Huge Amount of remotewebaccess.com Sites Found in Certificate Transparency Logs
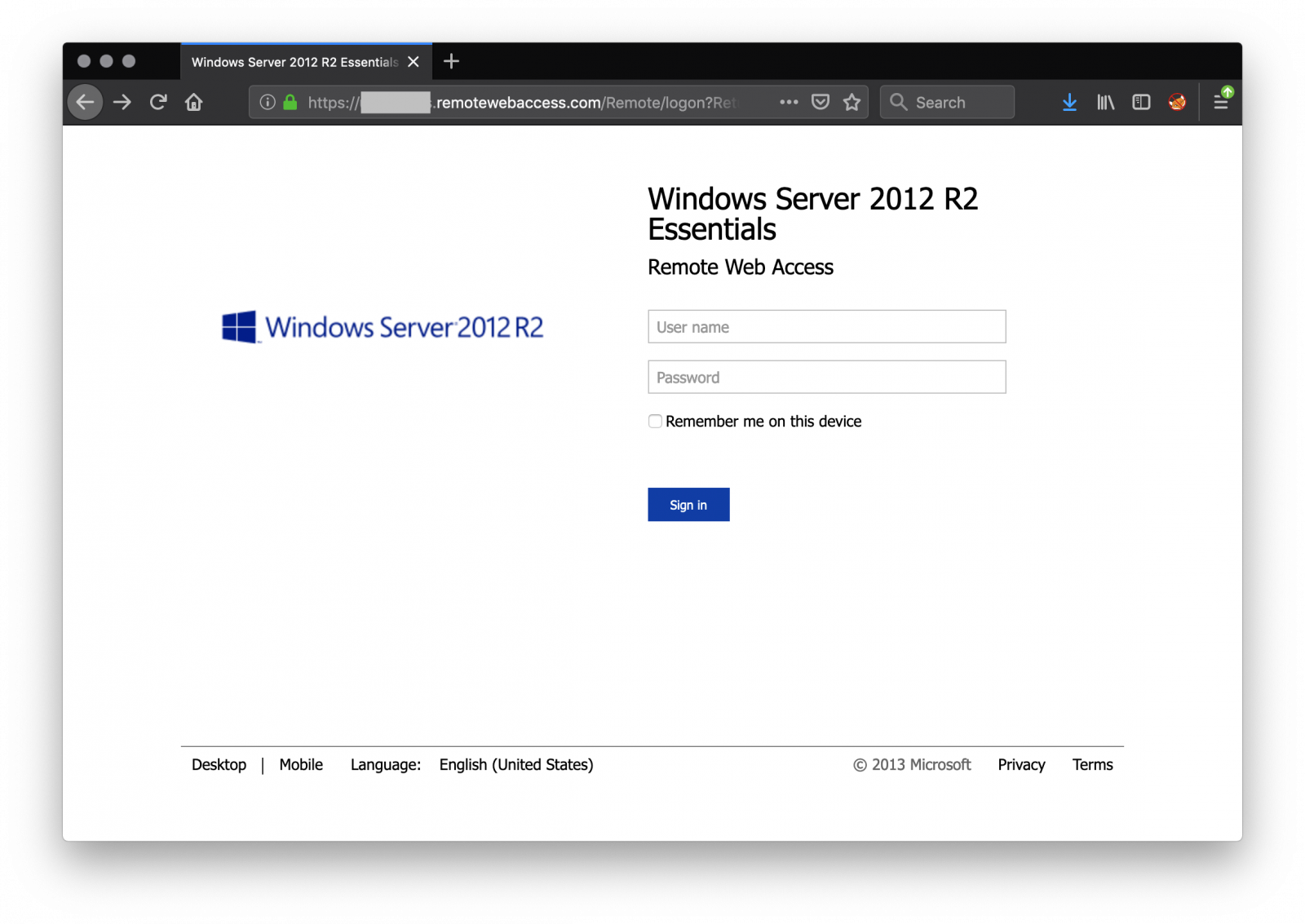
I'm keeping an eye on the certificate transparency logs[1] using automated scripts. The goal is to track domain names (and their variations) of my customers, sensitive services in Belgium, key Internet players and some interesting keywords. Yesterday I detected a peak of events related to the domain 'remotewebaccess.com'. This domain, owned by Microsoft, is used to provide temporary remote access to Windows computers[2]. Microsoft allows you to use your own domain but provides also (for more convenience?) a list of available domains. Once configured, you are able to access the computer from a browser:
In my logs, just for yesterday, I found 49610 entries based on the domain 'remotewebaccess.com'. In many cases, the first part of the FQDN reveals clearly the name of the company or the business (ex: 'clinic', 'health', etc). Amongst those sites, approximately 500 were alive and reachable from anywhere.
Be careful when you use this feature because your chosen FDQN can be disclosed in certificate transparency lists and they are not only watched by blue teams!
[1] http://www.certificate-transparency.org/known-logs
[2] https://techcommunity.microsoft.com/t5/Windows-Server-Essentials-and/Configuring-and-Customizing-Remote-Web-Access-on-Windows-Server/ba-p/398904
Xavier Mertens (@xme)
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key


Comments