YARA's Private Strings
YARA supports private strings.
A string can be marked as private by including string modifier "private".
Here is a use case.
This is a rule to detect wannacry malware based on its killswitch (I'm using a screenshot to avoid false positives on this diary entry):
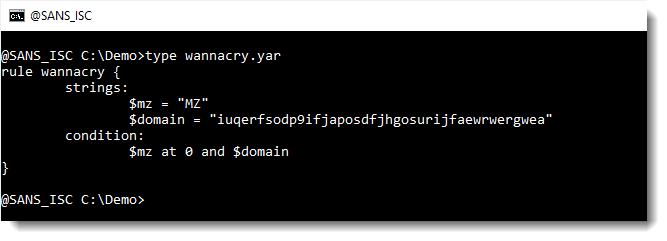
This rule searches for 2 strings: the $mz string and the $domain string.
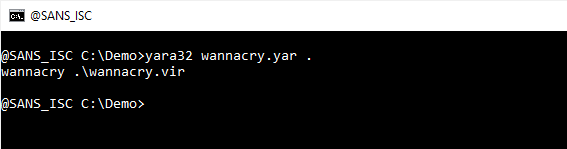
If they are found, the rule will trigger:
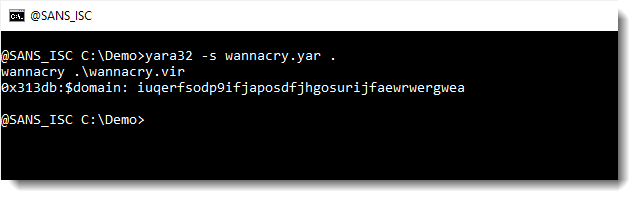
Using option -s, one can see where the strings were found inside a file:
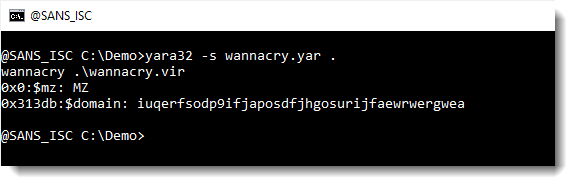
$mz at position 0x00 (that's the start of a PE file), and $domain at position 0x0313DB.
If one declares string $mz as private, like this:
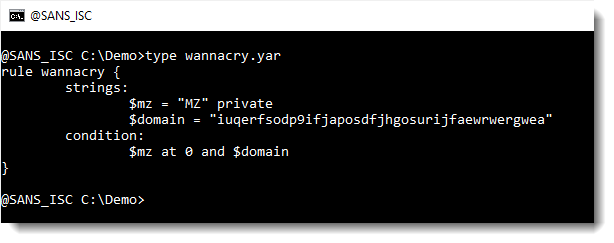
Then string $mz is not reported when option -s is used:
Thus modifier private can be used to hide some strings in YARA's output (or callback).
Personally, I've not had to use string modifier private yet. But it can help communicate which strings are important. For example to blue team members that handle the results of YARA rules you design.
$mz is not imporant here, because it is used as a simple trick to identify PE files. And PE files themselves, can be benign or malicious.
But if one finds a PE file containing the wannacry killswitch domain, then its most likely malicious.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com


Comments