Phishing Campaign with Blurred Images
For a few days, I’m seeing a lot of phishing emails that try to steal credentials from victims. Well, nothing brand new but, this time, the scenario is quite different : The malicious email contains an HTML body with nice logos and texts pretending to be from a renowned company or service provider. There is a link that opens a page with a fake document but blurred with a popup login page on top of it. The victim is enticed to enter his/her credentials to read the document. I found samples for most of the well-known office documents. Here are some screenshots: 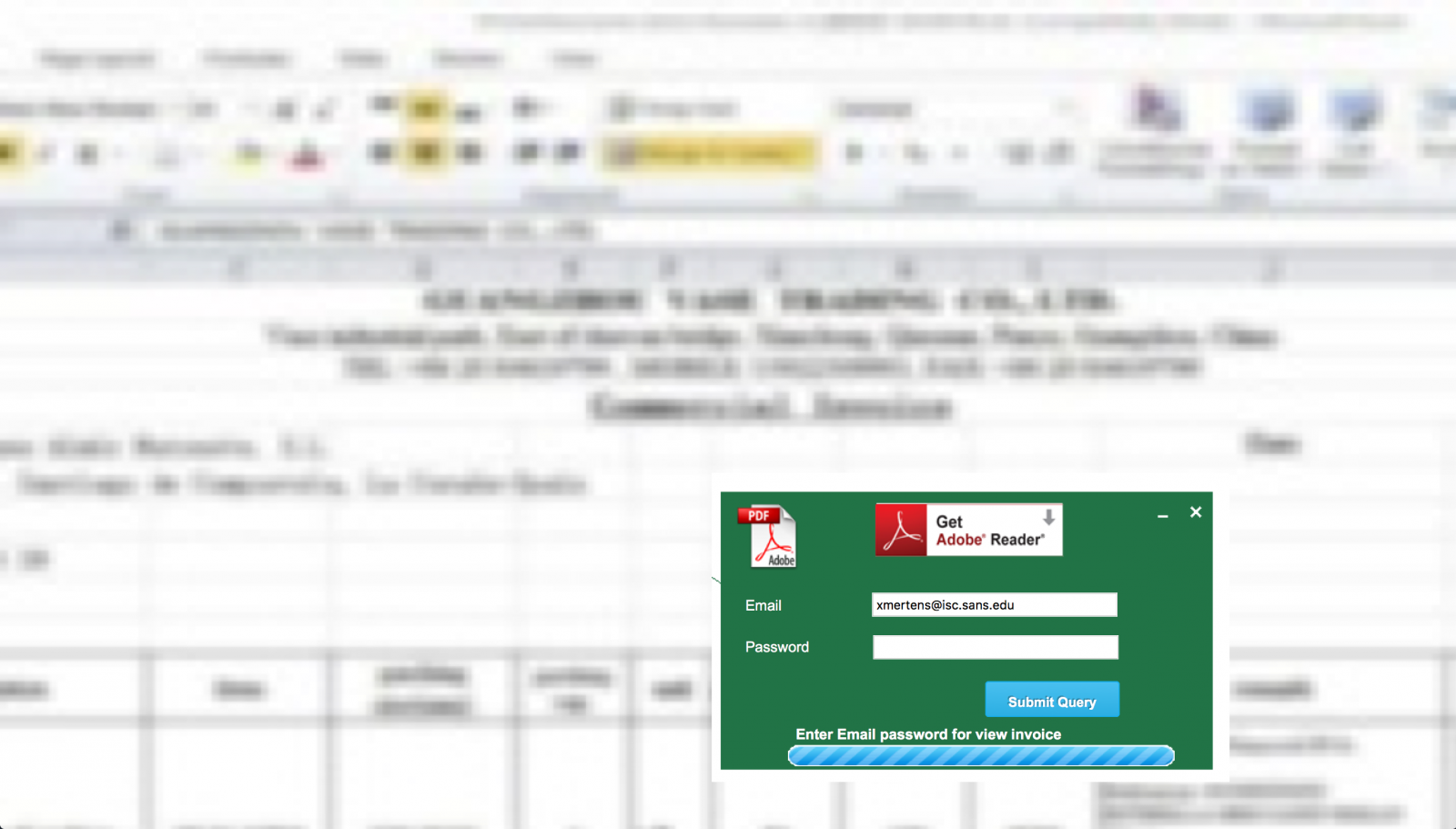
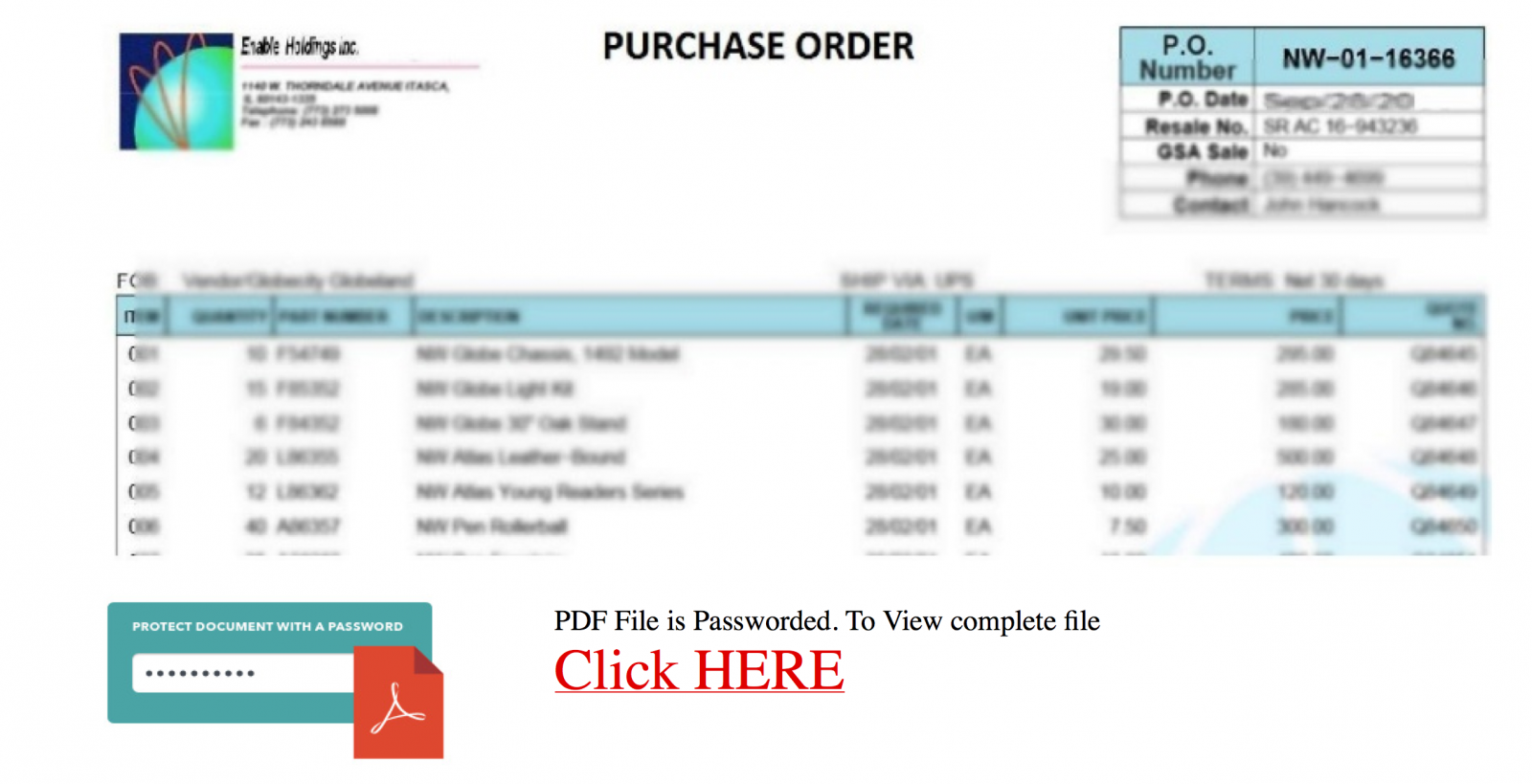
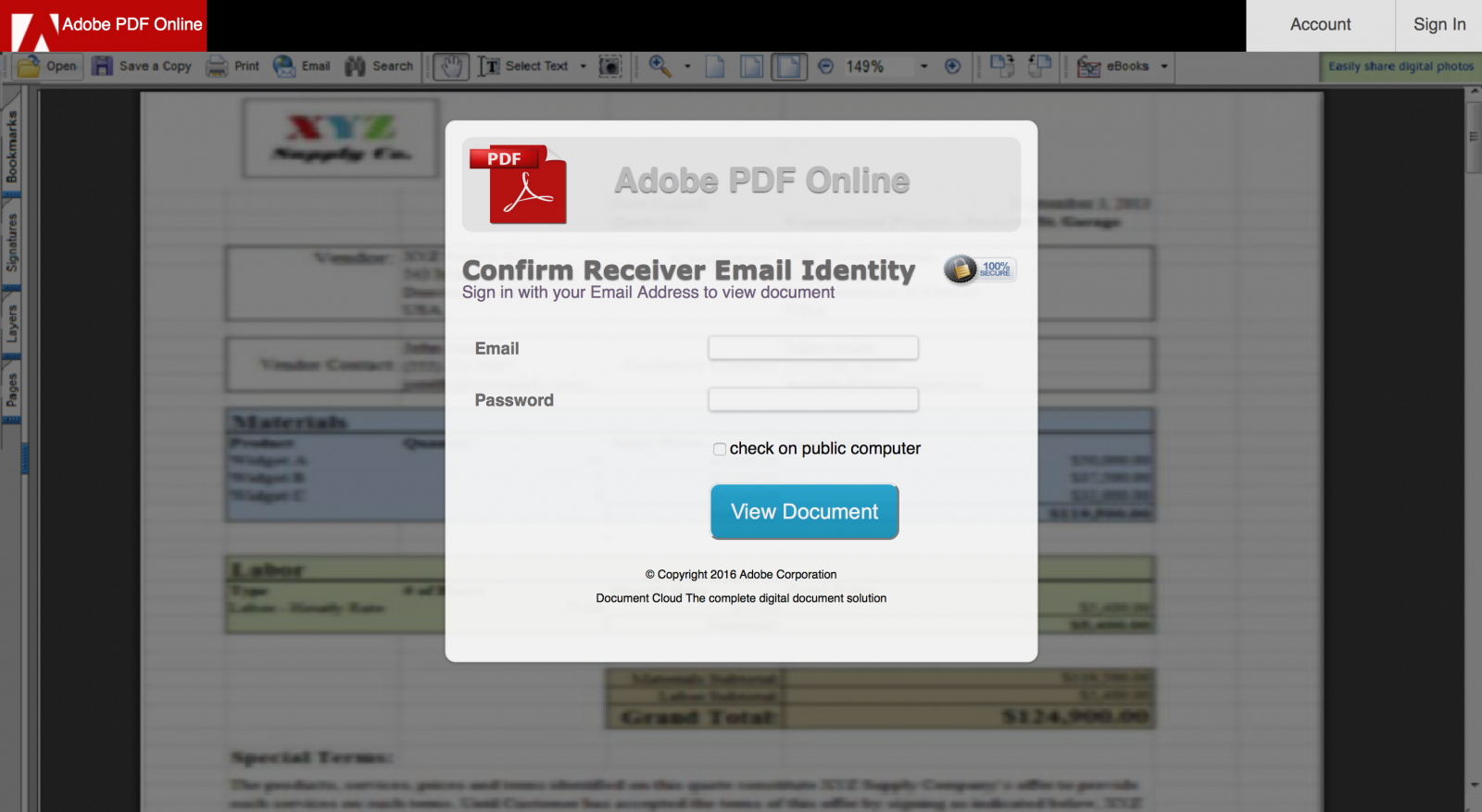
