Emotet -> Qakbot -> more Emotet
Introduction
On Friday 2020-10-30, I generated an Emotet infection in my lab and saw Qakbot as the follow-up malware. I let the activity run for a while, then another Emotet infection appeared on the same host after Qakbot started.
This appears to be an Emotet to Qakbot to another Emotet infection, with all three infections persistent on my infected lab host.
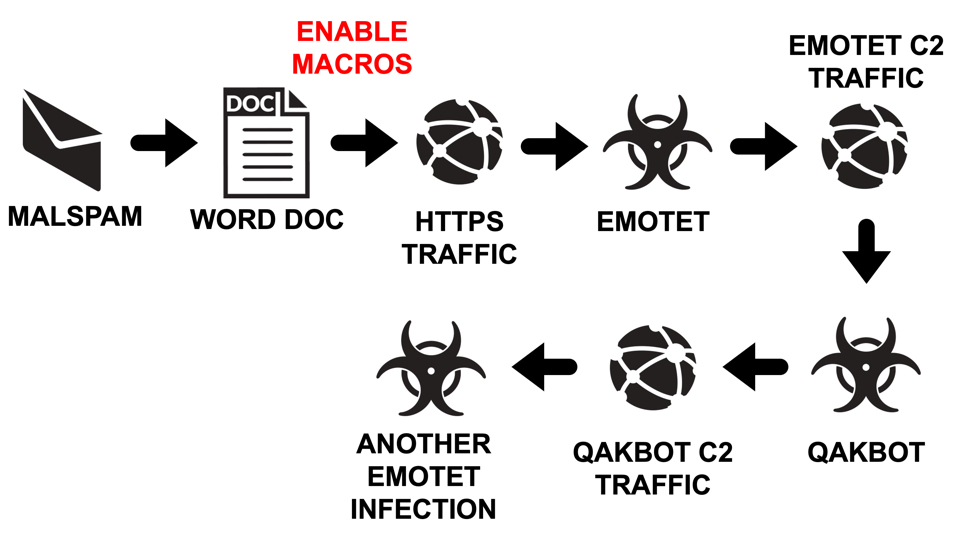
Shown above: Flow chart for the infection chain I saw on Tuesday 2020-10-27.
Today's diary reviews this Emotet to Qakbot to more Emotet infection from last week.
The malspam
The malicious spam (malspam) was a Halloween-themed message sent on Thursday 2020-10-29 to one of my honeypot email accounts. It had a Word doc attached to the message. The Word doc has a malicious macro designed to infect a vulnerable Windows host with Emotet.
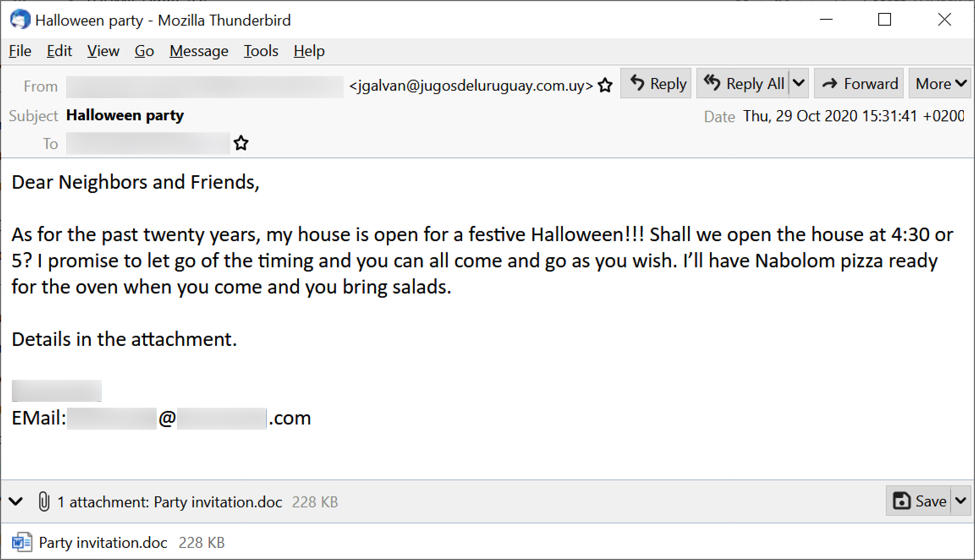
Shown above: Halloween-themed malspam with malicious Word doc attachment pushing Emotet.
The attached Word document uses a template that's typical for recent Word docs pushing Emotet.
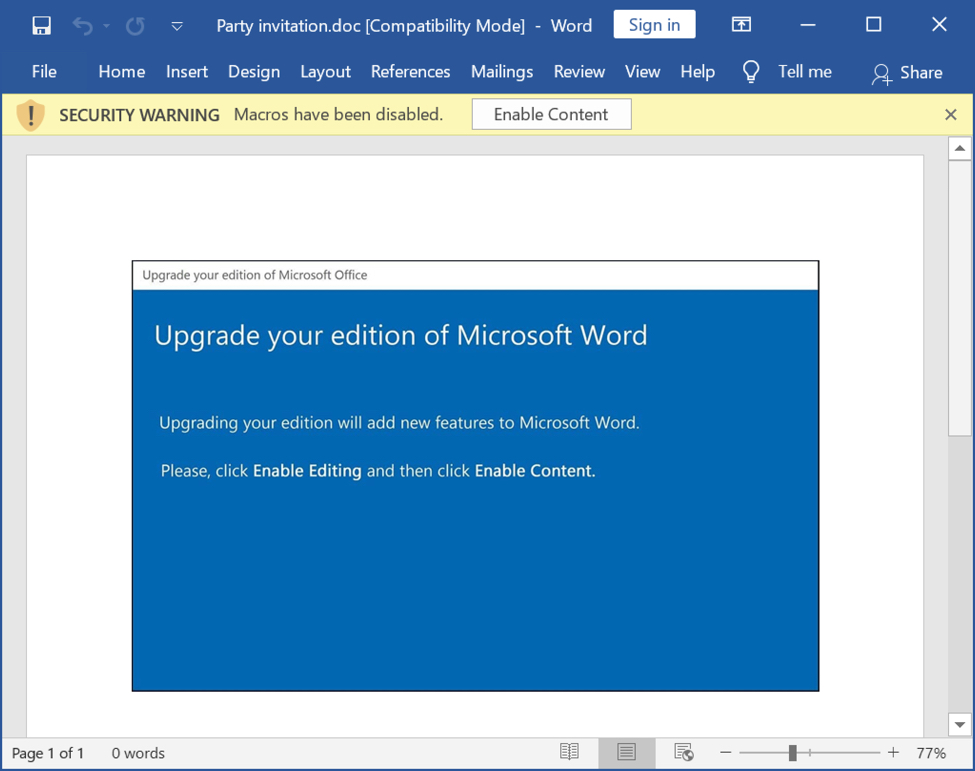
Shown above: Word doc with macro for Emotet.
Infection traffic
The traffic didn't look much different than what I've seen before for Emotet to Qakbot infections, there just seemed to be more Emotet traffic than normal after the Qakbot traffic kicked in. That didn't seem too unusual, though.
