Gama-rue, Where Are You!
Here’s one that’s making the rounds over the last few days and showed up in my SPAM folder with a helpful attachment. I'm one of those weird people who look to explore the depths of said SPAM folder to see what fun I might find therein.
As an example:
From: "United States Postal Service" <[email protected]>
Subject: USPS Delivery Failure Notification
Hello!
Unfortunately we failed to deliver the postal package you have sent on the…blah, blah, blah.
Ruh-roh!
The attachment is USPS report.pdf.zip and once unpacked yields USPS report.pdf.exe (MD5: 1fd6c3470b81f278572a27a1bf34cdf2)
A hash search finds this sample already submitted to ThreatExpert and VirusTotal yielding results that refer to the Gamarue family (multiple variants).
Nothing groundbreaking, downright pedestrian even, but bear with me. References to Gamarue.B show up in query results as of late September 2011; you may have seen similar with regard to ACH or Federal Reserve SPAM.
Data from the Microsoft Malware Protection Center shows a steady level of activity for the family overall and indications of this sample as new variant in the last couple of days (per the hash).
This particular sample, as is consistent with other Gamarue samples, modifies
HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run and injects itself into wuauclt.exe.These little exercises are always an opportunity to run output though some of my favorite tools (unabashed tool geek).
I ran the PCAP acquired during runtime through NetworkMiner 1.2 which reassembled the following malware downloaded when it phoned home to 85.121.38.27 (htobertur.ru):
Trojan:Win32/FakeSysdef (MD5: 8ae00c31b5546ee5a1b107c997171bde)
Trojan.Win32.Scar.fevl (MD5: d476533ea0aacb8244dfe0f5e65862a9)
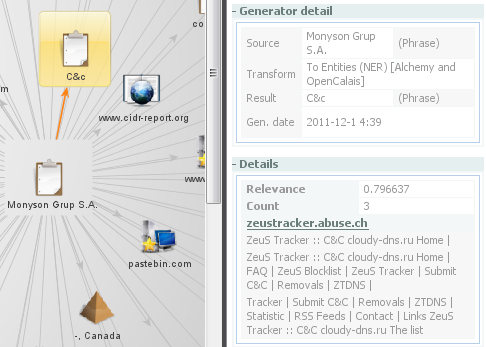
A quick review of the Romanian ASN (AS43215 Monyson Grup S.A.) for the above mentioned IP address shows a tendency towards association with the likes of Blackhole (as referred to in Pedro’s diary), fake AV, pharma SPAM, Zeus, SpyEye, and other instruments of ne'er do wells and malcontents. Zoinks!
A quick Maltego run on Monyson Grup S.A. as a phrase entity proves this out.
As a friend commented with both humor and sincerity: stay out of that neighborhood.
"And they would have gotten away with it too, if it weren't for those meddling kids…"
Keywords:
6 comment(s)
Click HERE to learn more about classes Russ is teaching for SANS
×
![modal content]()
Diary Archives


Comments
Jason
Dec 1st 2011
1 decade ago
Russ McRee
Dec 1st 2011
1 decade ago
liam
Dec 1st 2011
1 decade ago
Joseph
Dec 2nd 2011
1 decade ago
Mario
Dec 5th 2011
1 decade ago
For others: The spam has now been deleted.
Dr. J.
Dec 5th 2011
1 decade ago