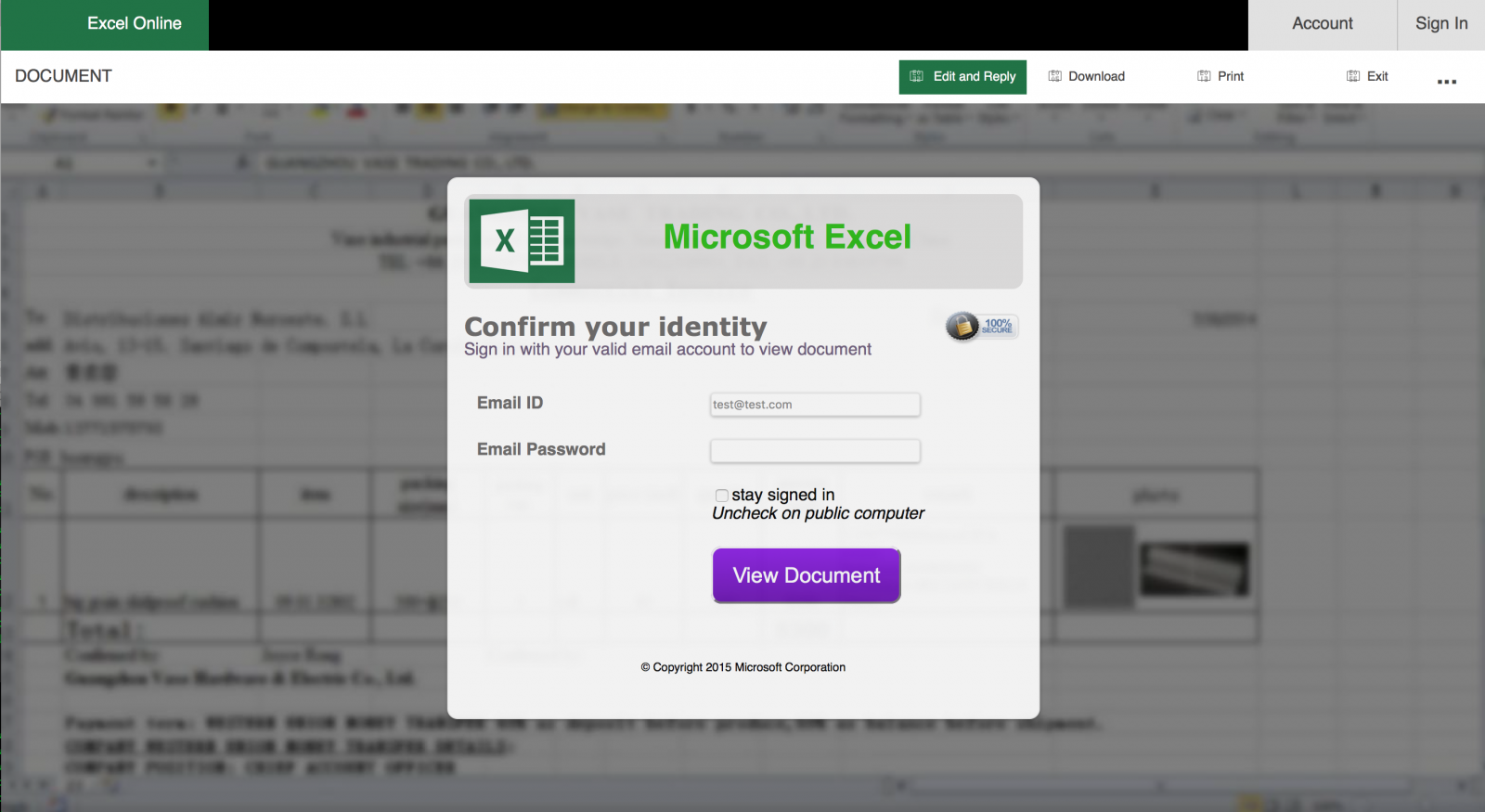 The strange fact is that it is not clear which credentials are targeted: Google, Microsoft or corporate accounts? The success of an efficient phishing is to take the victim by the hand and "force" him/her to disclose what we are expecting. So, nothing fancy behind this kind of phishing but it’s always interesting to perform further investigations and, for one of them, it was a good idea. Everybody makes mistakes and attackers too! The phishing page was hosted on a Brazilian website. Usually, such material is hosted on a compromised CMS like, not mentioning names but Wordpress, Joomla or Drupal. The Apache server had the feature 'directory indexing' enabled making all the files publicly available and, amongst the .php and .js files, a zip archive containing the "package" used by the attackers to build the phishing campaign. It was too tempting to have a look at it. The “blurred” effect was implemented in a very easy way: the fake document is a low-resolution screenshot displayed with a higher resolution. Like this:
The strange fact is that it is not clear which credentials are targeted: Google, Microsoft or corporate accounts? The success of an efficient phishing is to take the victim by the hand and "force" him/her to disclose what we are expecting. So, nothing fancy behind this kind of phishing but it’s always interesting to perform further investigations and, for one of them, it was a good idea. Everybody makes mistakes and attackers too! The phishing page was hosted on a Brazilian website. Usually, such material is hosted on a compromised CMS like, not mentioning names but Wordpress, Joomla or Drupal. The Apache server had the feature 'directory indexing' enabled making all the files publicly available and, amongst the .php and .js files, a zip archive containing the "package" used by the attackers to build the phishing campaign. It was too tempting to have a look at it. The “blurred” effect was implemented in a very easy way: the fake document is a low-resolution screenshot displayed with a higher resolution. Like this:  The most interesting finding is the presence of a JavaScript function to validate the victim’s email address but also to check the TLD. Is it a targeted attack? The presence of .mil, .edu or .gov is interesting while .com included all major free email providers.
