Sysmon Version 10: DNS Logging
Sysmon Version 10.0 brings DNS query logging.
By default, DNS query logging is not enabled. You need to provide a configuration file, like this simple config.xml:
<Sysmon schemaversion="4.21">
<EventFiltering>
<DnsQuery onmatch="exclude">
</DnsQuery>
</EventFiltering>
</Sysmon>
This config file will log all DNS queries: using onmatch="exclude" without any filters excludes no events at all.
Remark also that the event is DnsQuery (and not DNSQuery as listed on Sysinternals page for Sysmon).
Here is a simple "ping google.com" command, resulting in event 22 being logged in the Sysmon Windows event log:
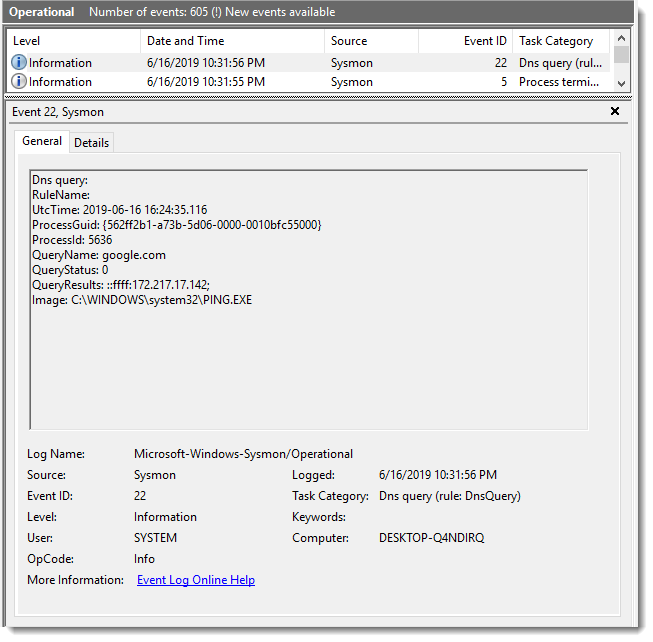
Remark that event 22 does not only log the DNS query, but also the replies and the program that issued the query.
If you enable DNS logging like I did (not exclusions) in a production environment, you will have too many events. SwiftOnSecurity's Sysmon config can help you exclude many queries that are not important for IR.
Sysmon DNS logging did not work on my Windows 7 VM, but I just noticed that Sysmon version 10.1 was released, I will test this again.
Update: version 10.1 on Windows 7 does not log DNS events.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments
For example if this was running on a Windows DC/DNS Server could it log the remote client that's performing the query.
Anonymous
Jun 20th 2019
6 years ago