Monster Libra (TA551/Shathak) --> IcedID (Bokbot) --> Cobalt Strike & DarkVNC
Introduction
On Monday, 2022-08-22, I generated an IcedID (Bokbot) infection based on Monster Libra (also known as TA551 or Shathak). See this tweet thread from @pr0xylife and @Max_Mal_ for details on Monday's specific wave of IcedID infection. My flow chart on this activity follows.
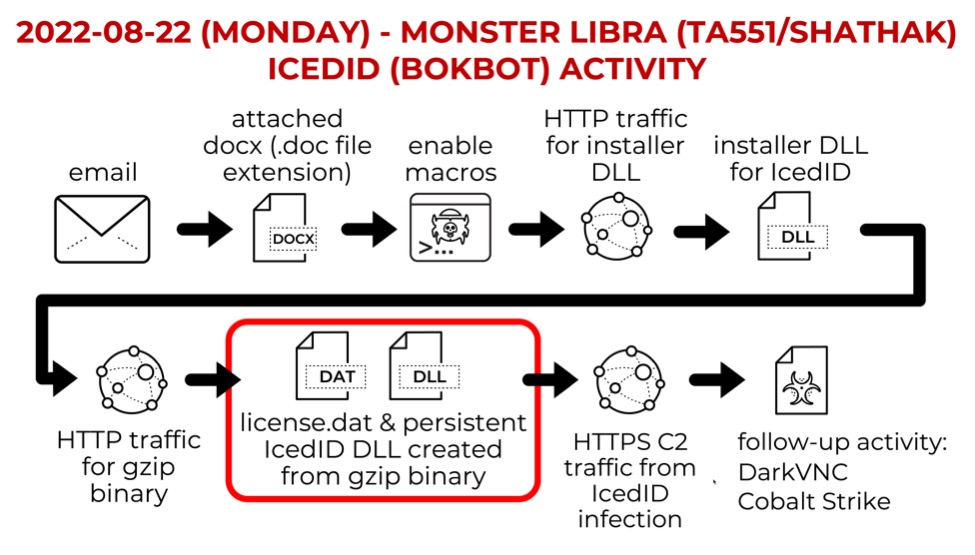
Shown above: Flow chart from Monster Libra (TA551/Shathak) IcedID infection on Monday 2022-08-22.
Malware and Artifacts
SHA256 hash: 7d0f80026a49bdc5c9e6b6bb614b37a9edbb0ca50127c7078ff52d4fc729afa8
- File size: 285,184 bytes
- File location: hxxp://138.124.183[.]50/barkss/u2lj2R9GN67SRsb7DZYKzF1jBt-yY6AVrA~~/5B6_95Swfy8TXGHD58qeEjYyxRXTL1bqhw~~/
- File location: File location: C:\Users\[username]\AppData\Local\Temp\iQG29uba.dll
- File description: 64-bit DLL installer for IcedID from Monster Libra (TA551) URL
- Run method: rundll32.exe [filename], #1
SHA256 hash: a969f17bf162032878417da351a229a3ef428cac99b485aedbded04f62291dee
- File size: 615,868 bytes
- File location: hxxp://satisfyammyz[.]com/
- File description: gzip binary from satisfyammyz[.]com used to create license.dat and persistent IcedID DLL
SHA256 hash: 1de8b101cf9f0fabc9f086bddb662c89d92c903c5db107910b3898537d4aa8e7
- File size: 342,218 bytes
- File location: C:\Users\[username]\AppData\Roaming\IslandDose\license.dat
- File description: data binary used to run persistent DLL for IcedID
- Note: this data binary was first submitted to VirusTotal on 2020-07-15
SHA256 hash: 501c05b11d90bbcc5b9439a41a66f9a4e1704447f795ce336492eb5e25c4ef8a
