Phishing 101: why depend on one suspicious message subject when you can use many?
There are many e-mail subjects that people tend to associate with phishing due to their overuse in this area. Among the more traditional and common phishing subjects, that most people have probably seen at some point, are variations on the “Your account was hacked”, “Your mailbox is full”, “You have a postal package waiting”, “Here are urgent payment instructions” and “Important COVID-19 information” themes.
Since security awareness courses often explicitly cover these, and e-mail messages with similar subjects are therefore usually classified by users as prima facie phishing attempts, one would reasonably expect that when a threat actor decides to use any such subject line, they would at least try to make the body of the e-mail a little more believable… However, as it turns out, this is not always the case.
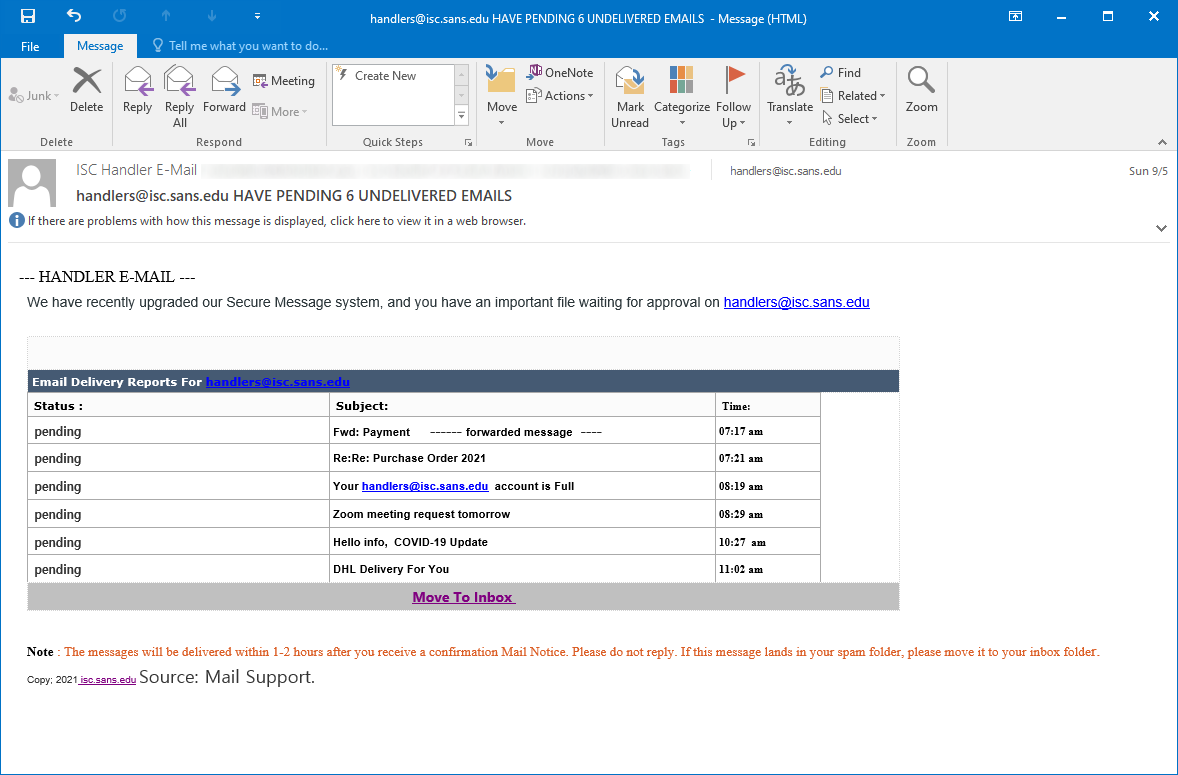
We’ve recently received a phishing on our Handler e-mail address, which I found interesting, since its authors obviously decided to go the “all in” route when came to the use of multiple obviously suspicious message subjects, rather than try to make their creation more believable.
“But how could a single phishing e-mail have multiple subjects”, I hear you ask, dear reader.
Well, in this case, the phishing was a variation on the “You have undelivered e-mail messages waiting” theme, but instead of a list of urgent looking, yet believable subject lines, it contained pretty much the whole aforementioned set of suspicious-at-first-glance subjects, as you may see for yourself in the following image…
Apart from this rather interesting (and slightly funny) approach on the side of its authors, the e-mail was rather a low-quality example of a phishing, its less than professional origins showing – among other places – in the fact that multiple links pointed to URLs that were obviously intended for previous recipients/recipients from other domains.
