Microsoft's Coreutils for Windows
I've been using the GnuWin32 CoreUtils for Windows for many years now (it gives you many *nix core commands on Windows).
Microsoft has just released their coreutils version for Windows.
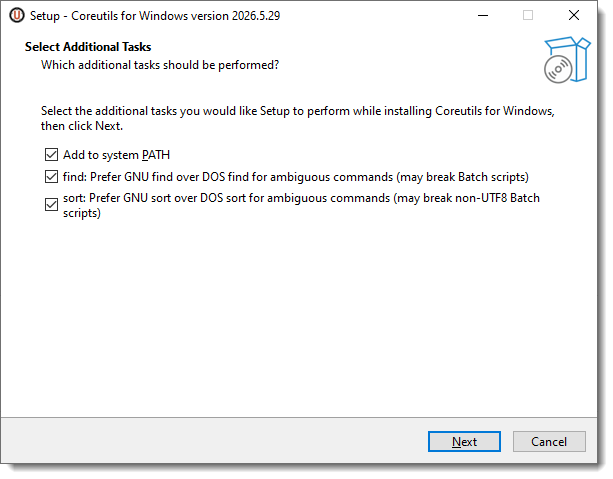
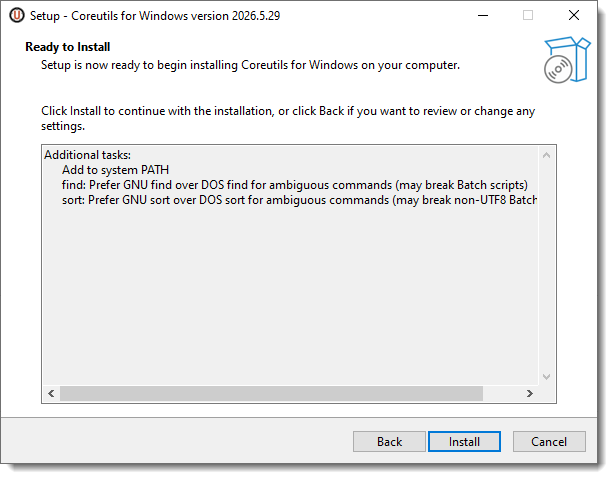
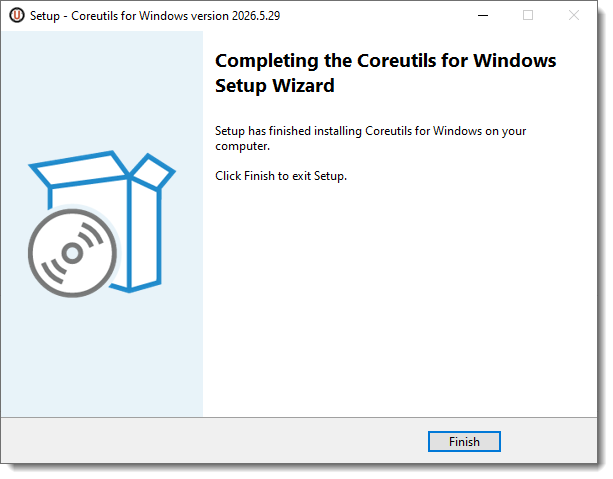
You can install them with a winget command (winget install Microsoft.Coreutils) or with the installer released on GitHub.