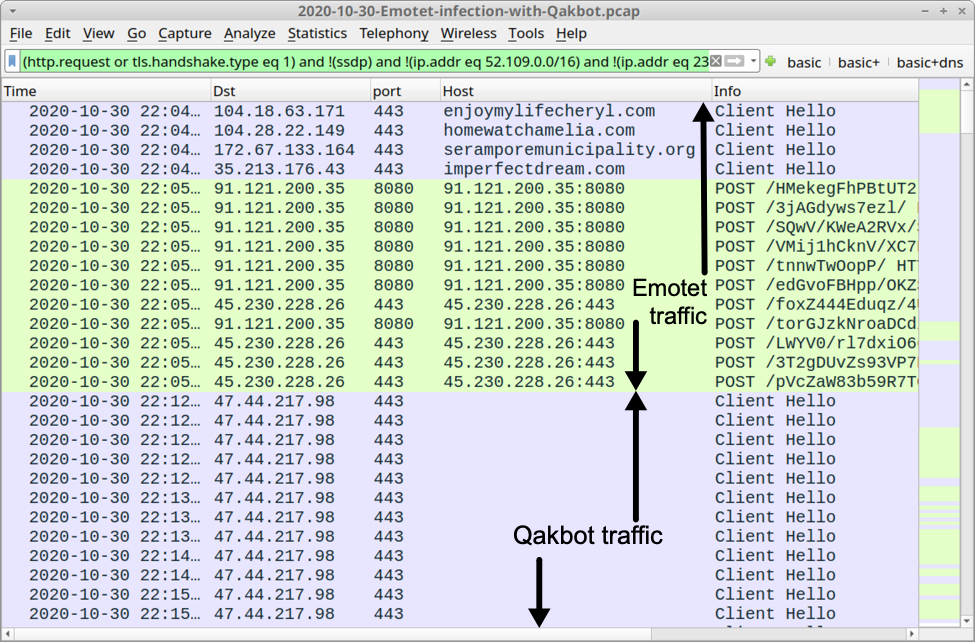
Shown above: Start of the infection traffic filtered in Wireshark.
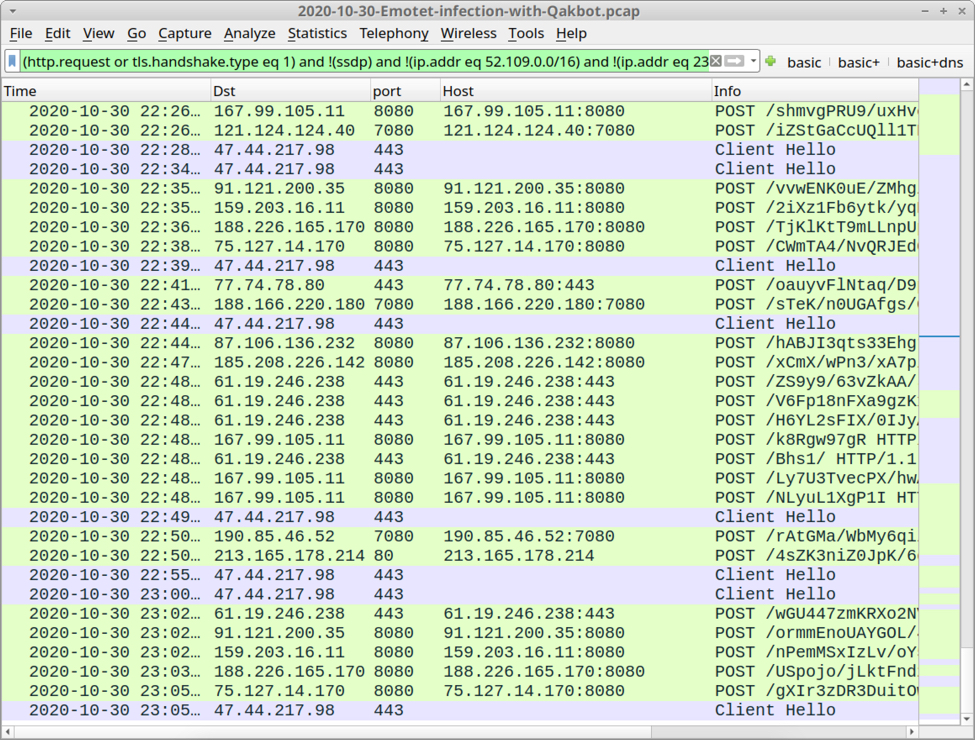
Shown above: Traffic from the end of my pcap filtered in Wireshark.
In the above image, Emotet traffic is more frequent than I usually see. Usually, Emotet will call back every 15 minutes, unless the host has been turned into a spambot. Emotet spambot activity includes more frequent C2 callback traffic, but we would also see indicators of spambot traffic, and that's not the case here.
