House for rent! Observing an Overpayment Scam
About a month ago, my wife posted a "House for Rent" ad on Craigslist. (real nice house in a great area btw... in case someone is moving to Jacksonville ;-) ). A couple responses came in, among them, one from a person in England. Odd, but there are actually a couple British living in the neighborhood, so she responded:
From: C M [*** names altered ***] Subject: Rent InquiryHello - I'm inquiring about the rental property, I will like to get some more details about the property, I'll like you to give me the below detail ...[*** questions about property ***]
From: H Subject: your inquire about ... Hi C thanks for your interest. Please see the answers to your detailed questions below. Please feel free to call my cell phone *** if you would like to see the property in person ... answers to questions removed ....
From: C M
Subject: Re: your inquire about ...
Hello H -
Thanks for your respond, firstly I would want you to know that the property
is OK with me and I would like to rent the property. I will be staying in the
property for 1 year after which I will extend my contract on the property if OK
with my need.
I work with '*** ENGINEERING LIMITED' in England as a CNC 5 axis machining centre
setter/operator/programmer and I'm on transfer to the USA.
I will be moving with my wife, I'd like to know how far is the place from bus station,
police station and gas station.
At this point I want you to know that my company will handle the first month
and the deposit which is ($2470) after which other payment for the property will
be handle by me in person.
I would also want you to know that all application and lease papers will be sign
by me in person when I arrive.
If this is OK with you, kindly send me the following details listed below ...
'Full Name that will be on the check'
'Mailing Address where you can receive the check'
'Home Phone'
'cell phone'
Once I receive these details from you, I'll send it to my employer, so that the
payment can be issued out to you immediately. We'll be moving in on the 1st of
November 2011. Looking forward to your reply.
Best Regards
C M
my wife responded (PO Box address she uses for the rental business, and she did not provide a home phone number). This was WAY too easy. A person being so fast signing up for a house unseen? We must have been too cheap!
And a few days later, the check arrived:
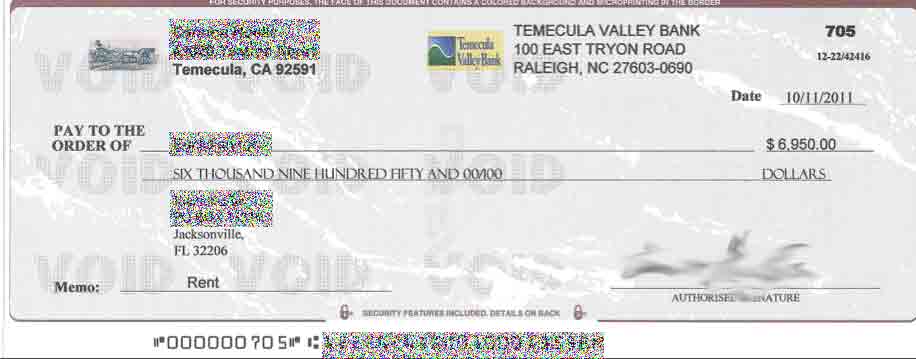
The check was written in the name of a person that is listed as an accountant / notary public in the town of Temecula, but the number I found is now used by a different company. The bank, Temecula Valley Bank, failed in July 2009 (http://fdic.gov/bank/individual/failed/temecula.html) and has since been acquired by First Citizens. It is not clear if the check would be honored (if it would be real). We didn't try to cash it.
It didn't take long to find out why we got such a "generous" check. First month rent + depost was only around $2,000. Instaed, we got almost $7,000!! An e-mail arrived essentially the same day the check arrived, apologizing for the overpayment, asking us to split the overpayment and send it via Western Union to two different addresses in the UK.
Luckily no damage has been done to us. I am still trying to figure out if the person named as origin of the check actually exists and got harmed. I have no reason to believe that this person, if they exist, are aware or profiting from this scan. We did report this to http://www.ic3.gov .
According to the FBI's Internet Crime Complaint Center (IC3), 3.6% of the complaints relate to overpayment fraud.
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
Oracle Critical Patch Update
Those of you that are Oracle product users will be used to the quarterly Critical Patch Update. In case you missed it, it was released on the 17th. There is a patch out for most of the major products. Detailed information can be found here http://www.oracle.com/technetwork/topics/security/cpuoct2011-330135.html
The appendix of the above note shows the affected CVEs and the associated CVS scores. The criteria for the scores are shown, so you should be able to determine the local impact for your organisation.
If you are running Oracle I suggest you start looking at these sooner rather than later, especially if you need to comply with PCI DSS and your onsite audit is getting near.
Mark H
The old new Stuxnet...DuQu?
Yes, the tittle probably makes no sense at first, but keep reading...:)
Today was a pretty good day if you like malware and RE...
Symantec, McAfee and F-Secure, to name a few security vendors, released information about what they are calling "DuQu"...yes, I agree that it is a terrible name, but it is because this malware creates some files on the user's temp folder, that starts with ~DQXXX.tmp (where the XXX can be any number)...
There are several common aspects between DuQu and Stuxnet that leads to the conclusion that they were written by the same group.
While the original Stuxnet was focused on Industrial systems, aka SCADA, this DuQu malware is mostly used on a recon process, and being used as an advanced RAT (Remote Administration Tool). Forget about Gh0st RAT or BlackShades RAT, just to name two "famous" ones...those are totally amateurs when compared to DuQu.
DuQu received commands via an encrypted config file, and seems to download a password stealer that is able to record several behaviors from user and machine and send to a Command and Control IP in India.
Like some of the components of the original Stuxnet, this one was also able to decrypt and extract additional components embedded into other PE files...fantastic!
Oh, and like Stuxnet, some components had a VALID digital signature...:)
And before I forget, according Symantec report, new samples with compilation time of October 17th were discovered and are still being checked...
Agree that it is a good day for Reverse Engineers?
_______________________________________________
Pedro Bueno (pbueno /%%/ isc. sans. org)
Twitter: http://twitter.com/besecure


Comments