It takes just a few clicks:
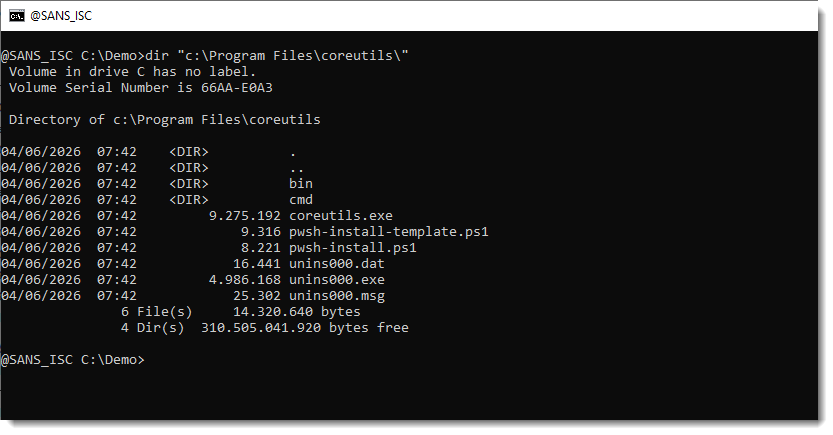
It installs a single executable compiled with Rust (coreutils.exe) in the program files folder:
And each individual command is a hard link to this executable:
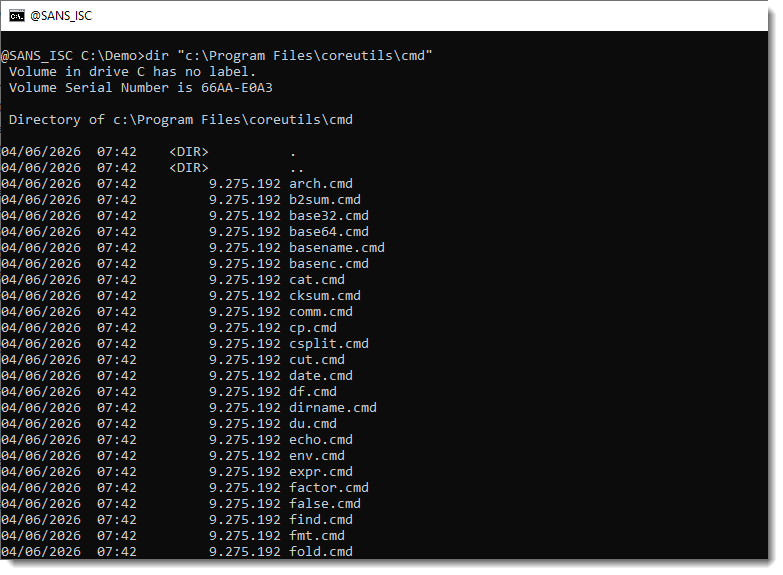
Here is the full list of commands:
arch.cmd
b2sum.cmd
base32.cmd
base64.cmd
basename.cmd
basenc.cmd
cat.cmd
cksum.cmd
comm.cmd
cp.cmd
csplit.cmd
cut.cmd
date.cmd
df.cmd
dirname.cmd
du.cmd
echo.cmd
env.cmd
expr.cmd
factor.cmd
false.cmd
find.cmd
fmt.cmd
fold.cmd
grep.cmd
head.cmd
hostname.cmd
join.cmd
link.cmd
ln.cmd
ls.cmd
md5sum.cmd
mkdir.cmd
mktemp.cmd
mv.cmd
nl.cmd
nproc.cmd
numfmt.cmd
od.cmd
pathchk.cmd
pr.cmd
printenv.cmd
printf.cmd
ptx.cmd
pwd.cmd
readlink.cmd
realpath.cmd
rm.cmd
rmdir.cmd
seq.cmd
sha1sum.cmd
sha224sum.cmd
sha256sum.cmd
sha384sum.cmd
sha512sum.cmd
shuf.cmd
sleep.cmd
sort.cmd
split.cmd
stat.cmd
sum.cmd
tac.cmd
tail.cmd
tee.cmd
test.cmd
touch.cmd
tr.cmd
true.cmd
truncate.cmd
tsort.cmd
unexpand.cmd
uniq.cmd
unlink.cmd
uptime.cmd
wc.cmd
xargs.cmd
yes.cmd
Didier Stevens
Senior handler
blog.DidierStevens.com
Keywords:
0 comment(s)ISC Stormcast For Thursday, June 4th, 2026 https://isc.sans.edu/podcastdetail/9958
×
![modal content]()
Diary Archives


Comments