Angler exploit kit pushes new variant of ransomware
Introduction
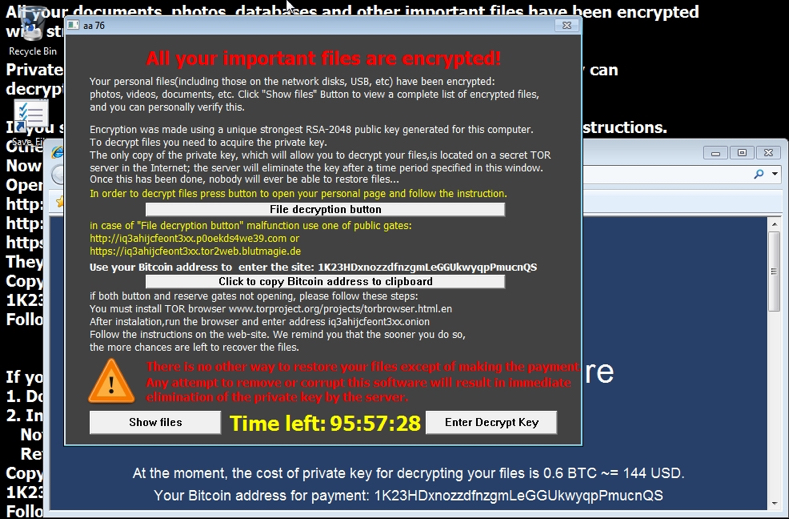
The Angler exploit kit (EK) is being used to push a new variant of TeslaCrypt/AlphaCrypt ransomware. I've been documenting cases of Angler EK pushing AlphaCrypt in recent weeks [1][2][3]. Last week on 2015-05-07, I started seeing a new variant [4]. This new variant has a popup window that uses CTB-Locker-style instructions.
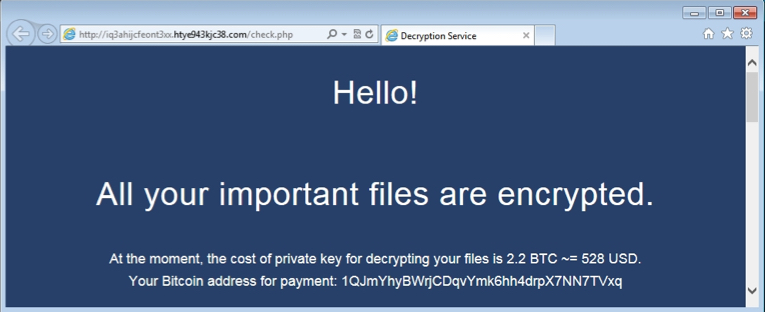
As seen below, this variant doesn't provide a name for itself in the decrypt instructions.
The same malware sample used a different bitcoin address for each host it infected.
Traffic Characteristics of this New Ransomware Variant
The traffic appears identical to what we've seen with previous infections from TeslaCrypt and AlphaCrypt. A few hours ago I infected a host from a site using Angler EK and received similar alerts from the network traffic.

Shown above: Alerts from monitoring the infection with Security Onion.

