Qakbot malspam sent from an infected Windows host
Introduction
Every once in a while, I'll see spambot-style traffic from the Windows hosts I infect in my lab environment. On Tuesday 2020-03-31, this happened during a Qakbot infection. I've covered examining Qakbot traffic before, but that didn't include examples of spambot emails sent from an infected Windows computer. Today's diary provides a quick review of some email examples from spambot traffic by my Qakbot-infected lab host.
The traffic
A pcap of the traffic used for today's diary can be found here. It's a short snippet of the malspam traffic sent from my Qakbot-infected lab host. Use the Wireshark filter smtp.data.fragment as shown below to confirm there are emails we can export from the pcap.

Shown above: Filtering on the pcap to see if any emails can be exported from the spambot traffic.
Once we've confirmed there are emails we can export from the pcap, use the menu path File --> Export Object --> IMF... to export these emails as shown below.
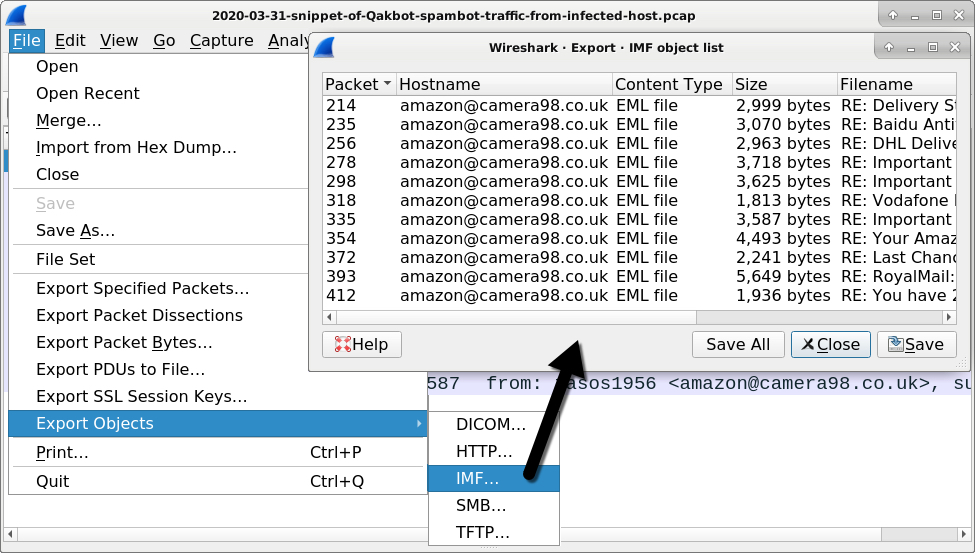
Shown above: Exporting IMF (Internet Mail Format) objects from the pcap.
The exported emails
A quick review of the emails indicates the information was taken from an infected user's mailbox. However, the recipients appear to be spoofed or malicious email addresses from old malspam circa 2013. See the images below for details.
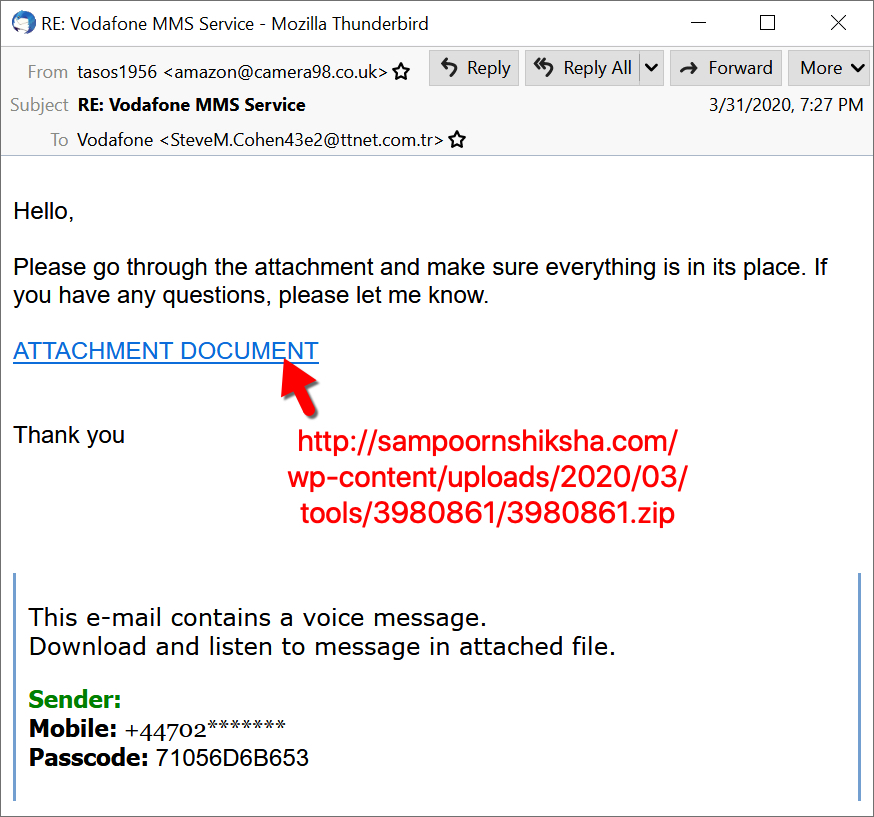
Shown above: The recipient of this malspam appears to be a sender from an old fake Vodafone message.
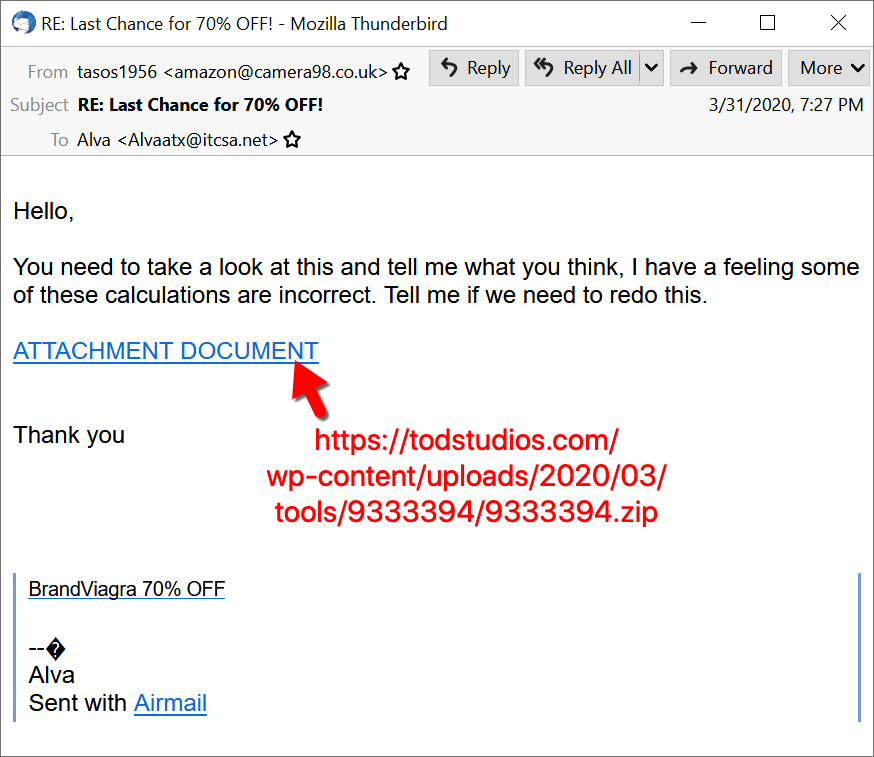
Shown above: The recipient of this malspam appears to be from an old Viagra-themed spam message.
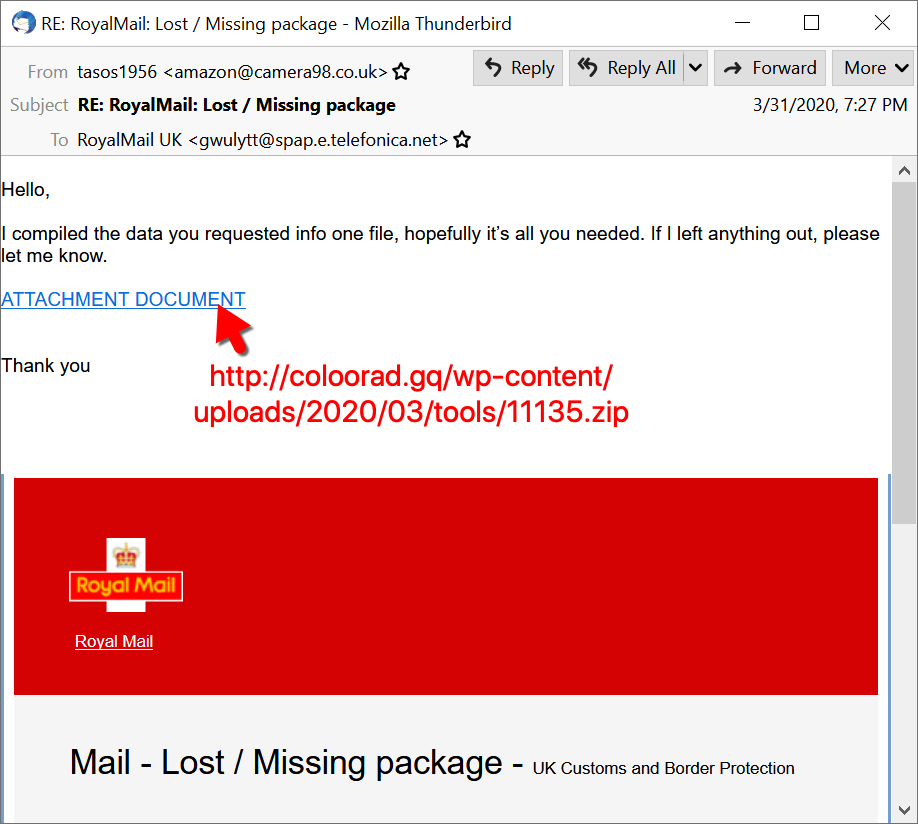
Shown above: The recipient of this malspam appears to be from an old fake Royal Mail message.
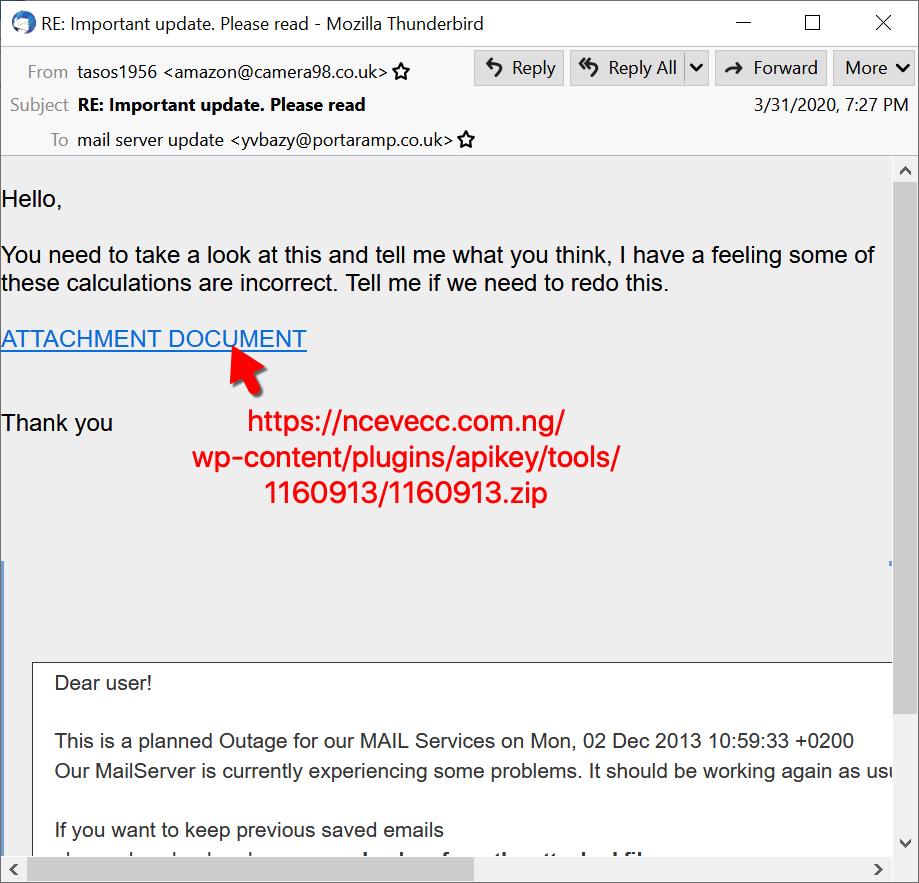
Shown above: The recipient of this malspam appears to be from an old mailbox-themed phishing message from 2013.