Forensics on an infected Windows host
When I checked the registry, I saw two entries for Emotet. When Emotet updates itself, it will replace an already existing binary. I'd never personally seen two separate Emotet binaries active and set up in the registry like this.
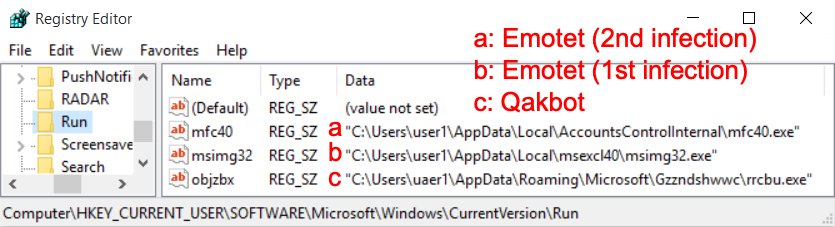
Shown above: Windows registry updates from my infected lab host.
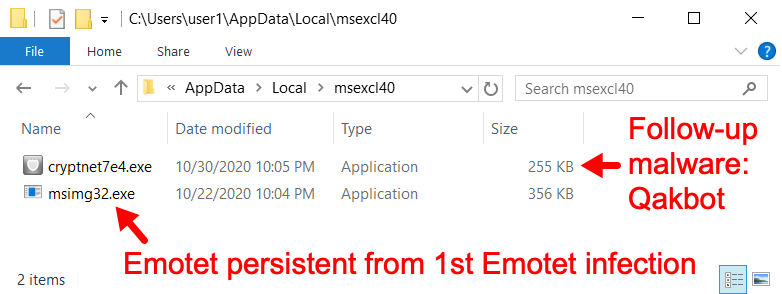
Shown above: Persistent Emotet EXE from 1st Emotet infection and Qakbot follow-up malware.
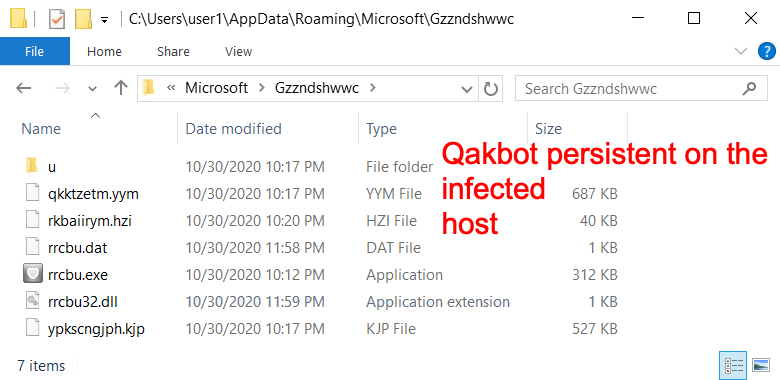
Shown above: Qakbot persistent on my infected lab host.
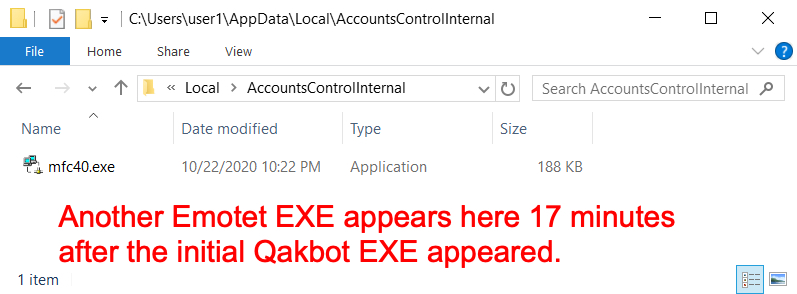
Shown above: Another Emotet infection persistent approximately 17 minutes after the initial Qakbot EXE appeared.
Of note, Emotet backdates the persistent EXE files 8 days before the current date. So the modified date on both of these Emotet EXE files is 2020-10-22, but the timestamp is the correct time for 2020-10-30. Based on the timestamps for these binaries, it appears that Qakbot caused the second Emotet infection.
