AutoIT based malware back in the wild
One week ago I wrote a diary[1] with an analysis of a malicious RAR archive that contained an AutoIT script[2]. The technique was not new but I was curious to see if this was a one-shot or not. To search for juicy samples, VirusTotal Intelligence or “VTI” is a nice source. Thanks to the “Retro Hunt” feature, it is possible to search for specific samples that were submitted. The search conditions are based on YARA rules.
My initial sample contained the AutoIT executable (SHA1: cae4e8c730de5a01d30aabeb3e5cb2136090ed8d[3]). This hash is a good candidate for a simple YARA rule:
import "hash"
rule AutoIT {
strings:
$m0 = { 4D 5A } // PE file
condition:
$m0 at 0 and
hash.sha1(0, filesize) == "cae4e8c730de5a01d30aabeb3e5cb2136090ed8d"
}
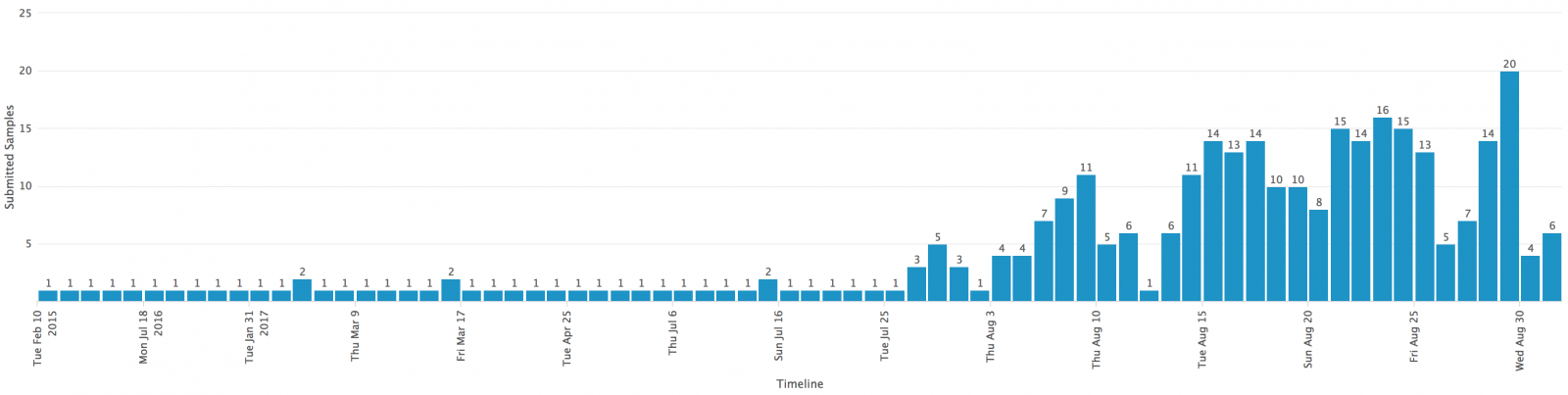