Shown above: HTTP traffic from the infection. Click on the image to see it full-size.
A sample of the ransomware can be found at:
https://malwr.com/analysis/MjE3ODRlYzc1MmQ2NGUyNDkyYWNkNWM0OWZiOGVjYzE/
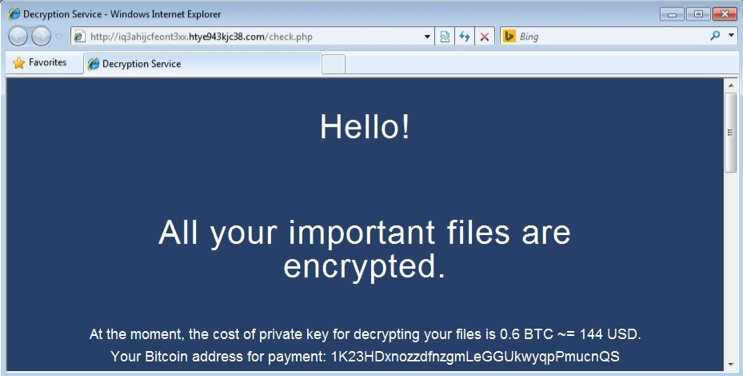
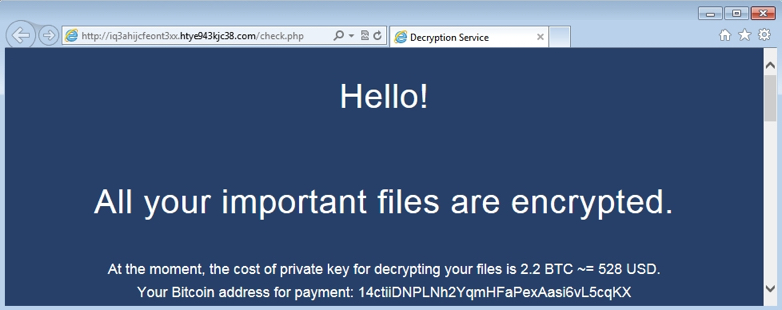
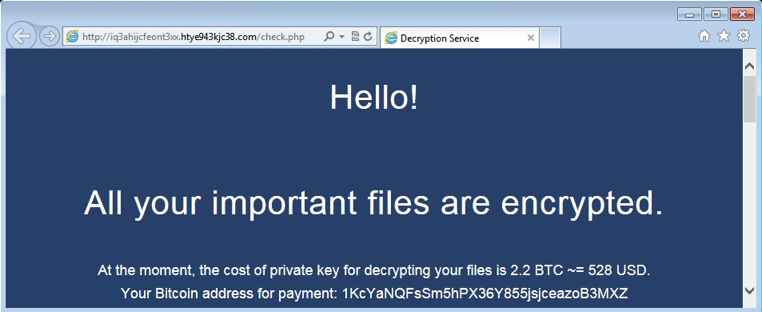
I infected 4 different hosts with Angler EK in a 5-hour timeframe and received the same ransomware. It was the same file with the same hash each time. However, the bitcoin address for the ransom payment was different for each infected host. Shown below are decrypt pages from the other 3 hosts:
Here are the bitcoin addresses from these infected hosts:
- 14ctiiDNPLNh2YqmHFaPexAasi6vL5cqKX
- 1K23HDxnozzdfnzgmLeGGUkwyqpPmucnQS
- 1KcYaNQFsSm5hPX36Y855jsjceazoB3MXZ
- 1QJmYhyBWrjCDqvYmk6hh4drpX7NN7TVxq
Pcap files of the infection traffic (Angler EK and the post-infection) are available at:
- http://www.malware-traffic-analysis.net/2015/05/11/2015-05-11-Angler-EK-traffic-example-01.pcap
- http://www.malware-traffic-analysis.net/2015/05/11/2015-05-11-Angler-EK-traffic-example-02.pcap
- http://www.malware-traffic-analysis.net/2015/05/11/2015-05-11-Angler-EK-traffic-example-03.pcap
- http://www.malware-traffic-analysis.net/2015/05/11/2015-05-11-Angler-EK-traffic-example-04.pcap
Final Words
From what I can tell, TeslaCrypt and AlphaCrypt are very similar to CryptoLocker. This new, unnamed variant appears to be another evolution from this family of ransomware.
I've been seeing a lot of Angler EK lately. In recent weeks, more often than not, it's been pushing ransomware. Since 2015-05-07, I've only seen this new variant.
---
Brad Duncan, Security Researcher at Rackspace
Blog: www.malware-traffic-analysis.net - Twitter: @malware_traffic
References:
[1] http://malware-traffic-analysis.net/2015/04/30/index.html
[2] http://malware-traffic-analysis.net/2015/05/06/index.html
[3] http://malware-traffic-analysis.net/2015/05/07/index.html
[4] http://malware-traffic-analysis.net/2015/05/07/index2.html



Comments
Anonymous
May 12th 2015
1 decade ago
Anonymous
Jun 28th 2016
9 years ago