- File size: 272,896 bytes
- File location: C:\Users\[username]\AppData\Roaming\[username]\[username]\Kiroepdn3.dll
- File description: 64-bit persistent DLL for IcedID
- Run method: rundll32.exe [filename],#1 --tapeeb="[path to license.dat]"
SHA256 hash: e4ffdbfb5878a94d27139e2e7ff3b5b91944e1434935028a3c34894988b353bf
- File size: 1,018,880 bytes
- File location: hxxps://rosiyife[.]com/je.dll
- File location: C:\Users\[username]\AppData\Local\Temp\Ehki64.dll
- File description: 64-bit DLL for Cobalt Strike stager
- Run method: regsvr32.exe [filename]
Infection Traffic
MONSTER LIBRA (TA551) URL FOR ICEDID INSTALLER DLL:
- hxxp://138.124.183[.]50/barkss/u2lj2R9GN67SRsb7DZYKzF1jBt-yY6AVrA~~/5B6_95Swfy8TXGHD58qeEjYyxRXTL1bqhw~~/
ICEDID INSTALLER TRAFFIC FOR GZIP BINARY:
- 164.92.65[.]3:80 - hxxp://satisfyammyz[.]com/
ICEDID C2 TRAFFIC:
- 142.93.145[.]128:443 - klareqvino[.]com - HTTPS traffic
- 46.21.153[.]211:443 - wiandukachelly[.]com - HTTPS traffic
- 146.190.24[.]131:443 - alohasockstaina[.]com - HTTPS traffic
TRAFFIC FOR COBALT STRIKE STAGER:
- 213.227.154[.]24:80 - hxxp://rosiyife[.]com/je.dll (redirects to HTTPS URL)
- 213.227.154[.]24:443 - hxxps://rosiyife[.]com/je.dll
COBALT STRIKE C2 TRAFFIC:
- 23.82.141[.]241:443 - jejonebew[.]com - HTTPS traffic
POSSIBLE COBALT STRIKE-RELATED DOMAIN:
- 64.44.135[.]116:443 - xizojize[.]com - HTTPS traffic
DARK VNC TRAFFIC:
- 135.181.175[.]108:8080 - encoded/encrypted traffic
Images from the Infection Traffic
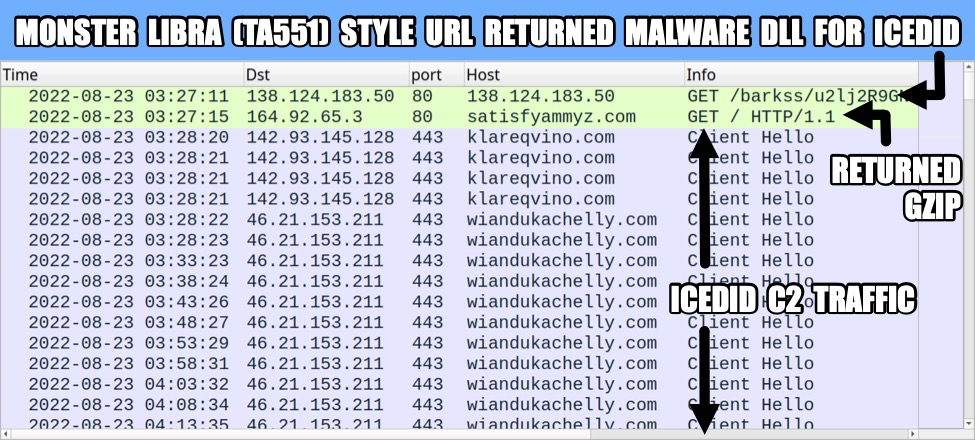
Shown above: Traffic from the infection filtered in Wireshark (1 of 4).