I performed my retro hunt search and a few hours later, I got the results in my mailbox: 319 hashes! The first submission was from February 2015 and the latest one, a few minutes ago. Here is a timeline with all the submissions, we can see clearly a trend that started around the end of July:
Are we facing a massive campaign? I don’t think so because the number of submissions per samples remains low:
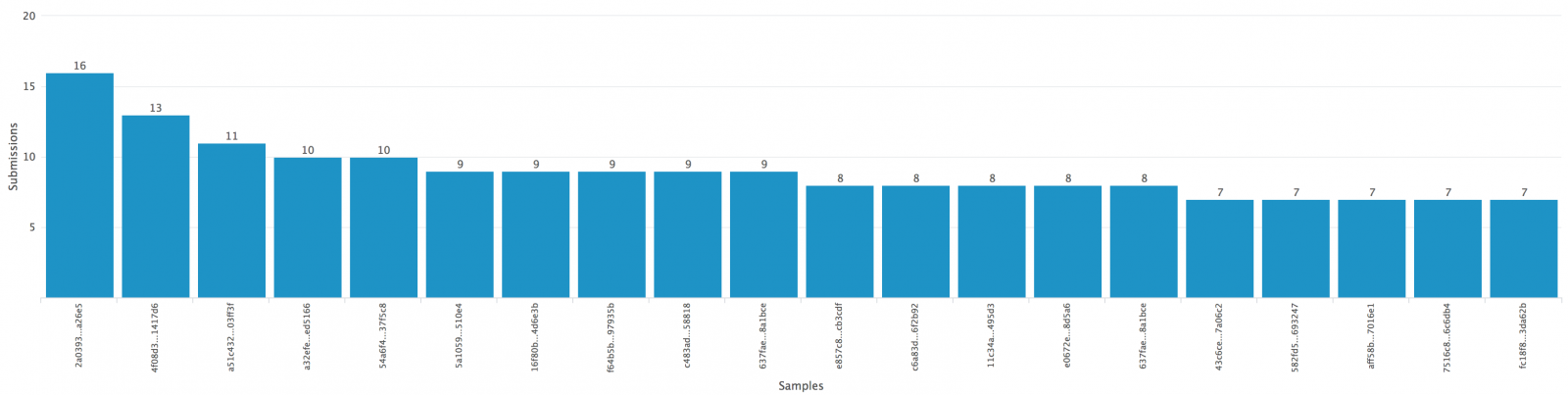
When there is a huge attack, samples will be submitted many times and it's not the case here: 16 submissions for a sample worldwide is very low. No specific geographical area targeted, samples were submitted from all over the world (CA,DE, US, VN, UA, RU, BR, CZ, FR, KR, HU) with maybe more sample coming from CZ and KR. Most samples have a good detection score:
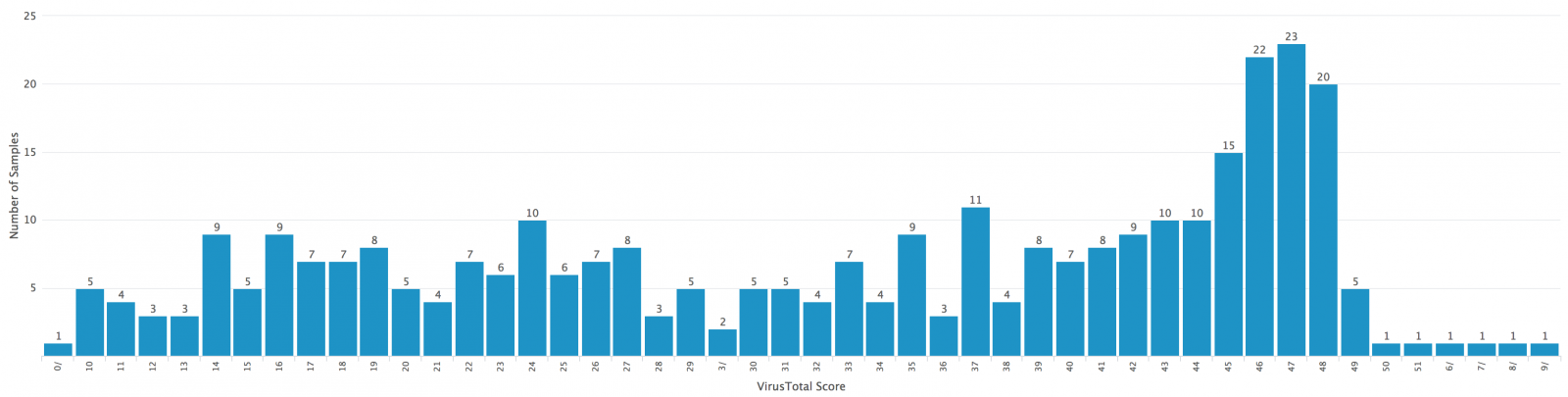
Note: the file with a null-score was not malicious and contained valid AutoIT scripts.
