YARA's BASE64 Strings
Since YARA version 4.0.0, Victor added support for detecting BASE64 encoded strings.
This means that from version 4.0.0 you can write a rule to search for strings that are BASE64 encoded.
For example, looking for string "Internet Storm Center" in BASE64 encoding, means searching for SW50ZXJuZXQgU3Rvcm0gQ2VudGVy (or other, depending on the position).
A rule for this string would look like this:
rule base64_ascii_ascii {
strings:
$a = "Internet Storm Center" base64
condition:
$a
}
This rule looks for ASCII strings that are valid BASE64 strings, and that decode to ASCII string "Internet Storm Center".
When you use keyword base64, you search for ASCII BASE64 strings. You can also search for UNICODE BASE64 strings, using keyword base64wide.
But in both cases, the decoded string is an ASCII string. If the decoded string has to be a UNICODE string, you need to use keyword wide.
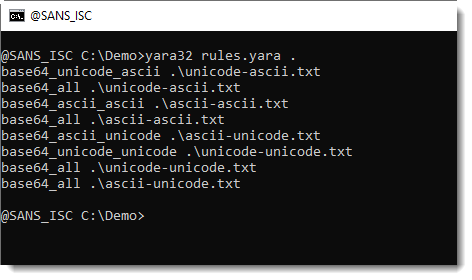
Here are 4 YARA rules, illustrating the 4 different combinations (ASCII ASCII, UNICODE ASCII,, ASCII UNICODE, and UNICODE UNICODE):
rule base64_ascii_ascii {
strings:
$a = "Internet Storm Center" ascii base64
condition:
$a
}rule base64_unicode_ascii {
strings:
$a = "Internet Storm Center" wide base64
condition:
$a
}rule base64_ascii_unicode {
strings:
$a = "Internet Storm Center" ascii base64wide
condition:
$a
}rule base64_unicode_unicode {
strings:
$a = "Internet Storm Center" wide base64wide
condition:
$a
}
If you don't know what combination you are looking for, you can also use the following rule that will match all combinations:
rule base64_all {
strings:
$a = "Internet Storm Center" ascii wide base64 base64wide
condition:
$a
}
Example:
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments