Phishing e-mail spoofing SPF-enabled domain
On Monday, I found what looked like a run-of-the-mill phishing e-mail in my malware quarantine. The "hook" it used was quite a common one – it was a fake DHL delivery notification inserted as an image into the body of the e-mail in an attempt to make user open its attachments.
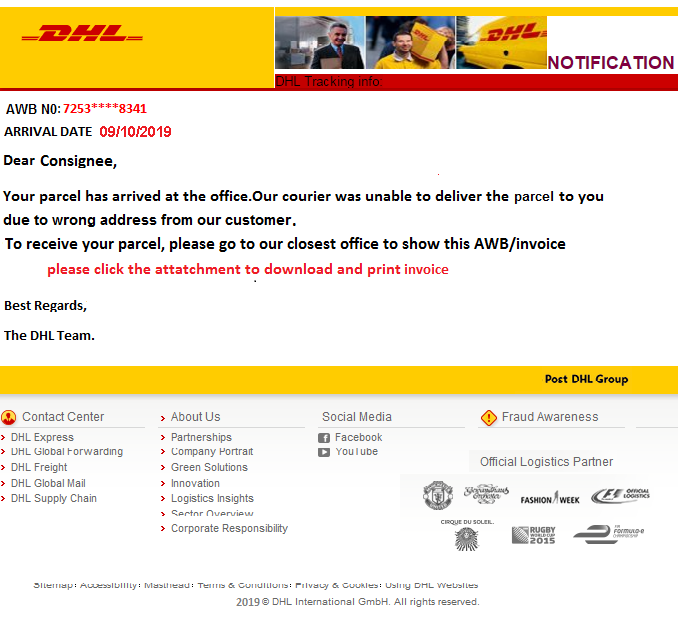
There were two attachments (see hashes bellow). RTF file masquerading as a Word Document ("SHIPPING DOCUMENT..doc"), which tried to exploit the famous CVE-2017-11882 vulnerability in Equation Editor used by Microsoft Office[1]. The second was an ACE archive ("INVOICE & AWB..ace"), containing a malicious executable ("mk.exe"). Although the executable was kind of interesting – it was an info stealer using Delphi packer[2] – the phishing turned out to be notable for a different reason. The spoofed sender domain had a Sender Policy Framework (SPF)[3,4] record set.
That, by itself, might not be that surprising – contrary to popular belief, setting a SPF record for a domain doesn’t mean that it will be impossible to use the domain in spoofed e-mail messages. Basically, SPF checks themselves cover only the "MAIL FROM" address (i.e. whether the sending server may send e-mails for the domain used in the "MAIL FROM" address) but don’t deal with contents of a "From" field in the e-mail header. This means that the following spoofing attempt will fail, providing that a SPF record for the "sender.tld" domain is correctly set.
HELO sender.tld
MAIL FROM:<[email protected]>
RCPT TO:<[email protected]>
DATA
From: "Sender" <[email protected]>
To: "Receiver" <[email protected]>
Date: Thu, 17 October 2019 10:15:00 +0100
Subject: Phishing?
However even with SPF record correctly set for the sender.tld domain, the following attempt at spoofing will pass SPF checks if the non-spf-domain.tld doesn’t have such record as well (although that doesn’t mean the spoofed e-mail won’t be blocked by some other security mechanism):
HELO non-spf-domain.tld
MAIL FROM:<[email protected]>
RCPT TO:<[email protected]>
DATA
From: "Sender" <[email protected]>
To: "Receiver" <[email protected]>
Date: Thu, 17 October 2019 10:15:00 +0100
Subject: Phishing?
Due to its simplicity and effectiveness (to a user, sender seems to be the address in the "From" header of the message, not the address which was specified in "MAIL FROM"), this technique is often used by phishing authors when they send spoofed e-mail messages.
One could therefore expect that the same technique was used in the case of our e-mail, however this was not the case.
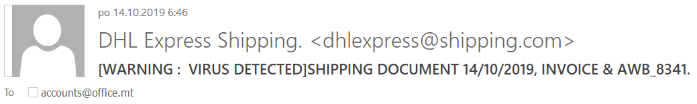
The sender appears to be [email protected] and if we take a look at the headers, we’ll see that the same e-mail was used as the "MAIL FROM" address. We may also discover that although a SPF check took place, it ended in "Neutral" result. This means that the SPF record doesn’t state whether the sending IP is or is not authorized to send e-mails for the domain.
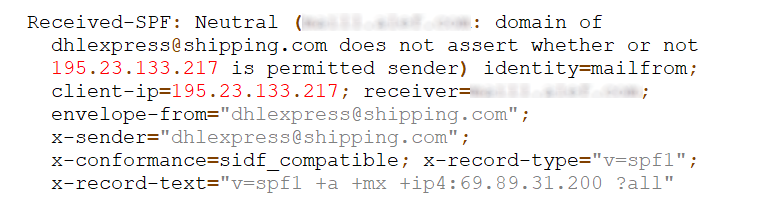
To understand the last line of the header and the reason for the result, one only needs to know that SPF enables us to use qualifiers to specify from which hosts should e-mails be accepted/passed (+), from which hosts they should be dropped/failed (-), from which they should be marked as suspicious/softfailed (~) and for which hosts the policy isn’t specified (?). The record for shipping.com which we see above therefore basically specifies that several servers are permitted to send e-mails for the domain and for all others may do so as well. Benefits of such SPF records are disputable at best.
Although it is not too usual to see such records and related phishing e-mails, this was not the first time I’ve come across such a case… And after having a look at the Alexa top 100 domains and finding two cases of SPF records containing "?all" even there, it seems that these are actually more common than one might think.
If you use such a SPF record on any of your domains, consider whether the more traditional "~all" or "-all" really isn’t an option for you.
And if you don’t have SPF set up yet, please do so – it will take you only a minute (all you need to do is create a new DNS TXT record) and although it’s not a silver bullet against phishing, it definitely won't hurt.
SHIPPING DOCUMENT..doc
MD5 - bc759db68c1f1611745216a4e0431201
SHA1 - 22e77a3ee9acc597500dbda6a82b7bd2d13d50b7
INVOICE & AWB..ace
MD5 - 673e823b66bce777f37377bd4aa07f71
SHA1 - 73f7a10fefa04432b18d9af9d4c774ecca815d5c
mk.exe
MD5 - 3c9aa414308ec74eb24b30875c755241
SHA1 - 06fba1adac357a7d338cc3a9a7eb2c68282d260b
[1] https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-11882
[2] https://www.fireeye.com/blog/threat-research/2018/09/increased-use-of-delphi-packer-to-evade-malware-classification.html
[3] https://tools.ietf.org/html/rfc4408
[4] https://tools.ietf.org/html/rfc7208


Comments
Most of the time, SPF is in use in conjunction with DMARC. And DMARC-aware receivers will take policy decisions as prescribed by the sender.
A recipe for a disaster: Introduce your SPF record with FAIL or SOFTFAIL policy in the presence of DMARC. Generic enterprise will have about a dozen mail senders, unknown to IT or unmanaged by IT. Essential chunk of mail will be either rejected, or placed to quarantine. It will NOT reach the intended recipients in a way, similar to how it was prior to making a simple and quick DNS change. Business people will be impacted.
R stands for Reporting in DMARC. Having visibility of DMARC reports is essential prior to making any changes to SPF policies, including publishing the SPF policy itself.
Anonymous
Oct 19th 2019
6 years ago
In an ideal world, SPF, DKIM and DMARC would be used by everyone. But for those unwilling or unable to set them all up, just publishing a SPF record can be a quick and easy win, if they do it as a part of considered security strategy and not in a haphazard fashion.
Anonymous
Oct 19th 2019
6 years ago