Shown above: The recipient of this malspam appears to be from an old DHL phishing message from 2013.

Shown above: The recipient of this malspam appears to be from an old malicious email impersonating someone from Baidu Antivirus.
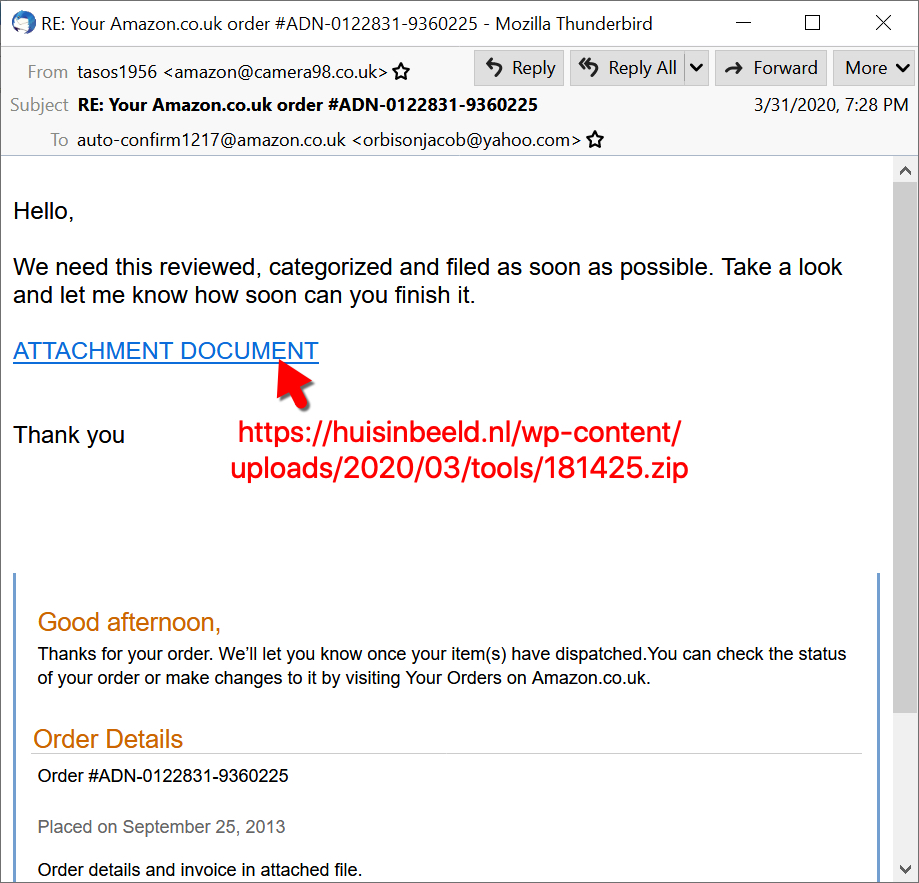
Shown above: The recipient of this malspam appears to be from an old fake Amazon email from 2013.
Final words
Reviewing these emails, you should notice patterns in how they are structured and the URLs used to deliver the initial malware, a zip archive downloaded from the web. The URLs I found from this Qakbot-related spambot traffic have all been submitted to URLhaus.
A pcap covering this snippet of Qakbot-related spambot traffic and the extracted 11 emails can be found here.
---
Brad Duncan
brad [at] malware-traffic-analysis.net


Comments