The most interesting finding is the presence of a JavaScript function to validate the victim’s email address but also to check the TLD. Is it a targeted attack? The presence of .mil, .edu or .gov is interesting while .com included all major free email providers.
function emailCheck(emailStr) {
...
var checkTLD=1;
var knownDomsPat=/^(com|net|org|edu|int|mil|gov|arpa|biz|aero|name|coop|info|pro|museum|ws)$/;
...
if (checkTLD && domArr[domArr.length-1].length!=2 &&
domArr[domArr.length-1].search(knownDomsPat)==-1) {
alert(errmsg);
return false;
}
...
errmsg="Please enter a valid email address.";
The HTTP POST data and extra information are sent to the bad guys via a 'mailer.php' script. Sent data are:
- GeoIP details based on $REMOTE_ADDR
- User-Agent
- FQDN / IP
- Email / Password
Then, an HTTP redirect is performed to a second page: "phone.html" which mimics a Google authentication page and asks for the user phone number. Here again, POST data are processed via "phone.php" which sends a second email with the victim's phone number. Emails are sent to two addresses (not disclosed here):
- One @gmail.com account
- One @inbox.ru account
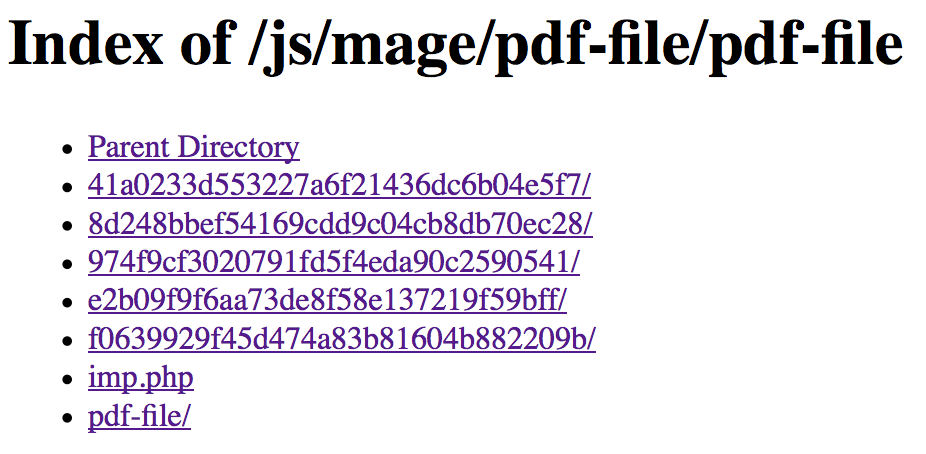
To conclude on a funny finding: there is a specific PHP script 'imp.php' which creates a copy of the material in a new directory. The directory name is based on a combination of a random number converted in Base64 and hashed. By calling this script in an automated way, it is possible to fill the web server file system with thousands of new directories:
From a technical point of view, it is a low-level attack but I'm pretty sure it still works. Take care!
Xavier Mertens (@xme)
ISC Handler - Freelance Security Consultant
PGP Key


Comments