/tmp, %TEMP%, ~/Desktop, T:\, ... A goldmine for pentesters!
When you are performing a penetration test, you need to learn how your target is working: What kind of technologies and tools are used, how internal usernames are generated, email addresses format, ... Grabbing for such information is called the reconnaissance phase. Once you collected enough details, you can prepare your different scenarios to attack the target. All pentesters have their personal toolbox that has been enhanced day after day. In many cases, there is no real magic: to abuse or get around a security control "x", use the tool "y". But there is also a question of chance... Lucky people can discover security issues "by chance". This also applies to bad guys.
A goldmine for the pentester are temporary directories. Almost all software use temporary files to perform their tasks. Users like to use them to exchange files with colleagues. I'll give you two real examples:
In a recent mission, I took control of a workstation connected to the Windows domain then I started to collect juicy data by browsing all the fileshares. The customer implemented access controls and access to files was restricted at group level (Example: only the IT team was able to access the "I:" drive containing technical documentation about the infrastructure). However, some people exchanged IT related files via the "T:" share and they were still available during the pentest.
Another one? When pivoting from workstation to workstation on a LAN, I discovered a screenshot on a user's desktop. This screenshot was a domain controller admin page which listed all the domain administrators. I just had to track them and, once a valid session found, to extract the user's password with Mimikatz to get domain admin privileges.
On Linux systems, the /tmp directory is usually cleaned at boot time or via a cron (files older than x days are removed) but other places like /var/tmp, /usr/local/tmp are not cleaned by default! It is easy to schedule the following command at regular interval. It will delete files from /tmp that haven't be modified for more than 7 days.
# find /tmp -mtime +7 -exec rm -rf {} \;
On Ubuntu, files in /tmp are cleaned at book time via the variable TMPTIME=
An easy way to automate this task is to create a small script and execute it at your best convenience (at boot time or at regular interval via a scheduled task:
rd %TEMP% /s /q md %TEMP%
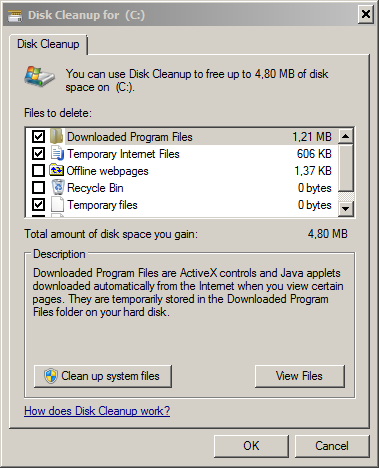
There exist plenty of tools which also take care of temporary files like CCleaner. To clean up files on a temporary fileshare, Powershell is helpful:
PS C:\> $days = (Get-Date).AddDays(-7)
PS C:\> $path = "T:\"
PC C:\> Get-ChildItem -Path $path -Recurse -Force | Where-Object { !$_.PSIsContainer -and $_.CreationTime -lt $days } | Remove-Item -Force
Some best practices:
- By definition, temporary files must have a very short life time.
- Do NOT share sensitive data via fileshares (database dumps, backups, passwords lists, ...)
- Once you finished to work with temporary files, don't forget to delete them.
- If you need to exchange files with colleagues via a shared folder, keep in mind that often other people could read them.
- Change the permissions to restrict access to authorized users/groups only via chmod / chown on UNIX or icacls on Windows (or the GUI).
- Encrypt sensitive data (internally, a password protected zip file will be enough in most cases).
- On Unix, use umask to change the default permissions of created files.
Xavier Mertens
ISC Handler - Freelance Security Consultant
PGP Key


Comments
a small typo in $days = (Get-Data).AddDays(-7)
Should be (Get-Date)
/Mattias Borg
Anonymous
Jan 20th 2016
1 decade ago
Anonymous
Jan 20th 2016
1 decade ago
rd %TEMP% /s /q
md %TEMP%
[/quote]
OUCH!
On Windows every user has an own %TEMP% located in the %USERPROFILE% and not accessible by other users.
0. the "crosstalk" you describe can only happen with a shared %TEMP%.
1. a script like this has to be run during user login.
2. you should NOT remove %TEMP%: it can have a custom (non-inherited) ACL which will not be recreated!
You better run %SystemRoot%\System32\RunDll32.Exe %SystemRoot%\System32\AdvPack.Dll,DelNodeRunDLL32 "%TEMP%",4
The flag '4' keeps the %TEMP% directory.
If you really want to use the command processor (and display it's window to the user) you better run
%COMSPEC% /C PushD "%TEMP%" && Erase /F /S /Q .
or
%COMSPEC% /C ChDir /D "%TEMP%" && RmDir /S /Q .
Anonymous
Jan 20th 2016
1 decade ago
# find /tmp -mtime +7 -exec rm -rf {} \;
[/quote]
OUCH!
That can be raced to remove anything at all:
http://seclists.org/bugtraq/1996/May/46
http://www.securityfocus.com/archive/1/304192
http://www.dwheeler.com/secure-programs/Secure-Programs-HOWTO/avoid-race.html#TEMPORARY-FILES
Anonymous
Jan 20th 2016
1 decade ago
Recent "find" have the "-P" flag enabled by default:
"-P Never follow symbolic links. This is the default behaviour. When find examines or prints information a file, and the file is a symbolic link, the information used shall be taken from the properties of the symbolic link itself."
(find will delete the symlink but the original file will remain)
Anonymous
Jan 21st 2016
1 decade ago
And it's amazing what you can find in browser caches which they thought long removed.
Anonymous
Jan 21st 2016
1 decade ago
# find /tmp -mtime +7 -exec rm -rf {} \;
OUCH! That can be raced to remove anything ...
You're right with old versions of "find". ...
Recent "find" have the "-P" flag ...
[/quote]
Sorry, but -P (or -nofollow) is irrelevant: passing pathnames
from find to rm is a typical ToCToU issue. Please see the bugtraq
thread mentioned for PoC that would work with -P as default.
Maybe you could advocate using "find ... -delete" (instead of
that messy "-exec rm")? I do not know how common that is...
nor have verified whether it is "safe".
Anonymous
Jan 22nd 2016
1 decade ago
Anonymous
Jan 22nd 2016
1 decade ago
Anonymous
Jan 22nd 2016
1 decade ago
Also consider to define your own "cleaners": see
https://msdn.microsoft.com/en-us/bb776782.aspx
For a working example see http://home.arcor.de/skanthak/download/OE_STALE.REG: this removes the bird droppings of Outlook Express 6 and Windows Mail.
Anonymous
Jan 22nd 2016
1 decade ago