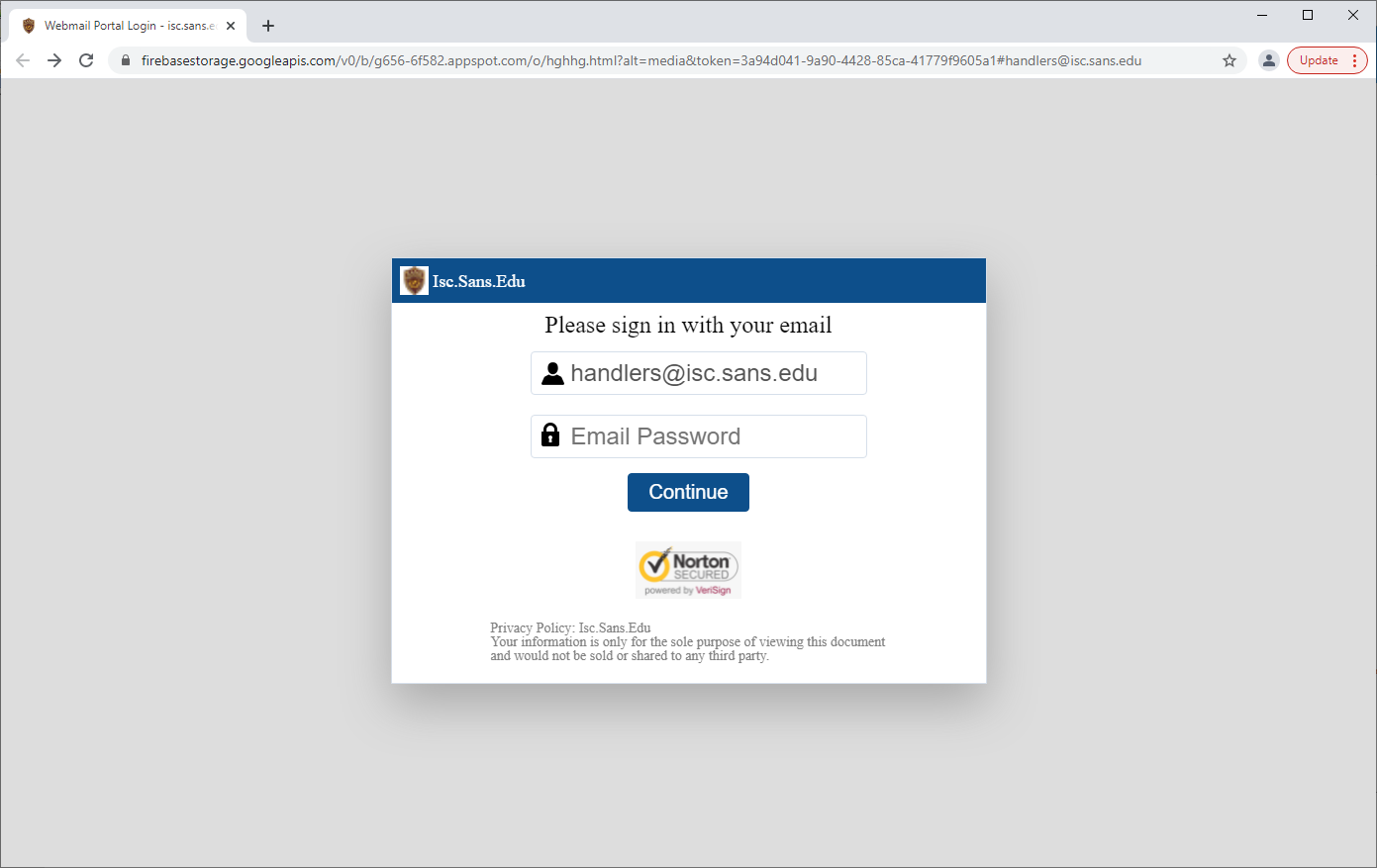
The only link that did lead to a phishing page pointed to an HTML document hosted on the Google Firebase Storage that, when accessed, displayed a dynamically generated login prompt and tried to load a web page hosted on the domain to which the e-mail address belonged in an iframe bellow this prompt in an attempt to make the login request look more believable (a technique that is fairly common[1], which provides another good reason why it’s advisable to use CSP/X-Frame-Options headers on ones webservers).
IoC
hxxps://firebasestorage[.]googleapis[.]com/v0/b/g656-6f582.appspot.com/o/hghhg.html?alt=media&token=3a94d041-9a90-4428-85ca-41779f9605a1#[email protected]
[1] https://isc.sans.edu/forums/diary/Slightly+broken+overlay+phishing/26586/


Comments