Fake AV is Back: LaCie Network Drives Used to Spread Malware
I have not seen much Fake AntiVirus lately. Maybe I haven't been looking for it. But this weekend, I received a few identical spam messages with slightly different subjects advertising that I had won a licensed copy of ESET's NOD32 Anti Virus. Many anti-malware products are offering free or highly discounted initial licenses to lure buyers, so this email may seem legitimate to some, even though it wasn't done terribly convincing (I am using a script to defang HTML in all email I receive which may account for some of the formatting issues):
The link, went down the folling redirect chain:
https://clck.ru/FSkJV
https://sba.yandex.net/redirect?url=ftp://[IP Address]/LaCie/Tirel/eav_1year.exe&client=clck&sign=[hex hash]
ftp://[IP Address]/LaCie/Tirel/eav_1year.exe
The FTP URL is typical for a LaCie network connected drive. It isn't clear how the attacker obtained access to this drive, but typically, these drives are compromised via weak passwords or vulnerable applications installed on the drive.
The binary does result in a mixed Virustotal picture, but oddly enough, it looks like I was the first one uploading it, about two days after I saw the email:
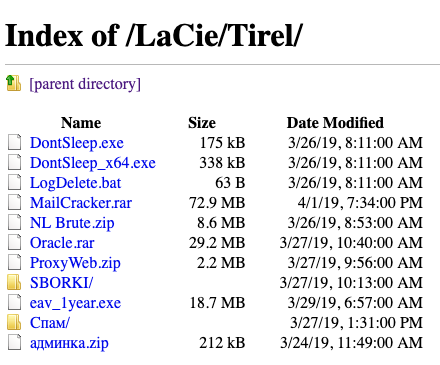
ESET's product did not recognize the file as malicious. This being an FTP URL made it easy to get a directory listing:
The executables in this folder are triggering various malware signatures. Other files appear to include simple password brute force utilities supporting the guess that this drive was compromised using a simple password.
The first directory contains a number of password protected zip files with various tools (based on the ZIP file listing) including openvpn configuration files.
Oracle.rar includes the obligatory xmrig miner which is still part of pretty much any compromised system I am running into.
---
Johannes B. Ullrich, Ph.D. , Dean of Research, SANS Technology Institute
Twitter|


Comments