Indicators of Compromise (IOCs)
SHA256 hash: ed51269c3602786ff6ddef3a808d8178d26e4e5960f4ac7af765e4bd642128dd
- File size: 233,466 bytes
- File name: Party invitation.doc
- File description: Word doc with macro for Emotet
SHA256 hash: a4c780c8b6ecb7d73f7498a4a46286cf2a2ecc6f378e2ba89deea06591c3cc04
- File size: 364,544 bytes
- File location: hxps://imperfectdream[.]com/wp-content/xb2csjPW6/
- File location: C:\Users\[username]\Nscs8ry\S8t4g_l\Epl6_wa2m.exe
- File location: C:\Users\[username]\AppData\Local\msexcl40\msimg32.exe
- File description: Emotet EXE retrieved by Word macro
SHA256 hash: dcda70b5cc63629dd2760dbc76ffda0bedefd0ee92af4d4e3740acc7dd2eaff2
- File size: 261,080 bytes
- File location: C:\Users\[username]\AppData\Local\msexcl40\cryptnet7e4.exe
- File location: C:\Users\[username]\AppData\Roaming\Microsoft\Gzzndshwwc\rrcbu.exe
- File description: Qakbot EXE retrieved by the Emotet-infected host
SHA256 hash: 4180c4c11e631a7545d40dadb74280c00f53271a75b113c387bb87adaf2cecf7
- File size: 318,992 bytes
- File location: C:\Users\[username]\AppData\Roaming\Microsoft\Gzzndshwwc\rrcbu.exe
- File description: Updated Qakbot EXE persistent on the infected Windows host
SHA256 hash: 4d1eeb527a61391ddcf30b0f9d6d9f96369e0179c1e1a65da5da33a196a991d4
- File size: 192,512 bytes
- File location: C:\Users\[username]\AppData\Local\AccountsControlInternal\mfc40.exe
- File description: Another Emotet EXE persistent on the infected Windows host
HTTPS traffic caused by Word macro to retrieve initial Emotet EXE:
- port 443 - enjoymylifecheryl[.]com
- port 443 - homewatchamelia[.]com
- port 443 - seramporemunicipality[.]org
- port 443 - imperfectdream[.]com
HTTP traffic caused by the two Emotet infections:
- 91.121.200[.]35 port 8080 - 91.121.200[.]35:8080
- 45.230.228[.]26 port 443 - 45.230.228[.]26:443
- 172.91.208[.]86 port 80 - 172.91.208[.]86
- 50.91.114[.]38 port 80 - 50.91.114[.]38
- 121.124.124[.]40 port 7080 - 121.124.124[.]40:7080
- 167.99.105[.]11 port 8080 - 167.99.105[.]11:8080
- 159.203.16[.]11 port 8080 - 159.203.16[.]11:8080
- 188.226.165[.]170 port 8080 - 188.226.165[.]170:8080
- 75.127.14[.]170 port 8080 - 75.127.14[.]170:8080
Traffic caused by Qakbot:
- 47.44.217[.]98 port 443 - HTTPS traffic
- 89.105.198[.]119 port 80 - a.strandsglobal[.]com - attempted TCP connections
- port 443 - cdn.speedof[.]me - HTTPS traffic
Caused by Qakbot and Emotet:
- various IP addresses - various ports - attempted TCP connections
Final words
In order to become infected, a victim must open the Word document and enable macros. In most cases, people would see a warning against enabling macros. Just opening the Word document by itself should not kick off the infection chain, unless the computer was set up to have macros automatically enabled.
Although Emotet pushes other families of malware like Qakbot, this is the first time I've seen indications that Qakbot has pushed Emotet.
A zip archive containing a pcap from today's infection is available here. The Word doc and EXE files from the IOCs have been submitted to MalwareBazaar Database.
---
Brad Duncan
brad [at] malware-traffic-analysis.net


Comments