Finding Strings With oledump.py
In diary entry "CFBF Files Strings Analysis" I show how to extract strings from CFBF/ole files with my tool oledump.py.
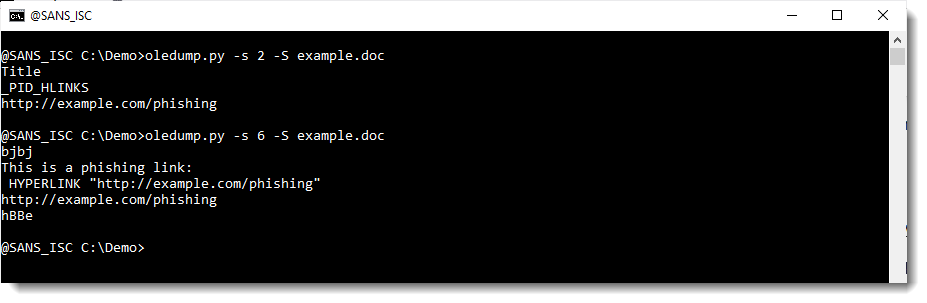
What if you have found an interesting string, and want to know from which stream it was extracted? Like the URL extracted in my previous diary entry: hxxp://example[.]com/phishing
oledump has an option to check the content of streams with YARA rules: -y.
You could make a small YARA rule to search for example.com, save it to disk and use it as oledump's -y value:
oledump.py -y rule.yara example.com
But you don't need to create a file with a YARA rule, you can also do this from the command-line using "Ad Hoc rules", like this:
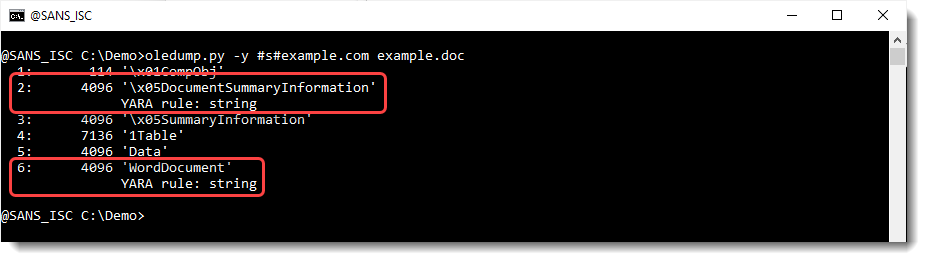
With this result, we know that stream 2 and 8 contain string example.com:
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com


Comments