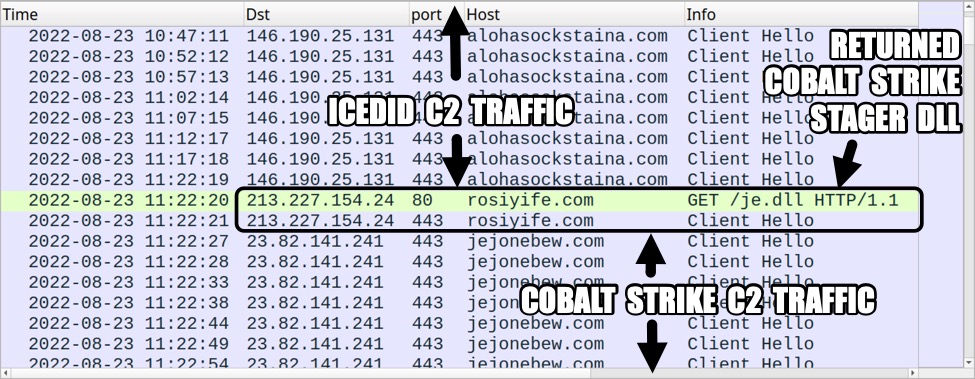
Shown above: Traffic from the infection filtered in Wireshark (2 of 4).
Shown above: Traffic from the infection filtered in Wireshark (3 of 4).
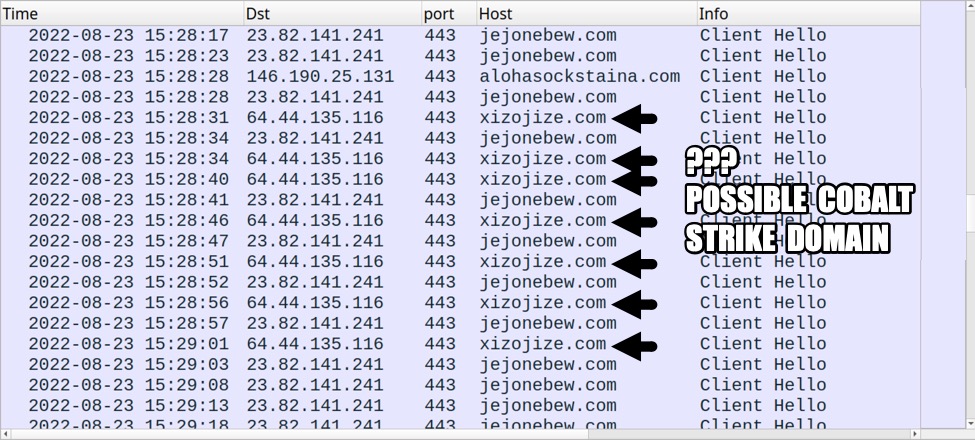
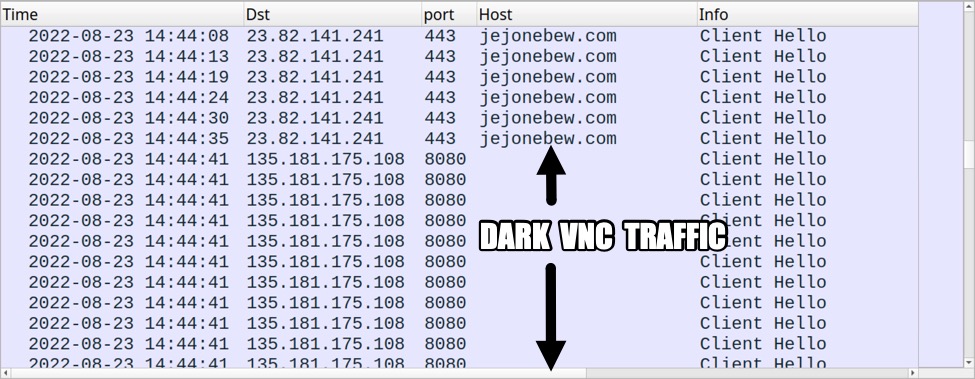
Shown above: Traffic from the infection filtered in Wireshark (4 of 4).
Final Words
We expect to see more of this activity in the coming weeks.
Brad Duncan
brad [at] malware-traffic-analysis.net


Comments