Exploit Attempts Against Older Hikvision Camera Vulnerability
I notice a new URL showing up in our web honeypot logs, which looked a bit interesting:
/System/deviceInfo?auth=YWRtaW46MTEK
The full request: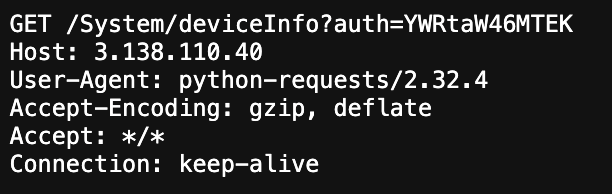
GET /System/deviceInfo?auth=YWRtaW46MTEK Host: 3.87.70.24 User-Agent: python-requests/2.32.4 Accept-Encoding: gzip, deflate Accept: */* Connection: keep-alive
The "auth" string caught my attention, in particular as it was followed by a base64 encoded string. The string decodes to admin:11.
This "auth" string has been around for a while for a number of Hikvision-related URLs. Until this week, the particular URL never hit our threshold to be included in our reports. So far, the "configurationFile" URL has been the most popular. It may give access to additional sensitive information.
| Earliest Report | Most Recent Report | Total Number of Reports | URL |
|---|---|---|---|
| 2018-08-18 | 2025-09-23 | 6720 | /System/configurationFile?auth=YWRtaW46MTEK |
| 2017-12-14 | 2025-09-23 | 2293 | /Security/users?auth=YWRtaW46MTEK |
| 2021-03-09 | 2025-09-23 | 2002 | /system/deviceInfo?auth=YWRtaW46MTEK |
| 2020-09-25 | 2023-02-04 | 727 | /security/users/1?auth=YWRtaW46MTEK |
| 2018-09-09 | 2025-09-23 | 445 | /onvif-http/snapshot?auth=YWRtaW46MTEK |
| 2017-10-06 | 2017-10-06 | 6 | /Streaming/channels/1/picture/?auth=YWRtaW46MTEKYOBA |
| 2025-04-09 | 2025-04-29 | 2 | /ISAPI/Security/users?auth=YWRtaW46MTEK |
Some Googleing leads to CVE-2017-7921 [1]. Hikvision's advisory is sparse and does not identify a particular vulnerable URL [2]. But this looks to me more like some brute forcing. The CVE-2017-7921 vulnerability is supposed to be some kind of backdoor (Hikvision's description of it as "privilege escalation" was considered euphemistic at the time). But I doubt the password is "11", and a typical Hikvision default password is much more complex ("123456" in the past).
We have written about Hikvision many times before; its cameras, as well as cameras from competitors like Dahua, are well known for their numerous security vulnerabilities, hard-coded "support passwords", and other issues. One issue with many of these cameras has been a limited user interface. The DVR used to collect footage from these cameras often only includes a mouse and an onscreen keyboard, making it difficult to select reasonable passwords. This attack may count on users setting a simple password like "11" as by default, only a numeric onscreen keyboard is displayed on some models.
Another issue is the use of credentials on the URL, which is discouraged as they tend to leak easily in logs. But it may be yet again a convenience decision as you are able to create hyperlinks that will log you in automatically.
[1] https://nvd.nist.gov/vuln/detail/cve-2017-7921
[2] https://www.hikvision.com/us-en/support/document-center/special-notices/privilege-escalating-vulnerability-in-certain-hikvision-ip-cameras/
--
Johannes B. Ullrich, Ph.D. , Dean of Research, SANS.edu
Twitter|


Comments