I downloaded some samples to investigate them deeper. They were based on the same one as analyzed in my previous diary. They were also close to each other:
AutoIT viper 1593fc1ac7f8bb3cc32ecefdf7c09dfccc2f7c715eb66fba5620575eaf8d8972 > open -l 3; fuzzy [*] Session opened on /home/nonroot/workdir/projects/AutoIT/binaries/c/6/e/c/c6eccb4f284791a809c71cfd6fdf169fef6f51e79a5be88d4a885b2c7c4c2e2c [*] 10 relevant matches found +-------+------------------------------------------------------------------+------------------------------------------------------------------+ | Score | Name | SHA256 | +-------+------------------------------------------------------------------+------------------------------------------------------------------+ | 65% | f5459ce54b04e3327a6282bc7b3c4f8f7ac8a24731b370d053bfa7ec8d727e3c | f5459ce54b04e3327a6282bc7b3c4f8f7ac8a24731b370d053bfa7ec8d727e3c | | 54% | c12d73b45adb681d490a621d6e4b4a85d49ec3325d92aa6e340b765c499a3d9b | c12d73b45adb681d490a621d6e4b4a85d49ec3325d92aa6e340b765c499a3d9b | | 55% | ba81f985e1eb8ceb787f7e93dc90db9ec3d9dc37a69a5141b15b3c61b8f95153 | ba81f985e1eb8ceb787f7e93dc90db9ec3d9dc37a69a5141b15b3c61b8f95153 | | 58% | b68f8c83dc0945ebc3d72e65a5029cd9ab7451a510ed04afa63a93e190264cad | b68f8c83dc0945ebc3d72e65a5029cd9ab7451a510ed04afa63a93e190264cad | | 63% | 8aad218a6ec84386f6793348eed65055842e9fdd7f52043669897dfd20f0263a | 8aad218a6ec84386f6793348eed65055842e9fdd7f52043669897dfd20f0263a | | 41% | 87fda93356c98fd07f15c979acb164520c27ff255520c3877b549618d6ad3f98 | 87fda93356c98fd07f15c979acb164520c27ff255520c3877b549618d6ad3f98 | | 44% | 796dece2ee25bf190b940d02a96269e005175e46ecaf994a9b56fd0384a58d25 | 796dece2ee25bf190b940d02a96269e005175e46ecaf994a9b56fd0384a58d25 | | 46% | 767e7552c3c0d4b38d3635bfc9a8cfde583a9c21eebd606d67278b436898e8f8 | 767e7552c3c0d4b38d3635bfc9a8cfde583a9c21eebd606d67278b436898e8f8 | | 49% | 645f9f9ef1de9b25afbb93a7b35b417442d01a895b07acd7aaf294174c4f77ad | 645f9f9ef1de9b25afbb93a7b35b417442d01a895b07acd7aaf294174c4f77ad | | 52% | 1593fc1ac7f8bb3cc32ecefdf7c09dfccc2f7c715eb66fba5620575eaf8d8972 | 1593fc1ac7f8bb3cc32ecefdf7c09dfccc2f7c715eb66fba5620575eaf8d8972 | +-------+------------------------------------------------------------------+------------------------------------------------------------------+
I also added a hunting rule on VTI to detect the same kind of malicious files. Since I performed the retro hunt query (2 days ago), I already got 24 notifications! Always the same kind of file, a self-extracting RAR archive with the AutoIT official binary and a bunch of malicious AutoIT scripts.
[1] https://isc.sans.edu/forums/diary/Malicious+AutoIT+script+delivered+in+a+selfextracting+RAR+file/22756/
[2] https://www.autoitscript.com/site/
[3] https://www.virustotal.com/#/file/fb73a819b37523126c7708a1d06f3b8825fa60c926154ab2d511ba668f49dc4b/detection
Xavier Mertens (@xme)
ISC Handler - Freelance Security Consultant
PGP Key


Comments
For now we have added the AutoIt compiled .exe to the scan exception list.
Anonymous
Sep 2nd 2017
8 years ago