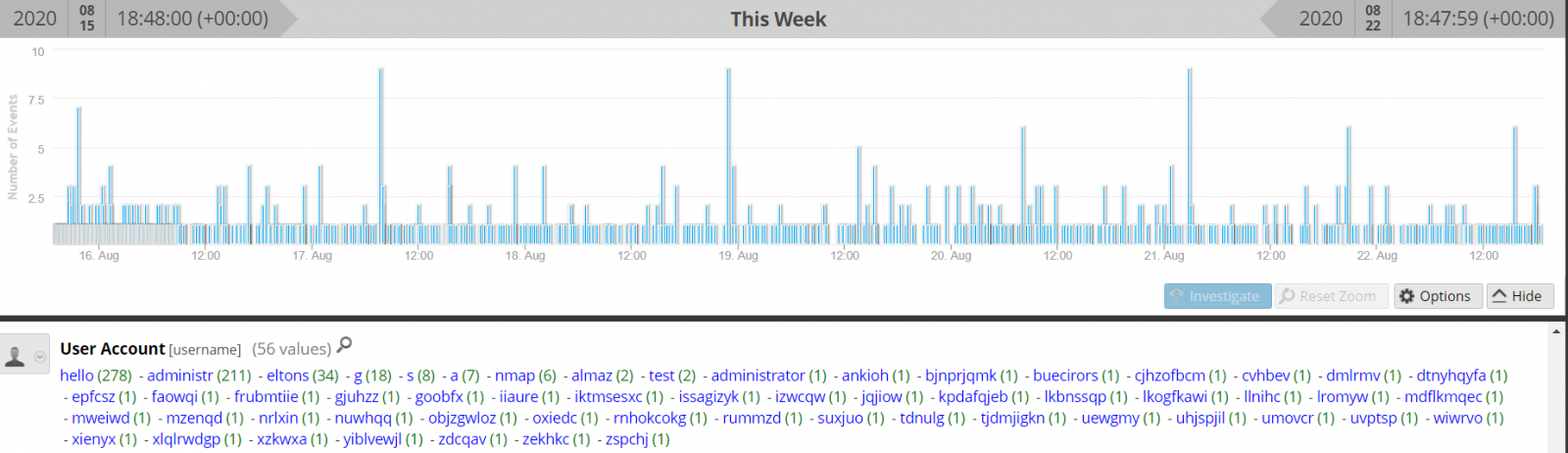
Last 7 Days - Port TCP/3389
This activity shows the list of usernames contained in the Cookie: mstshash= string sent to the port.
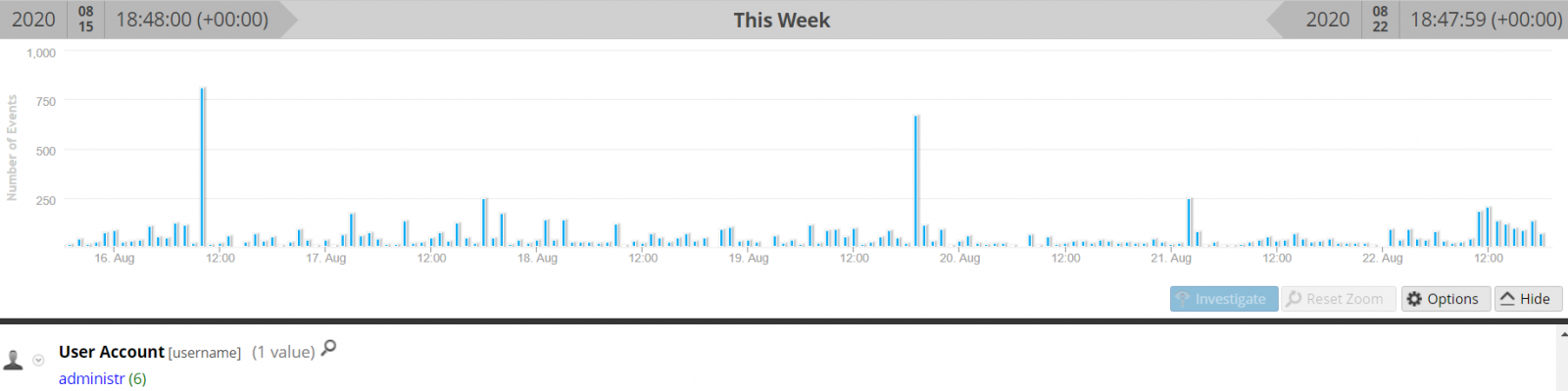
Last 7 Days - Port TCP/23
This activity shows the only username contained in the Cookie: mstshash= string sent to the port.
Last 7 Days - All Ports
This graph shows all the ports that received the Cookie: mstshash= string. Obviously, much of the activity is against TCP/3389 but other ports are being probed.
Several patches were released this year to secure the service [1][2][3][4] as well as some exploit code like BlueGate released earlier this year. It is always a good idea to review what the gateway is allowing inbound the network. Even moving the RDP service to a port other than TCP/3389, there is someone out there searching for this service and attempt to exploit it.
[1] https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2020-0609
[2] https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2020-0610
[3] https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2020-0612
[4] https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2020-0655
[5] https://isc.sans.edu/diary/Random+Port+Scan+for+Open+RDP+Backdoor/24422
[6] https://github.com/ollypwn/BlueGate
[7] https://www.dshield.org/forums/diary/An+Update+on+the+Microsoft+Windows+RDP+Bluekeep+Vulnerability+CVE20190708+now+with+pcaps/24960/
[8] https://isc.sans.edu/ipdetails.html?ip=104.140.188.38
-----------
Guy Bruneau IPSS Inc.
My Handler Page
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu
.PNG)


Comments