December 2021 Forensic Challenge
Introduction
Today's diary is a forensic challenge for December 2021. This month's challenge is based on network traffic from an Active Directory (AD) environment where a Windows client becomes infected. The prize for this contest is a Raspberry Pi.
The packet capture (pcap) is in a password-protected zip archive available here.
Rules for the contest follow:
- Only one submission per person.
- Participants who submit the correct answers will be entered into a drawing, and one will win the Raspberry Pi.
- Submissions should be made using the form on our contact page at: https://isc.sans.edu/contact.html
- Use
December 2021 Forensic Challengefor the Subject: line. - Provide the following information:
- IP address of the infected Windows computer.
- Host name of the infected Windows computer.
- User account names from the infected Windows computer.
- Date and time the infection activity began in UTC (the GMT or Zulu timezone).
- The family of malware that caused this infection.
We will accept submissions through Sunday December 19th, 2021. Everyone who submits the correct answers will be entered in a drawing, and the winner will be randomly chosen. The winner will be announced in an ISC diary on Wednesday December 22nd, and that diary will also provide analysis of the infection traffic.
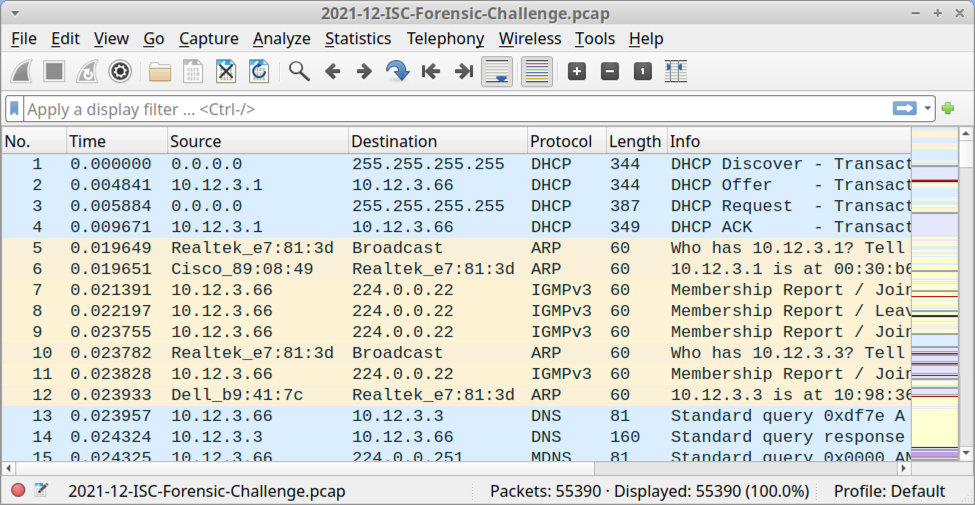
Shown above: Pcap for this monht's forensic challenge opened in Wireshark using the default column display.
Requirements
Analysis of the infection traffic requires Wireshark or some other pcap analysis tool. Wireshark is my tool of choice to review pcaps of infection traffic. However, default settings for Wireshark are not optimized for web-based malware traffic. That's why I encourage people to customize Wireshark after installing it. To help, I've written a series of tutorials. The ones most helpful for this quiz are:
- Wireshark Tutorial: Changing Your Column Display
- Wireshark Tutorial: Identifying Hosts and Users
- Wireshark Tutorial: Display Filter Expressions
- Using Wireshark - Exporting Objects from a Pcap
I always recommend participants review these pcaps in a non-Windows environment like BSD, Linux, or macOS. Why? Because this pcap contains Windows-based malware in some of the traffic. If you're using a Windows host to review this pcap, your antivirus (or Windows Defender) may delete or alter the pcap. Worst case? If you extract malware from this pcap and accidentally run it, you might infect your Windows computer.
Active Directory (AD) Environment
The infected Windows host is part of an AD environment, so the pcap contains information about the Windows user account. The user account is formatted as firstname.lastname. The AD environment characteristics are:
- LAN segment range: 10.12.3.0/24 (10.12.3.0 through 10.12.3.255)
- Domain: fargreentech.com
- Domain Controller: 10.12.3.3 - FARGREENTECH-DC
- LAN segment gateway: 10.12.3.1
- LAN segment broadcast address: 10.12.3.255
Final Words
Again, the zip archive with a pcap of the infection traffic is available here. The winner of today's contest and analysis of the infection traffic will be posted in an upcoming ISC diary two weeks from today on Wednesday December 22nd.
---
Brad Duncan
brad [at] malware-traffic-analysis.net


Comments